Procurement Mind Map
•Download as PPTX, PDF•
0 likes•23 views
Procurement Mind Map.pptx
Report
Share
Report
Share
Recommended
Azure_DP_300_Vocabulary_Cards.pptx

This document contains definitions and explanations of various Azure database and networking terminology. It includes definitions for concepts like license mobility, constant time, provisioned compute tiers, serverless compute tiers, elastic query, ExpressRoute connections, peering, BGP sessions, Microsoft peering and private peering, Azure virtual networks, hybrid Azure Active Directory, Azure Sentinel, geo-replicated databases, nodes, snapshots, Always On availability groups, auto-failover groups, Azure Arc, Azure SQL Edge, row-level security, privilege escalation, Azure IoT Edge, the Parquet format, Microsoft Volume Licensing, license mobility, software assurance, scale automatically, TDS, Azure Hybrid Use Benefits, Azure Key Vault, the principle
Azure-Interview-Questions-Slides.pptx

This document contains 30 interview questions about Microsoft Azure. It begins with basic questions like what is Azure and the Azure portal. It then covers Azure roles, storage, networking, security, databases, virtual machines, and other services. The questions range from conceptual to technical and would be useful for someone preparing for an Azure interview.
01_DP-300T00A-Intro.pptx

Module 1 provides an introduction to Azure database administration. It describes the roles of Azure database administrators and other data platform roles. It also describes the different SQL deployment options on Azure including SQL Server VMs, Azure SQL Database, and Azure SQL Managed Instance. Key features of each option like high availability, backups, and scaling are discussed.
02_DP_300T00A_Plan_implement.pptx

This document provides an overview of deploying and configuring Azure SQL resources. It discusses deploying SQL Server on virtual machines using various methods like the Azure portal, PowerShell scripts, and ARM templates. It also covers deploying SQL databases using the PaaS offerings like single databases, elastic pools, and hyperscale. Key aspects covered include high availability and disaster recovery options, storage configurations, licensing models, and migration strategies.
07_DP_300T00A_HA_Disaster_Recovery.pptx

This document provides an overview of high availability and disaster recovery strategies for Azure SQL solutions. It discusses recovery time and point objectives and available options like Always On availability groups and failover cluster instances. It also covers backup and restore, factors to consider in a HADR strategy, and differences between infrastructure as a service and platform as a service solutions. Specific options covered include availability sets, availability zones, log shipping, Azure Site Recovery, temporal tables, active geo-replication, and auto failover groups.
06_DP_300T00A_Automate.pptx

This document provides an overview of automating database tasks for Azure SQL. It covers automating deployments using ARM templates, Bicep, and tools like PowerShell and CLI. It also discusses creating scheduled SQL Server Agent jobs for maintenance activities and configuring alerts and notifications. Finally, it introduces automation options for Azure PaaS services like Azure Policy, Automation, elastic jobs, and Logic Apps.
05_DP_300T00A_Optimize.pptx

This document provides an overview of Module 5: Optimize query performance in Azure SQL. The module contains 3 lessons that cover analyzing query plans, evaluating potential improvements, and reviewing table and index design. Lesson 1 explores generating and comparing execution plans, understanding how plans are generated, and the benefits of the Query Store. Lesson 2 examines database normalization, data types, index types, and denormalization. Lesson 3 describes wait statistics, tuning indexes, and using query hints. The lessons aim to help administrators optimize query performance in Azure SQL.
Recommended
Azure_DP_300_Vocabulary_Cards.pptx

This document contains definitions and explanations of various Azure database and networking terminology. It includes definitions for concepts like license mobility, constant time, provisioned compute tiers, serverless compute tiers, elastic query, ExpressRoute connections, peering, BGP sessions, Microsoft peering and private peering, Azure virtual networks, hybrid Azure Active Directory, Azure Sentinel, geo-replicated databases, nodes, snapshots, Always On availability groups, auto-failover groups, Azure Arc, Azure SQL Edge, row-level security, privilege escalation, Azure IoT Edge, the Parquet format, Microsoft Volume Licensing, license mobility, software assurance, scale automatically, TDS, Azure Hybrid Use Benefits, Azure Key Vault, the principle
Azure-Interview-Questions-Slides.pptx

