Embed presentation
Downloaded 39 times
































































































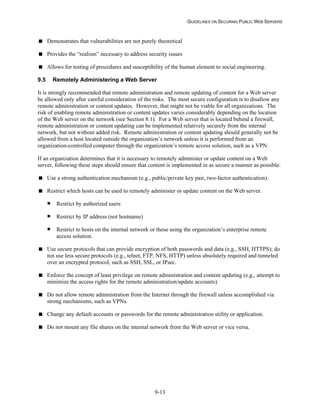
























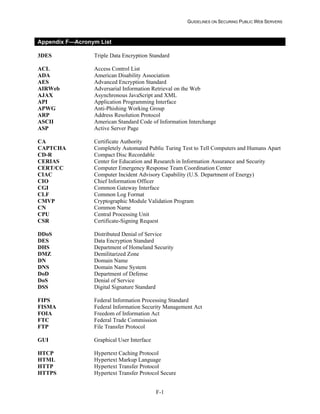




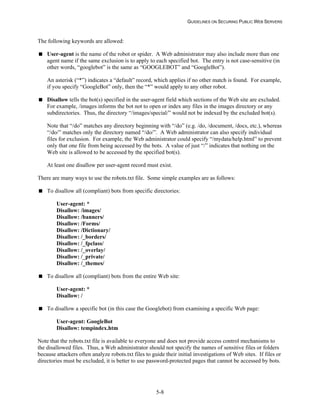
This document from the National Institute of Standards and Technology provides guidelines for securing public web servers. It was written by Miles Tracy, Wayne Jansen, Karen Scarfone, and Theodore Winograd. The document offers recommendations to help organizations securely configure and manage their public-facing web servers.