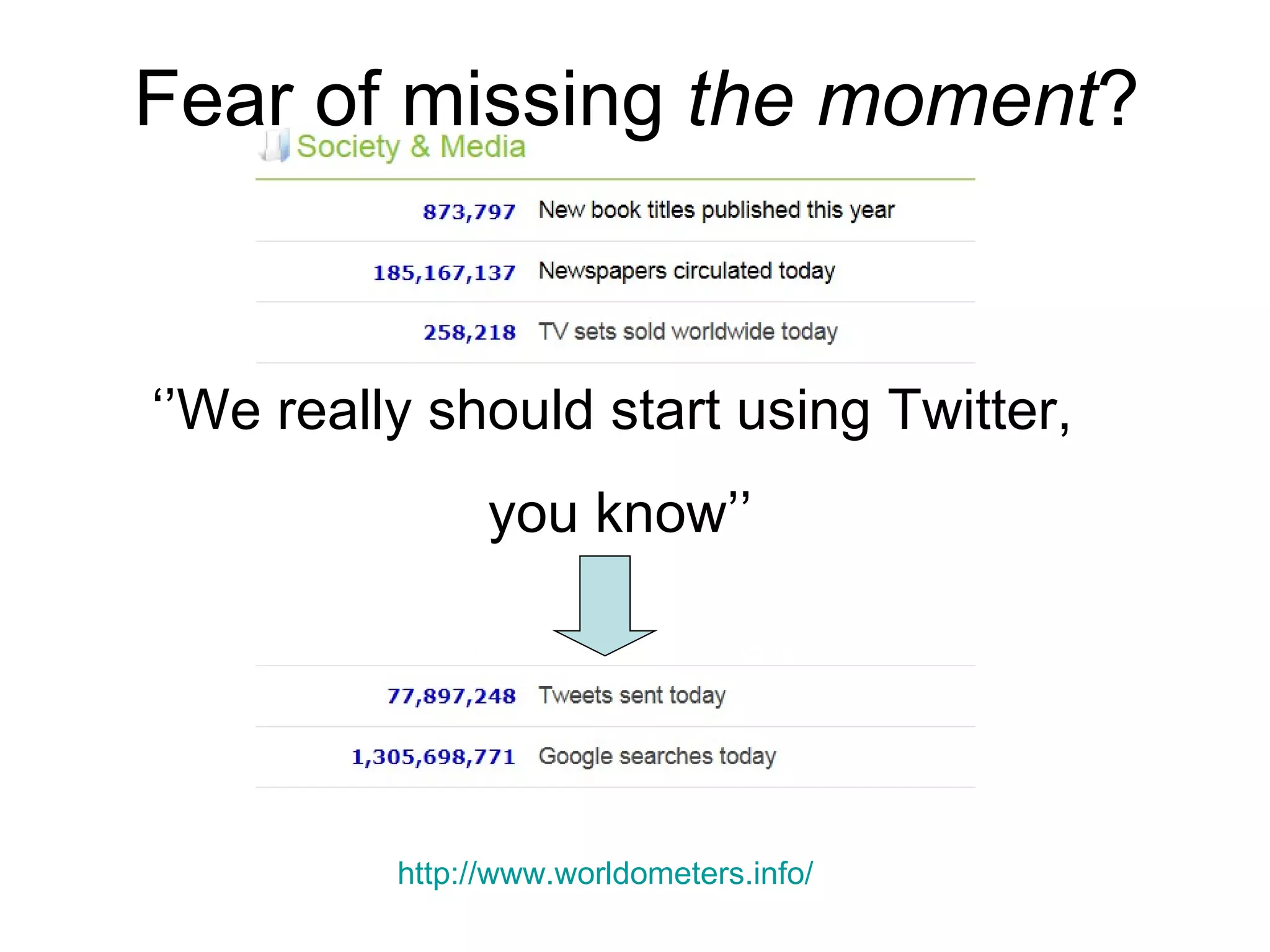
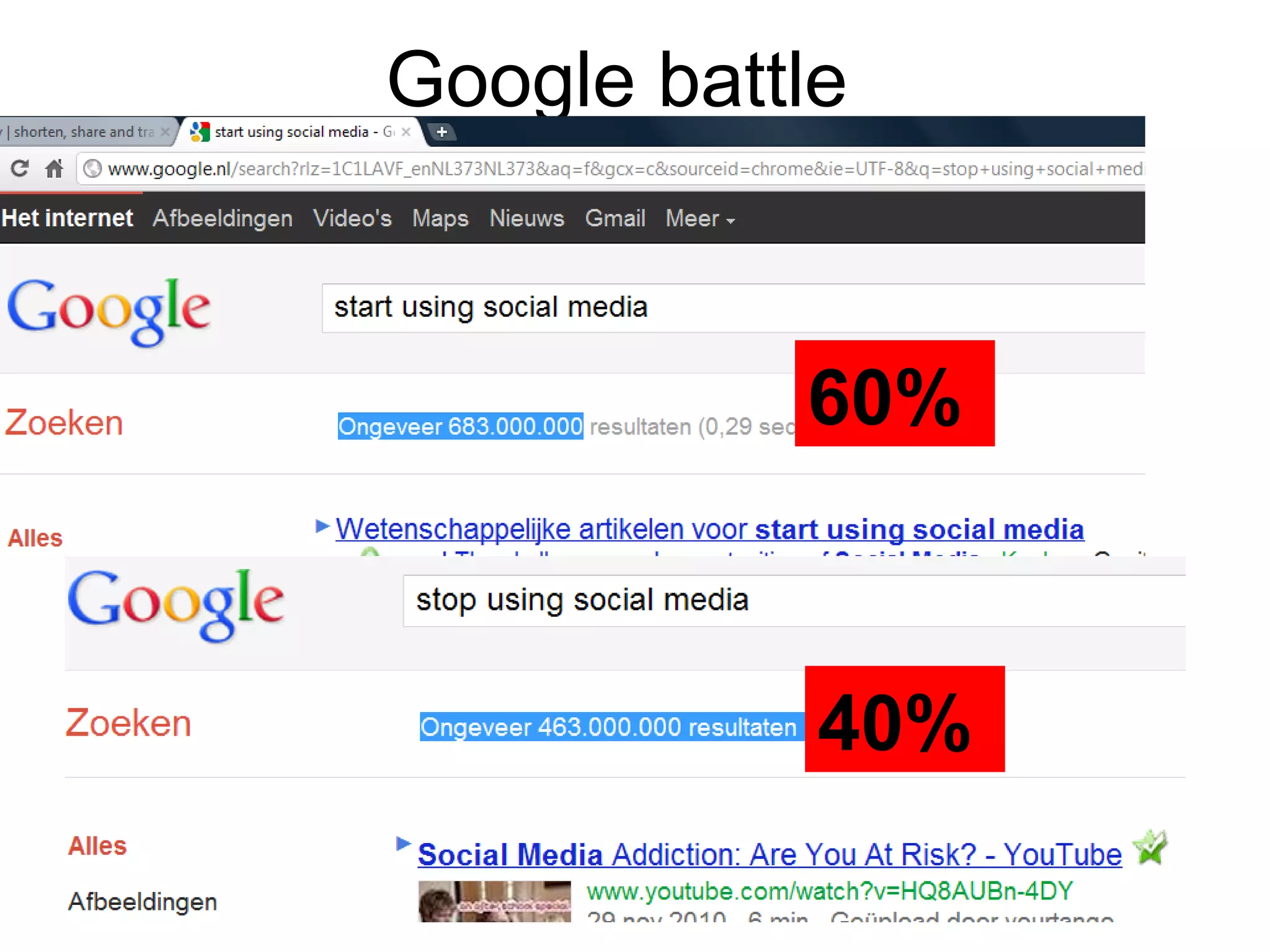
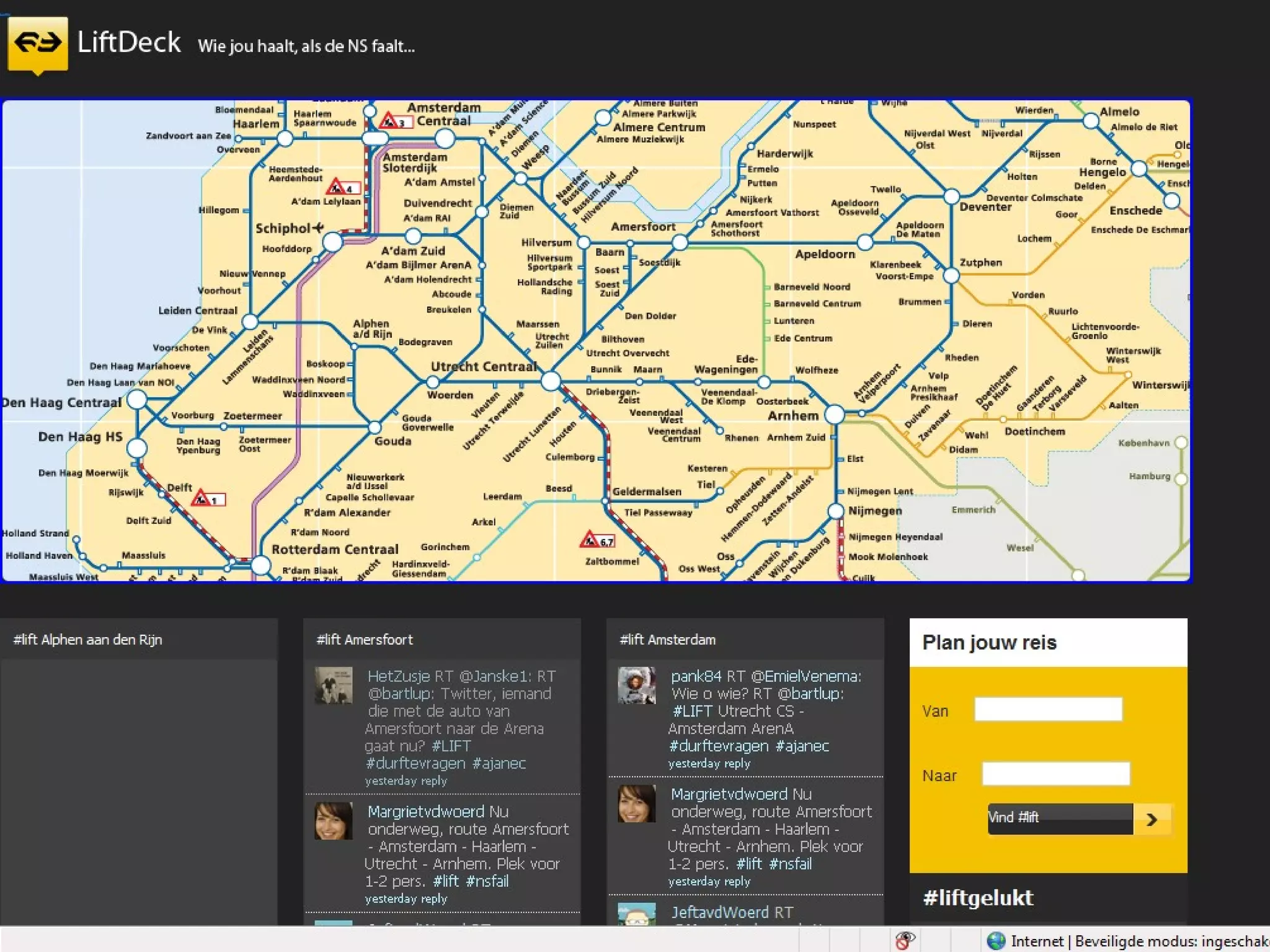