This document contains 30 interview questions about Microsoft Azure. It begins with basic questions like what is Azure and the Azure portal. It then covers Azure roles, storage, networking, security, databases, virtual machines, and other services. The questions range from conceptual to technical and would be useful for someone preparing for an Azure interview.
01_DP-300T00A-Intro.pptx

Module 1 provides an introduction to Azure database administration. It describes the roles of Azure database administrators and other data platform roles. It also describes the different SQL deployment options on Azure including SQL Server VMs, Azure SQL Database, and Azure SQL Managed Instance. Key features of each option like high availability, backups, and scaling are discussed.
02_DP_300T00A_Plan_implement.pptx

This document provides an overview of deploying and configuring Azure SQL resources. It discusses deploying SQL Server on virtual machines using various methods like the Azure portal, PowerShell scripts, and ARM templates. It also covers deploying SQL databases using the PaaS offerings like single databases, elastic pools, and hyperscale. Key aspects covered include high availability and disaster recovery options, storage configurations, licensing models, and migration strategies.
07_DP_300T00A_HA_Disaster_Recovery.pptx

This document provides an overview of high availability and disaster recovery strategies for Azure SQL solutions. It discusses recovery time and point objectives and available options like Always On availability groups and failover cluster instances. It also covers backup and restore, factors to consider in a HADR strategy, and differences between infrastructure as a service and platform as a service solutions. Specific options covered include availability sets, availability zones, log shipping, Azure Site Recovery, temporal tables, active geo-replication, and auto failover groups.
06_DP_300T00A_Automate.pptx

This document provides an overview of automating database tasks for Azure SQL. It covers automating deployments using ARM templates, Bicep, and tools like PowerShell and CLI. It also discusses creating scheduled SQL Server Agent jobs for maintenance activities and configuring alerts and notifications. Finally, it introduces automation options for Azure PaaS services like Azure Policy, Automation, elastic jobs, and Logic Apps.
05_DP_300T00A_Optimize.pptx

This document provides an overview of Module 5: Optimize query performance in Azure SQL. The module contains 3 lessons that cover analyzing query plans, evaluating potential improvements, and reviewing table and index design. Lesson 1 explores generating and comparing execution plans, understanding how plans are generated, and the benefits of the Query Store. Lesson 2 examines database normalization, data types, index types, and denormalization. Lesson 3 describes wait statistics, tuning indexes, and using query hints. The lessons aim to help administrators optimize query performance in Azure SQL.
04_DP_300T00A_Monitor.pptx

The document discusses monitoring and optimizing performance in Azure SQL. It covers establishing performance baselines using tools like Azure Monitor and Performance Monitor. It discusses using Extended Events and Query Performance Insights to identify expensive queries. It also covers configuring resources like storage, TempDB, and using the SQL VM resource provider. It discusses maintenance tasks like index maintenance and statistics updates. It covers database configuration options and intelligent query processing features in Azure SQL.
03_DP_300T00A_Secure_Environment.pptx

This document provides an overview of implementing a secure environment for an Azure SQL database. It discusses authentication options like Azure Active Directory authentication and SQL authentication. It also covers encrypting data at rest using Transparent Data Encryption (TDE) and encrypting data in transit. Additionally, it describes configuring firewall rules and private endpoints for network security. The document demonstrates configuring an Active Directory admin, permission chaining, and Always Encrypted for encrypting column values. It also discusses using Azure Key Vault for securely storing encryption keys.
DP-300 Administering Relational Databases Azure_Oct2020

This document describes a case study for the DP-300 exam on administering relational databases on Microsoft Azure. It provides background on the existing environment including the network, identity, and database configurations. It then outlines requirements, planned changes, technical requirements, security and compliance requirements, and business requirements for the scenario. The first question asks about migrating databases from an on-premises SQL Server to Azure SQL Database and minimizing downtime. Subsequent questions cover topics like compression, migration options, and backup configurations.
Pmp Complete Notes

Here are the key inputs, tools and techniques, and outputs of the Estimate Activity Durations process:
Inputs:
- Activity list
- Enterprise environmental factors
- Organizational process assets
Tools and Techniques:
- Expert judgment
- Analogous estimating
- Parametric estimating
- Three-point estimating
Outputs:
- Activity duration estimates
- Basis of estimates
- Project documents updates
The primary output is the activity duration estimates, which are time estimates for completing individual activities based on factors such as resource availability, complexity, past experience, etc. These estimates are an important input for developing the project schedule.
Pmp Complete Diagrams

