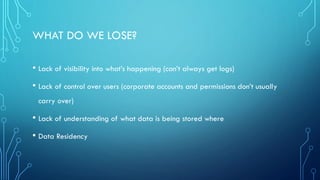
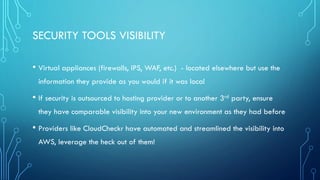
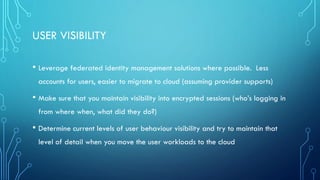
The document outlines the security challenges and considerations companies face when migrating to the cloud, emphasizing the importance of maintaining visibility and managing user access and permissions. It discusses practical steps to enhance security, such as utilizing cloud provider information, logging activities, and employing the Cloud Security Alliance's controls matrix for vendor evaluations. The author calls for organizations to assess their current visibility and security practices to ensure robust protection during and after the transition to cloud services.