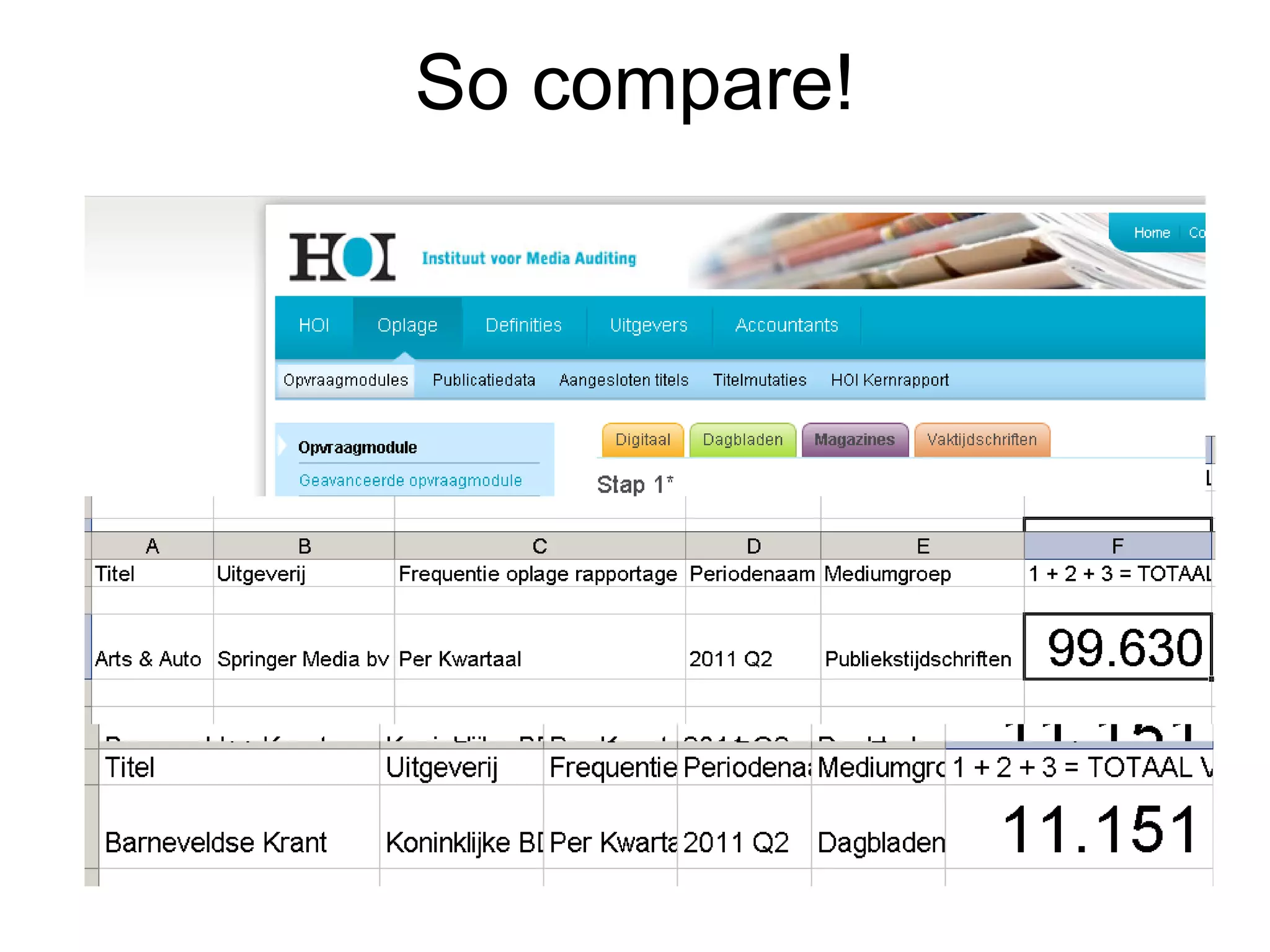
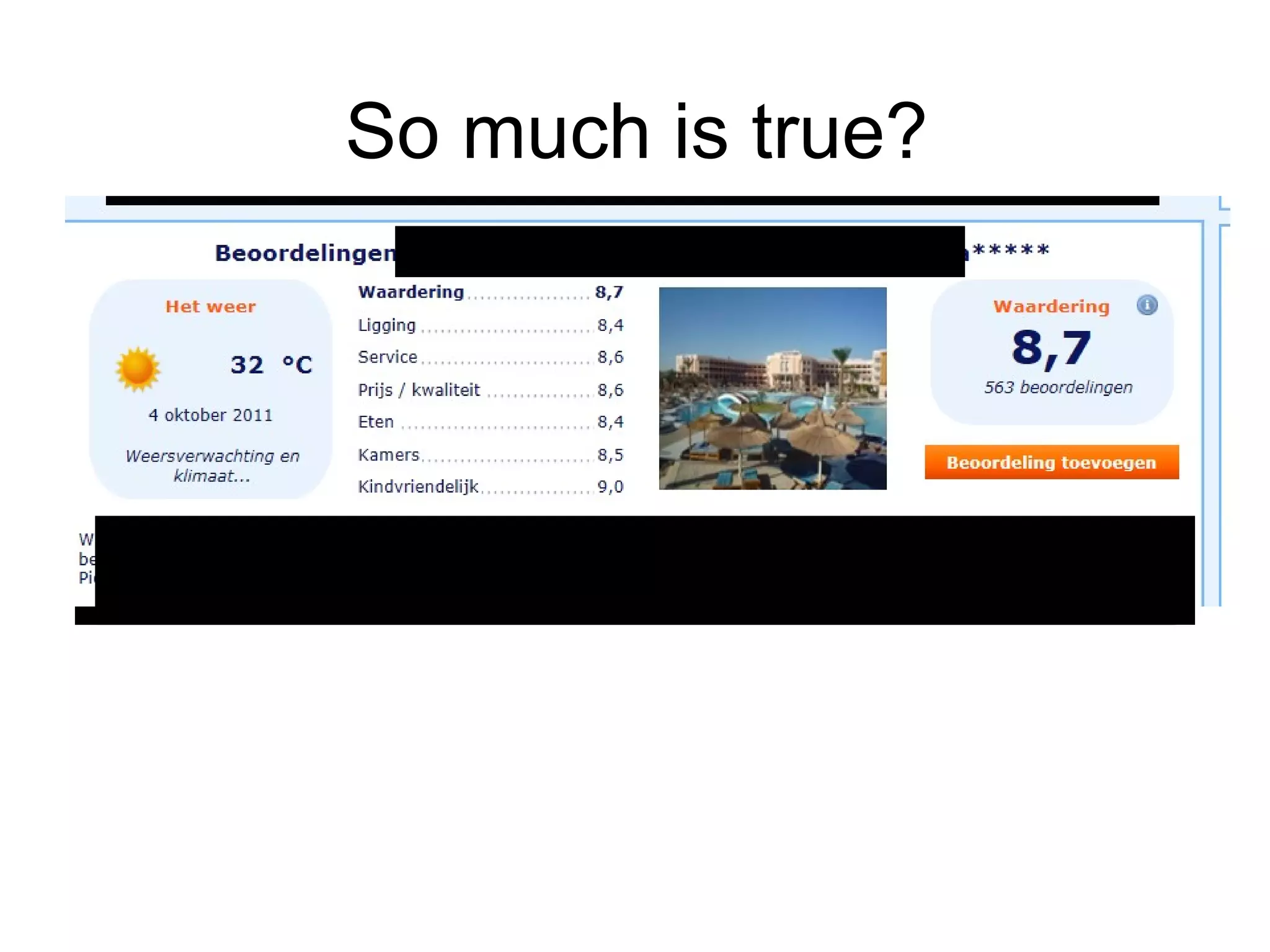
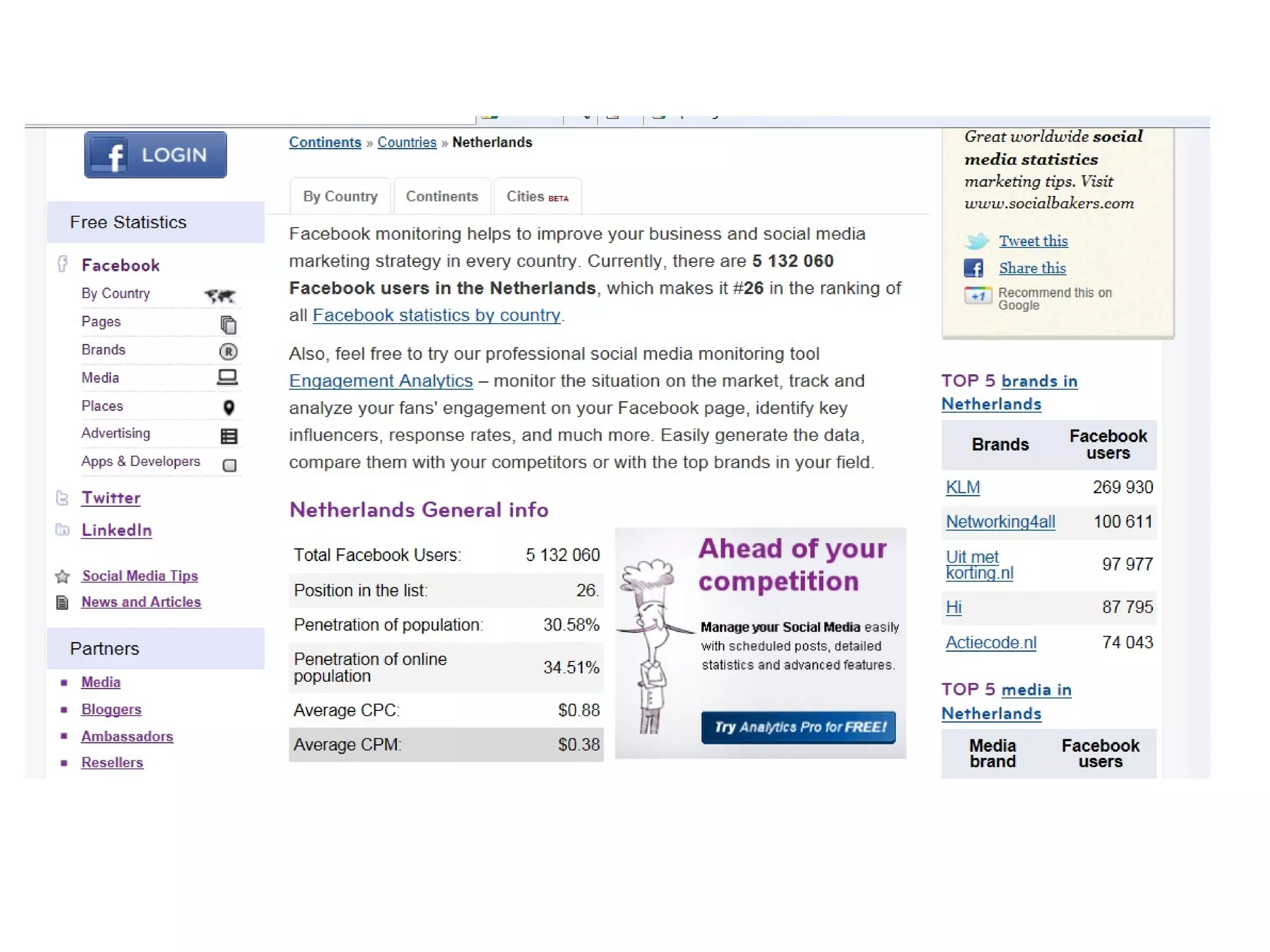
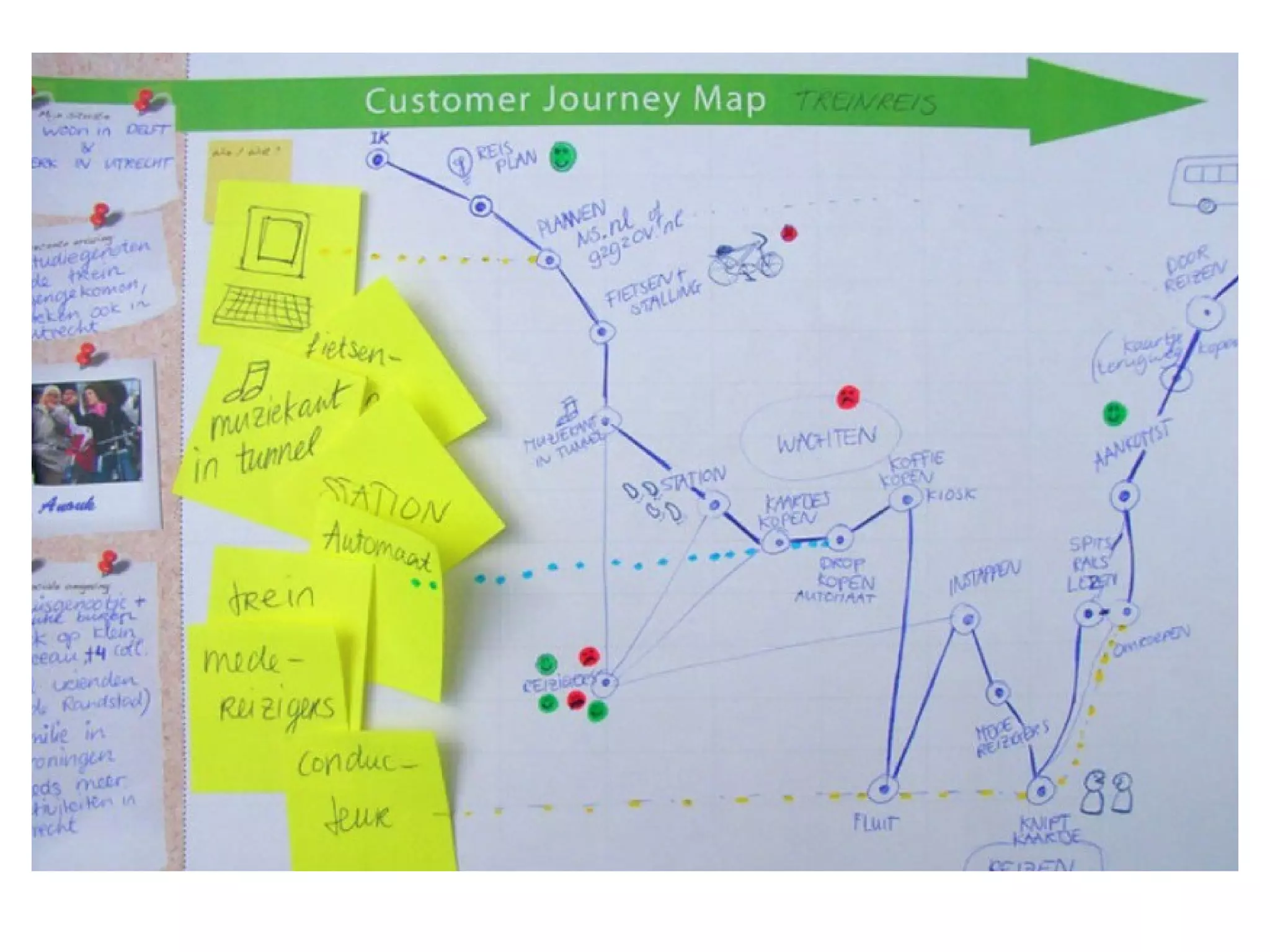
