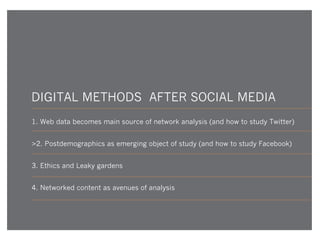
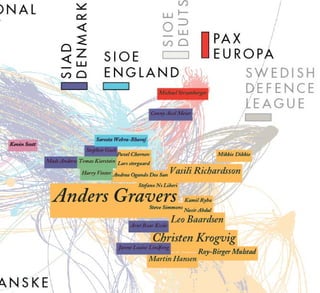
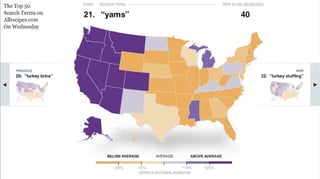
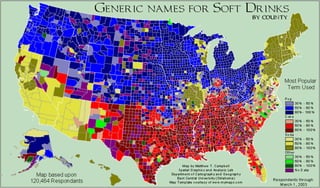
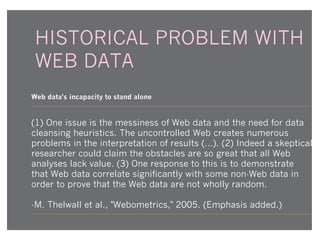
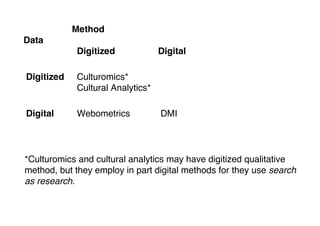
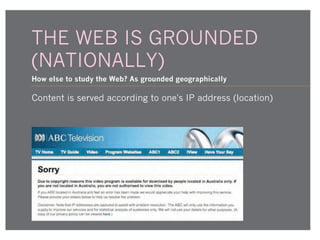
The document explores the evolution and current state of digital methods, particularly in relation to social media and the web, highlighting historical, theoretical, and empirical approaches in internet research. Key themes include the challenges of using web data, methods for analyzing cultural and social phenomena, and the importance of recognizing the influence of geography and culture in online studies. It also discusses various frameworks like cultural analytics and culturomics, and evaluates the implications of social media data in contemporary research methodologies.








![WEB AS DATA
Web data as offering the previously impossible and unacceptable
The Internet offers an entirely different channel for understanding
what people are saying...
Tracing the spread of arguments, rumors, or positions about
political and other issues in the blogosphere…
[T]he concerns of an electorate become visible in the searches
they conduct. They offer ample opportunities for research that
would otherwise be impossible or unacceptable.
Lazer et al., Computational Social Science, Science, 323, 2009.](https://image.slidesharecdn.com/rogersdigitalmethodsaftersocialmedianov2013optimized-131203051008-phpapp01/85/Rogers-digitalmethodsaftersocialmedia-nov2013_optimized_-17-320.jpg)










![TWITTER III - DATA MARKET
Terms of service change and Twitter softens blow by donating to Library of Congress - e
"[Twitter is not] considering the myriad number of PhD students
who basically just lost their work, or the researchers that were
close to saying something meaningful and now have no way
to do it" (Watter, 2011).
Must you work at Twitter to use it as researcher?](https://image.slidesharecdn.com/rogersdigitalmethodsaftersocialmedianov2013optimized-131203051008-phpapp01/85/Rogers-digitalmethodsaftersocialmedia-nov2013_optimized_-63-320.jpg)