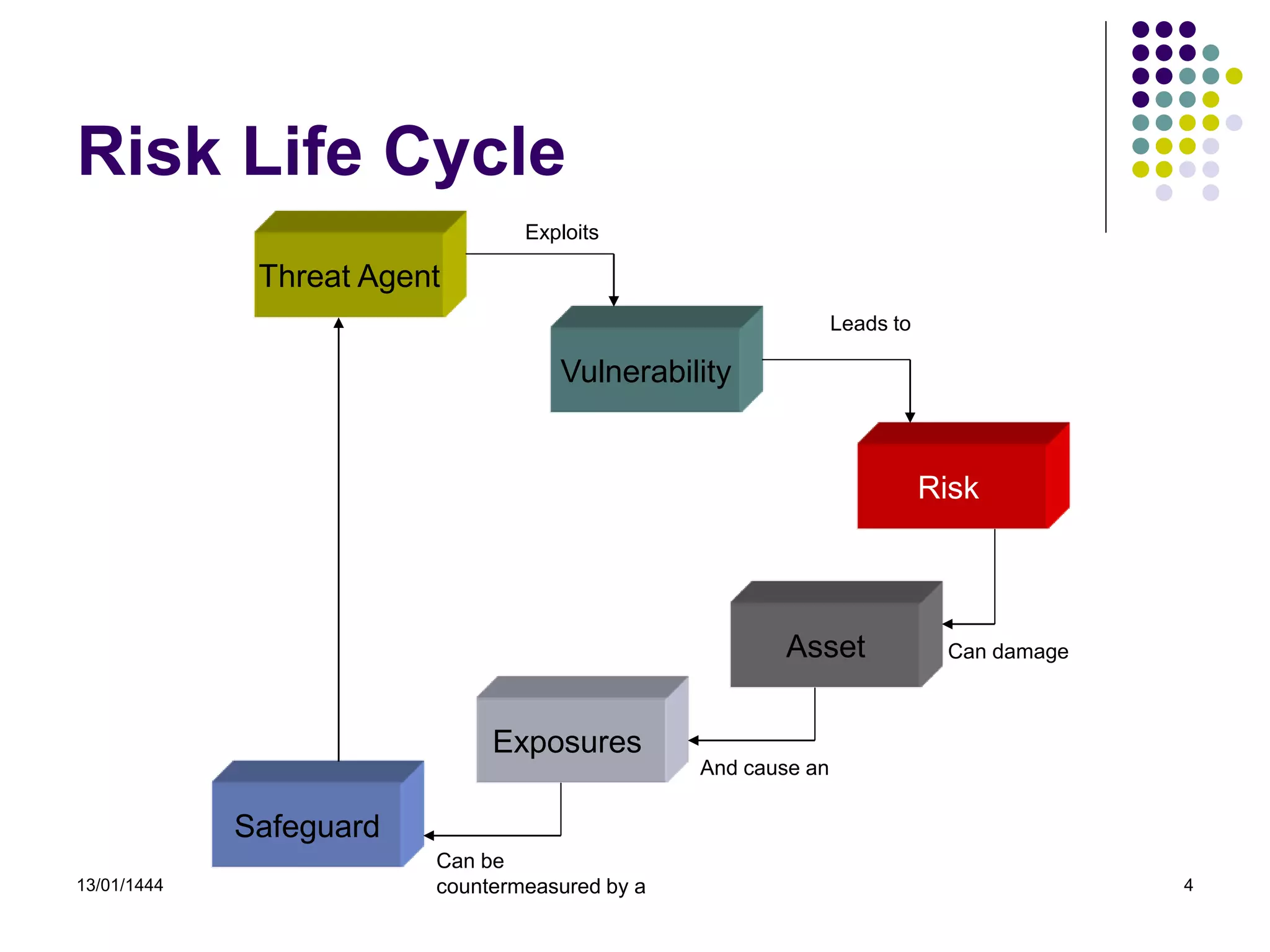
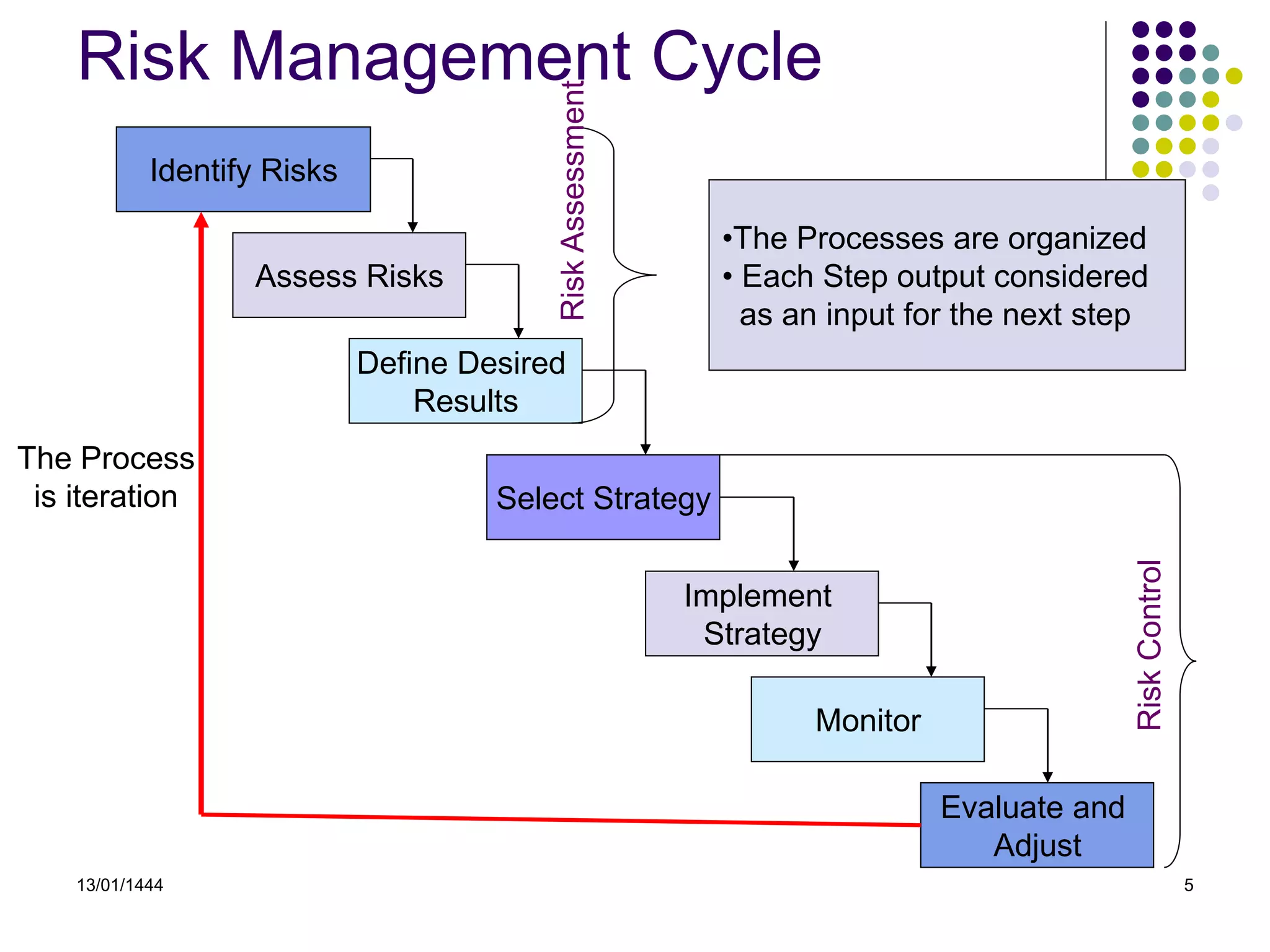
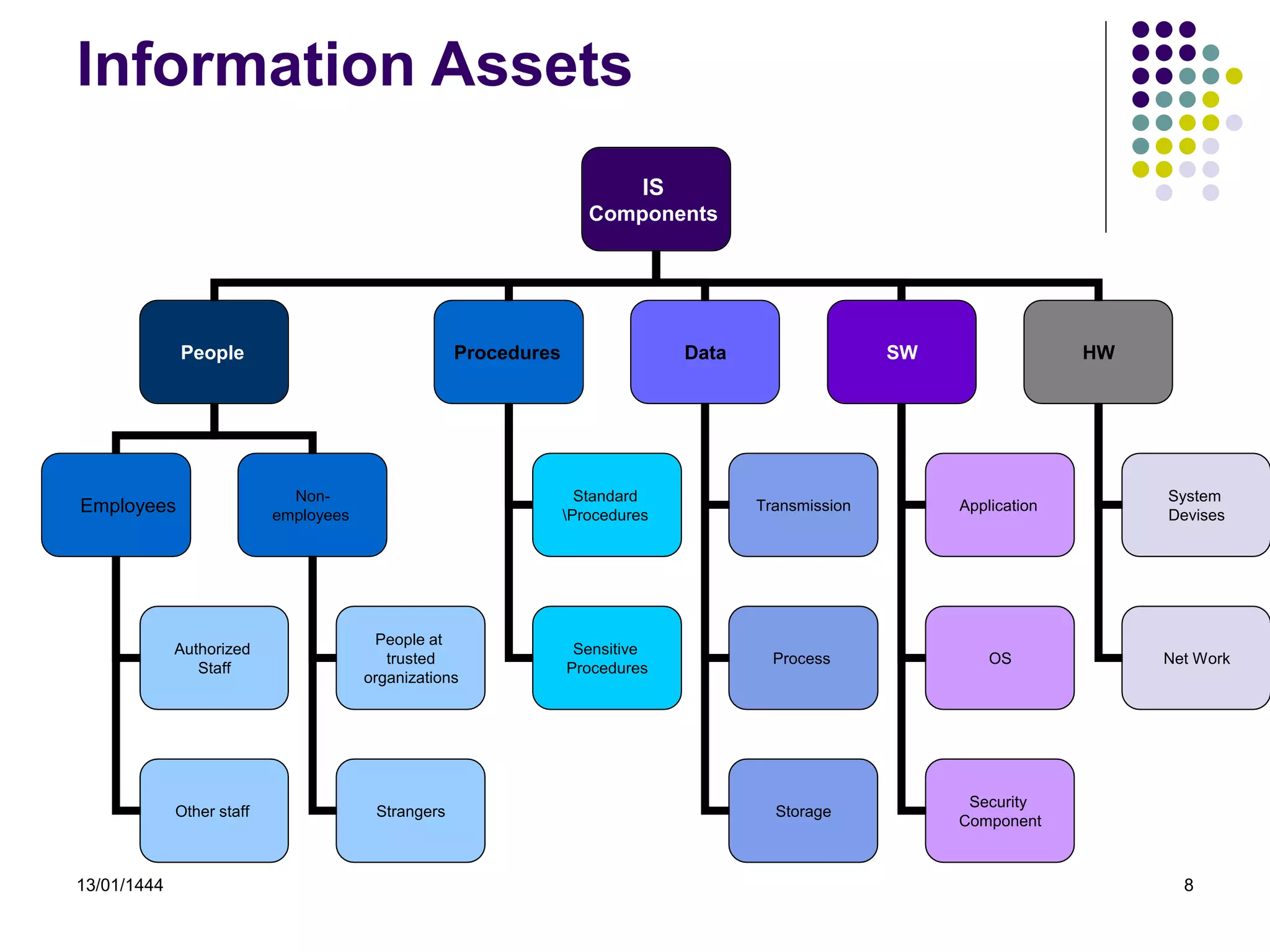
