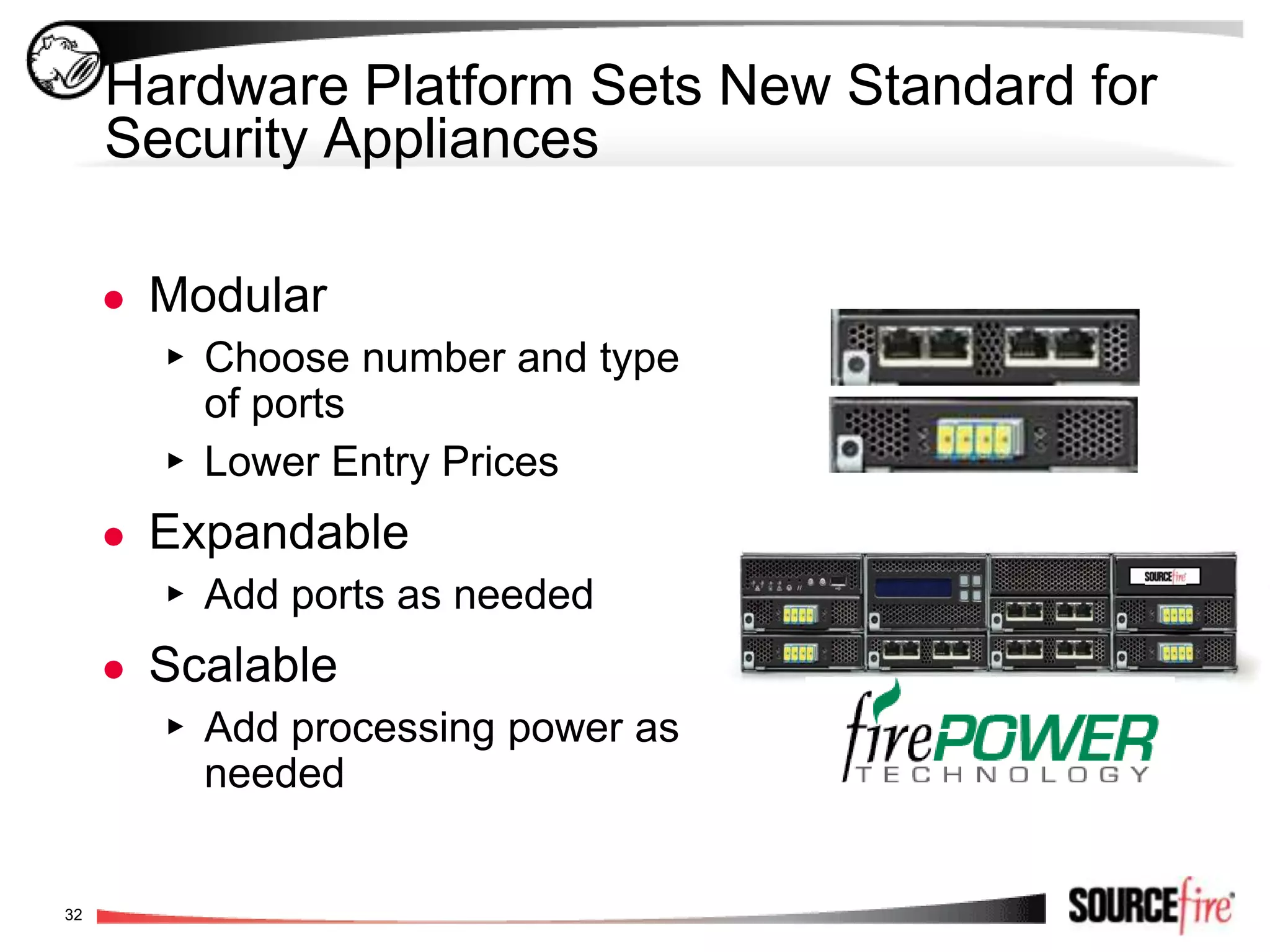
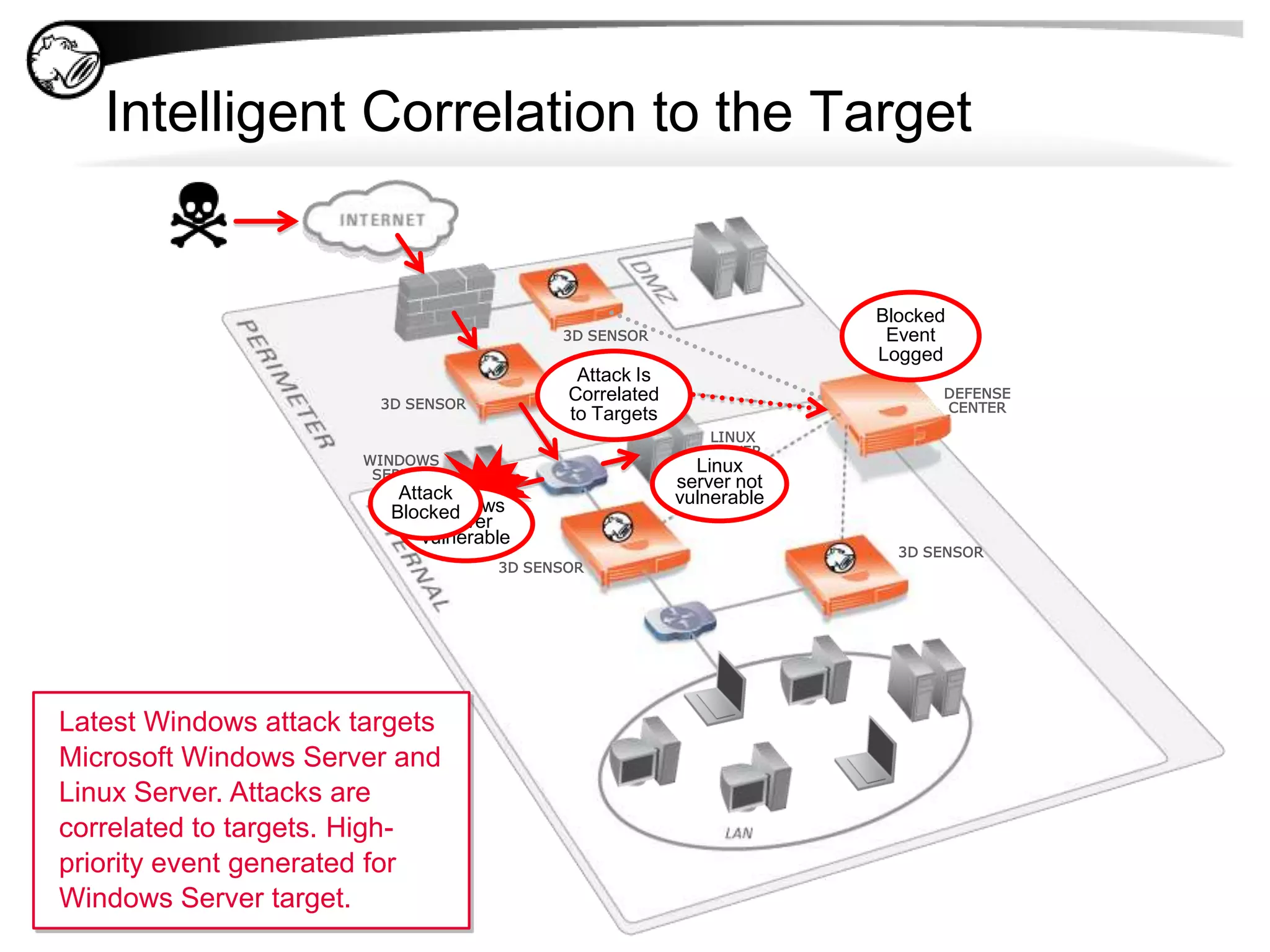
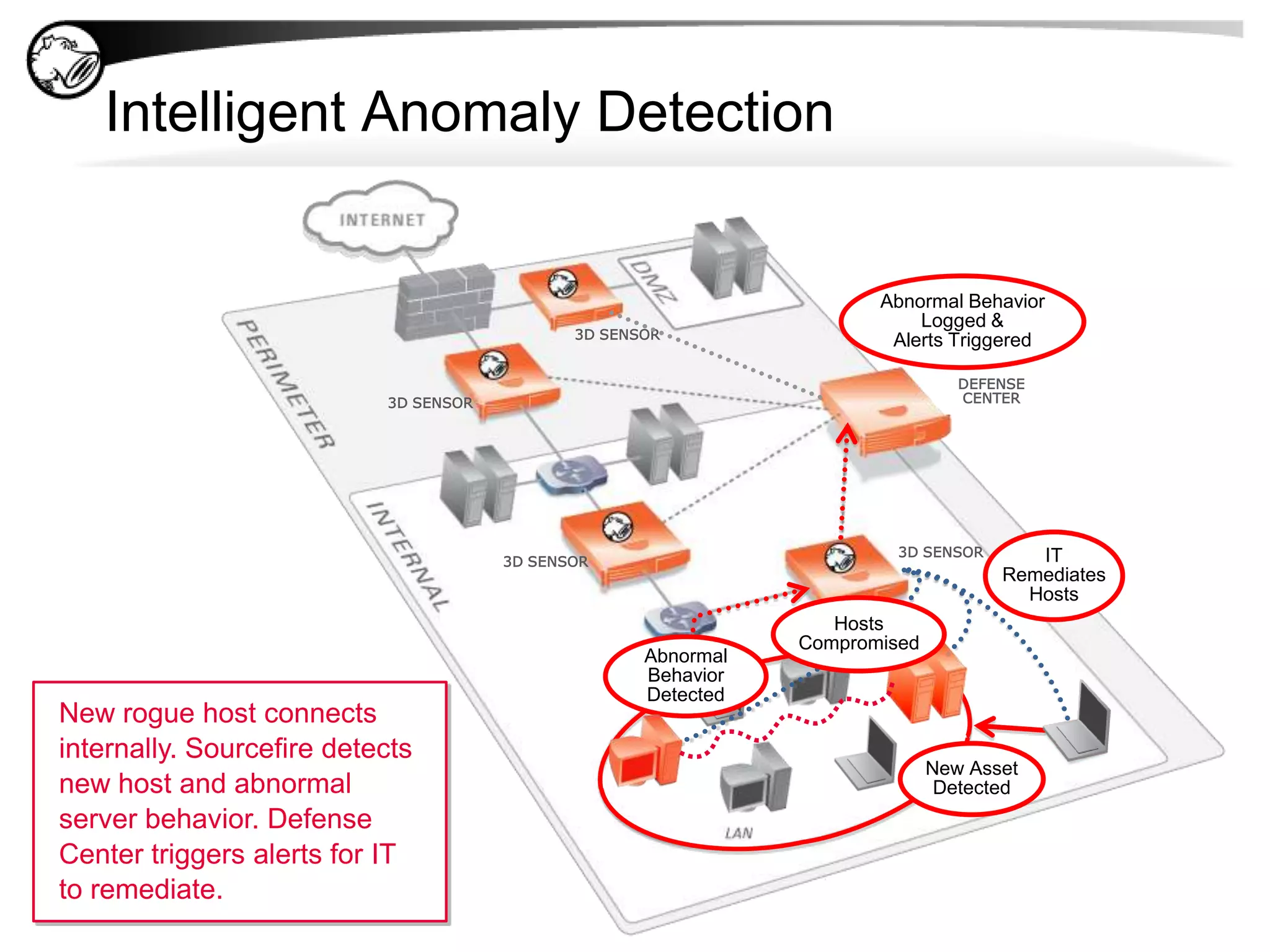
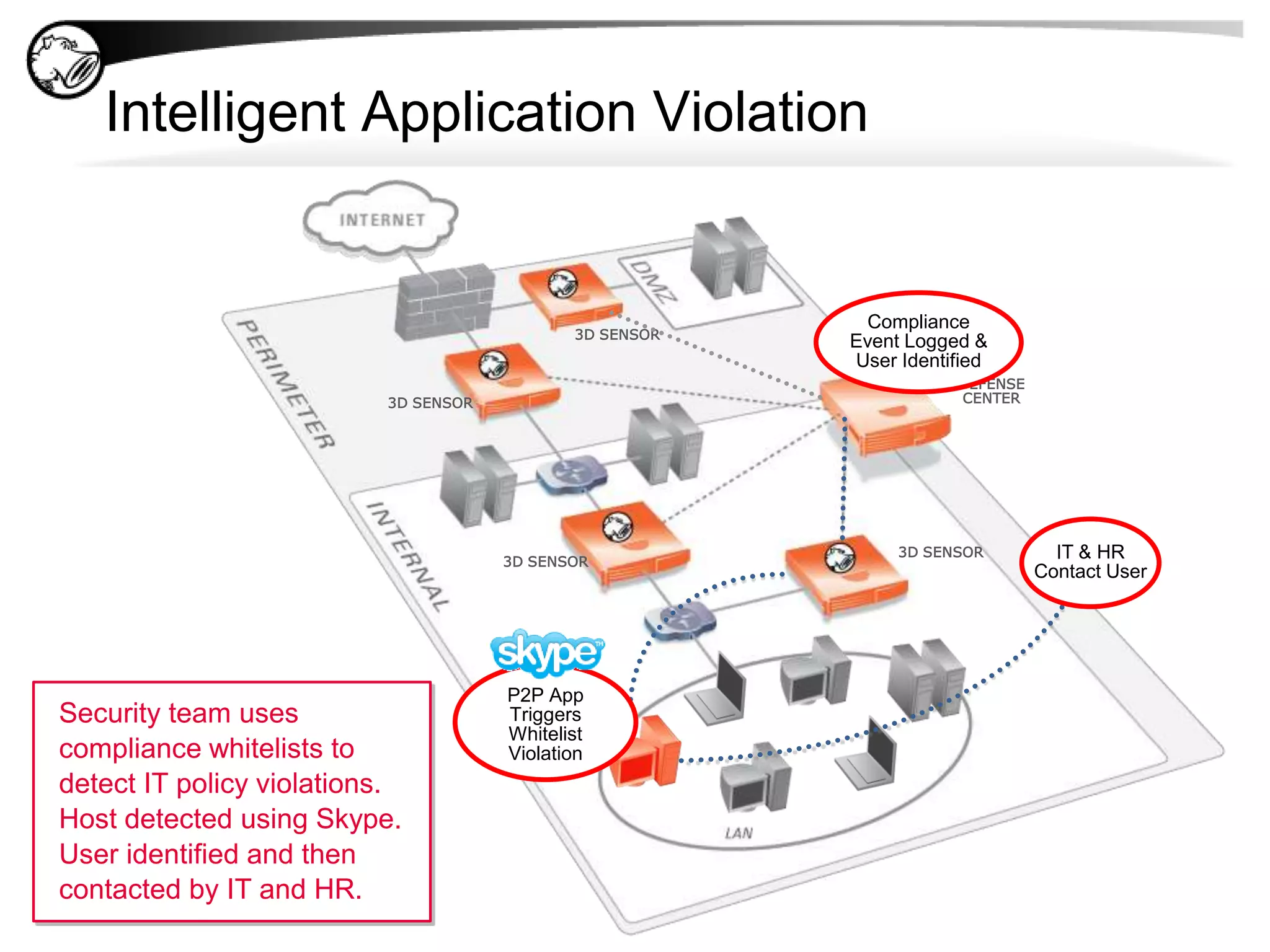
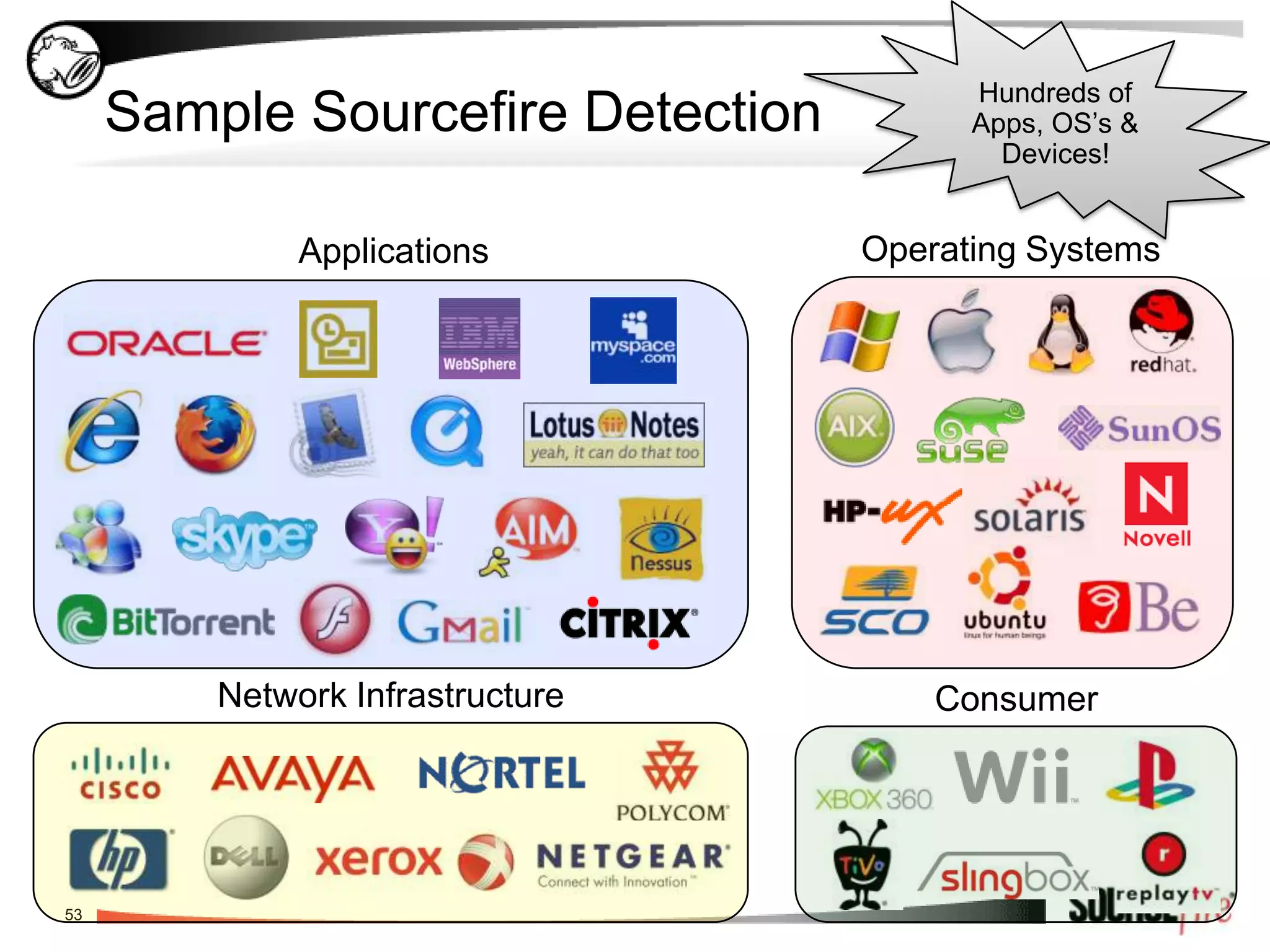