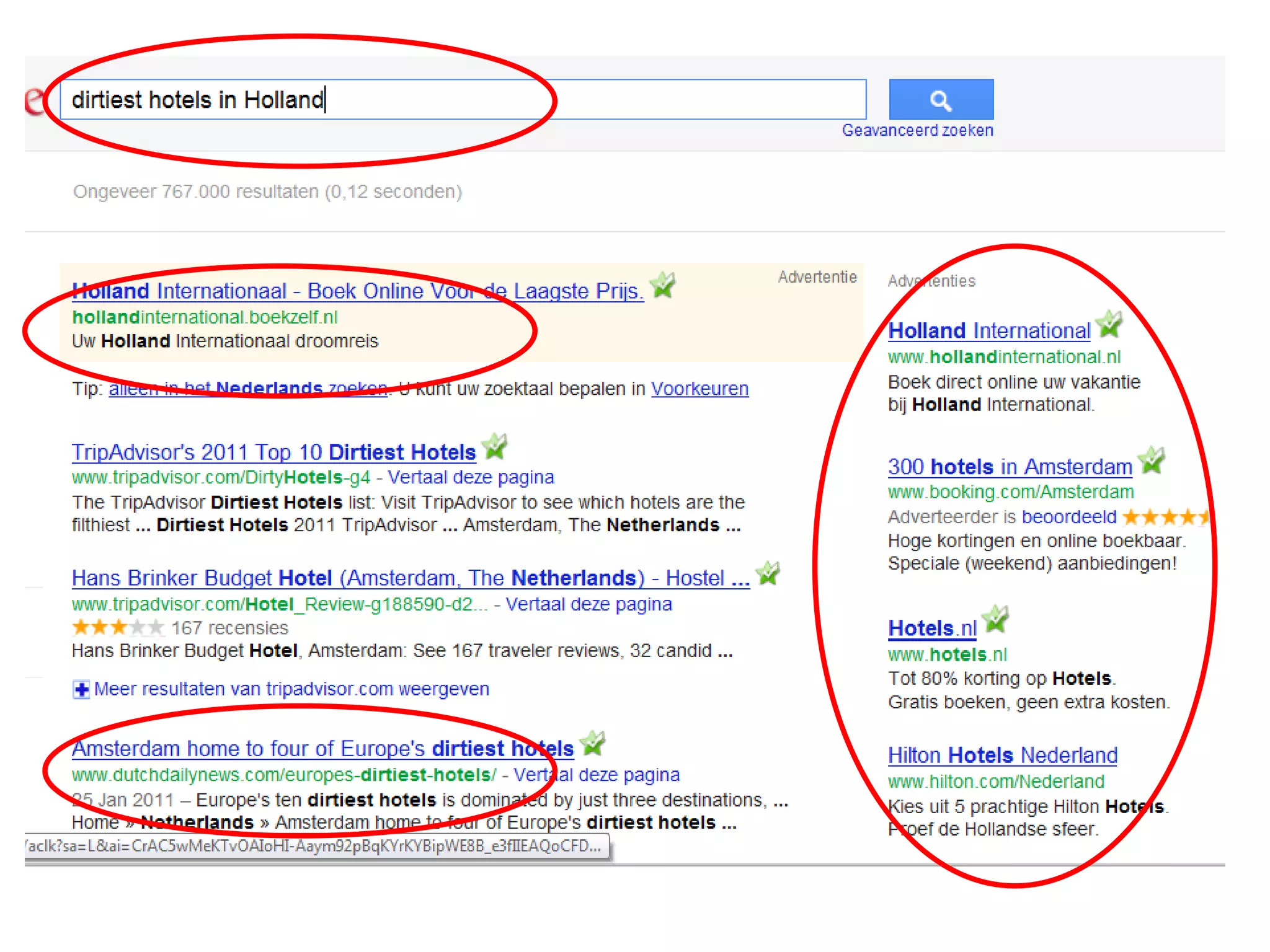
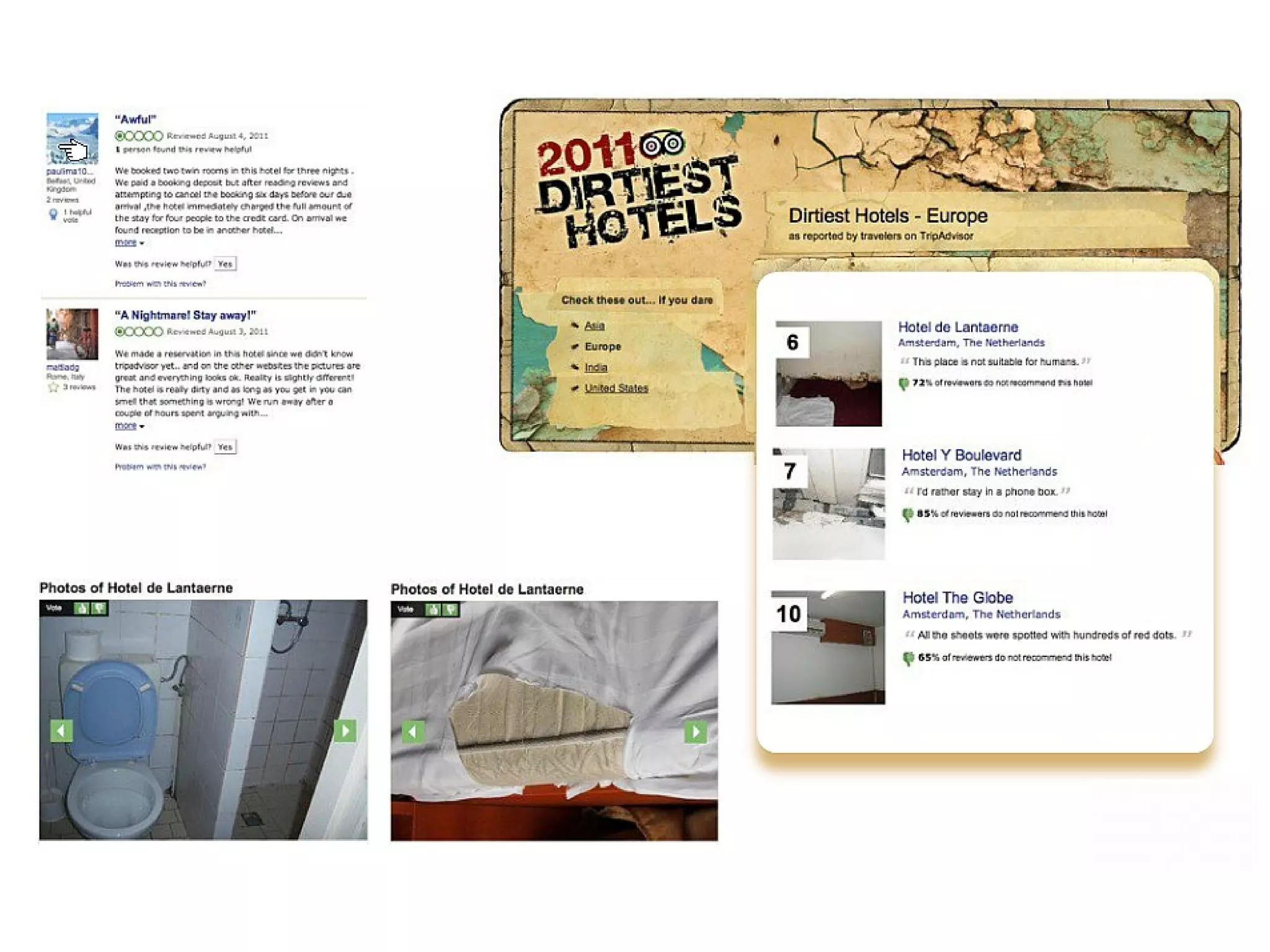
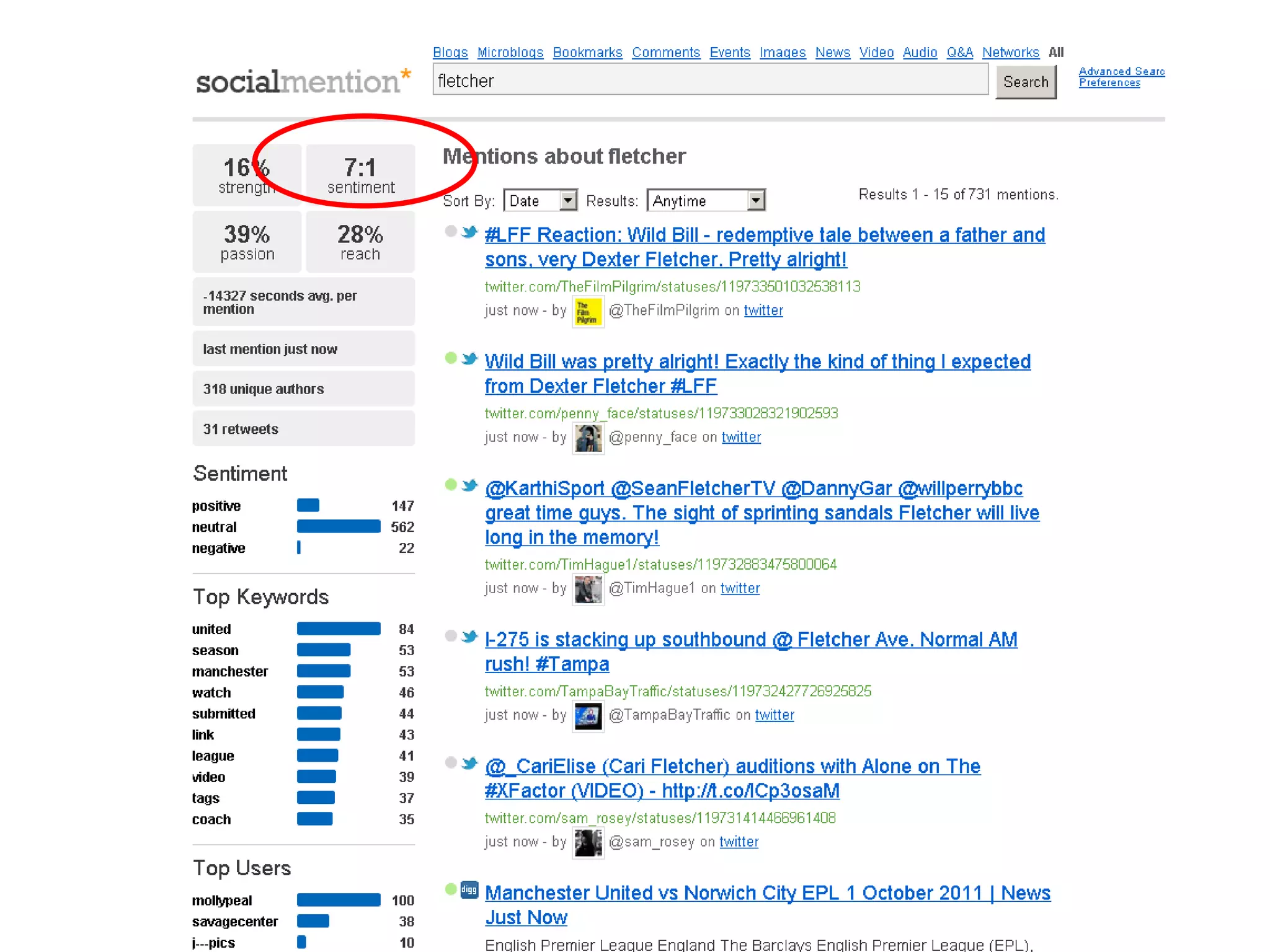