The document discusses various project management concepts including predictive, iterative, and adaptive life cycles; organizational structures; project influences; the role of the project manager; stakeholders; scope management techniques like work breakdown structures and user stories; sequencing and estimating activities; developing the project schedule; managing quality; resource management; communications management; risk management; procurement; and stakeholder management. Several tools are also presented such as precedence diagramming, Gantt charts, burndown charts, and stakeholder analysis matrices.
Pmp Complete Notes

The document discusses project life cycles and the five process groups of project management: initiating, planning, executing, monitoring and controlling, and closing. It also discusses the ten knowledge areas that projects typically use: integration management, scope management, time management, cost management, quality management, human resource management, communications management, risk management, procurement management, and stakeholder management. Finally, it provides an overview of organizational structures, communications, and the role of the project management office in supporting projects.
Pmp Complete Diagrams

This document provides an overview of various project management tools and techniques across multiple knowledge areas. It discusses predictive, iterative, and adaptive life cycles as well as variables that impact project life cycles. Various organizational structures are described including functional, weak matrix, balanced matrix, strong matrix, and projectized structures. Tools for developing schedules, managing costs, planning quality management, and performing risk analysis are also outlined.
Pmp ITTO Complete

This document provides a mind map overview of the processes involved in project management. It outlines 13 key processes including developing the project charter and management plan, directing project work, managing risk, procurement, and stakeholder engagement. For each process it lists the main inputs, tools and techniques, and outputs to plan, monitor, and control the various aspects of a project.
PMP Mind Maps Complete

This document provides a mind map overview of the processes involved in project integration management. It outlines seven key processes: develop the project charter, develop the project management plan, direct and manage project work, manage project knowledge, monitor and control project work, perform integrated change control, and close the project or phase. For each process, it lists the typical inputs, tools and techniques, and outputs involved. The mind map provides a high-level view of the integration of all project management processes.
Pmp Questions Complete

This document contains 20 multiple choice questions related to project scope management. The questions cover topics such as inputs and outputs of scope management processes, tools and techniques used in scope planning and control, and differences between scope documentation in waterfall and agile project approaches. Correct answers are provided for each question.
Pmp Extrenal Documents

May Wong provides tips on memorizing the 10 knowledge areas and 5 process groups of the PMP. She suggests creating stories or using visual tools like charts and colors. As an example, she maps the knowledge areas to characters in a story about two crows having coffee and reading poetry. She also provides memory techniques like creating acronyms or using the knowledge areas and process groups to describe steps to make cookies. The document focuses on providing creative methods for memorizing the foundational elements of project management.
Stakeholder Chapter 13

This document discusses the processes for managing project stakeholders: identify stakeholders through data gathering and analysis techniques to create a stakeholder register; plan stakeholder engagement using a stakeholder engagement assessment matrix to document current and desired engagement levels; manage engagement through communication skills and meetings; monitor engagement using the assessment matrix and provide updates based on feedback. The overall goal is to engage stakeholders appropriately throughout the project to ensure success.
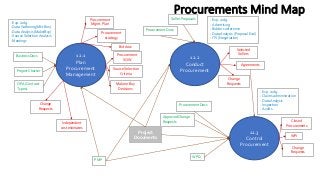
Procurements Chapter 12

The document discusses the three processes for managing procurements: plan procurement management, conduct procurements, and control procurements. In plan procurement management, inputs like the project charter and business documents are used with tools like expert judgment and data analysis to create outputs including the procurement management plan, procurement strategy, and bid documents. Conduct procurements uses the procurement documentation and seller proposals along with tools like bidder conferences and negotiation to select sellers and generate agreements. Control procurements monitors performance using tools like audits and trend analysis, and results in closing procurements and updating procurement documents and plans.
Procurement ITTO

This document outlines the three main processes for procurement management: plan procurement management, conduct procurements, and control procurements. It details the key activities in each process such as gathering market research, analyzing make-or-buy decisions, selecting suppliers, negotiating agreements, administering contracts, and closing out procurements. A mind map is also provided to show the relationships between the three procurement management processes and their associated inputs, outputs, and activities.
Stakeholder ITTO

