The document discusses a research project by Dr. Marco Benini on programming systems that ensure correctness without allowing inspection of outputs. It explores the philosophical implications and technical details of abstracting data types in programming, specifically using lists, and presents a method for achieving correctness by construction in functional programming. The findings suggest that the techniques may apply broadly to various data structures and raise questions about program inspectability and computability.
![Concrete manipulation of a list
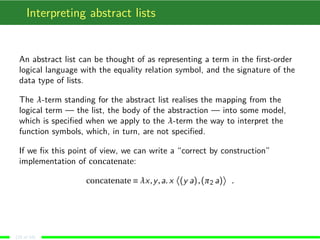
As an example of program, we consider the concatenate function.
Its specification is: “Given the lists [x1,...,xn] and [y1,...,ym], concatenate
has to return the list [x1,...,xn,y1,...,ym]”.
Usually, it is implemented as
concatenate(x,y) ≡
if x = nil then return y
else q := x
while q = nil do
p := q
q := q → tail
p → tail := y
return x
(4 of 18)](https://image.slidesharecdn.com/main-140604200842-phpapp01/85/Programming-modulo-representations-4-320.jpg)
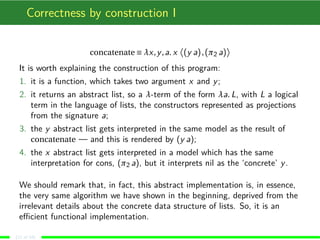
![Correctness
The previous algorithm is correct. In fact, when x = nil, it returns y,
satisfying the specification.
When x = nil, x = [x1,...,xn]. So, at the end of the i-th iteration step,
p = [xi ,...,xn] and q = [xi+1,...,xn], as it is immediate to prove by induction.
Also, the cycle terminates after n iterations, and p = [xn].
But, in the concrete representation of x, p → tail must be nil and the
assignment p → tail := y substitutes nil with y. So x becomes
[x1,...,xn,y1,...,ym], as required.
The proof sketched above uses in an essential way the concrete
representation of the x list, because the algorithm uses “list surgery”.
The algorithm, as one deduces from the proof, computes in O (|x|) steps,
and uses a constant amount of memory, apart the one used the represent
the input.
(5 of 18)](https://image.slidesharecdn.com/main-140604200842-phpapp01/85/Programming-modulo-representations-5-320.jpg)
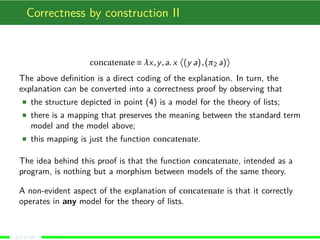
![A functional derivation
Dropping list surgery, we can use the abstract formalisation of lists directly:
concatenate(x,y) ≡
if x = nil then return y
else return cons (hdx) (concatenate(tlx,y))
where hd and tl return the head and the tail of its argument, respectively.
Of course, this is a functional program, and it is justified by the following
reasoning, which can be immediately converted into a formal correctness
proof by induction on the structure of x:
1. we want that concatenate([x1,...,xn],[y1,...,ym]) = [x1,...,xn,y1,...,ym],
2. as before, if x = nil, the result is just y
3. when x = nil, concatenate([x1,...,xn],[y1,...,ym]) yields the same result
as consx1 (concatenate([x2,...,xn],[y1,...,ym]));
4. in the line above, the recursive application decreases the length of the
first argument, so recursion terminates after n steps, yielding the result.
(6 of 18)](https://image.slidesharecdn.com/main-140604200842-phpapp01/85/Programming-modulo-representations-6-320.jpg)
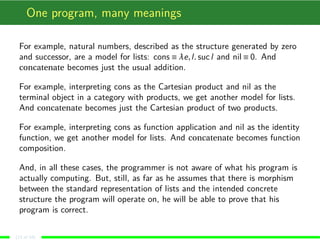
![Abstracting over lists
We formalised a list [x1,...,xm] as consx1 (consx2 (...(consxm nil)...)). We
can use a slightly different representation1:
λn,c. c x1 (c x2 (...(c xm n)...)) .
The key idea is to abstract over the structure of the data type, making it
part of the representation of the datum.
Alternatively, we can interpret this representation A as the abstract datum,
and the concrete one, C can be obtained by passing the instances of the
constructors to A.
For example, the standard formalisation is obtained by (Anilcons).
1As far as I know, the general algorithm to derive such a representation is due to
Böhm and Berarducci, and it can be traced back to Church. But the paper of Böhm and
Berarducci is subtle as it relies on a typed λ-system.
(8 of 18)](https://image.slidesharecdn.com/main-140604200842-phpapp01/85/Programming-modulo-representations-8-320.jpg)
![Abstracting one step further
In fact, it is possible, by assuming that the λ-calculus (type theory) we are
using has pairs, to abstract a bit further, so to completely hide the data
type. Instead of writing [x1,...,xm] as
λn,c. c x1 (c x2 (...(c xm n)...)) ,
we may substitute the constructors with the data type a, which is a 2-tuple,
the first element being the concrete representation for nil, the second being
the concrete representation for cons:
λa. π2 ax1 (π2 ax2 (...(π2 axm (π1 a))...)) ,
where π1 and π2 are the standard projections.
In this way, the programmer does not know how the list is concretely
represented, but simply that the first element of a is how to interpret nil and
the second element of a is how to represent cons.
(9 of 18)](https://image.slidesharecdn.com/main-140604200842-phpapp01/85/Programming-modulo-representations-9-320.jpg)