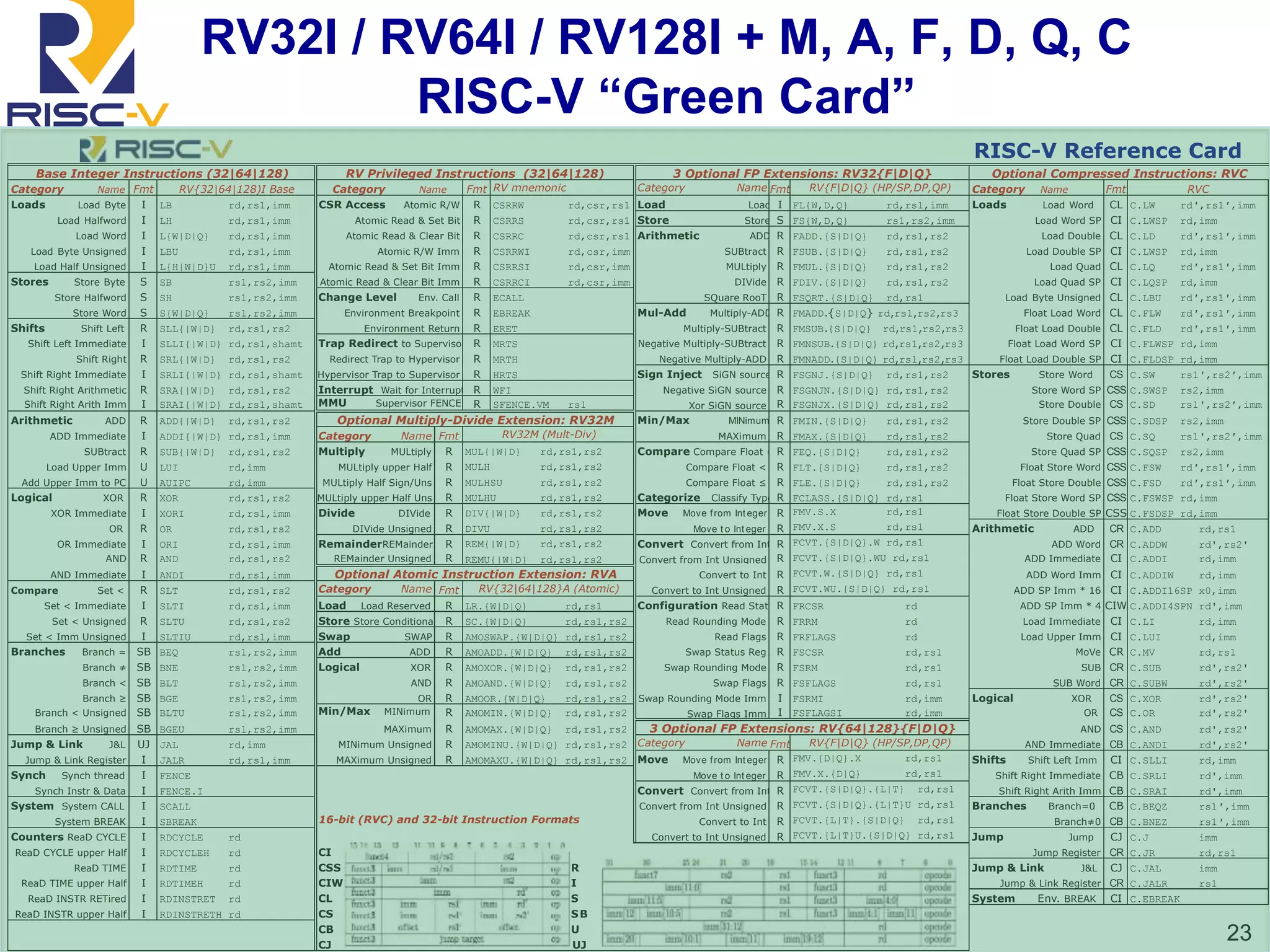
This document discusses the RISC-V instruction set architecture (ISA). It begins by providing background on how ISAs determine what processors can be used in different markets. It then describes the origins of RISC-V as a clean-slate open ISA developed at UC Berkeley to address limitations of prior proprietary ISAs. The document outlines key attributes of RISC-V that differentiate it, such as its modularity, extensibility, and support for a wide range of implementations through standard extensions.












![RISC-V Standard Base ISA Details
▪ 32-bit fixed-width, naturally aligned instructions
▪ 31 integer registers x1-x31, plus x0 zero register
▪ rd/rs1/rs2 in fixed location, no implicit registers
▪ Immediate field (instr[31]) always sign-extended
▪ Floating-point adds f0-f31 registers plus FP CSR, also
fused mul-add four-register format
▪ Designed to support PIC and dynamic linking
14](https://image.slidesharecdn.com/riscv-20160507-patterson-160507071645/75/Riscv-20160507-patterson-14-2048.jpg)




![Proposed V Extension State
x0
x1
x31
f0
f1
f31
Standard RISC-V scalar x
and f registers
p0[0]
p1[0]
p7[0]
p0[1]
p1[1]
p7[1]
p0[MVL-1]
p1[MVL-1]
p7[MVL-1]
8 vector predicate registers, with
1 bit per element
vlr
vcfg
Vector
configuration
CSR
Vector length
CSR
v0[0]
v1[0]
v31[0]
v0[1]
v1[1]
v31[1]
v0[MVL-1]
v1[MVL-1]
v31[MVL-1]
Up to 32 vector data registers, v0-v31,
of at least 4 elements each, with
variable bits/element (8,16,32,64,128)
MVL is maximum vector length,
implementation and configuration dependent,
but MVL >= 4](https://image.slidesharecdn.com/riscv-20160507-patterson-160507071645/75/Riscv-20160507-patterson-19-2048.jpg)