Report
Share
Download to read offline
Recommended
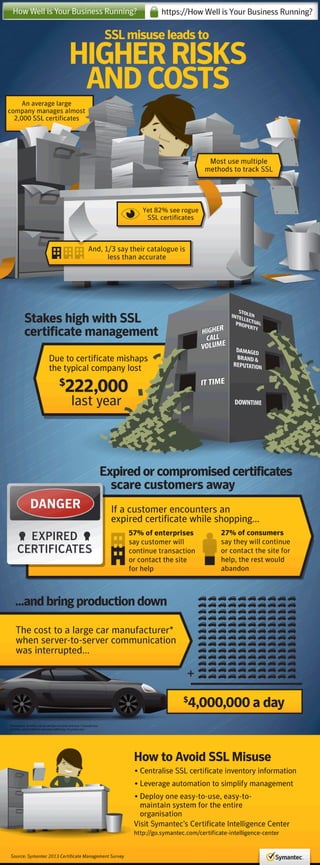
Business Critical SSL Certificate Management - Infographic

Take control of SSL certificates to avoid costly damages.
Ponemon - Cost of Failed Trust: Threats and Attacks

Every enterprise is exposed to losing up to $400 million over two years from attacks against cryptographic keys and digital certificates—yet few enterprises are managing these critical resources, which are the foundation of trust. The “Cost of Failed Trust” on demand webinar reveals new threats and challenges, and quantifies the costs of key and certificate management security failures.
View the on-demand webinar at http://www.venafi.com/cost-of-failed-trust-webinar/?cid=70150000000noHV
Four Must Know Certificate and Key Management Threats That Can Bring Down You...

In this on demand webinar, learn how to identify these risks and the steps to keep your enterprise in control over trust.
1. Learn the four certificate and key management threats to your business
2. Hear how criminals are ruining businesses with attacks on certificates
3. Get insights into the five simple steps to prevent your own disaster
Five Must Haves to Prevent Encryption Disasters

Simple errors, old and weak cryptography, and alarming, malicious attacks are turning digital certificates and encryption keys into an expressway to downtime, targeted attacks, failed compliance, and data breaches. Fortunately, there are simple steps you can take to make sure your organization doesn’t fall victim.
From online banking to the production line, thousands of certificates and keys in every enterprise are the difference between controlling success or failure.
In this live webinar, learn how enterprises are using NIST and industry best practices to develop an effective Enterprise Key and Certificate Management strategy.
Go to http://www.venafi.com/five-musts-ekcm/ to view the full On Demand Webinar.
SANS 20 Critical Security Control 17 Requirements for SSL/TLS Security and Ma...

• Learn how SSL/TLS certificates create trust and impact business when they are misused
• Review five new SANS 20 CSC 17 requirements for SSL/TLS management
• Discover five steps needed to comply with the new requirements
• Understand how to build an immune system for your network that identifies what SSL/TLS keys and certificates are “self” and trusted, and which are not and therefore dangerous
Trojans

In the field of computing, Trojans have been around for
even longer than computer viruses – but traditionally have
been less of a cause for concern amongst the community of
personal computer users. In recent years, however, they have
been the focus of increased attention from anti-virus
companies and heightened levels of user concern due to the
popularity of networked computers.
As the world is moving to an age of computers which
are open to sharing of resources and communication, a very
dark cloud has been thrown over by the unfortunate publishing
of easily used and abused programs so called as Trojans.
Almost every existing network operating system provides the
sort of features that make Trojans possible. If an awareness of
such programs is not made then sneakier people can easily
attack any networked computer with similar tactics without
warning.
The vulnerability that exists is that computers don’t
have any internal controls, it is the user who controls the
computers. If computers are not controlled properly, we’ll
either have increasingly serious security breaches or the
computer industry will go back to locked down main frame
type processing computers to force automatic controls.
As it is said, ”Prevention is better then cure” and hence
with the help of this paper we will be discussing the various
Trojan functions, Trojan variations, Media of infection and the
dis-infection procedures, which will assure prevention from a
Trojan attack.
Recommended
Business Critical SSL Certificate Management - Infographic

Take control of SSL certificates to avoid costly damages.
Ponemon - Cost of Failed Trust: Threats and Attacks

Every enterprise is exposed to losing up to $400 million over two years from attacks against cryptographic keys and digital certificates—yet few enterprises are managing these critical resources, which are the foundation of trust. The “Cost of Failed Trust” on demand webinar reveals new threats and challenges, and quantifies the costs of key and certificate management security failures.
View the on-demand webinar at http://www.venafi.com/cost-of-failed-trust-webinar/?cid=70150000000noHV
Four Must Know Certificate and Key Management Threats That Can Bring Down You...

