Embed presentation
Downloaded 44 times

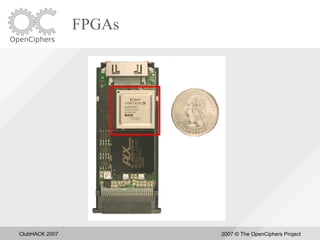





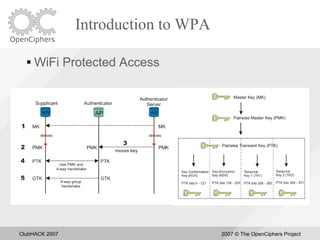

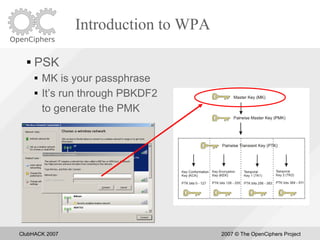
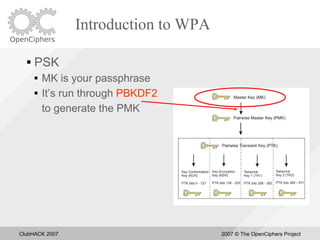

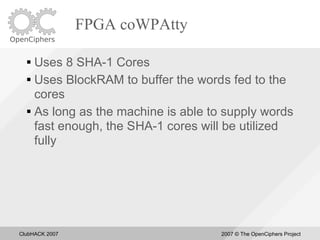
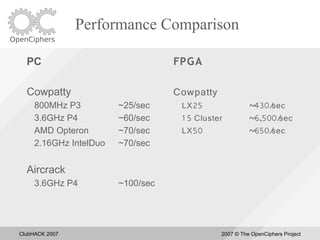









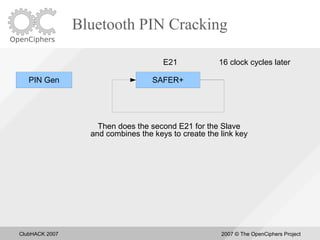

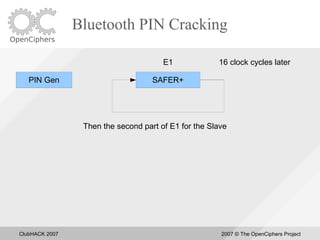

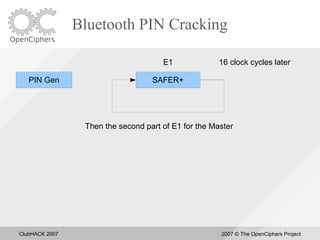
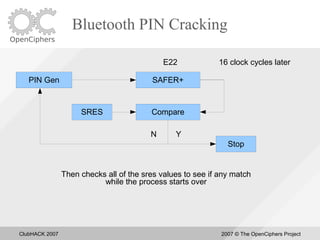















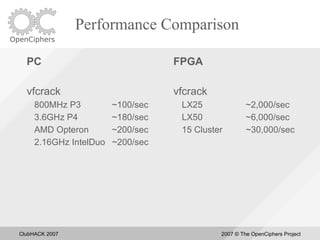









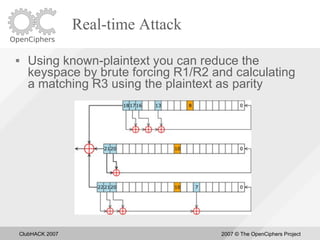
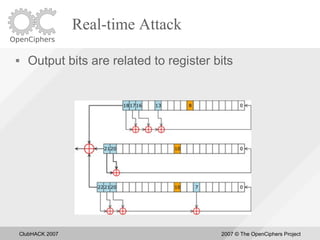
























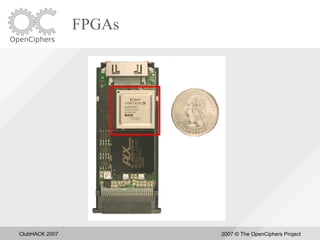
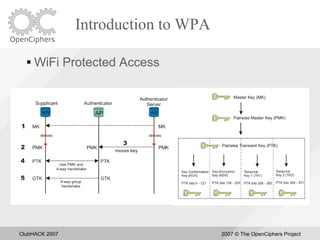
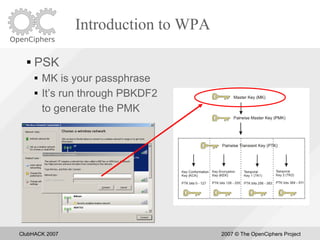
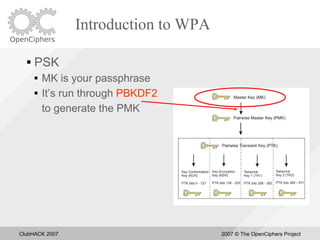
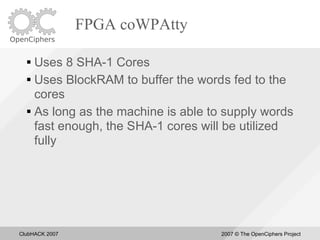
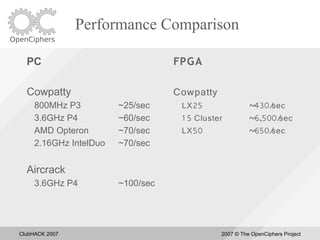
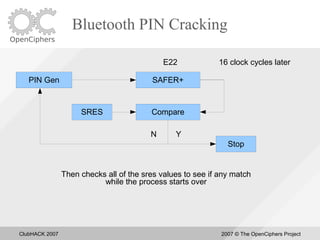
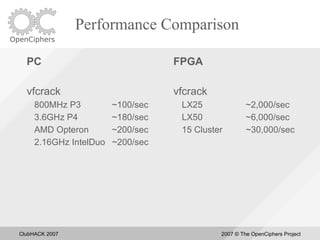
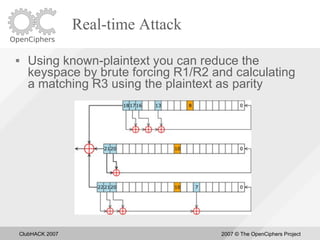
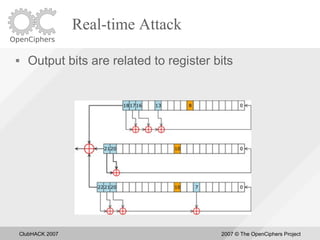
This document summarizes David Hulton's presentation on using FPGAs for password cracking. It introduces several new password cracking tools developed since the last Defcon or Shmoocon conferences, including CoWPAtty for cracking WPA passwords, BTCrack for cracking Bluetooth PINs, and tools for cracking WinZip AES encryption and Apple FileVault encryption. It demonstrates that FPGAs can provide significant performance increases over CPUs for password cracking applications.