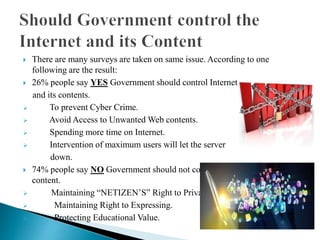
The document discusses the nature of the internet as a global network of interconnected systems, the roles of organizations like ICANN and TRAI in governing internet content, and the debate over government control. Surveys reveal that while 26% of people support government regulation to prevent cybercrime, 74% oppose it, valuing privacy and freedom of expression instead. The conclusion suggests enhancing security without exerting control is crucial for fostering development and progress.