Sample Deliverable Report
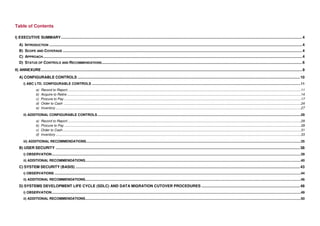
- 1. Table of Contents I) EXECUTIVE SUMMARY ...................................................................................................................................................................................................................................... 4 A) INTRODUCTION ................................................................................................................................................................................................................................................. 4 B) SCOPE AND COVERAGE .................................................................................................................................................................................................................................... 4 C) APPROACH ....................................................................................................................................................................................................................................................... 4 D) STATUS OF CONTROLS AND RECOMMENDATIONS ............................................................................................................................................................................................... 6 II) ANNEXURE ......................................................................................................................................................................................................................................................... 9 A) CONFIGURABLE CONTROLS .................................................................................................................................................................................................................... 10 i) ABC LTD. CONFIGURABLE CONTROLS ..........................................................................................................................................................................................................................11 a) Record to Report....................................................................................................................................................................................................................................................11 b) Acquire to Retire ....................................................................................................................................................................................................................................................14 c) Procure to Pay .......................................................................................................................................................................................................................................................17 d) Order to Cash ........................................................................................................................................................................................................................................................24 e) Inventory ................................................................................................................................................................................................................................................................27 ii) ADDITIONAL CONFIGURABLE CONTROLS ....................................................................................................................................................................................................................29 a) Record to Report....................................................................................................................................................................................................................................................29 b) Procure to Pay .......................................................................................................................................................................................................................................................29 c) Order to Cash .........................................................................................................................................................................................................................................................31 d) Inventory ................................................................................................................................................................................................................................................................33 iii) ADDITIONAL RECOMMENDATIONS ................................................................................................................................................................................................................................35 B) USER SECURITY ......................................................................................................................................................................................................................................... 38 i) OBSERVATION ....................................................................................................................................................................................................................................................................39 ii) ADDITIONAL RECOMMENDATIONS .................................................................................................................................................................................................................................40 C) SYSTEM SECURITY (BASIS) ...................................................................................................................................................................................................................... 43 i) OBSERVATIONS .................................................................................................................................................................................................................................................................44 ii) ADDITIONAL RECOMMENDATIONS .................................................................................................................................................................................................................................46 D) SYSTEMS DEVELOPMENT LIFE CYCLE (SDLC) AND DATA MIGRATION CUTOVER PROCEDURES .............................................................................................. 48 i) OBSERVATION ....................................................................................................................................................................................................................................................................49 ii) ADDITIONAL RECOMMENDATIONS .................................................................................................................................................................................................................................50