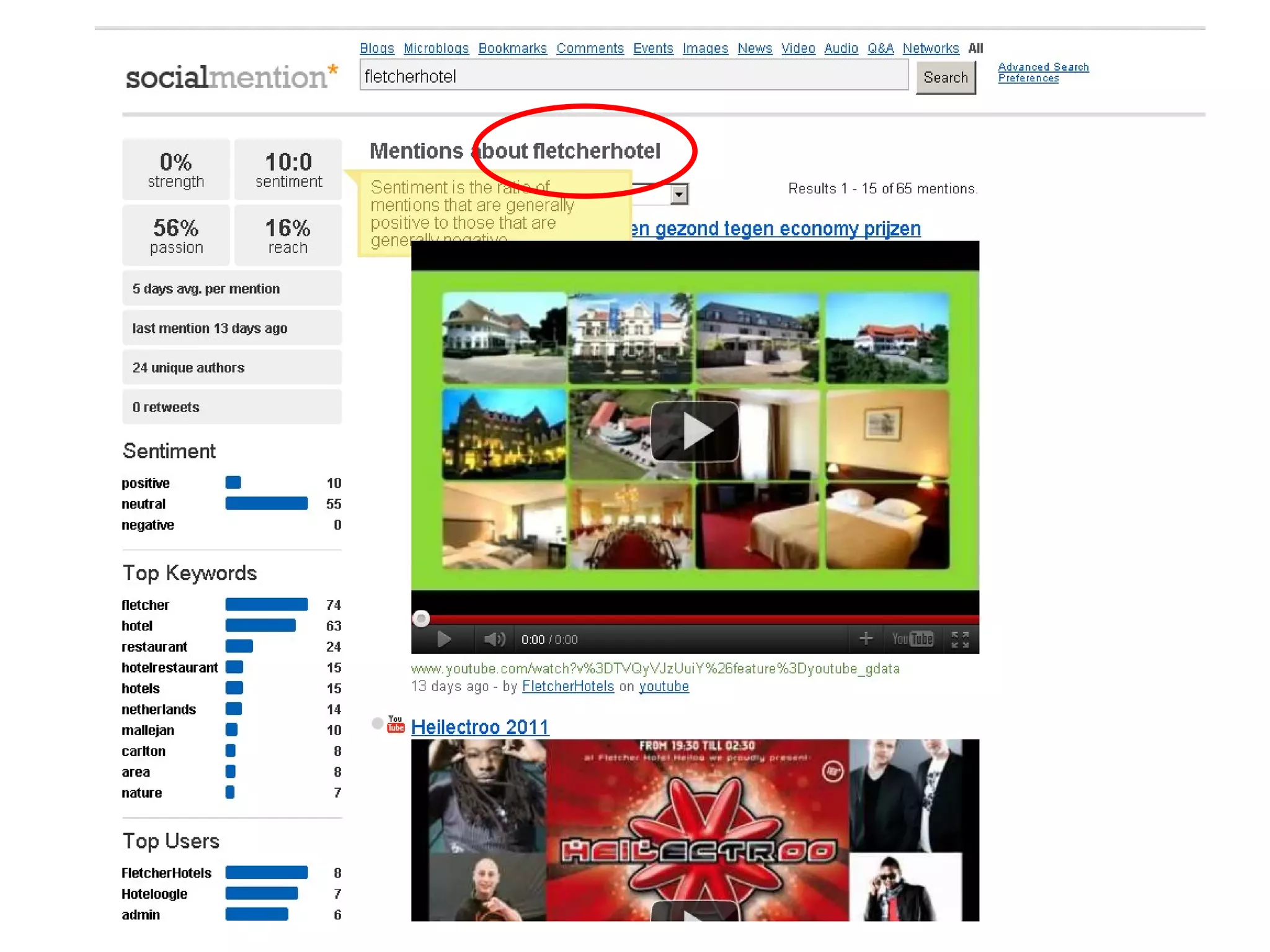
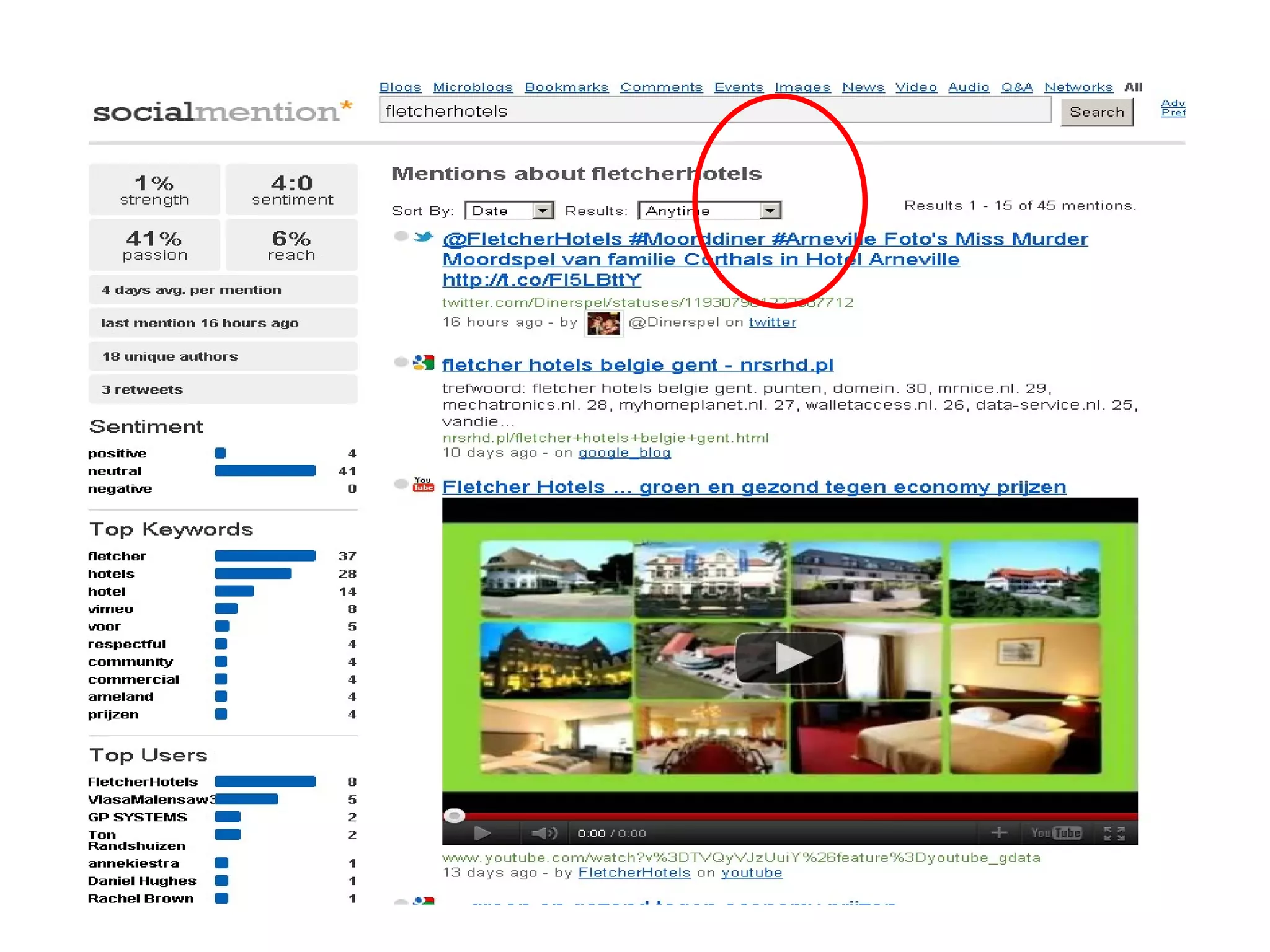
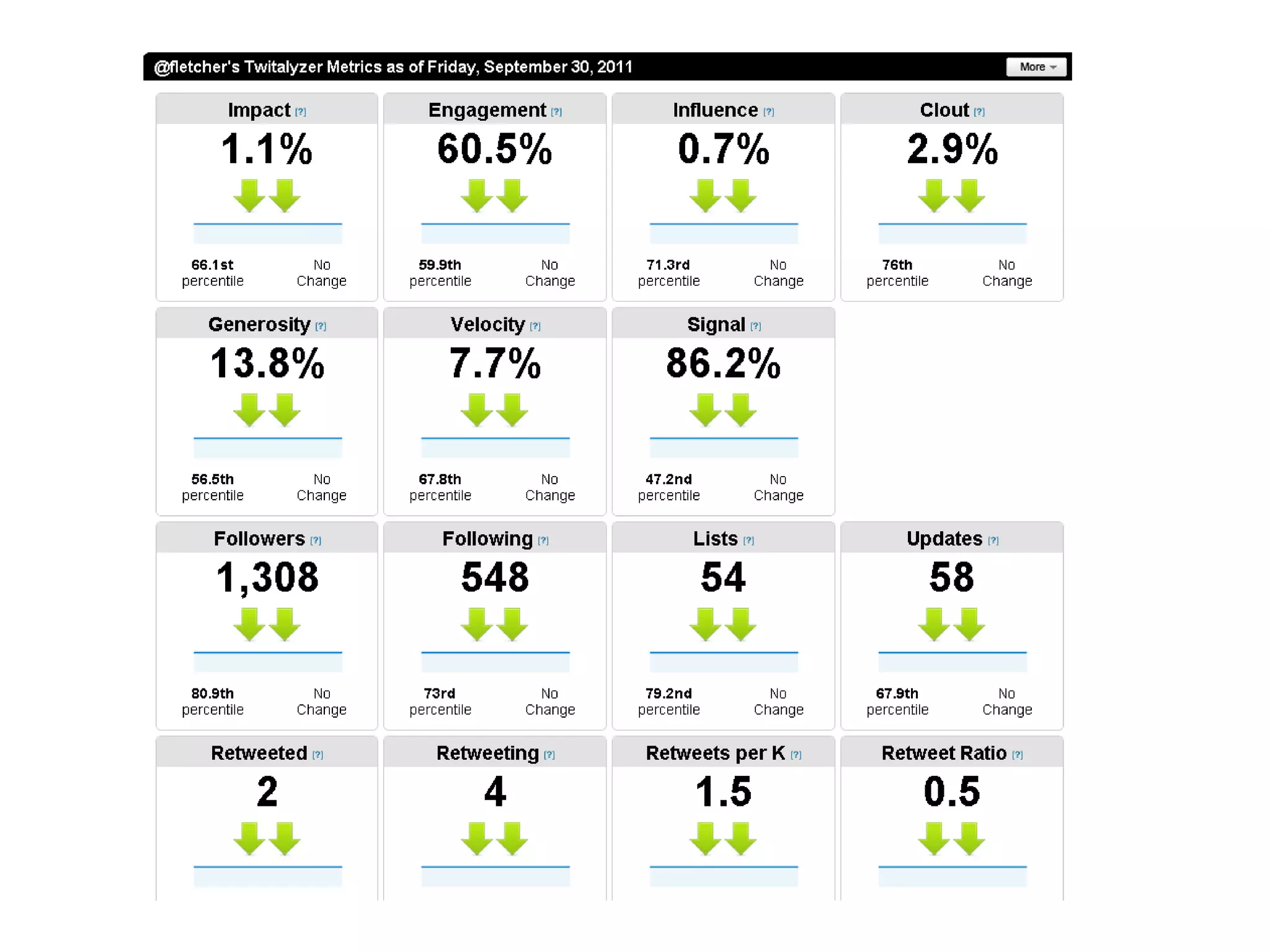
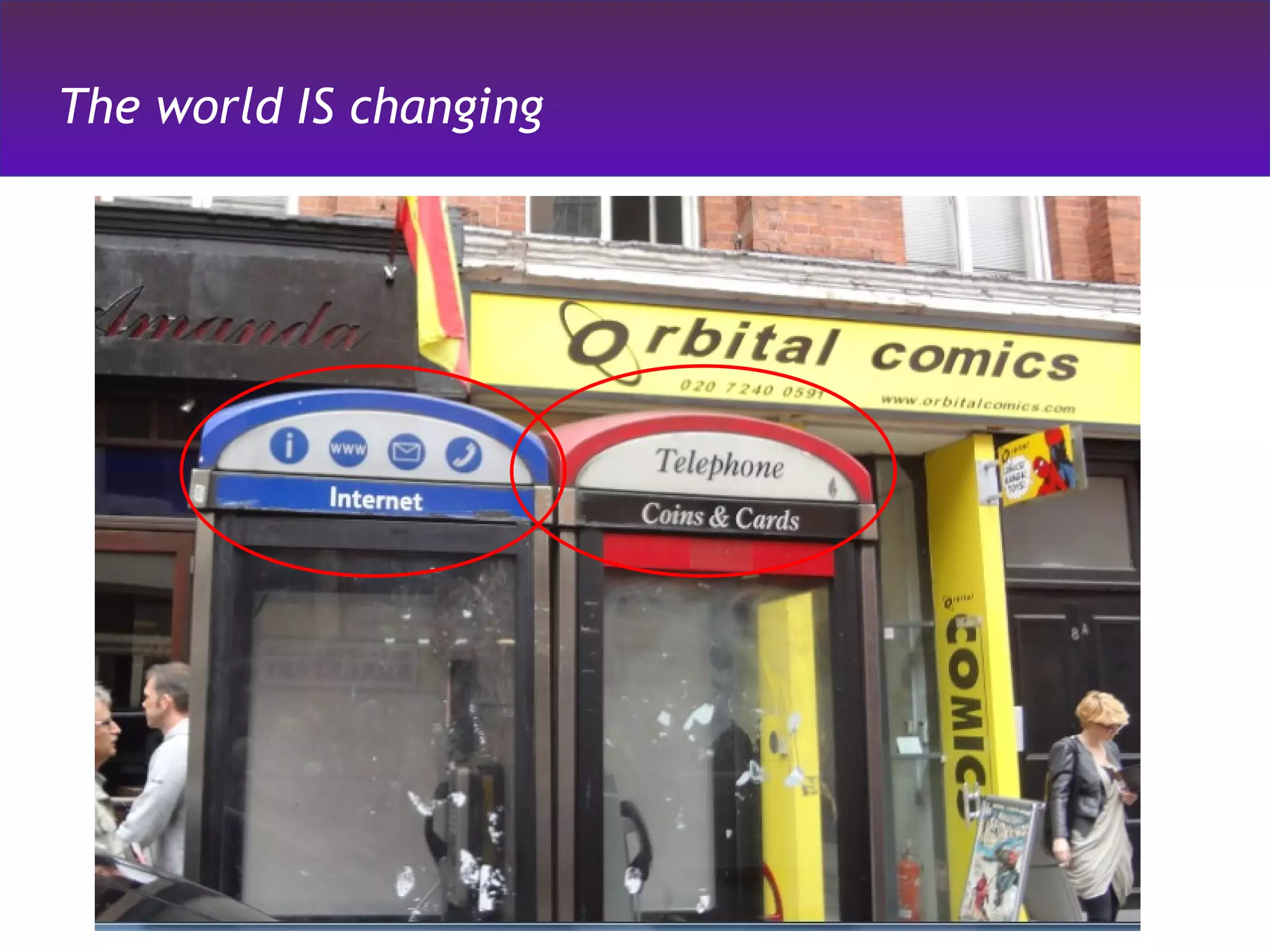