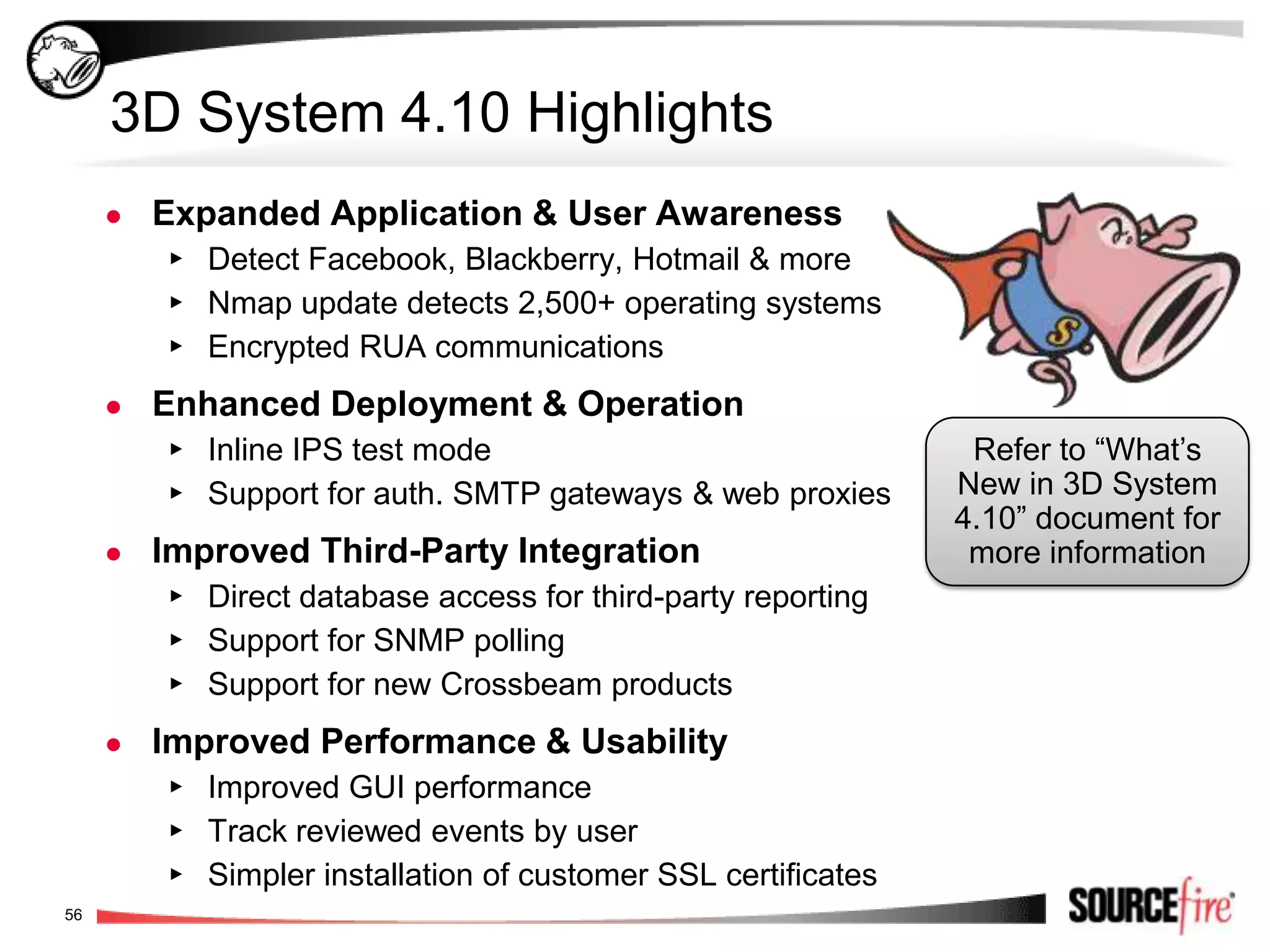
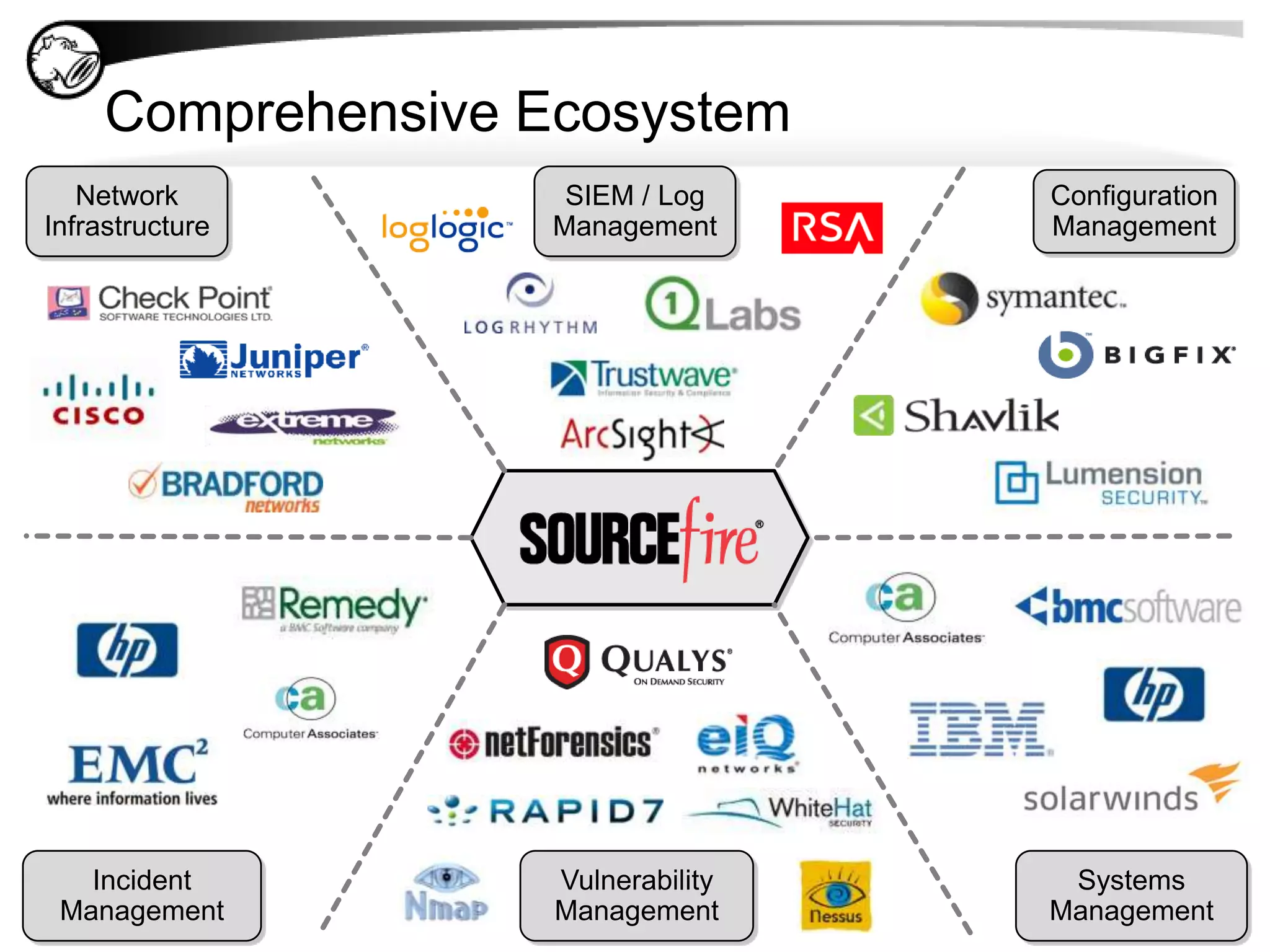
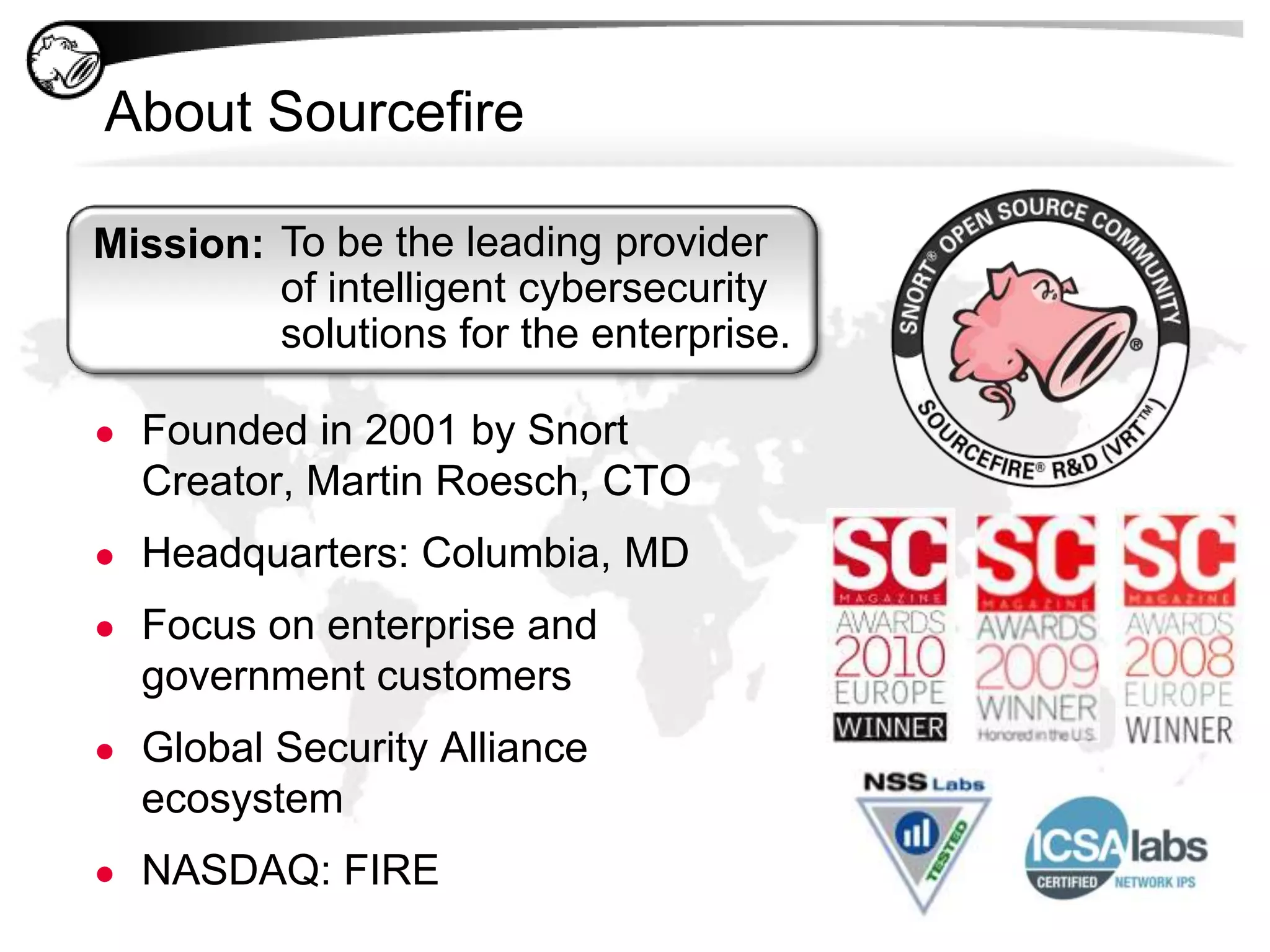
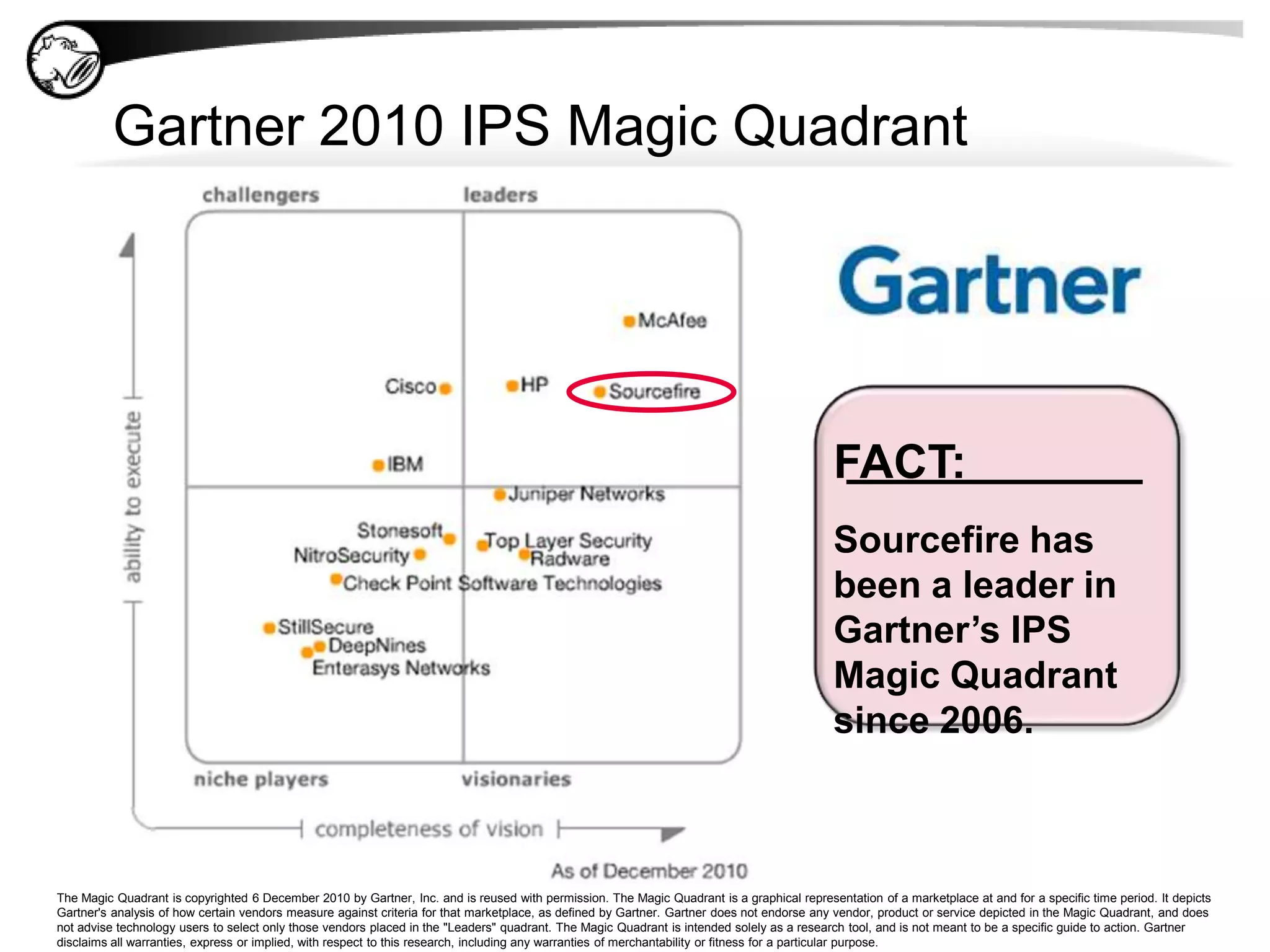
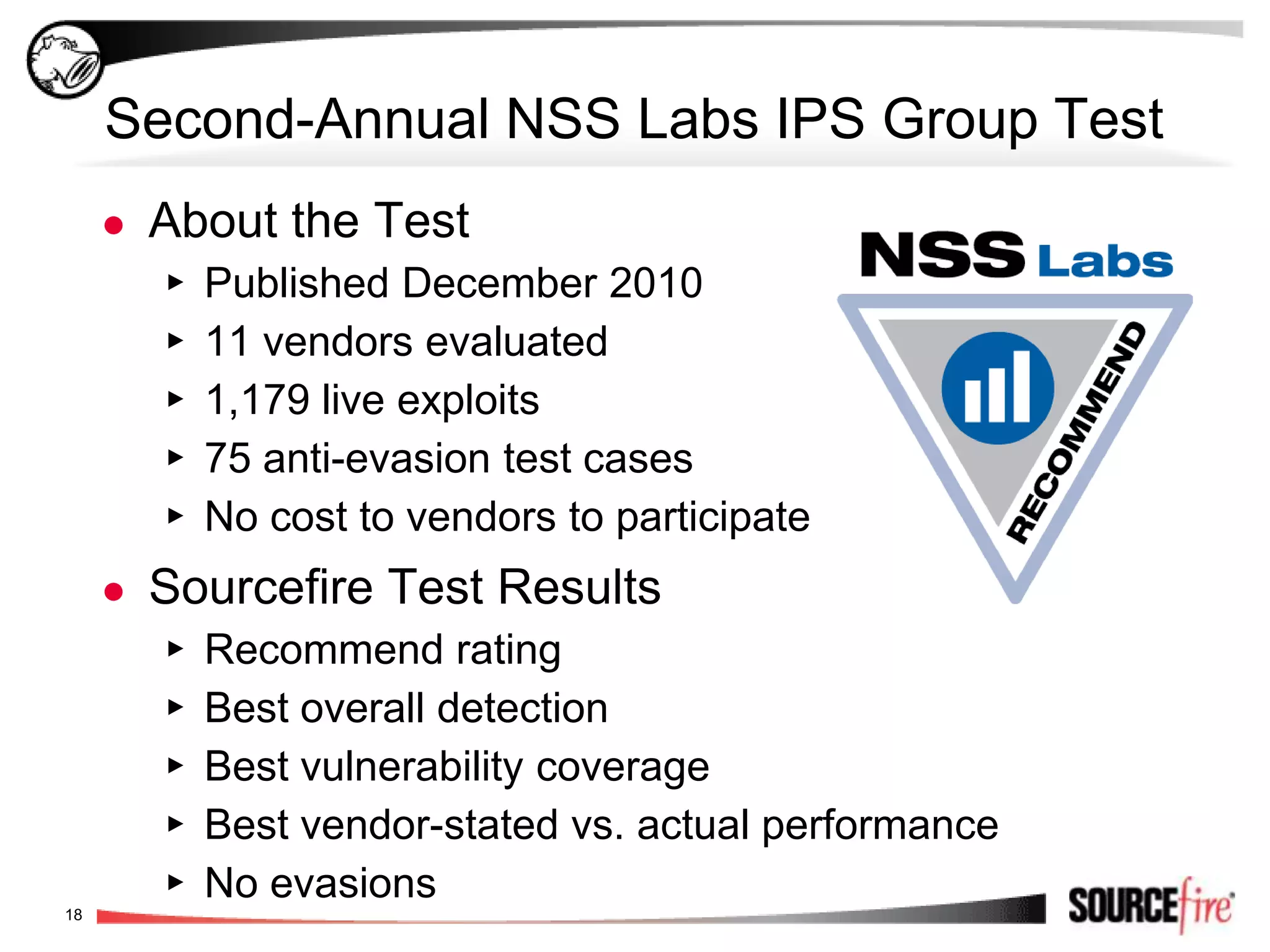
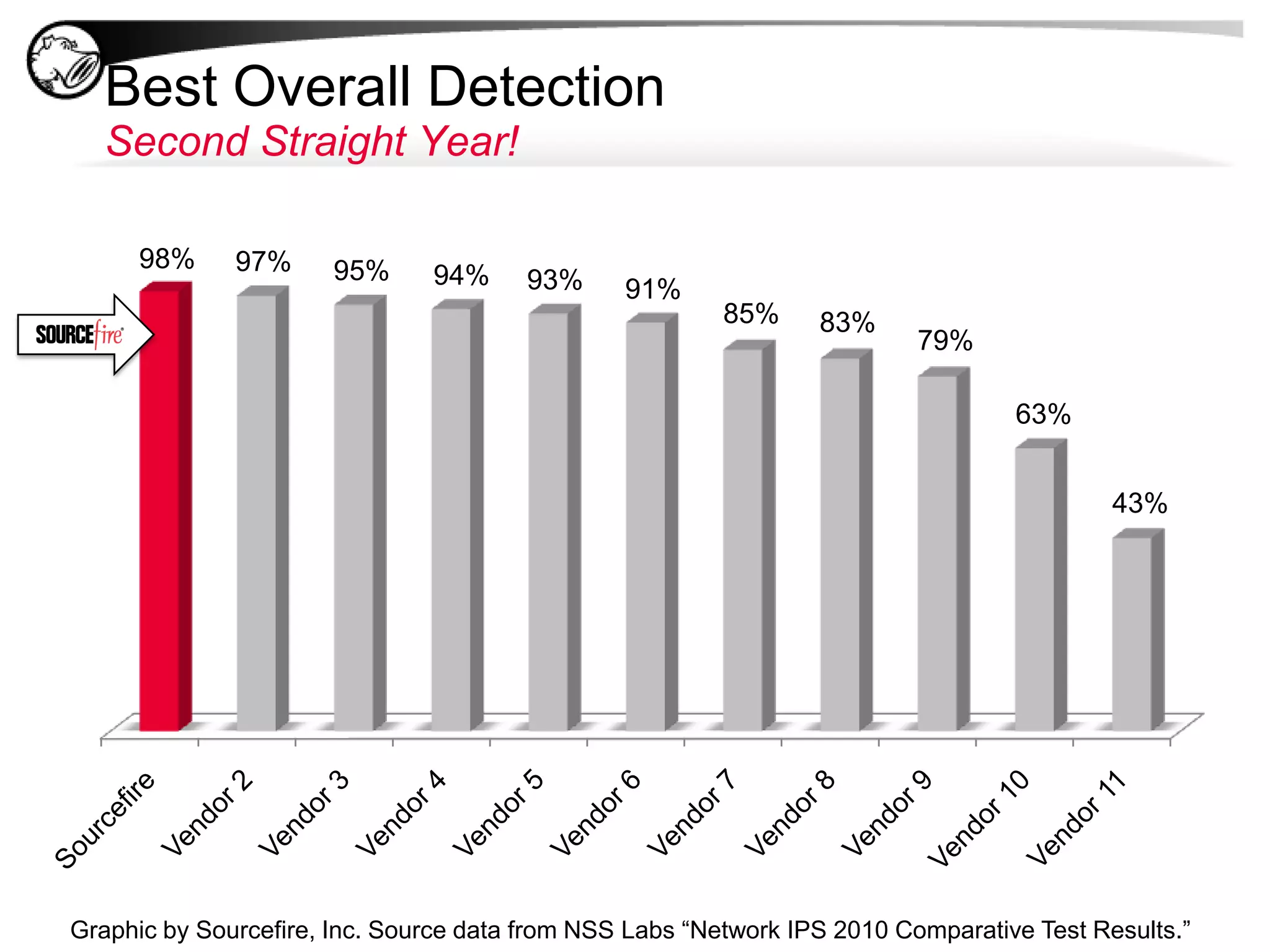
