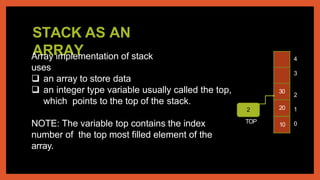
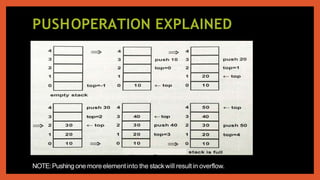
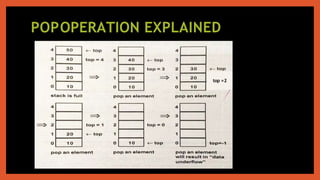
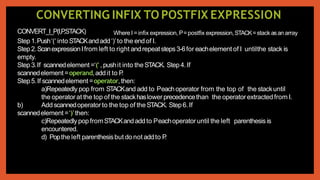
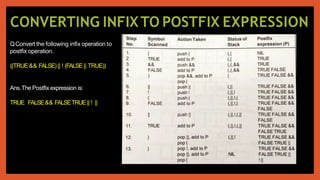
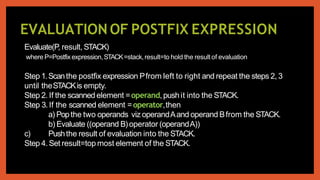
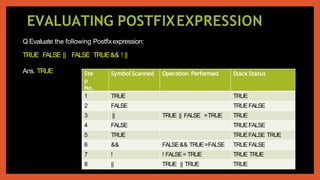
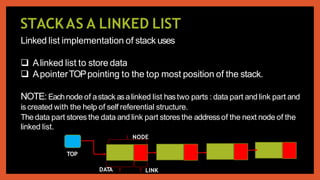
The document discusses stacks and their implementation and operations. It defines a stack as a linear data structure that follows the LIFO principle. Stacks can be implemented using arrays or linked lists. The two main operations on a stack are push and pop. Push adds an element to the top of the stack, while pop removes an element from the top. The document provides examples of these operations and discusses applications of stacks such as converting infix to postfix notation.

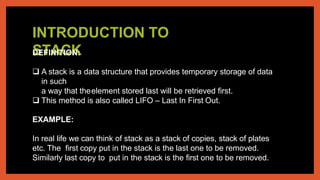

![PROGRAM TO ILLUSTRATE OPERATIONS ON STACK
ASA LINKED LIST
#include<iostream.h>
#include<conio.h>
struct node
{
int roll;
charname[20];
float total;
node *next;
};
classstack
{
node *top;
public :
stack()
{ top=NULL;}
void push();
void pop();
void display();
};
void stack::push()
{
node *temp;
temp=new node;
cout<<"Enter roll :";
cin>>temp->roll;
cout<<"Enter name:";
cin>>temp->name;
cout<<"Enter total :";
cin>>temp->total;
temp->next=top;
top=temp;
}
void stack::pop()
{
if(top!=NULL)
{
node*temp=top;
top=top->next;
cout<<temp->roll<<temp-
>name<<temp->total
<<"deleted";
delete temp;
}
else
cout<<"Stack empty";
}
void stack::display()
{
node *temp=top;
while(temp!=NULL)
{
cout<<temp->roll<<temp-
>name<<temp->total<<" ";
temp=temp->next;
} }
void main()
{ stack st;
char ch;
do
{ cout<<"stack
optionsnPpush
nO PopnD
Display nQquit";
cin>>ch;
switch(ch)
{ case'P':
st.push();break;
case'O':
st.pop();break;
case'D':
st.display();break;
}
}while(ch!='Q');
}](https://image.slidesharecdn.com/stackdatastructure-210915003350/85/Stack-data-structure-18-320.jpg)
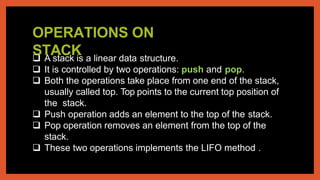
![PROGRAM TO ILLUSTRATE OPERATIONS ON STACK
AS A LINKED LIST :Explanation
struct node
{
int roll;
charname[20];
float total;
node *next;
};
Self Referential Structure:Theseare specialstructures which
contains pointers tothemselves.
Here, next is apointer of type node itself.
Self Referential structures are needed to create Linked Lists.
classstack
{
node*top;
public :
stack()
{ top=NULL;}
void push();
void pop();
void display();
};
classstack: It contains pointerTOPwhich will point to the top
of thestack.
Theconstructor function initializesTOPto NULL.](https://image.slidesharecdn.com/stackdatastructure-210915003350/85/Stack-data-structure-19-320.jpg)