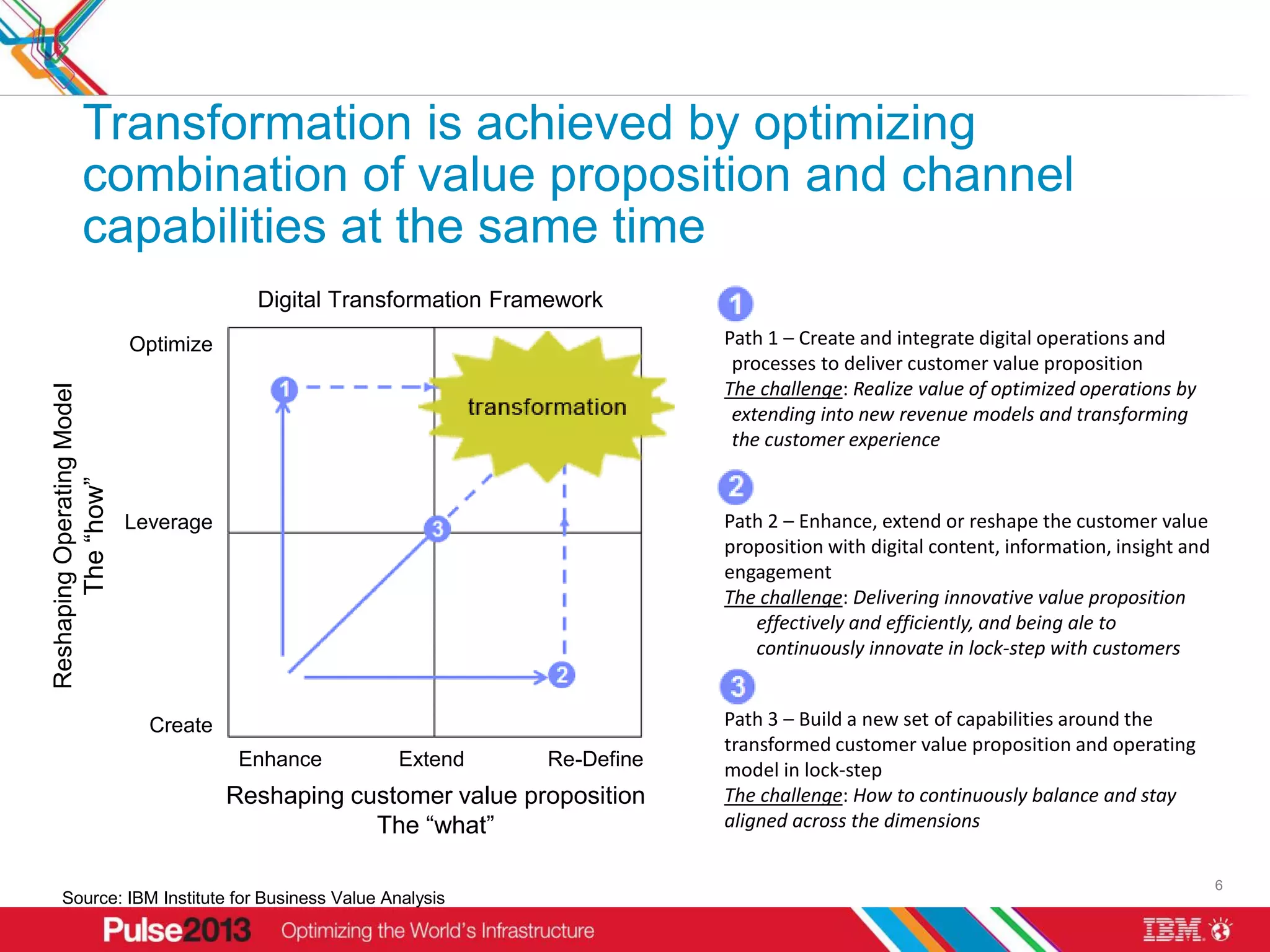
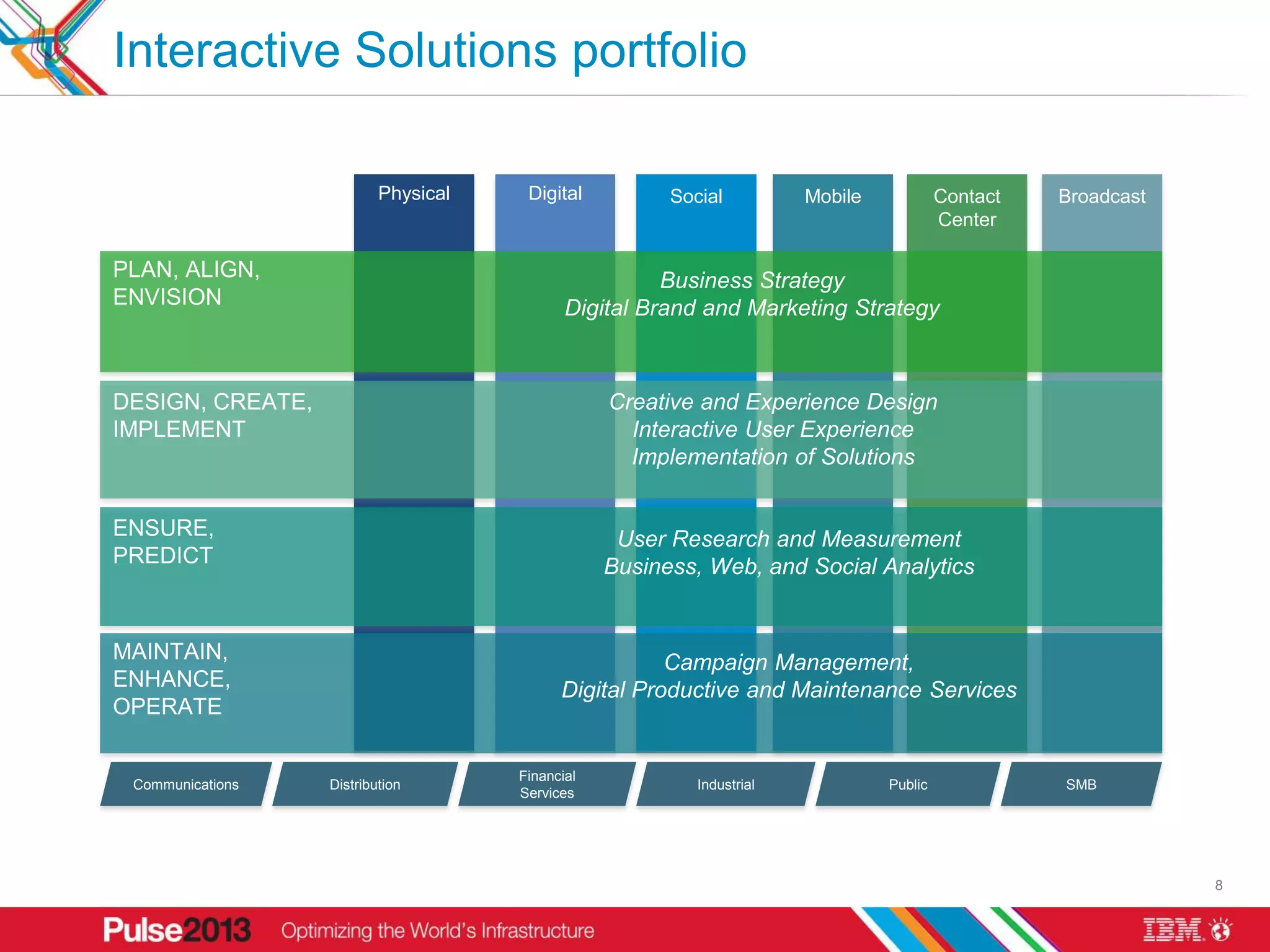
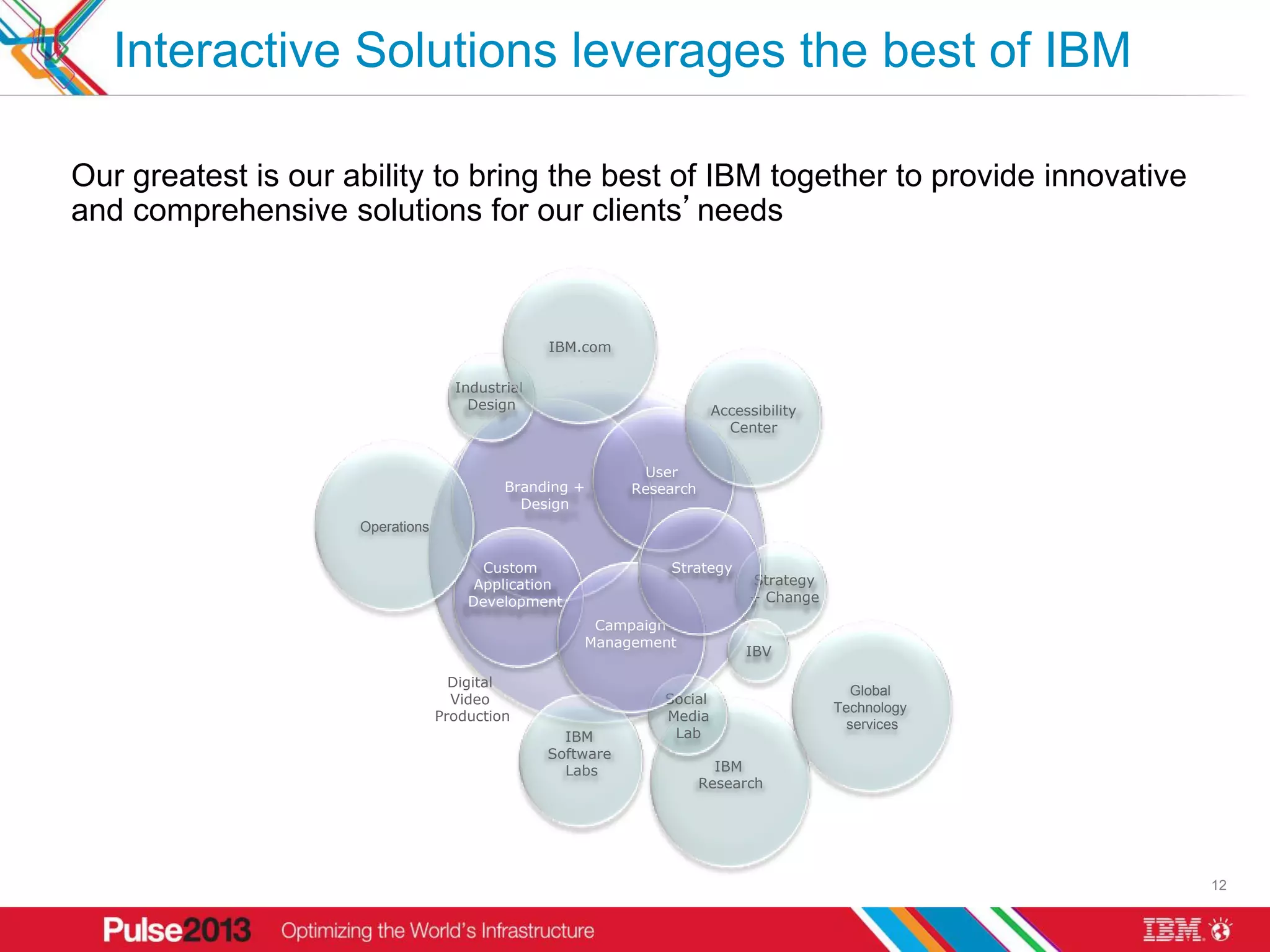
