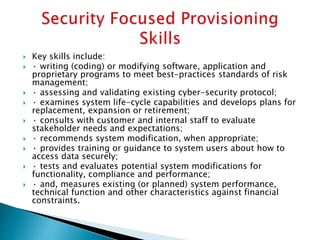
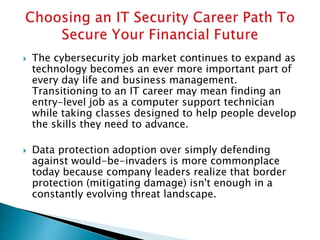
There are currently around 500,000 computer security jobs in North America and approximately three million globally, making it an opportune time for individuals seeking a career shift into IT security. Fast-track technical training and industry certifications are essential for candidates to develop the necessary skills, including data analysis, risk management, and technical problem-solving. The increasing importance of data protection, alongside the growing technological landscape and demand for cybersecurity professionals, suggests a persistent shortage of qualified applicants in the field.