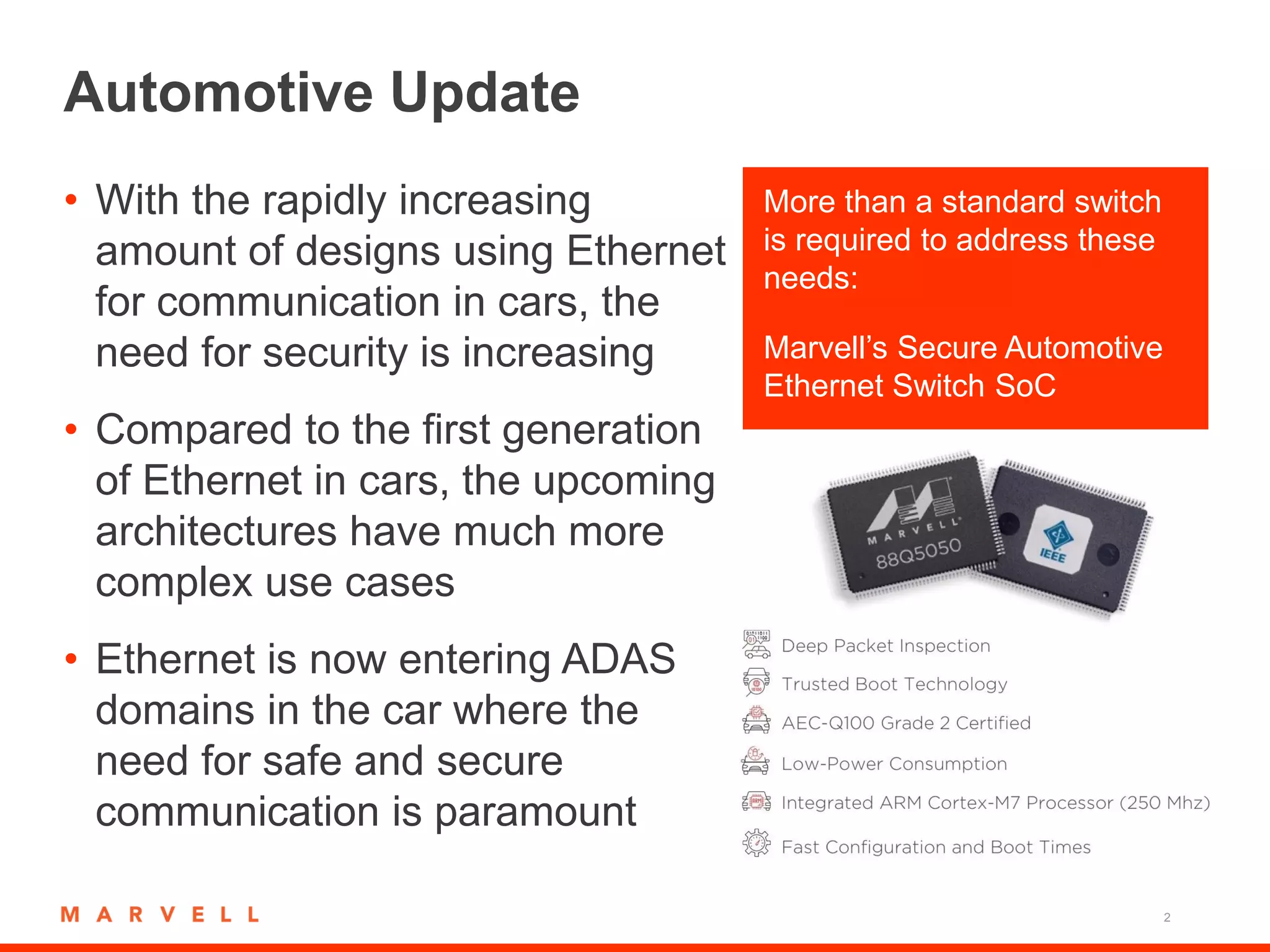
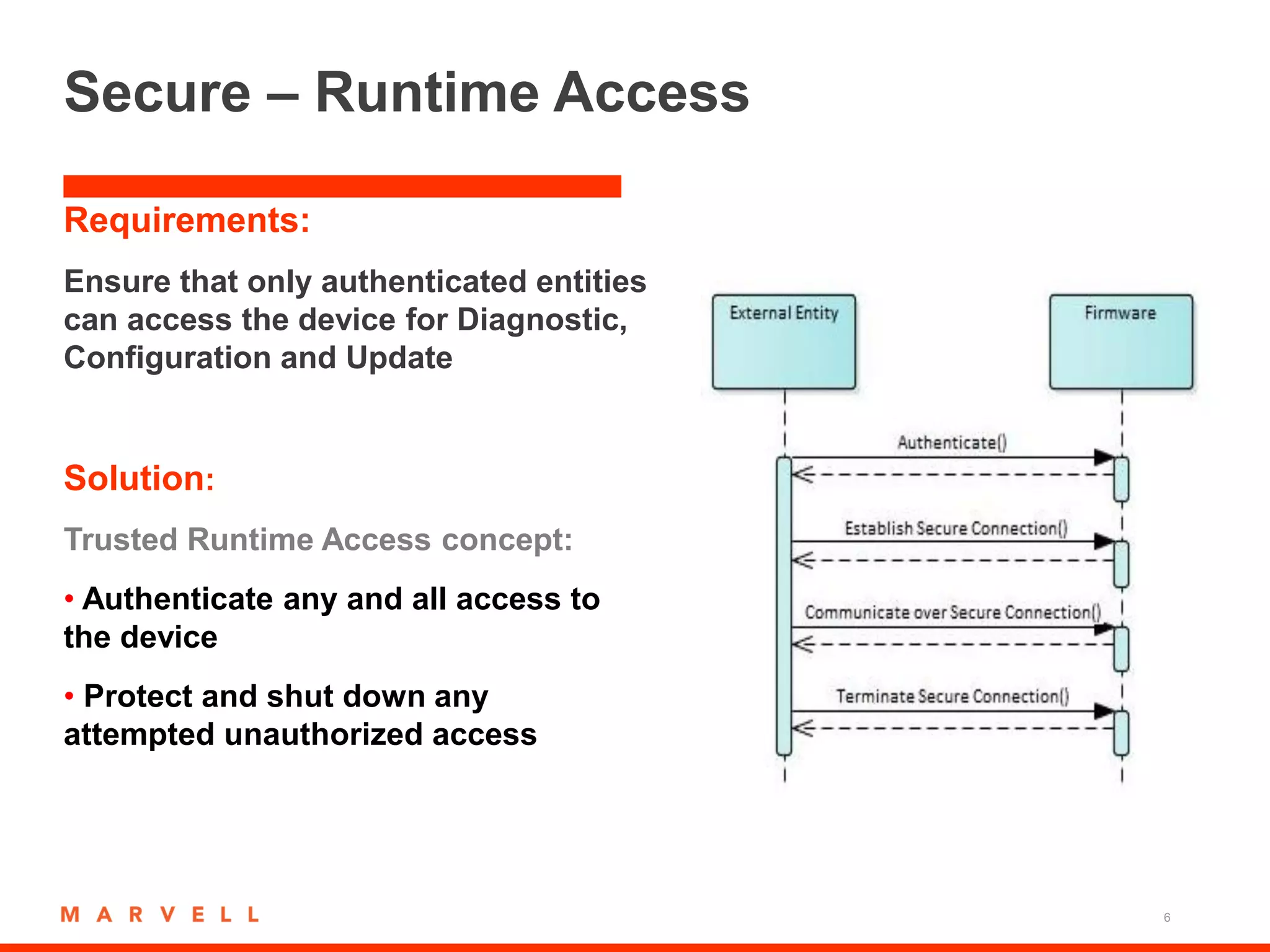
The document discusses the need for increased security in automotive Ethernet architectures as connectivity and the use of Ethernet expands in vehicles. It summarizes Marvell's secure automotive Ethernet switch system-on-chip, which provides trusted boot, update, and runtime access concepts to securely configure, update, and access the device. It also details intrusion prevention and detection solutions to monitor data flows, detect anomalies, and execute countermeasures.