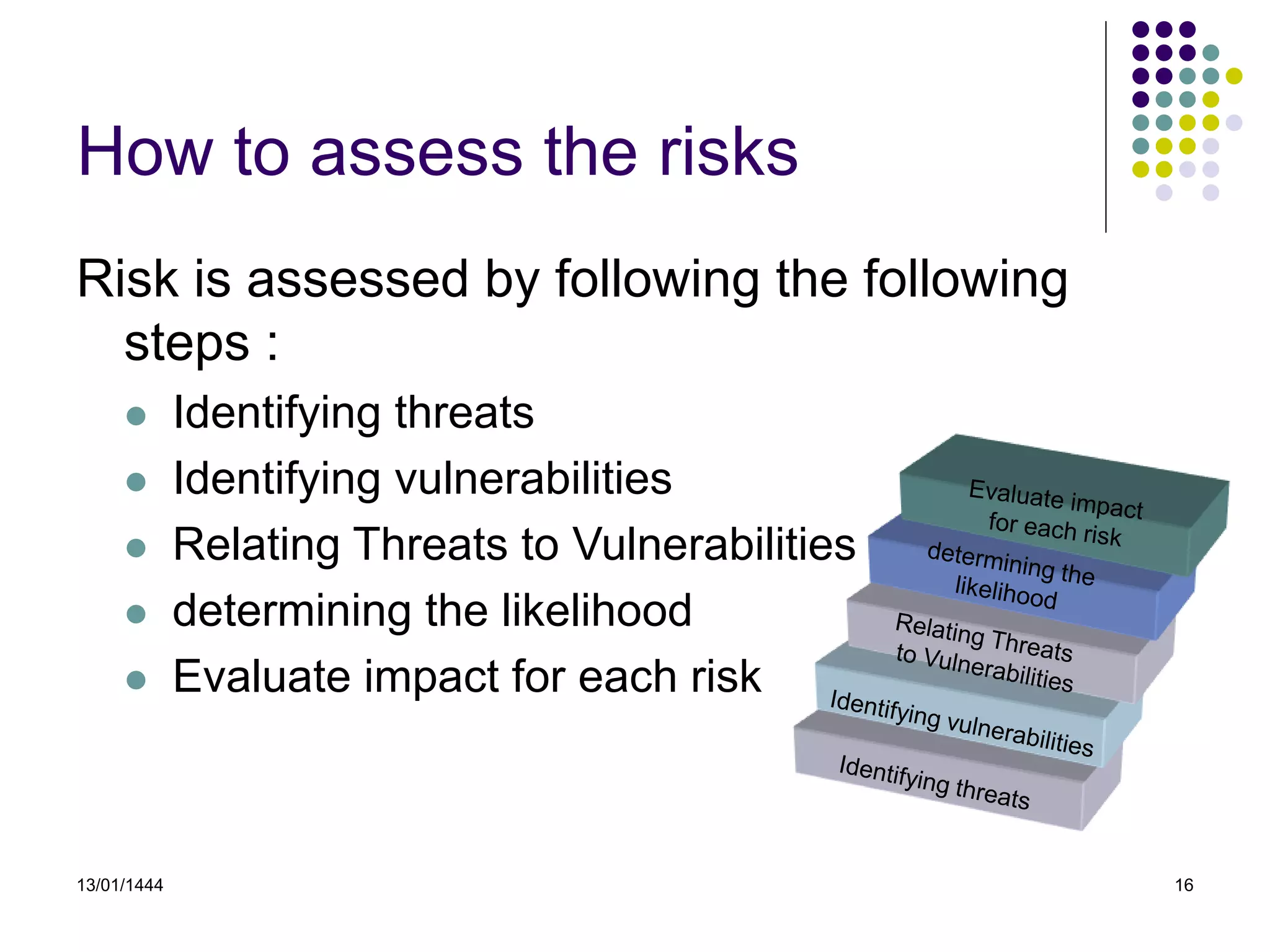
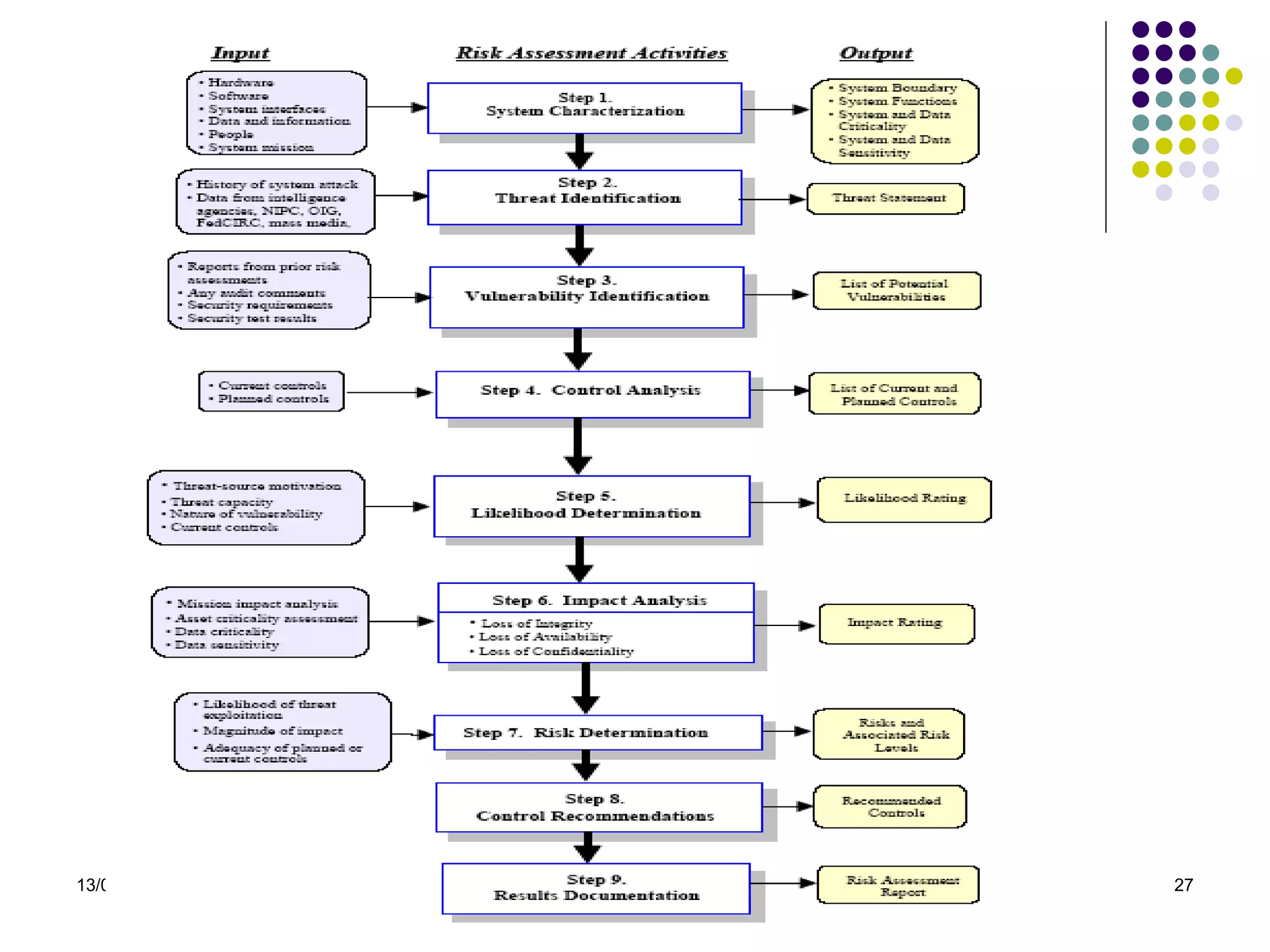
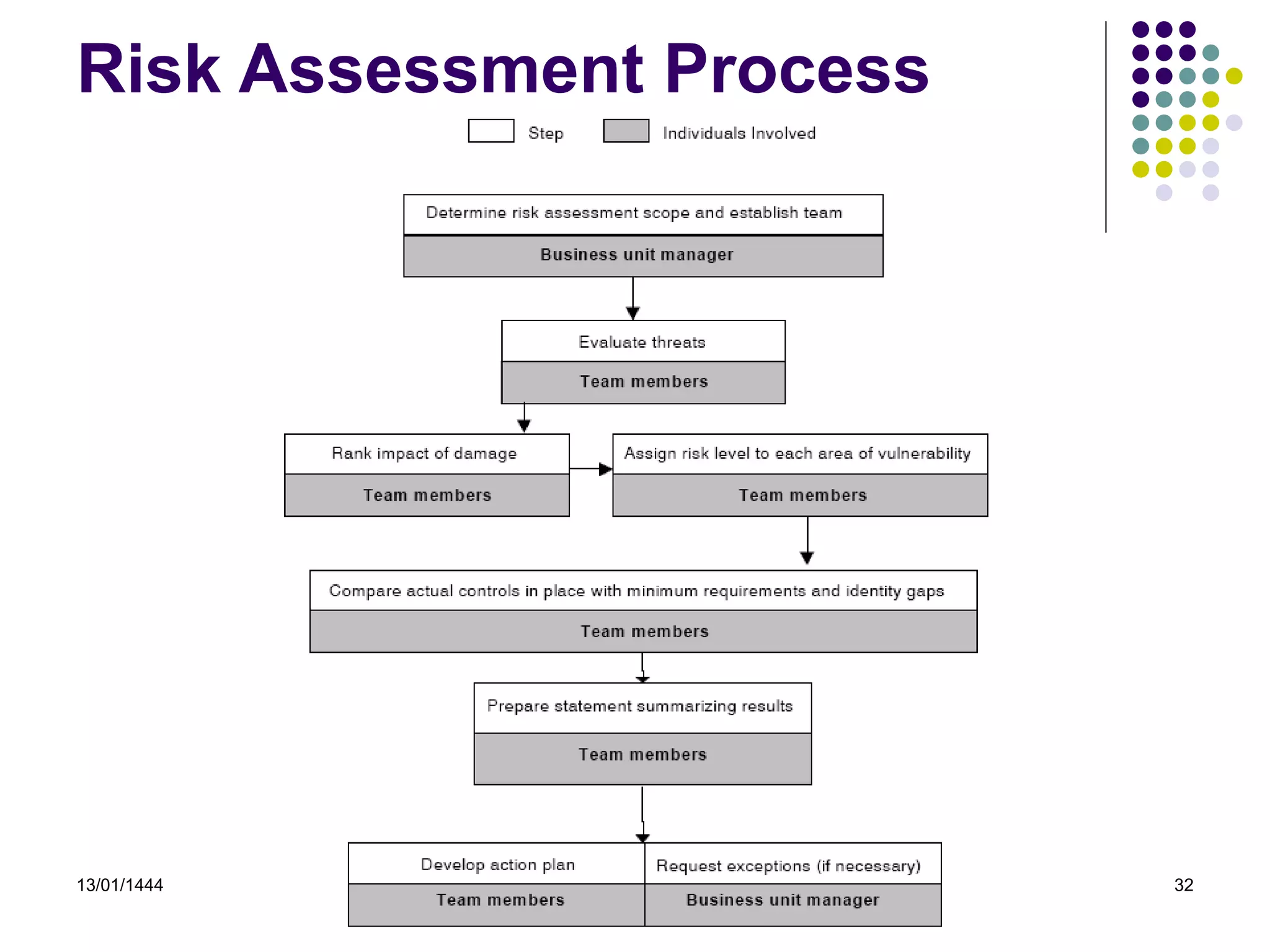
