Embed presentation
Download as PDF, PPTX























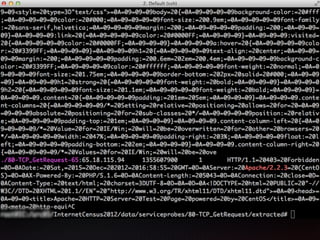


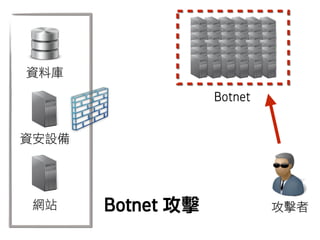



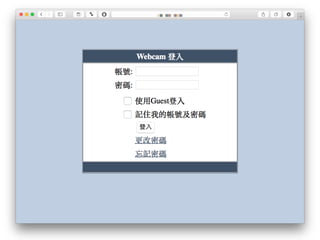









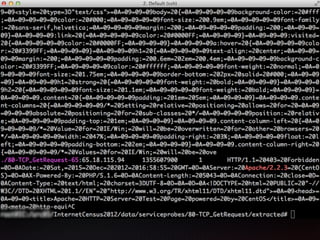
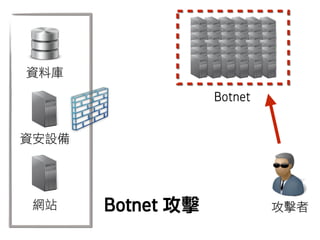
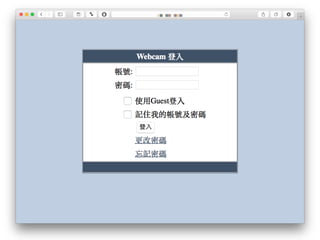
The document references an event involving hacking at the Intaiwan conference in August 2015 at the Central Research Institute. It includes discussions on various cyber vulnerabilities such as cross-site scripting, SQL injection, and others. Additionally, it highlights trends in cybersecurity related to big data.