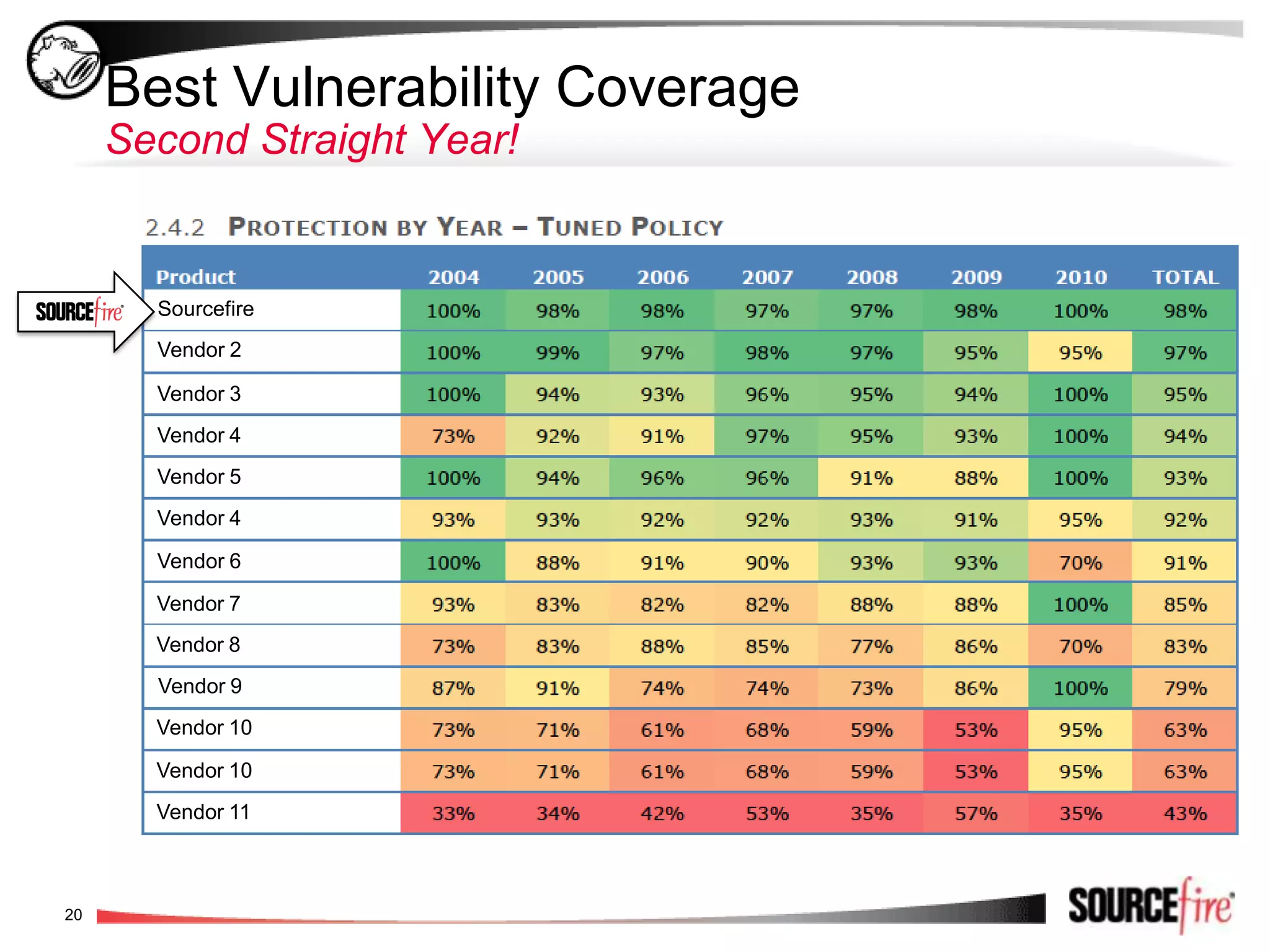
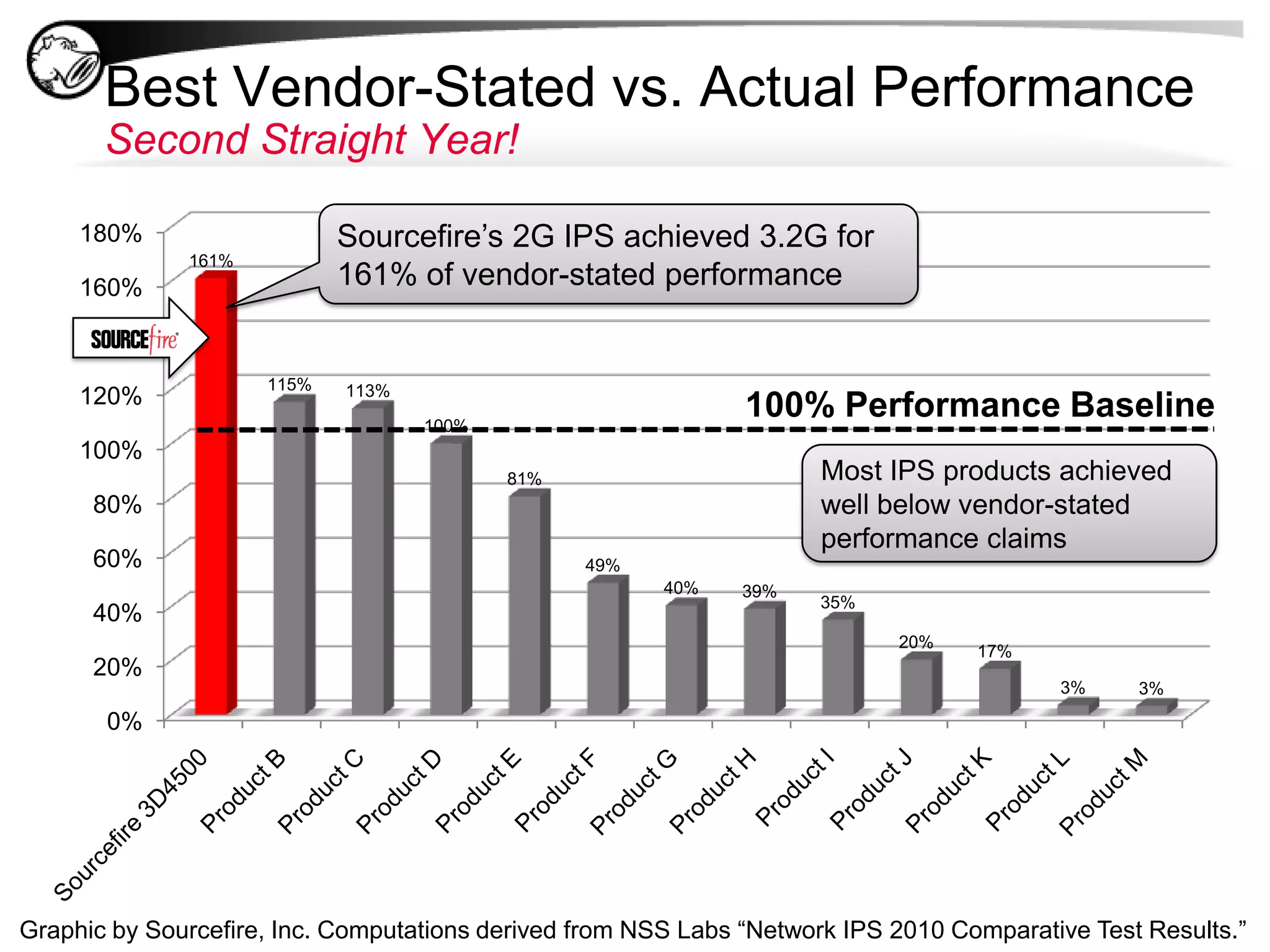
Sourcefire offers innovative intrusion detection and prevention solutions, emphasizing a transition to context-aware and adaptive