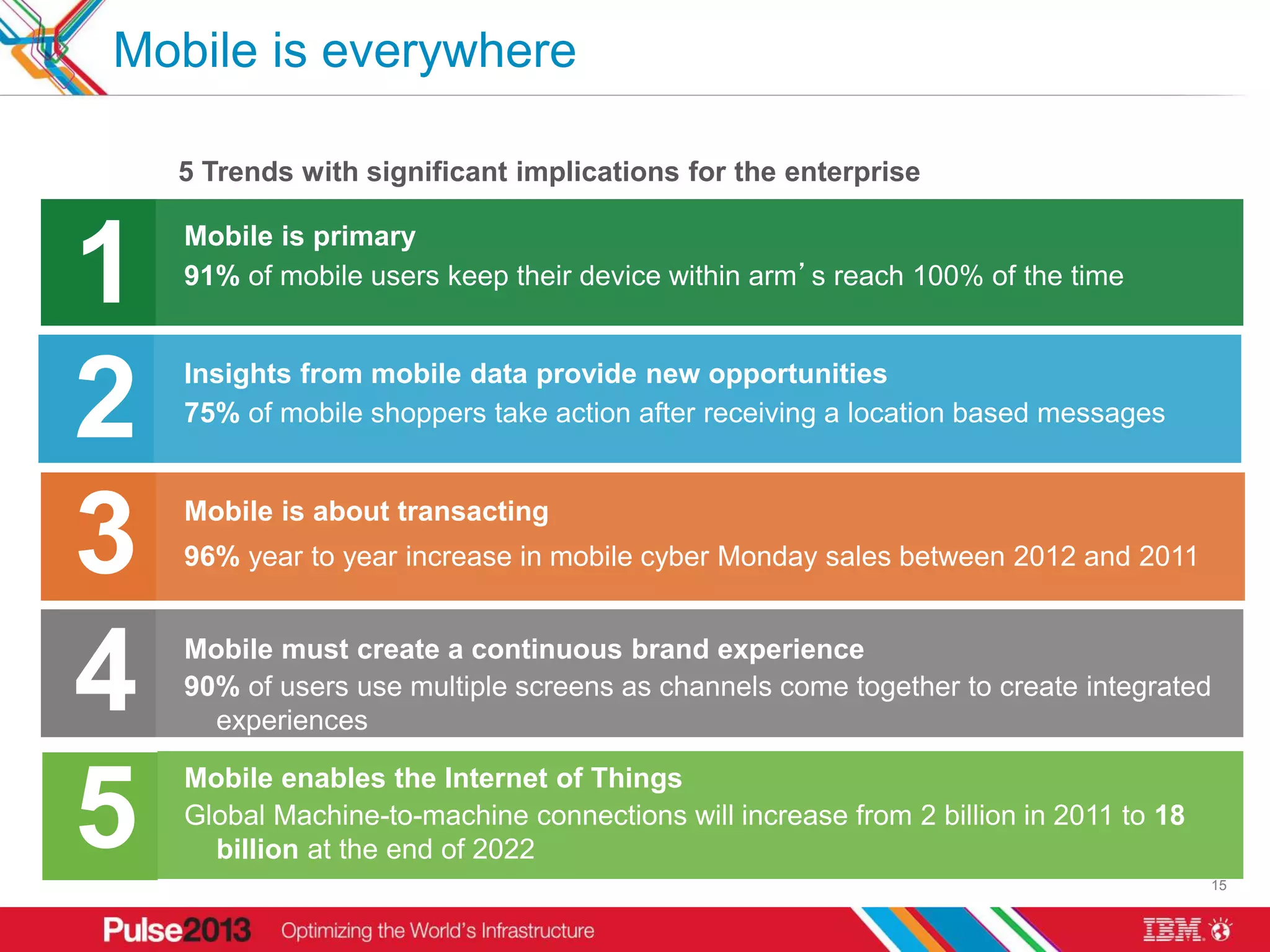
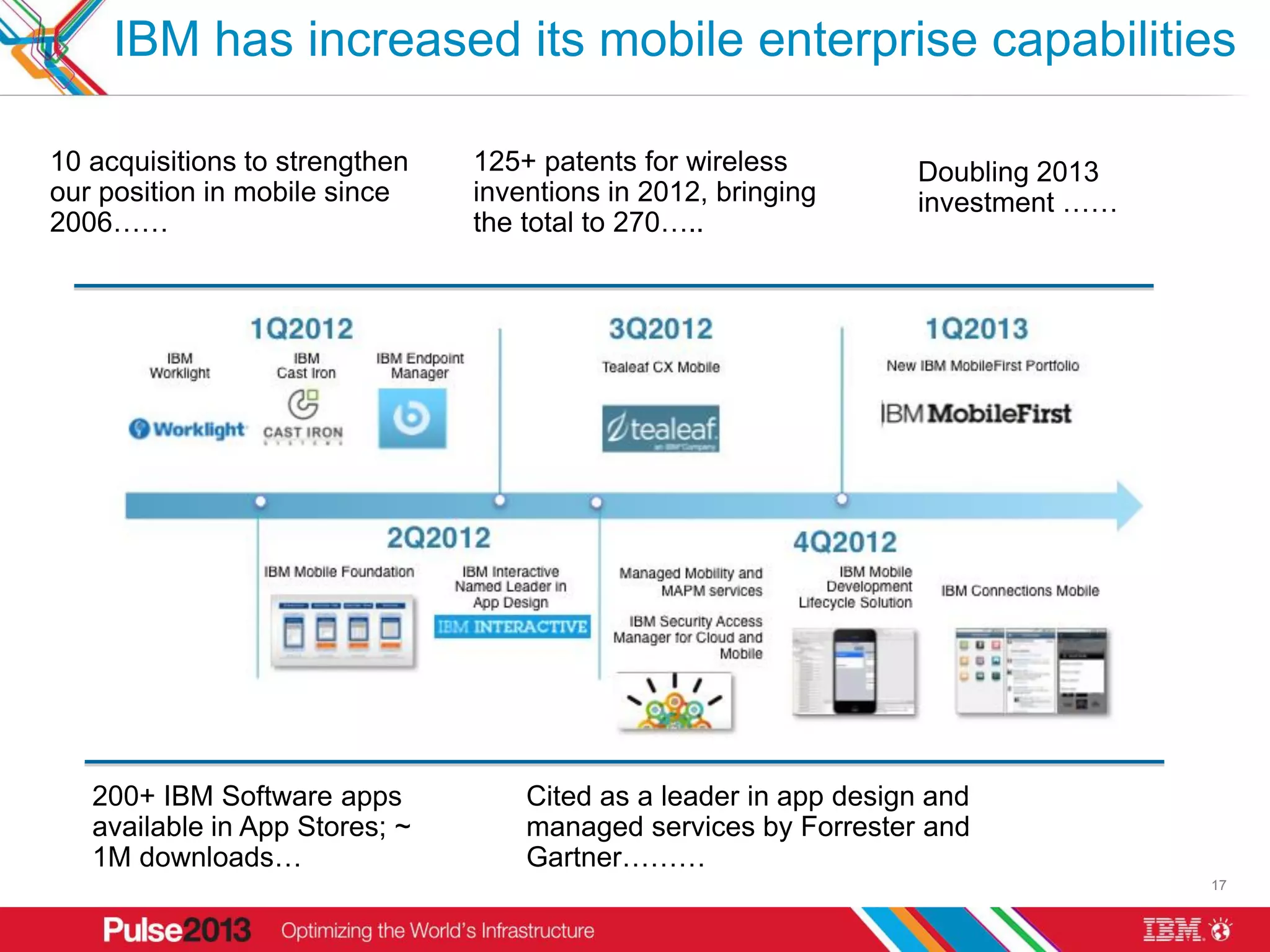
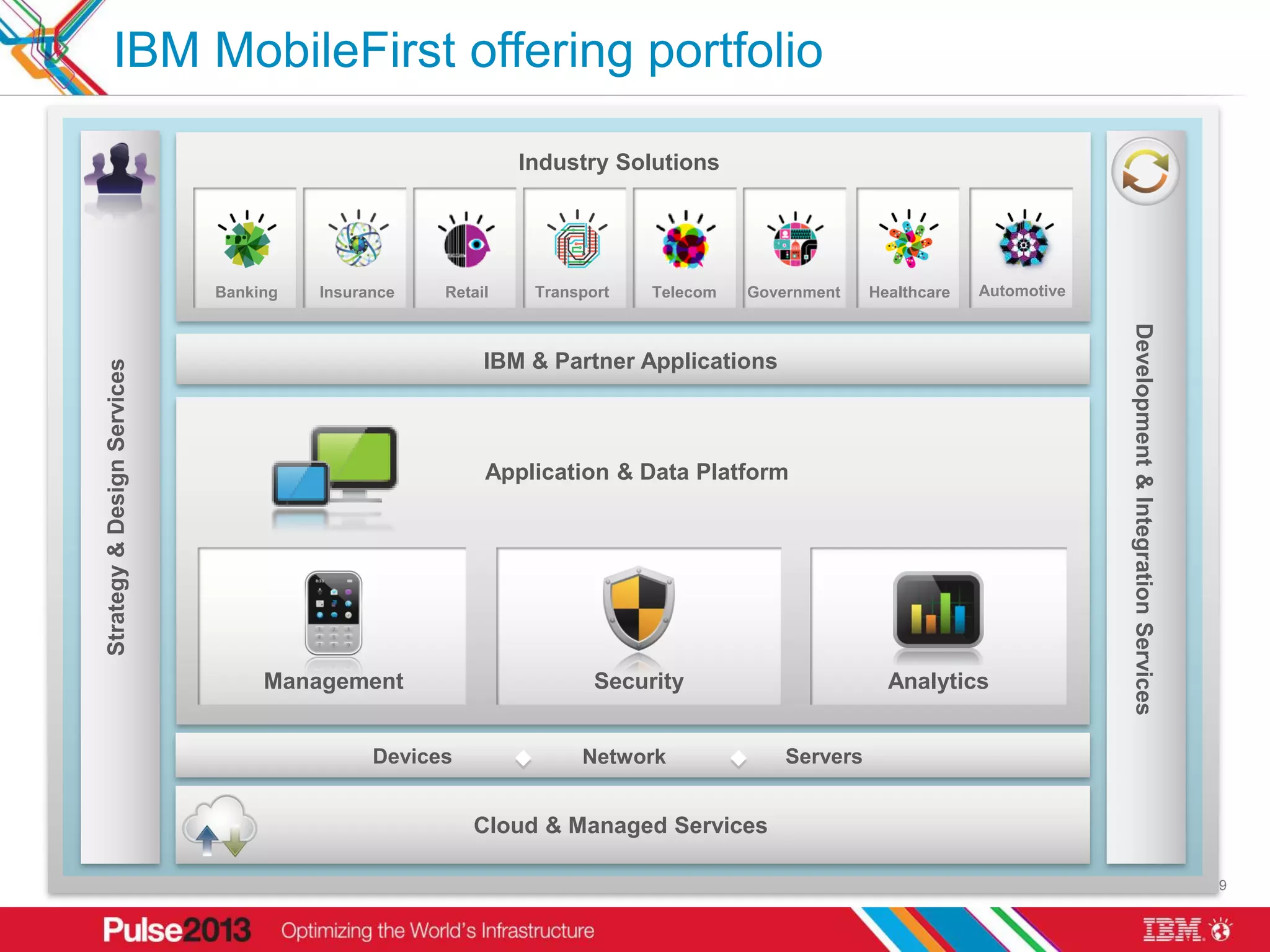