- 2. EXECUTIVE SUMMARY • Privileged User Access Review (Recommended as a pre go-live check) I) Executive Summary • Critical Transaction Access Review (Recommended as a pre go-live check) 3) System Security Review (BASIS): A) Introduction ABC Ltd. has embarked on an initiative to transition from legacy IT applications to • Critical Security Parameter Review - Direct changes to Production client, user SAP to align itself to the corporate systems and to gain process efficiencies authentication and table maintenance parameters utilizing SAP. The SAP implementation project name is ABC Ltd. which will be used throughout this report. In order to ensure a secured internal control • Security Table and Log Maintenance - Log enabling of critical security and environment for the new implementation, ABC Ltd. has engaged AGC to perform financial data tables as per leading practices a Pre-Implementation Review encompassing Configurable Controls, System and User Security, and the Systems Development Life Cycle (SDLC). This report • Password Controls - Compliance of SAP password parameters with ABC provides a summary of the scope, approach, findings and recommendations of LTD. password standards this review. • Security Change Management Procedures - Transport Management System (TMS) security and parameter configuration for compliance with SDLC B) Scope and Coverage 4) Systems Development Life Cycle (SDLC) and Data Migration Cutover AGC performed a project assurance review of the ABC Ltd. SAP Implementation Procedures Review: project. This was not an audit and therefore we do not express an overall opinion or conclusion on the reliability or integrity of the system. The review was SDLC Review: Adherence to ABC LTD. IT Project Lifecycle Methodology/ASAP performed “real-time” as the project was in progress therefore recommendations Implementation Methodology; Adherence to Checkpoint Reviews on overall internal control enhancements and risk mitigation were directed to the project team as the system was being implemented. Project Governance Review: 1) Configurable Controls Review: • Program Management Structure - Roles & Responsibilities (RACI matrix) • Evaluation of the existing configurable controls for their applicability, • Scope & Delivery Management - Deliverables tracking, Acceptance criteria existence, completeness and operating effectiveness. (QA/sign-offs), Scope Control, Change Management, Issue Tracking and Resolution • Propose and evaluate additional configurable control opportunities • Project Health Status Measurement, Monitoring & Reporting Procedures - 2) User Security Review: Scope, Deliverables, Schedule, Cost, Risks, Issues • Segregation of Duties Review - Adequacy and Completeness of GRC rule C) Approach sets 1) Configurable Controls Review: • User Role Design - Review of appropriateness of user/role creation procedures; Sample validation of users/roles The existing configurable controls were evaluated for their applicability to ABC Ltd. and all the applicable controls were tested in the Development environment. SAP PRE-IMPLEMENTATION REVIEW REPORT Page 4 of 53 DRAFT FOR DISCUSSION
- 3. EXECUTIVE SUMMARY Further, upon understanding the business processes, additional configurable control opportunities were proposed to the ABC Ltd. project team. Upon confirmation of the applicability/ feasibility of these controls, they were tested in the Development environment to confirm they were properly designed and operating effectively. All exceptions were discussed with the ABC Ltd. team for inclusion in the SAP configuration, as applicable. 2) User Security Review: Segregation of Duties Review – The SAP GRC Access Control Rule sets were reviewed for adequacy and completeness. The review included rule sets and underlying transaction codes. User Role Design – ABC’s procedures for designing user roles in SAP were reviewed for their alignment with leading practices and recommendations were provided to strengthen the controls. Privileged User Access Review and Critical Transaction Access Review – Since the user roles and users were not set up completely in the system at the time of this review, these are recommended to be included in the pre go-live check procedures 3) System Security Review (BASIS): We reviewed the SAP Development environment for critical system security (BASIS) parameters, activations for log maintenance for security and financial data tables, password controls in compliance with ABC LTD. standards and leading practices, and system change management procedures. 4) SDLC and Data Migration Cutover Procedures Review: As a part of our review, we walked through the SDLC procedures and their compliance with the ABC LTD. IT Project Lifecycle Methodology / ASAP implementation methodology and project governance aspects related to scope and delivery management, monitoring and reporting procedures for scope, deliverables, schedule, costs, risks and issues. We obtained the necessary documentation for the review from the ABC Ltd. project team and ABC LTD. PMO. Findings and recommendations were shared with the project team for consideration. SAP PRE-IMPLEMENTATION REVIEW REPORT Page 5 of 53 DRAFT FOR DISCUSSION
- 4. EXECUTIVE SUMMARY D) Status of Controls and Recommendations i) Configurable Controls Review ABC Ltd. configurable controls: Status of Control as on Report issue date Business Process Total Controls Initial Observations Business To be validated in a Compliant Requirement future assessment Record to Report 10 4 9 0 1 Acquire to Retire 6 4 6 0 0 Procure to Pay 19 14 14 0 5 Order to Cash 10 5 9 1 0 Inventory 3 3 3 0 0 TOTAL 48 30 41 1 6 SAP PRE-IMPLEMENTATION REVIEW REPORT Page 6 of 53 DRAFT FOR DISCUSSION
- 5. EXECUTIVE SUMMARY Additional Configurable Controls: Total Status of Control as on Report issue date Control Applicable Control Not Applicable Business Process Recommended for ABC Ltd. for ABC Ltd. Business To be validated in a Controls Compliant Requirement future assessment Record to Report 3 3 0 1 0 2 Procure to Pay 8 5 3 5 0 0 Order to Cash 7 2 5 1 0 1 Inventory 2 1 1 1 0 0 TOTAL 20 11 9 8 0 3 Status Definitions Compliant Controls configured in SAP post recommendation Business Requirement Controls cannot be configured for valid business requirements To be validated in a future assessment Controls to be assessed on a future data after necessary changes made in SAP Additional Recommendations for Configurable Controls • We provided 7 high-level recommendations based on the trends we observed in ABC Ltd. and in alignment with the leading practices for similar scale SAP implementations. SAP PRE-IMPLEMENTATION REVIEW REPORT Page 7 of 53 DRAFT FOR DISCUSSION
