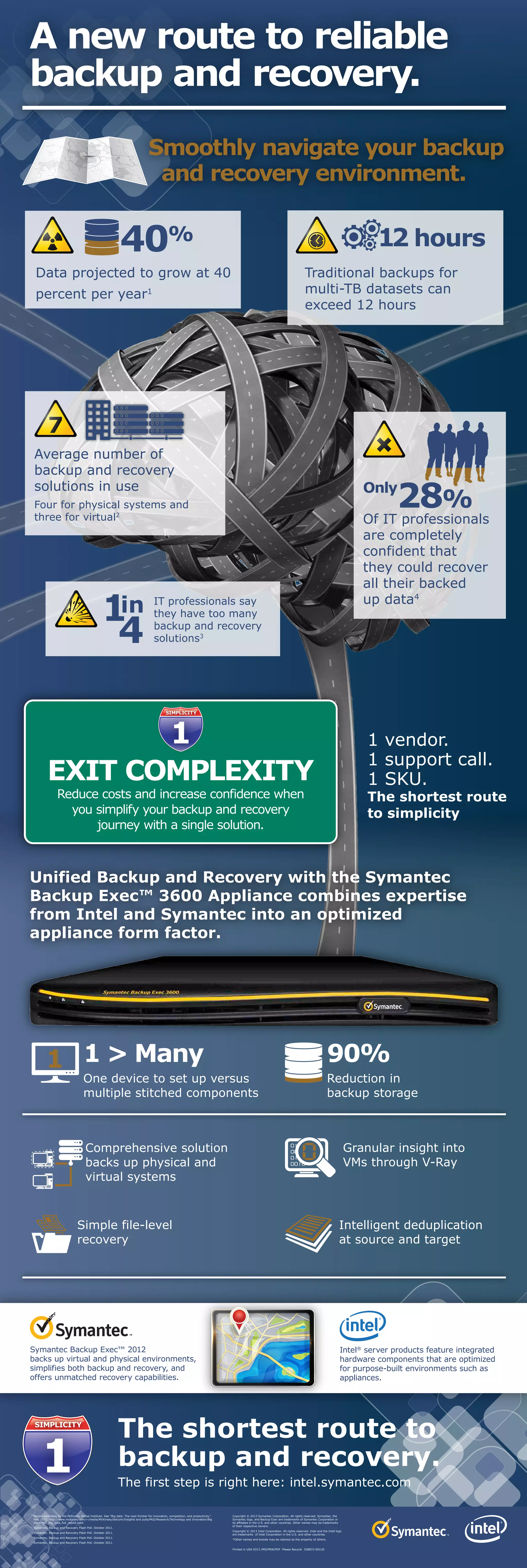
The document summarizes a new backup and recovery solution from Symantec and Intel that aims to simplify the backup process. It notes that traditional backup solutions for large datasets can take over 12 hours and that many organizations use multiple backup and recovery solutions. The new unified Backup Exec 3600 Appliance combines Symantec and Intel expertise into an optimized appliance that provides backup for both physical and virtual systems with features like 90% reduction in backup storage and granular insight into virtual machines. It positions the solution as providing simplicity with a single vendor, support call and SKU.