In this on demand webinar, learn how to identify these risks and the steps to keep your enterprise in control over trust.
1. Learn the four certificate and key management threats to your business
2. Hear how criminals are ruining businesses with attacks on certificates
3. Get insights into the five simple steps to prevent your own disaster
Five Must Haves to Prevent Encryption Disasters

Simple errors, old and weak cryptography, and alarming, malicious attacks are turning digital certificates and encryption keys into an expressway to downtime, targeted attacks, failed compliance, and data breaches. Fortunately, there are simple steps you can take to make sure your organization doesn’t fall victim.
From online banking to the production line, thousands of certificates and keys in every enterprise are the difference between controlling success or failure.
In this live webinar, learn how enterprises are using NIST and industry best practices to develop an effective Enterprise Key and Certificate Management strategy.
Go to http://www.venafi.com/five-musts-ekcm/ to view the full On Demand Webinar.
SANS 20 Critical Security Control 17 Requirements for SSL/TLS Security and Ma...

• Learn how SSL/TLS certificates create trust and impact business when they are misused
• Review five new SANS 20 CSC 17 requirements for SSL/TLS management
• Discover five steps needed to comply with the new requirements
• Understand how to build an immune system for your network that identifies what SSL/TLS keys and certificates are “self” and trusted, and which are not and therefore dangerous
Trojans

In the field of computing, Trojans have been around for
even longer than computer viruses – but traditionally have
been less of a cause for concern amongst the community of
personal computer users. In recent years, however, they have
been the focus of increased attention from anti-virus
companies and heightened levels of user concern due to the
popularity of networked computers.
As the world is moving to an age of computers which
are open to sharing of resources and communication, a very
dark cloud has been thrown over by the unfortunate publishing
of easily used and abused programs so called as Trojans.
Almost every existing network operating system provides the
sort of features that make Trojans possible. If an awareness of
such programs is not made then sneakier people can easily
attack any networked computer with similar tactics without
warning.
The vulnerability that exists is that computers don’t
have any internal controls, it is the user who controls the
computers. If computers are not controlled properly, we’ll
either have increasingly serious security breaches or the
computer industry will go back to locked down main frame
type processing computers to force automatic controls.
As it is said, ”Prevention is better then cure” and hence
with the help of this paper we will be discussing the various
Trojan functions, Trojan variations, Media of infection and the
dis-infection procedures, which will assure prevention from a
Trojan attack.
Kent King - PKI: Do You Know Your Exposure?

Since the introduction of public key cryptography by Diffie and Hellman in 1976, uses and infrastructure have grown in unimaginable ways. The security that has been afforded through Public Key Infrastructure (PKI) is now an integral and essential part of the internet. The proliferation of digital certificates, certificate authorities and PKI implementations creates a large and enticing attack surface. Most businesses rely heavily on PKI for their data security, yet few organizations could tell you how many certificates they have deployed, where they are and their current status. This presentation will discuss a few of the most critical PKI implementations and threats they face today. The talk will conclude with mitigation recommendations and practical ways you can improve the PKI in your organization.
Tutorial membuat Public Key Infrastructure

Nama : Suci Rahmawati
Nim : 11453201617
Mahasiswa Sistem Informasi Uin Suska Riau
Securing your Windows Network with the Microsoft Security Baselines

IT professionals everywhere strive to secure their network, but it can be a daunting task. Luckily, Microsoft provides some boilerplate templates to get you started.
In this session, Frank begins by providing an overview of the Microsoft Security Baselines, explaining what they are and how they relate to the Center for Internet Security (CIS) Benchmarks, why Security Baselines are important (especially in PCI- or HIPAA-regulated environments), what to expect to change when implementing a baseline, when it is appropriate to implement a Microsoft Security Baseline, and provide you with project success criteria.
Then it's time for the details: Frank explains how to inventory your systems, how to download the Microsoft Security Baselines, how to apply your first Baseline to Active Directory, and how to manage the implementation---including recommendations on how to make changes (or "overrides") to the Security Baselines both from a process standpoint and a technical standpoint (using Group Policy Management).
Implementing a Secure and Effective PKI on Windows Server 2012 R2

