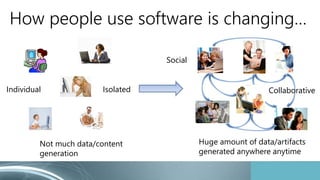
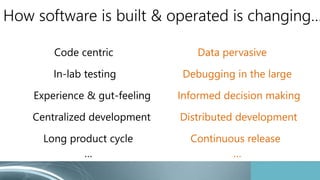
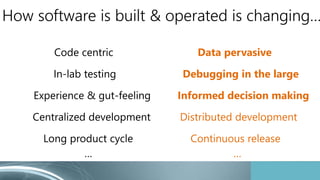
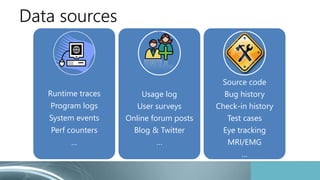
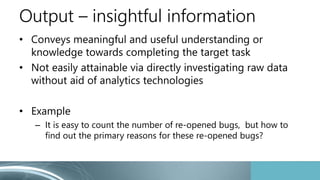
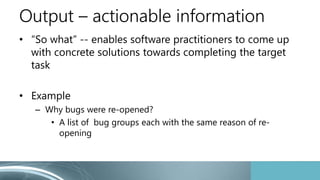
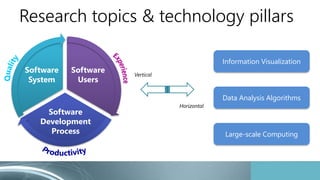
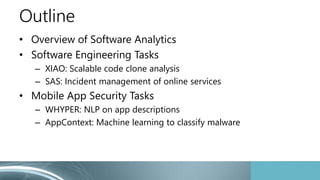
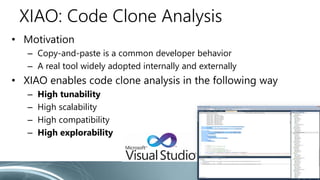
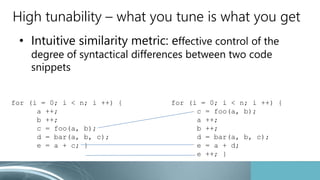
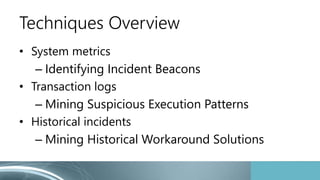
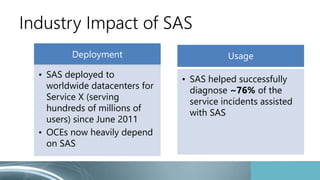
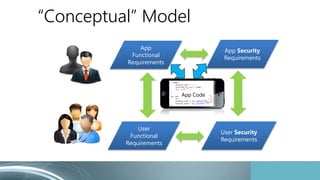
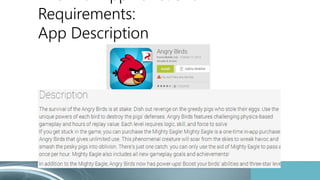
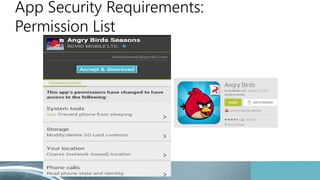
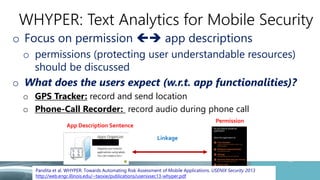
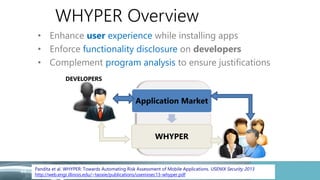
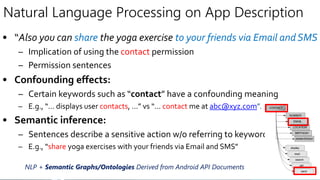
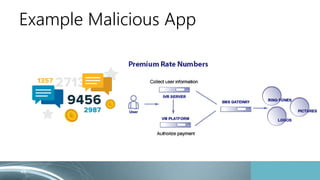
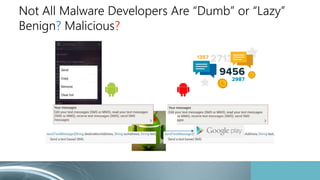
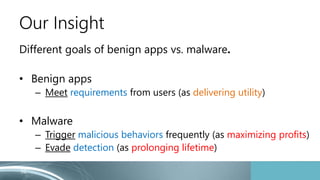
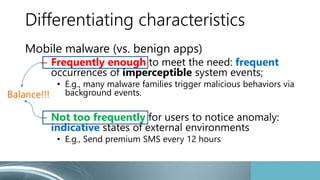
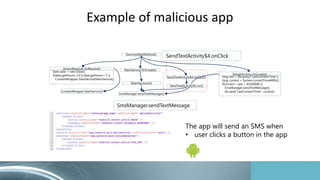
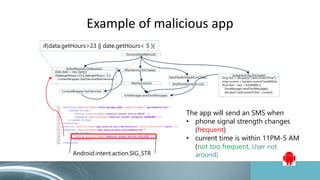
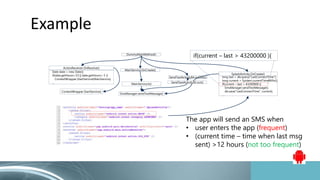
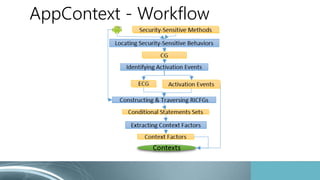
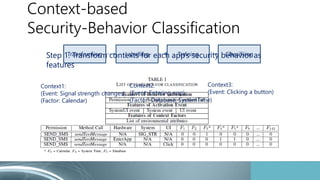
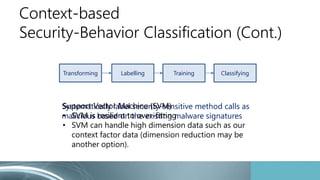
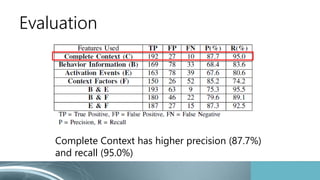
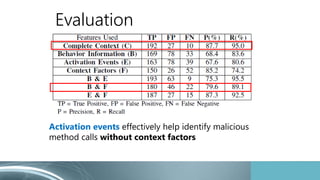
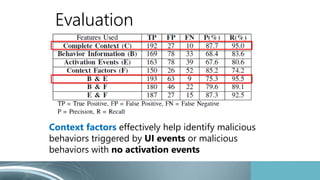
Frodo Baggins presents on software analytics for software engineering and security tasks. The presentation discusses how software and how it is built and used is changing, with data now being ubiquitous and software having continuous development and release. Software analytics aims to enable software practitioners to perform data exploration and analysis to obtain useful insights. Examples of software analytics techniques discussed include XIAO for scalable code clone analysis, and SAS for incident management of online services. The presentation then shifts to discussing software analytics techniques for mobile app security, including WHYPER for natural language processing on app descriptions to link permissions to functionality, and AppContext for machine learning to classify malware.