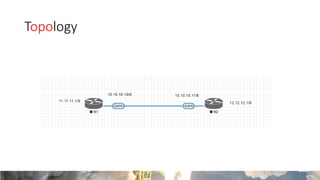
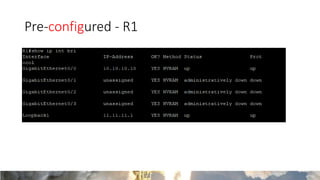
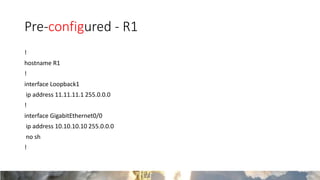
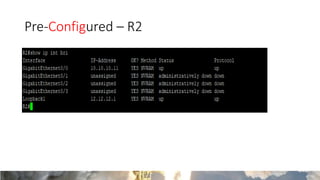
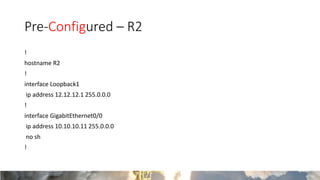
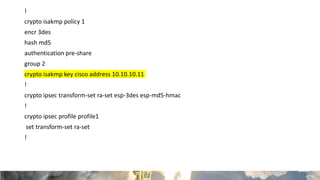
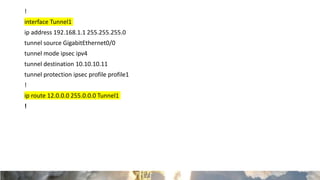
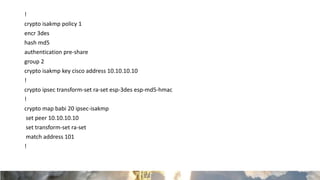
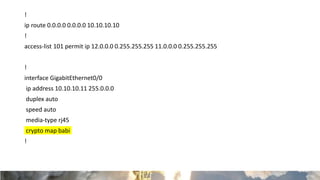
This document provides a guide for setting up a site-to-site VPN between two Cisco IOS routers, one using route-based VPN and the other using policy-based VPN. It includes pre-configured router settings, detailed configuration steps for both routers (R1 and R2), and verification references for successful implementation. The process focuses on crypto policies and IP address assignments to establish secure connections.