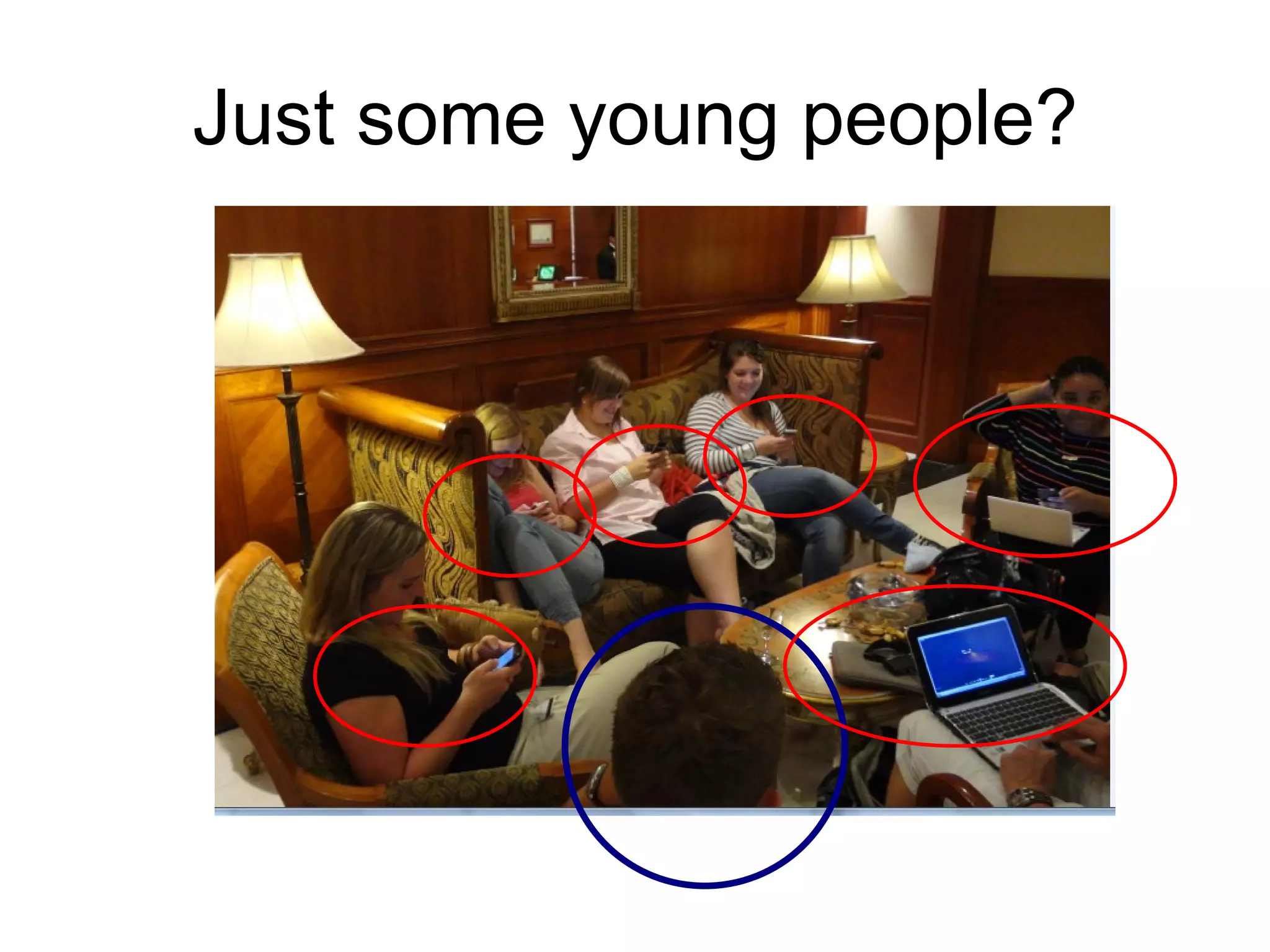
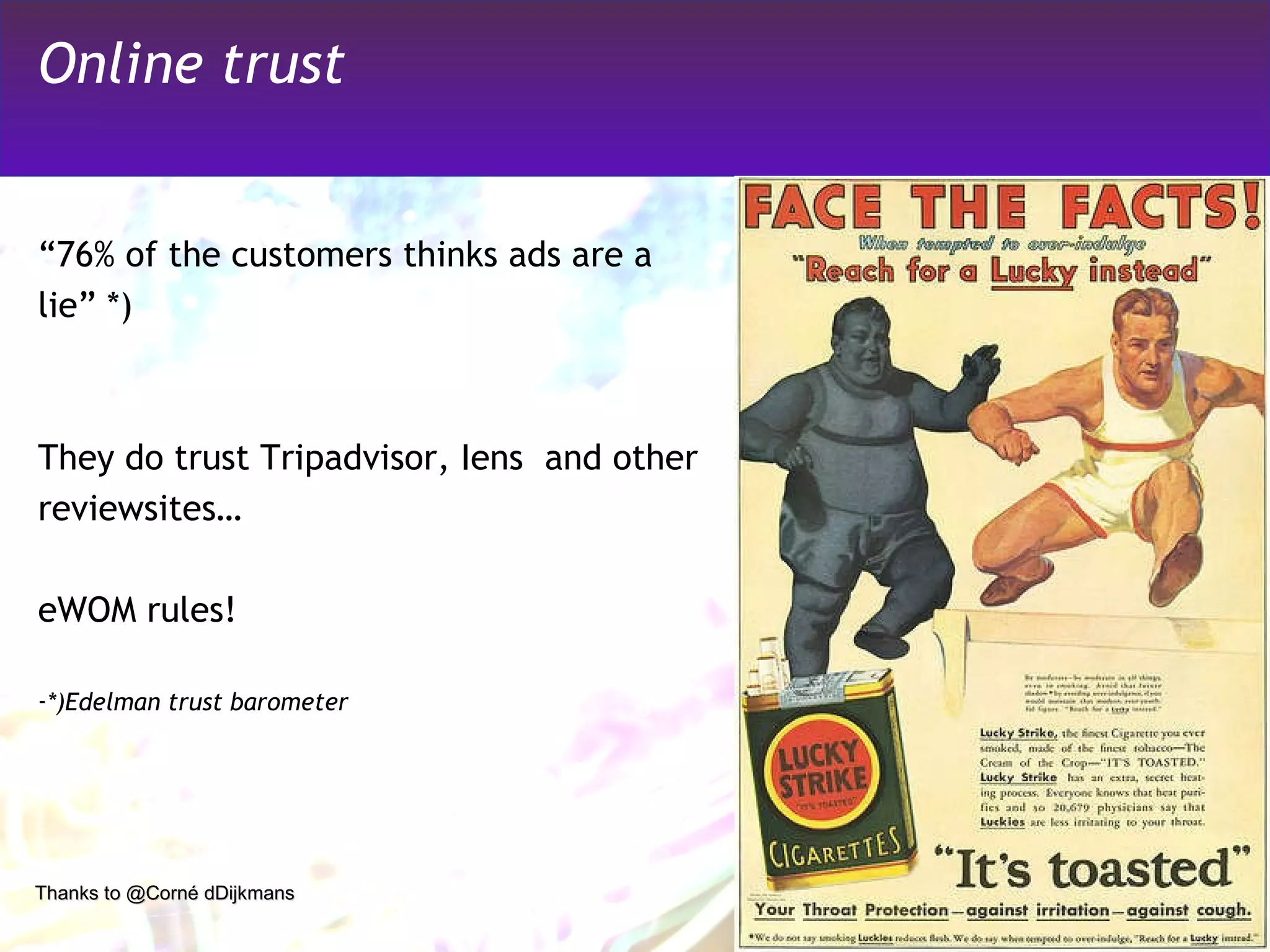
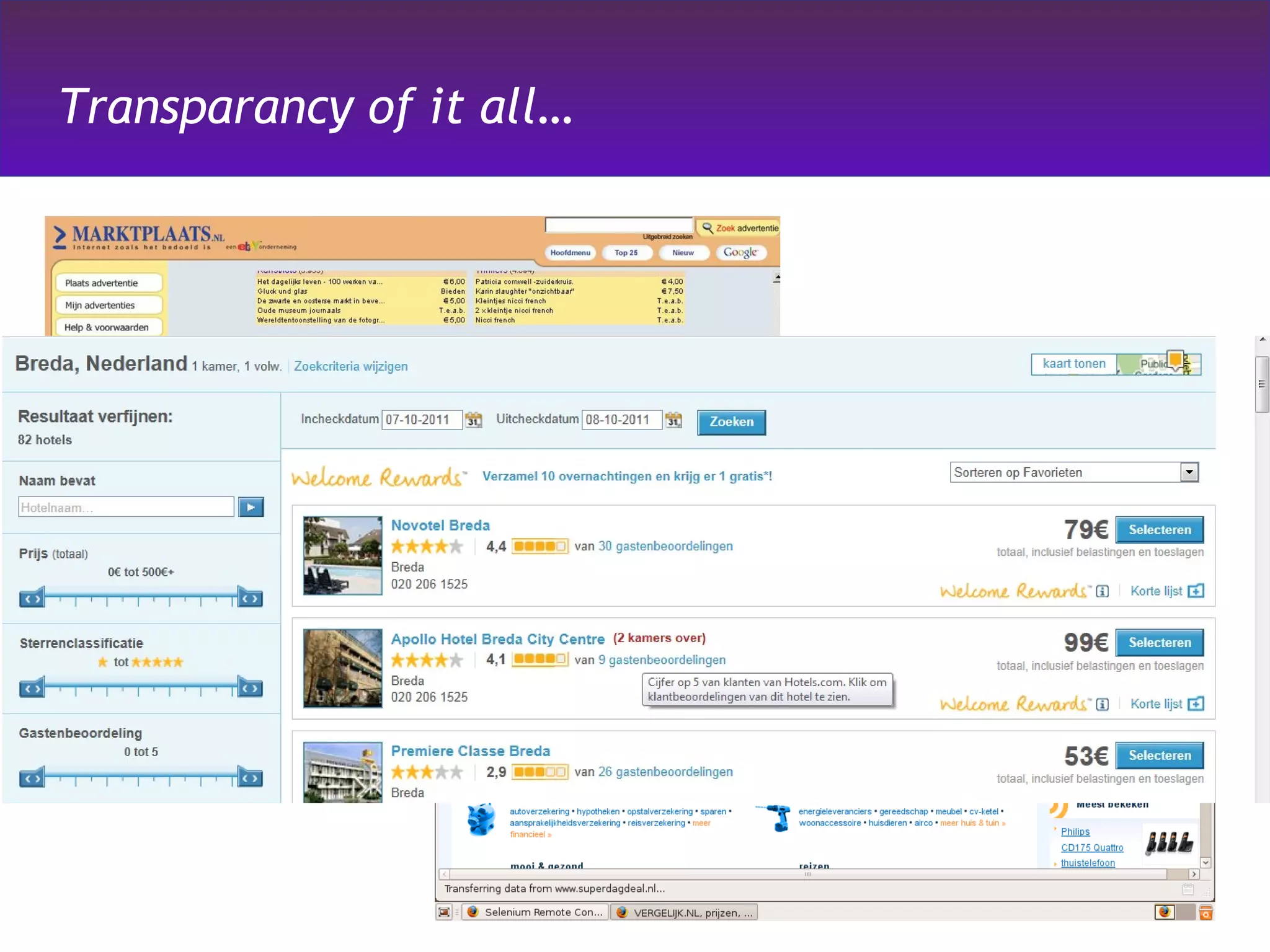
