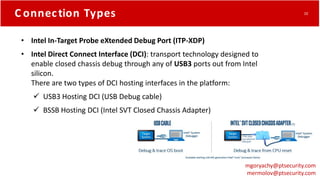
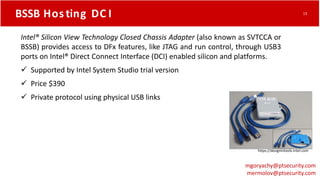
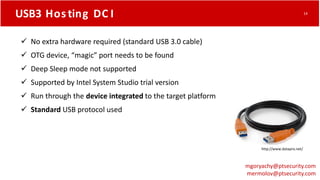
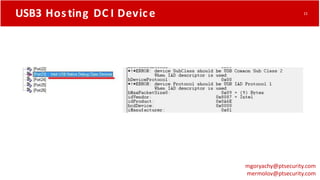
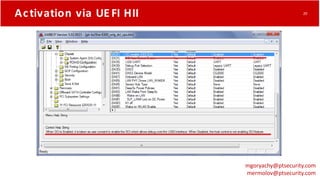
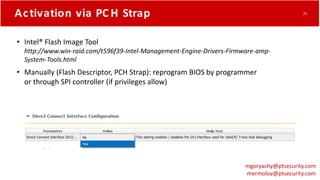
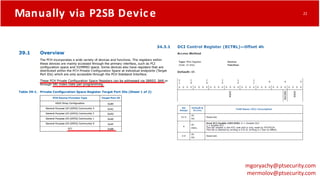
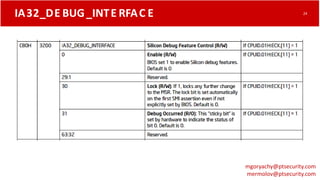
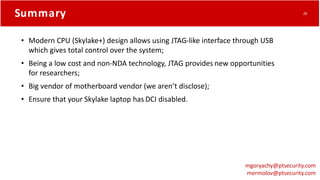
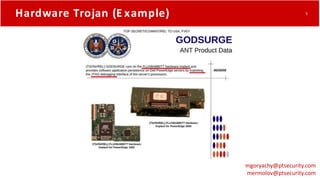
The document discusses how modern Intel CPUs contain debugging features like JTAG that could enable hardware trojans if activated. It describes how the Intel Direct Connect Interface allows activating JTAG-like debugging over USB, potentially allowing full system control. It demonstrates activating DCI on a laptop through the UEFI and explains how to detect if DCI is enabled. The document warns that DCI could lead to a "new age of BadUSB" if used maliciously.
![What Is JTAG?
Joint Test Action Group IEEE 1149.1
• https://en.wikipedia.org/wiki/JTAG
• IEEE Standard 1149.1
https://standards.ieee.org/findstds/standard/1149.1-2013.html
• Blackbox JTAG Reverse Engineering [26C3]
https://www.youtube.com/watch?v=Up0697E5DGc
https://www.xjtag.com
mgoryachy@ptsecurity.com
mermolov@ptsecurity.com
7](https://image.slidesharecdn.com/tappingintothecore-161229114904/85/Tapping-into-the-core-7-320.jpg)