security infrastructures. The company, founded by the creator of Snort, focuses on enterprise and government markets, boasting strong revenue growth and high performance in independent testing. Their next-generation IPS technology provides comprehensive threat intelligence, automated operation, and enhanced visibility into network activities.
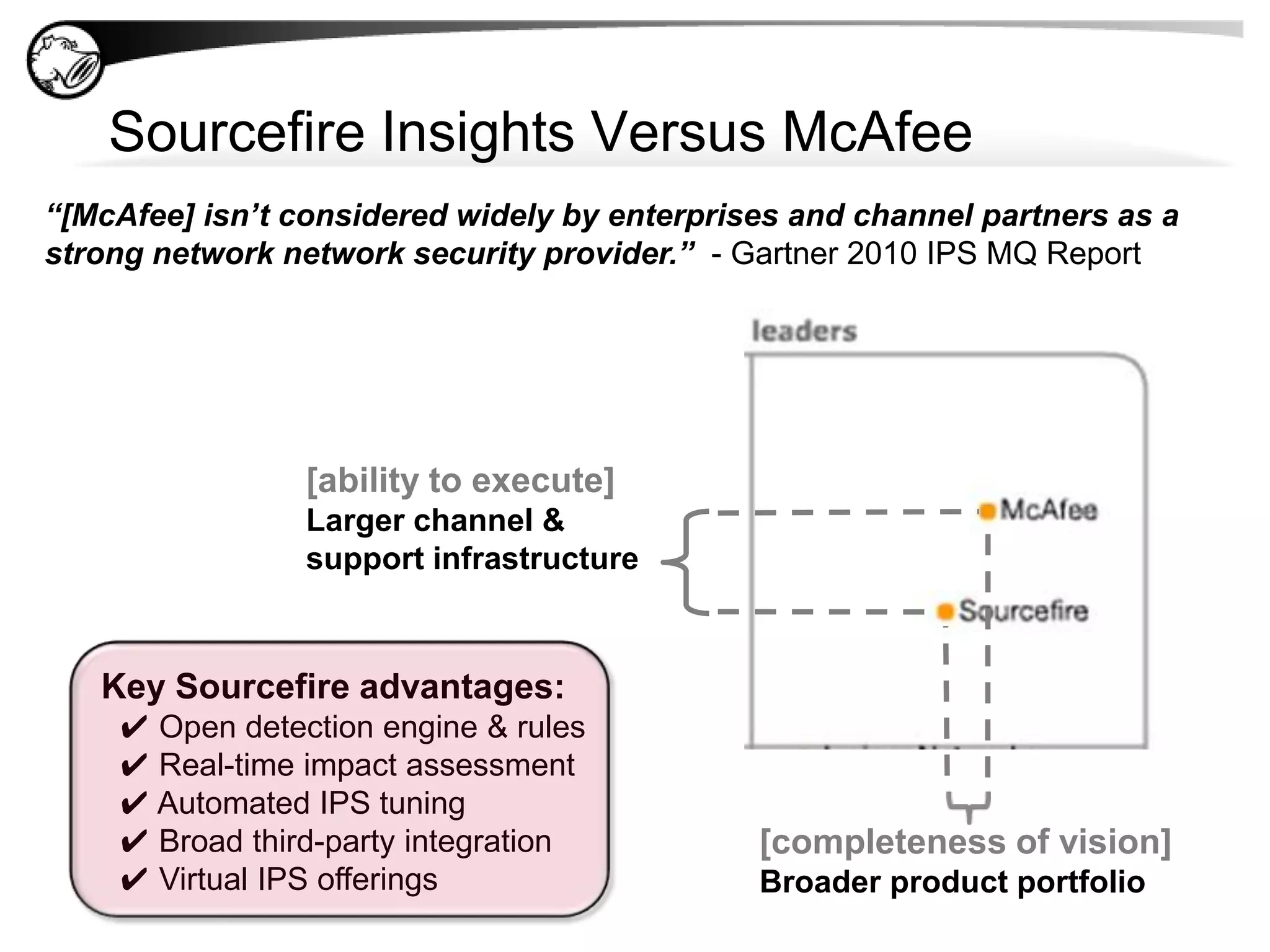
![Sourcefire Insights Versus McAfee“[McAfee] isn’t considered widely by enterprises and channel partners as a strong network network security provider.” - Gartner 2010 IPS MQ Report[ability to execute]Larger channel & support infrastructureKey Sourcefire advantages:✔ Open detection engine & rules✔ Real-time impact assessment ✔ Automated IPS tuning](https://image.slidesharecdn.com/sourcefirenewspresentationwebinar-13043507860199-phpapp01/75/Sourcefire-Webinar-NEW-GENERATION-IPS-18-2048.jpg)

![✔ Virtual IPS offerings[completeness of vision]Broader product portfolio](https://image.slidesharecdn.com/sourcefirenewspresentationwebinar-13043507860199-phpapp01/75/Sourcefire-Webinar-NEW-GENERATION-IPS-20-2048.jpg)