The infrastructure that deploys and manages digital certificates, known as a Public Key Infrastructure (PKI), is often the center for cryptography in an organization. It is also in service for 10+ years, which means that one must carefully consider design options before implementation. In this presentation, Frank will cover modern standards for cryptography, how they apply to a Microsoft PKI infrastructure, and share recommendations based on he has seen in the field.
B.Noviansyah - “National Public Key Infrastructure: Friend or Foe?"

National Public Key Infrastructure: Friend or Foe?
Switch to SHA-2 SSL - A Step-by-Step Migration Guide

Avoiding pitfalls, meeting critical deadlines and eliminating service disruptions during SHA-1 certificate deprecation.
This paper will describe the technical and business impact of SHA-1 migration as it pertains to SSL certificates only. It will outline a recommended migration path to minimize the cost and operational impact of replacing affected SSL certificates.
Muhammad Abrar Istiadi - “How to hack #IDSECCONF2016 ctf online challenge"

How to hack #IDSECCONF2016 ctf online challenge
Smoothly Navigate Your Backup & Recover Environment - Infographic

A new route to reliable backup and recovery.
More Related Content
Viewers also liked
Kent King - PKI: Do You Know Your Exposure?

Since the introduction of public key cryptography by Diffie and Hellman in 1976, uses and infrastructure have grown in unimaginable ways. The security that has been afforded through Public Key Infrastructure (PKI) is now an integral and essential part of the internet. The proliferation of digital certificates, certificate authorities and PKI implementations creates a large and enticing attack surface. Most businesses rely heavily on PKI for their data security, yet few organizations could tell you how many certificates they have deployed, where they are and their current status. This presentation will discuss a few of the most critical PKI implementations and threats they face today. The talk will conclude with mitigation recommendations and practical ways you can improve the PKI in your organization.
Tutorial membuat Public Key Infrastructure

Nama : Suci Rahmawati
Nim : 11453201617
Mahasiswa Sistem Informasi Uin Suska Riau
Securing your Windows Network with the Microsoft Security Baselines

IT professionals everywhere strive to secure their network, but it can be a daunting task. Luckily, Microsoft provides some boilerplate templates to get you started.
In this session, Frank begins by providing an overview of the Microsoft Security Baselines, explaining what they are and how they relate to the Center for Internet Security (CIS) Benchmarks, why Security Baselines are important (especially in PCI- or HIPAA-regulated environments), what to expect to change when implementing a baseline, when it is appropriate to implement a Microsoft Security Baseline, and provide you with project success criteria.
Then it's time for the details: Frank explains how to inventory your systems, how to download the Microsoft Security Baselines, how to apply your first Baseline to Active Directory, and how to manage the implementation---including recommendations on how to make changes (or "overrides") to the Security Baselines both from a process standpoint and a technical standpoint (using Group Policy Management).
Implementing a Secure and Effective PKI on Windows Server 2012 R2

The infrastructure that deploys and manages digital certificates, known as a Public Key Infrastructure (PKI), is often the center for cryptography in an organization. It is also in service for 10+ years, which means that one must carefully consider design options before implementation. In this presentation, Frank will cover modern standards for cryptography, how they apply to a Microsoft PKI infrastructure, and share recommendations based on he has seen in the field.
B.Noviansyah - “National Public Key Infrastructure: Friend or Foe?"

National Public Key Infrastructure: Friend or Foe?
Switch to SHA-2 SSL - A Step-by-Step Migration Guide

Avoiding pitfalls, meeting critical deadlines and eliminating service disruptions during SHA-1 certificate deprecation.
This paper will describe the technical and business impact of SHA-1 migration as it pertains to SSL certificates only. It will outline a recommended migration path to minimize the cost and operational impact of replacing affected SSL certificates.
Muhammad Abrar Istiadi - “How to hack #IDSECCONF2016 ctf online challenge"

How to hack #IDSECCONF2016 ctf online challenge
Viewers also liked (16)
Securing your Windows Network with the Microsoft Security Baselines

Securing your Windows Network with the Microsoft Security Baselines
Implementing a Secure and Effective PKI on Windows Server 2012 R2

Implementing a Secure and Effective PKI on Windows Server 2012 R2
B.Noviansyah - “National Public Key Infrastructure: Friend or Foe?"

