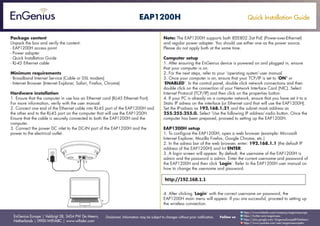
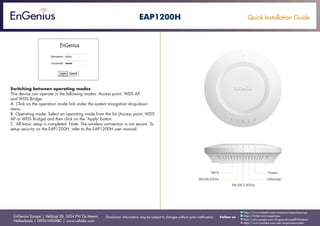
This quick installation guide summarizes the steps to set up the EnGenius EAP1200H access point. It includes unpacking the contents of the package and verifying minimum system requirements. The guide outlines connecting the access point via Ethernet cable and power adapter. It provides instructions for configuring the computer's IP settings and accessing the access point's web interface using the default IP to complete basic setup. Functionality of the access point includes operating in access point, WDS AP, or WDS bridge modes which can be selected in the web interface.