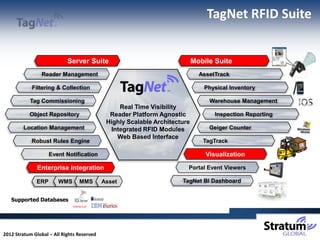
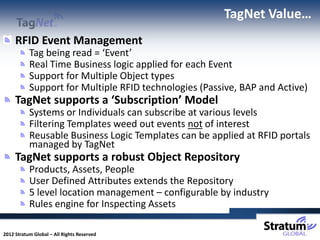
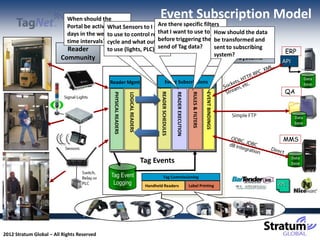
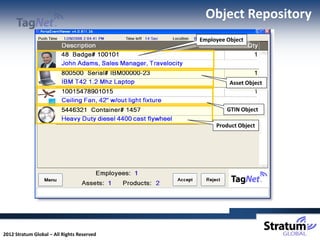
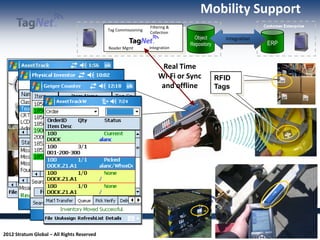
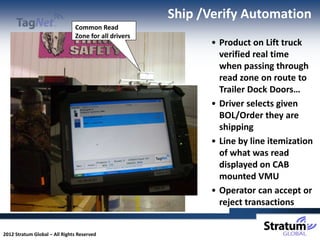
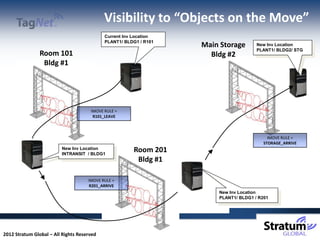
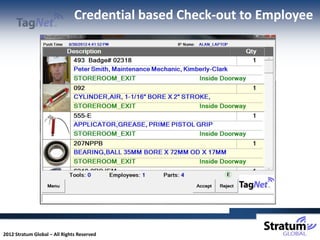
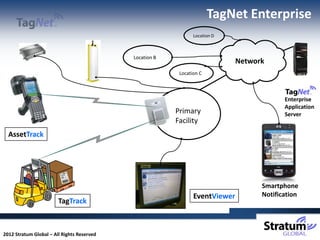
This document provides an overview of RFID technology and its implementations. It discusses how RFID can be used for physical inventory, manufacturing, distribution, inventory control, jobsite asset and worker tracking, IT asset management, and access control. It then describes the TagNet RFID suite which includes reader management, filtering and collection, tag commissioning, warehouse management, and inspection reporting capabilities. Finally, it provides examples of how RFID can provide visibility, automation, and reporting for inventory management, lift trucks, check-out systems, and preventative maintenance.