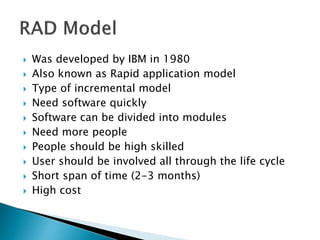
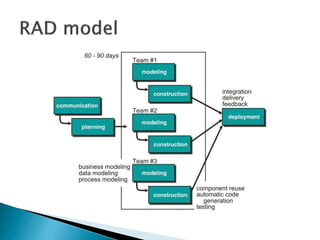
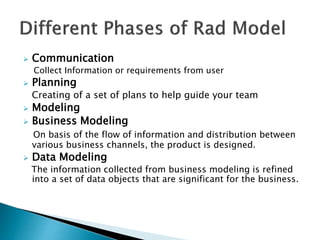
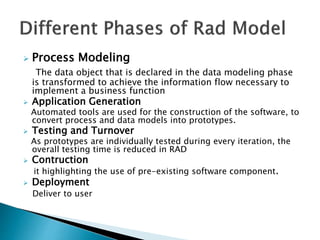
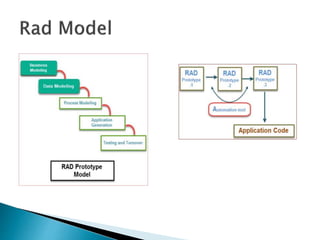
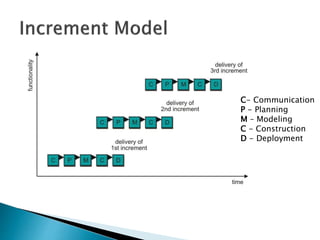
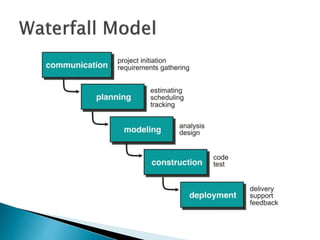
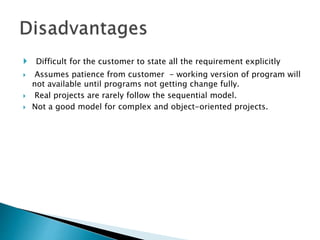
The document discusses the Rapid Application Development (RAD) model. It is an incremental model that is useful for projects that need software quickly. It involves dividing a project into modules that can be developed by a team of skilled developers within a short time span, usually 2-3 months. The RAD process involves communication, planning, modeling, construction, and deployment phases. It allows for flexibility, adaptation to changes, and reduced defects through prototyping. However, it requires committed developers and is not suitable for smaller projects.