B.Noviansyah - “National Public Key Infrastructure: Friend or Foe?"
Switch to SHA-2 SSL - A Step-by-Step Migration Guide

Switch to SHA-2 SSL - A Step-by-Step Migration Guide
Muhammad Abrar Istiadi - “How to hack #IDSECCONF2016 ctf online challenge"

Muhammad Abrar Istiadi - “How to hack #IDSECCONF2016 ctf online challenge"
More from David Martin
Smoothly Navigate Your Backup & Recover Environment - Infographic

A new route to reliable backup and recovery.
More from David Martin (6)
Charting The Rise Of a CyberCriminal - Infographic

Charting The Rise Of a CyberCriminal - Infographic
Symantec Survey: Cybersecurity Threats! Are You Prepared?

Symantec Survey: Cybersecurity Threats! Are You Prepared?
Smoothly Navigate Your Backup & Recover Environment - Infographic

Smoothly Navigate Your Backup & Recover Environment - Infographic
2014 Security Predictions from Symantec - Infographic

2014 Security Predictions from Symantec - Infographic
Recently uploaded
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Welocme to ViralQR, your best QR code generator.

Welcome to ViralQR, your best QR code generator available on the market!
At ViralQR, we design static and dynamic QR codes. Our mission is to make business operations easier and customer engagement more powerful through the use of QR technology. Be it a small-scale business or a huge enterprise, our easy-to-use platform provides multiple choices that can be tailored according to your company's branding and marketing strategies.
Our Vision
We are here to make the process of creating QR codes easy and smooth, thus enhancing customer interaction and making business more fluid. We very strongly believe in the ability of QR codes to change the world for businesses in their interaction with customers and are set on making that technology accessible and usable far and wide.
Our Achievements
Ever since its inception, we have successfully served many clients by offering QR codes in their marketing, service delivery, and collection of feedback across various industries. Our platform has been recognized for its ease of use and amazing features, which helped a business to make QR codes.
Our Services
At ViralQR, here is a comprehensive suite of services that caters to your very needs:
Static QR Codes: Create free static QR codes. These QR codes are able to store significant information such as URLs, vCards, plain text, emails and SMS, Wi-Fi credentials, and Bitcoin addresses.
Dynamic QR codes: These also have all the advanced features but are subscription-based. They can directly link to PDF files, images, micro-landing pages, social accounts, review forms, business pages, and applications. In addition, they can be branded with CTAs, frames, patterns, colors, and logos to enhance your branding.
Pricing and Packages
Additionally, there is a 14-day free offer to ViralQR, which is an exceptional opportunity for new users to take a feel of this platform. One can easily subscribe from there and experience the full dynamic of using QR codes. The subscription plans are not only meant for business; they are priced very flexibly so that literally every business could afford to benefit from our service.
Why choose us?
ViralQR will provide services for marketing, advertising, catering, retail, and the like. The QR codes can be posted on fliers, packaging, merchandise, and banners, as well as to substitute for cash and cards in a restaurant or coffee shop. With QR codes integrated into your business, improve customer engagement and streamline operations.
Comprehensive Analytics
Subscribers of ViralQR receive detailed analytics and tracking tools in light of having a view of the core values of QR code performance. Our analytics dashboard shows aggregate views and unique views, as well as detailed information about each impression, including time, device, browser, and estimated location by city and country.
So, thank you for choosing ViralQR; we have an offer of nothing but the best in terms of QR code services to meet business diversity!
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

Building better applications for business users with SAP Fiori.
• What is SAP Fiori and why it matters to you
• How a better user experience drives measurable business benefits
• How to get started with SAP Fiori today
• How SAP Fiori elements accelerates application development
• How SAP Build Code includes SAP Fiori tools and other generative artificial intelligence capabilities
• How SAP Fiori paves the way for using AI in SAP apps
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Recently uploaded (20)
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx

Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
