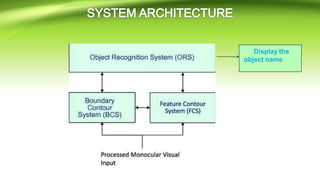
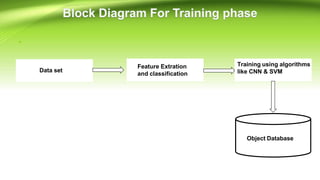
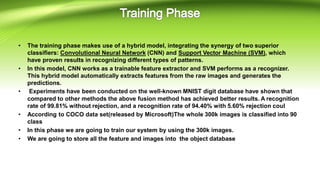
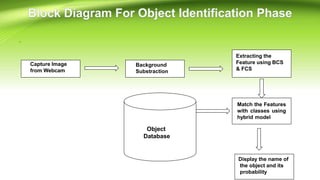
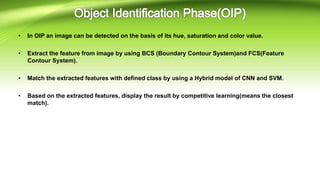
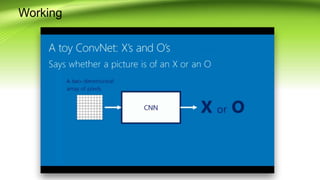
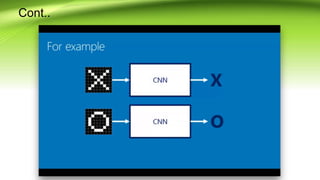
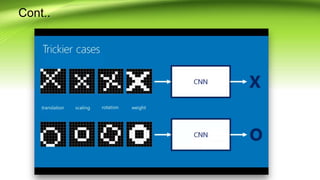
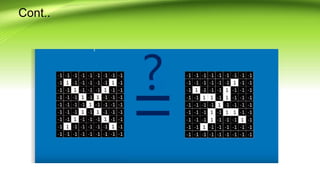
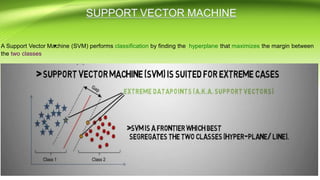
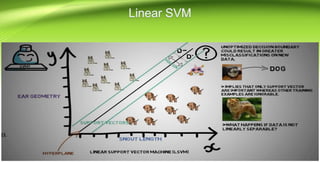
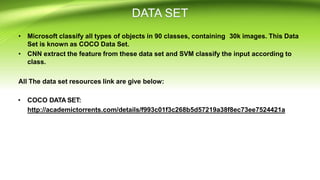
This document summarizes a project on real-time object detection using computer vision techniques. It discusses using a system that can recognize objects in a video stream from a camera and label them with bounding boxes and labels. It notes that most video surveillance footage is uninteresting unless there are moving objects. The project aims to address this by building an accurate, fast object detection system that can run on resource-constrained devices. It proposes using a hybrid CNN-SVM model trained on a large dataset to recognize objects and discusses the training and detection phases of the system.