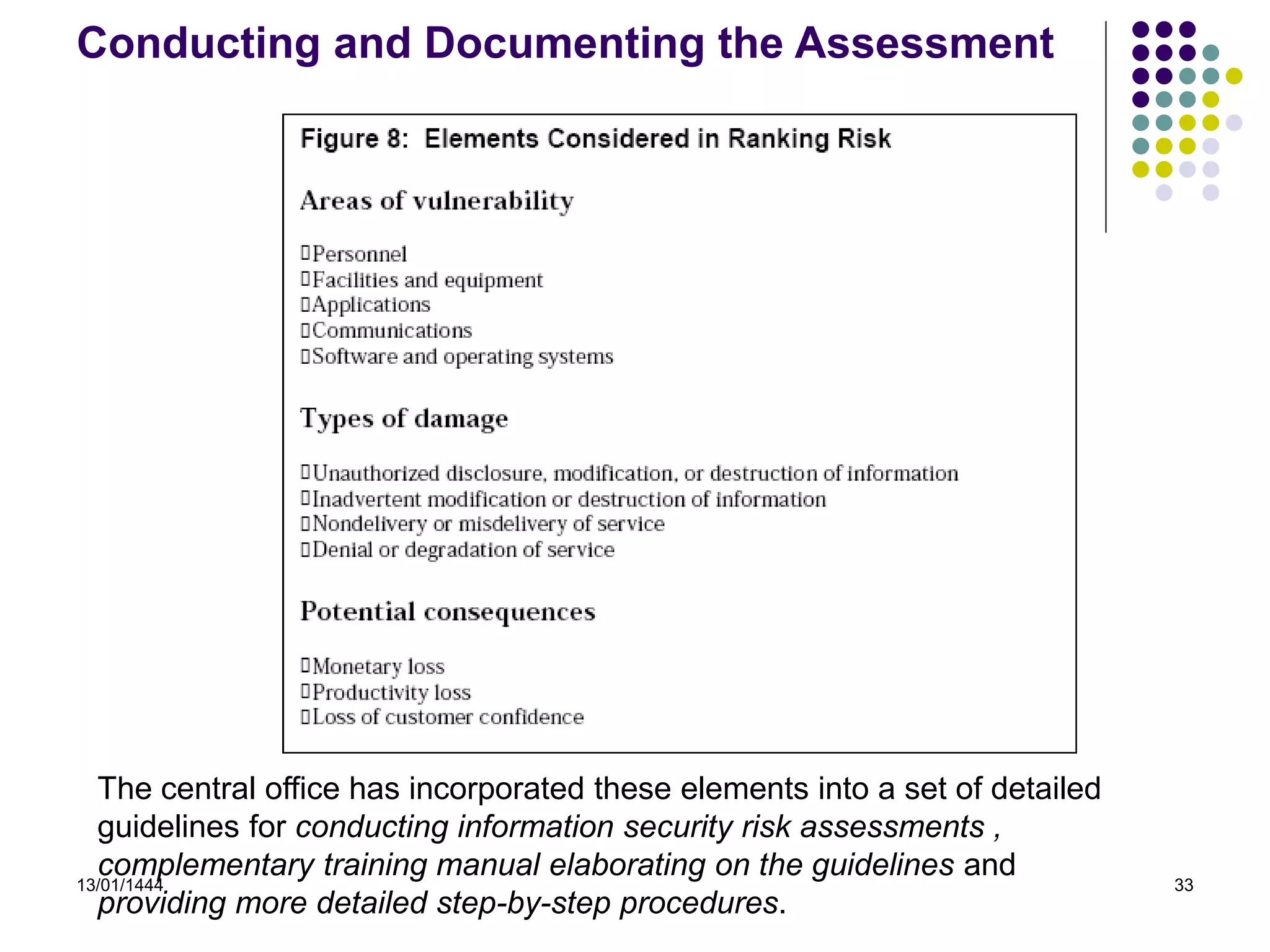
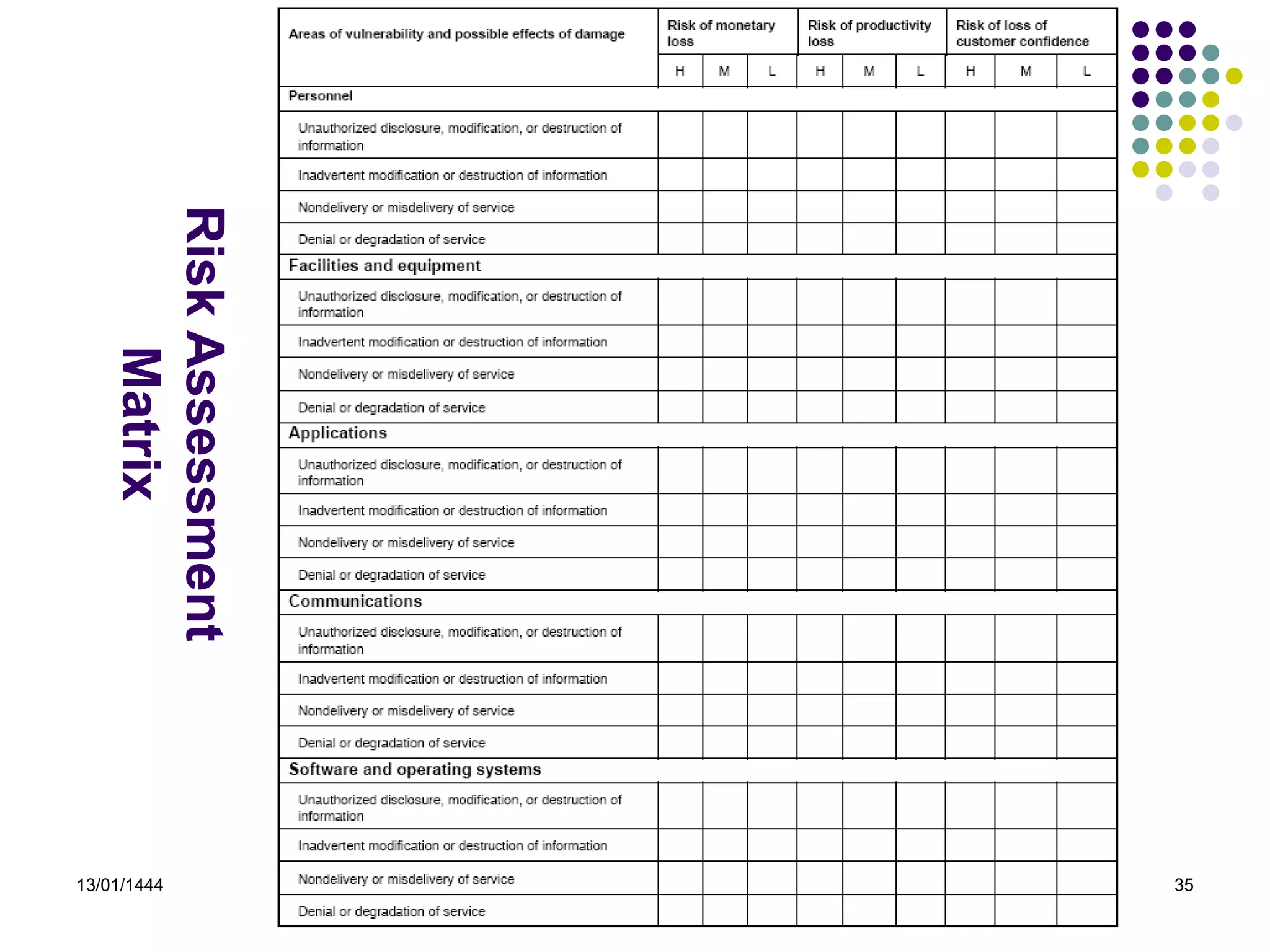
This document provides an overview of risk identification and assessment. It defines risk and risk management, and outlines the key steps in the risk management cycle including risk identification, assessment, and analysis. Methods of risk assessment are also discussed, including qualitative, quantitative and hybrid approaches. National Institute of Standards and Technology (NIST) methodology is explained as one of the common risk assessment methodologies used. The responsibilities of different parties in conducting risk assessments are highlighted. A case study on risk assessment of a regulatory organization is presented to demonstrate the process.