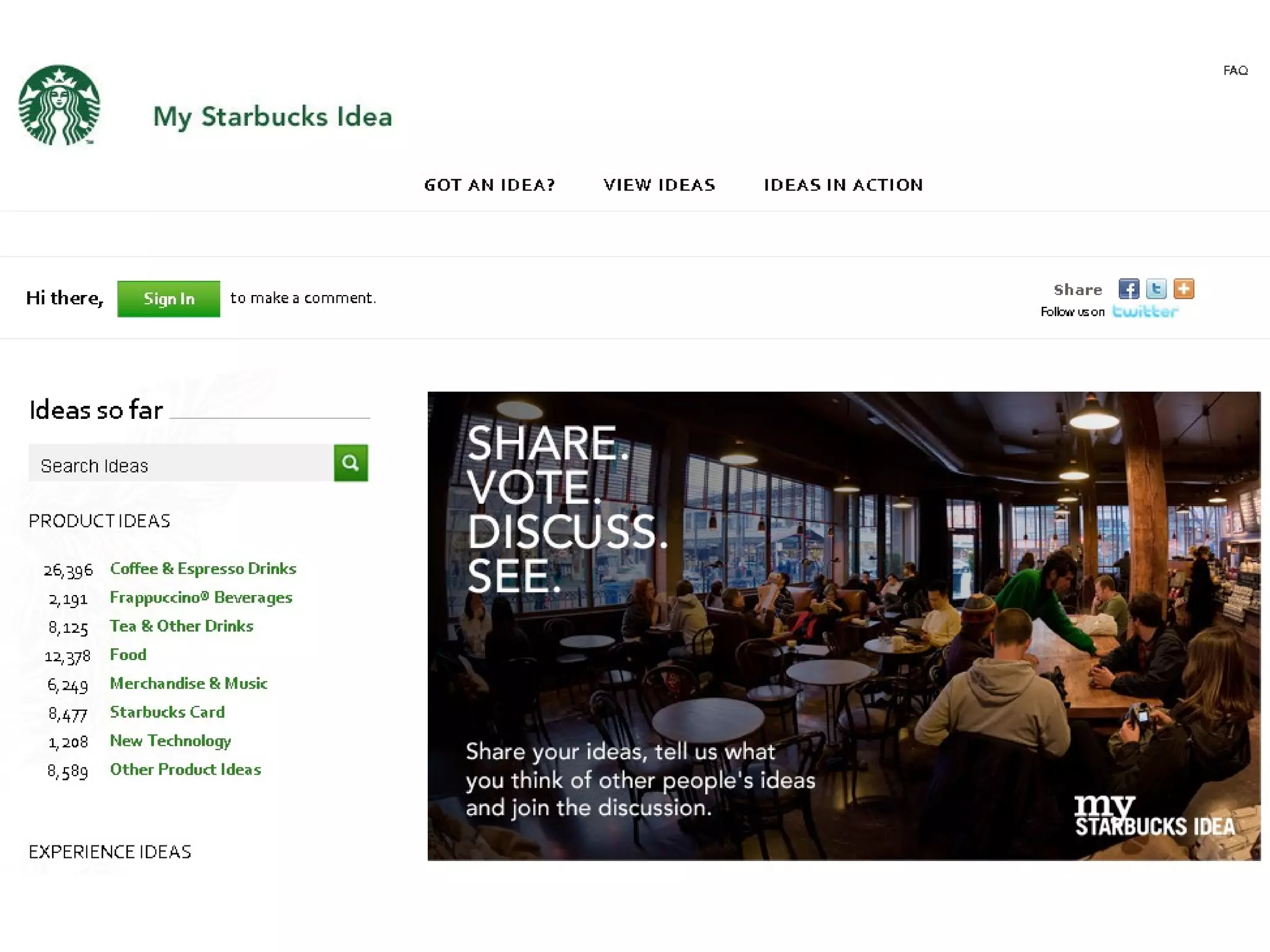
The document outlines reasons to reconsider the use of social media for business, emphasizing the need for understanding metrics, time, and expertise. It points out that social media should align with business goals and suggests listening to customer feedback and competitor actions. The message encourages a careful approach before integrating social media into a business strategy.