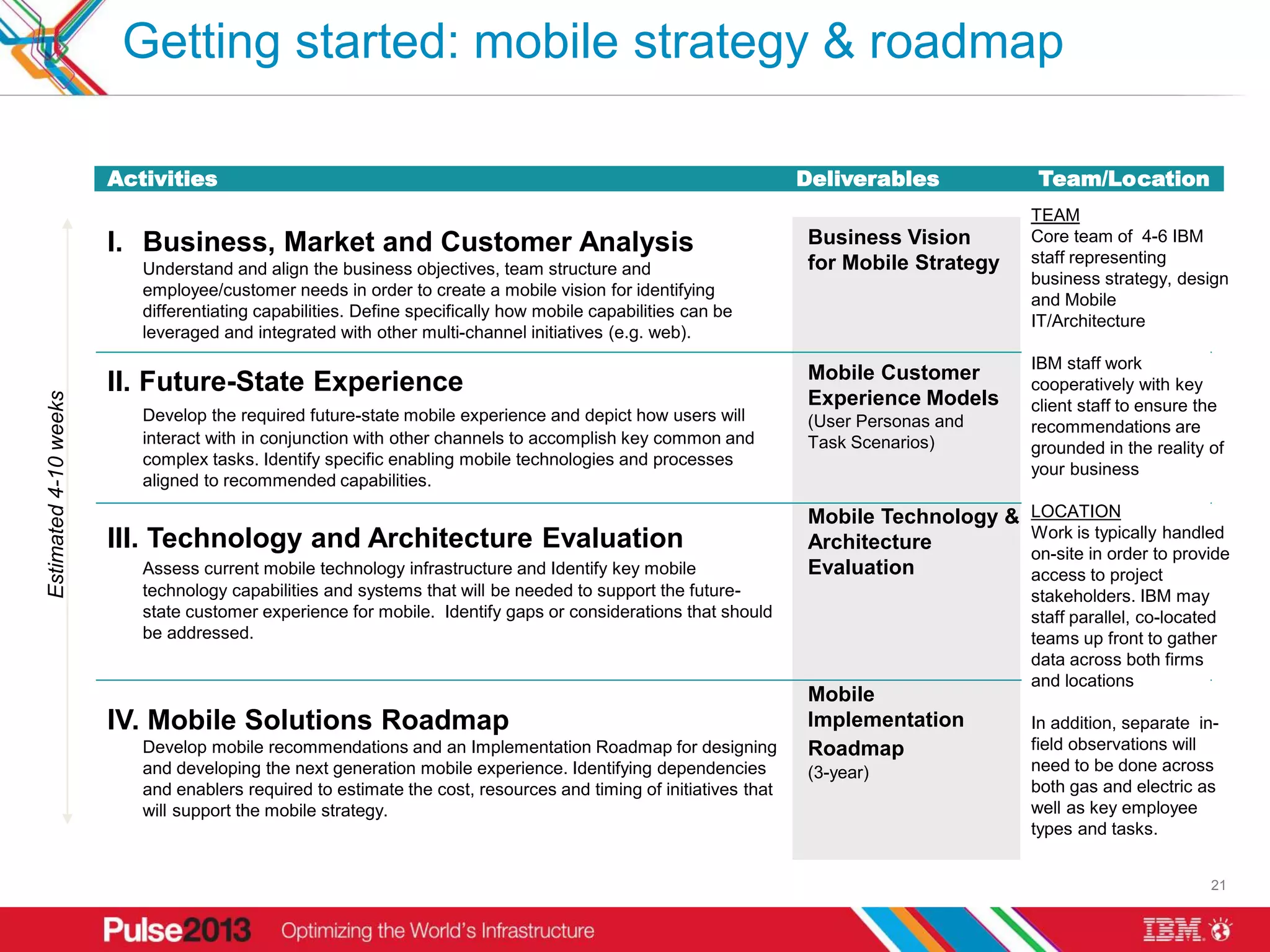
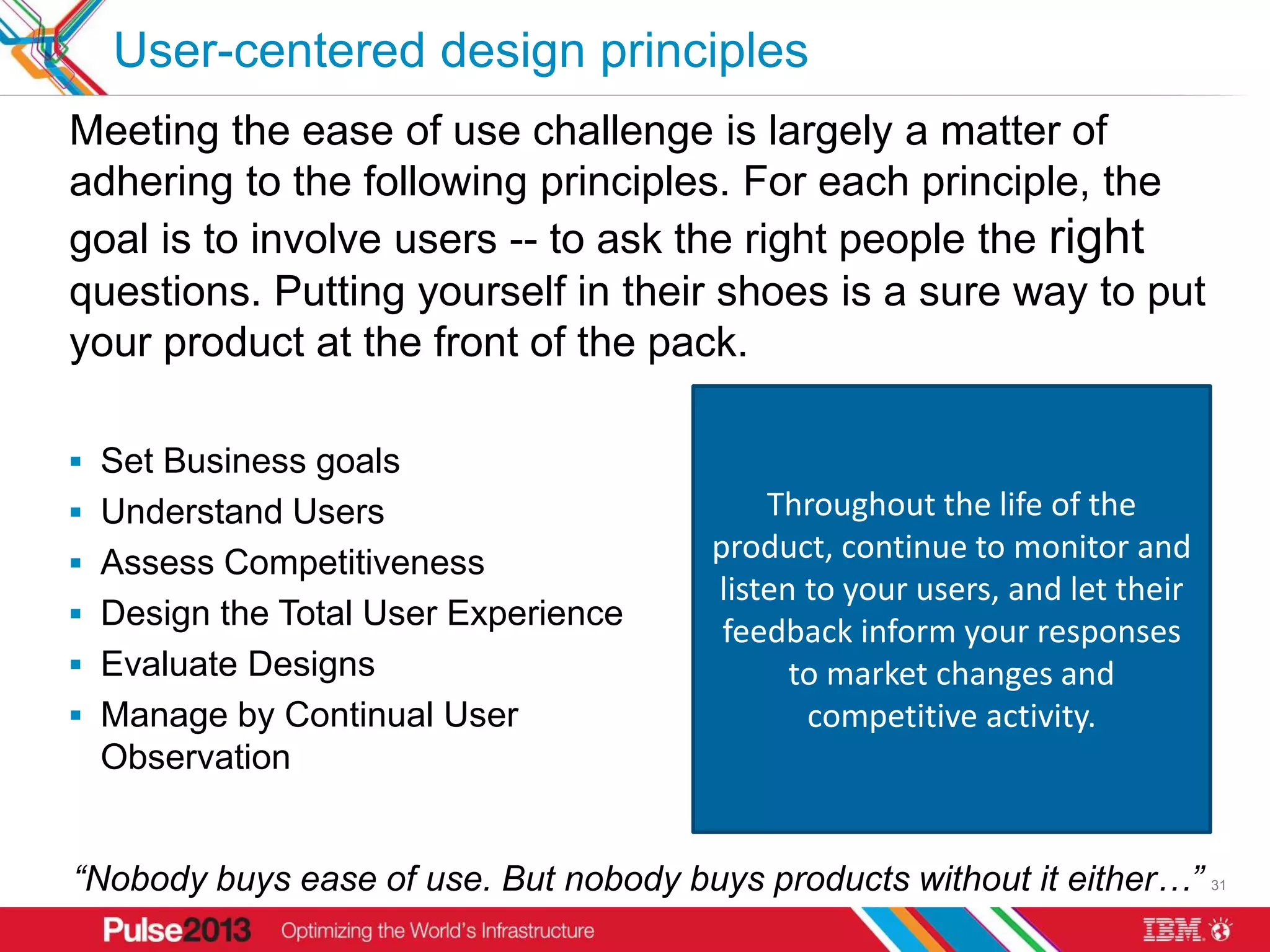
The document provides an overview of IBM's mobile strategy and user-centered design approach. It discusses (1) how mobile adoption is changing consumer and business behavior, (2) IBM's Interactive Solutions portfolio and expertise in mobile strategy, design, and technology, (3) IBM's MobileFirst offering and focus on delivering comprehensive mobile solutions, and (4) a sample mobile engagement process that assesses business needs, defines a future mobile experience, evaluates technology requirements, and develops a roadmap. The document emphasizes IBM's capabilities across mobile strategy, user experience design, and technology to help organizations transform their business in a mobile-first world.