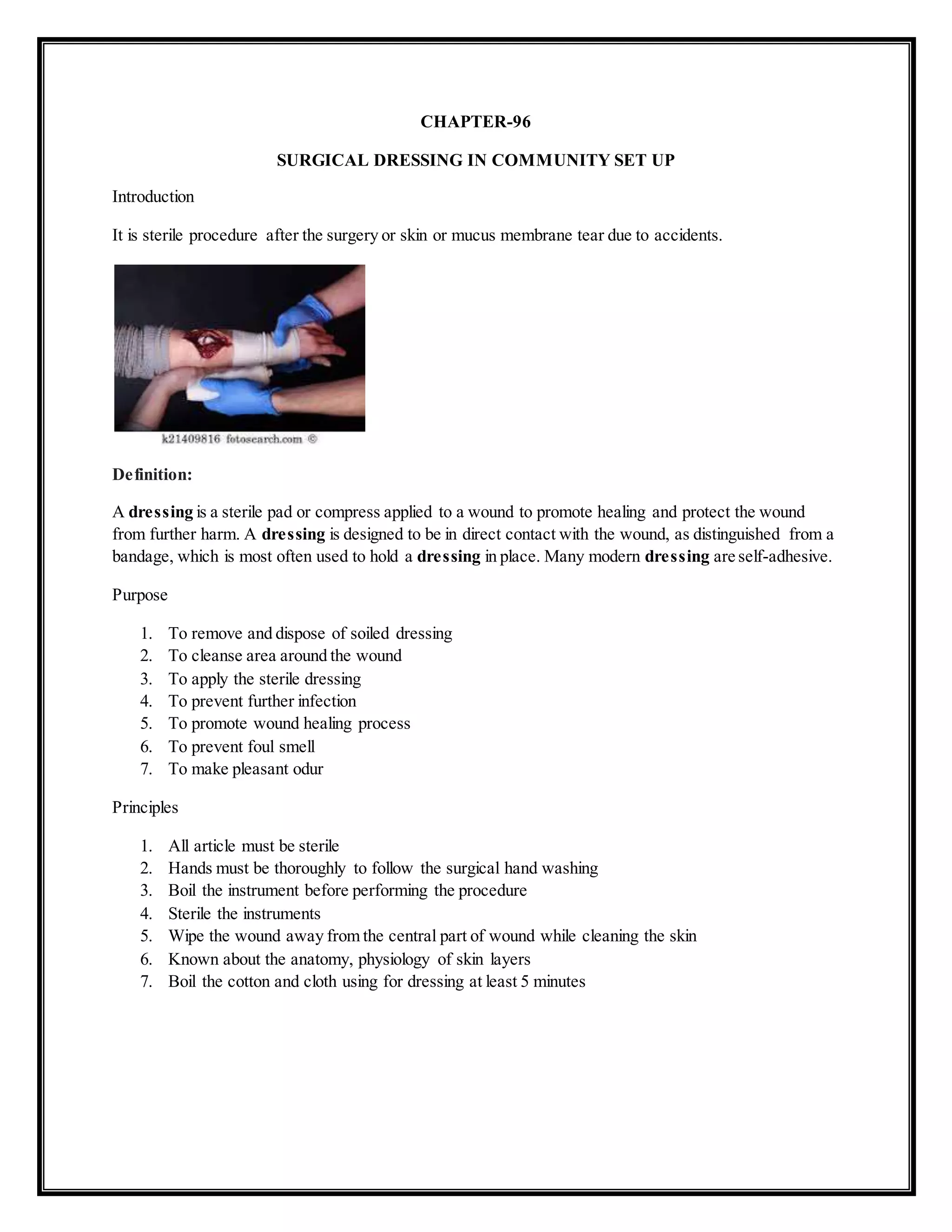
1. A dressing is applied directly to a wound to promote healing and protect it. It is distinguished from a bandage, which holds the dressing in place.
2. The purposes of wound dressing are to control bleeding, absorb exudate, ease pain, and protect newly formed tissue from further harm.
3. Proper wound dressing involves cleaning the area, applying any necessary ointments, covering with sterile gauze or pads, securing with a bandage, and instructing the patient on aftercare.