This document outlines the four main processes for managing stakeholder engagement on a project: 1) identify stakeholders using data gathering and analysis to create a stakeholder register, 2) plan engagement using a stakeholder engagement matrix to develop an engagement plan, 3) manage engagement through communication, meetings and issue tracking, and 4) monitor engagement using metrics to update the engagement plan as needed. Key project documents like the project charter and change requests feed into and out of each process.
Stakeholder Mind Map

This document outlines the stakeholder management process which includes four steps: identifying stakeholders through data gathering and analysis to create a stakeholder register; planning stakeholder engagement using a stakeholder engagement assessment matrix; managing engagement through communication, meetings, and change requests; and monitoring engagement by updating the assessment matrix and measuring against the engagement plan. Key project documents like the project charter and change requests are also referenced.
Risk Chapter 11.pptx

This document discusses the key processes involved in project risk management according to the PMBOK Guide. It includes 11 sections that cover planning risk management, identifying risks, performing qualitative and quantitative risk analyses, planning and implementing risk responses, and monitoring risks. Various tools and techniques are used in each process, such as expert judgment, data gathering, analysis, and meetings. The key outputs include the risk management plan, risk register, risk report, and updates to project documents and management plans.
Risk ITTO

This document outlines the seven steps for project risk management: 1) plan risk management, 2) identify risks, 3) perform qualitative risk analysis, 4) perform quantitative risk analysis, 5) plan risk responses, 6) implement risk responses, and 7) monitor risks. For each step it lists the key inputs, tools and techniques, and outputs to effectively manage project risks. The overall process is represented by a risk mind map showing the flow from risk planning to monitoring.
Risk Mind Map

The document outlines the steps in a risk management plan including planning risk management, identifying risks, performing qualitative and quantitative risk analysis, planning and implementing risk responses, and monitoring risks. Key project documents include the risk management plan, risk register, and change requests. Risk analysis involves expert judgement, data gathering and analysis, and tools like impact and severity matrices.
More Related Content
More from KareemBullard1
04_DP_300T00A_Monitor.pptx

The document discusses monitoring and optimizing performance in Azure SQL. It covers establishing performance baselines using tools like Azure Monitor and Performance Monitor. It discusses using Extended Events and Query Performance Insights to identify expensive queries. It also covers configuring resources like storage, TempDB, and using the SQL VM resource provider. It discusses maintenance tasks like index maintenance and statistics updates. It covers database configuration options and intelligent query processing features in Azure SQL.
03_DP_300T00A_Secure_Environment.pptx

This document provides an overview of implementing a secure environment for an Azure SQL database. It discusses authentication options like Azure Active Directory authentication and SQL authentication. It also covers encrypting data at rest using Transparent Data Encryption (TDE) and encrypting data in transit. Additionally, it describes configuring firewall rules and private endpoints for network security. The document demonstrates configuring an Active Directory admin, permission chaining, and Always Encrypted for encrypting column values. It also discusses using Azure Key Vault for securely storing encryption keys.
DP-300 Administering Relational Databases Azure_Oct2020

This document describes a case study for the DP-300 exam on administering relational databases on Microsoft Azure. It provides background on the existing environment including the network, identity, and database configurations. It then outlines requirements, planned changes, technical requirements, security and compliance requirements, and business requirements for the scenario. The first question asks about migrating databases from an on-premises SQL Server to Azure SQL Database and minimizing downtime. Subsequent questions cover topics like compression, migration options, and backup configurations.
Pmp Complete Notes

Here are the key inputs, tools and techniques, and outputs of the Estimate Activity Durations process:
Inputs:
- Activity list
- Enterprise environmental factors
- Organizational process assets
Tools and Techniques:
- Expert judgment
- Analogous estimating
- Parametric estimating
- Three-point estimating
Outputs:
- Activity duration estimates
- Basis of estimates
- Project documents updates
The primary output is the activity duration estimates, which are time estimates for completing individual activities based on factors such as resource availability, complexity, past experience, etc. These estimates are an important input for developing the project schedule.
Pmp Complete Diagrams

The document discusses various project management concepts including predictive, iterative, and adaptive life cycles; organizational structures; project influences; the role of the project manager; stakeholders; scope management techniques like work breakdown structures and user stories; sequencing and estimating activities; developing the project schedule; managing quality; resource management; communications management; risk management; procurement; and stakeholder management. Several tools are also presented such as precedence diagramming, Gantt charts, burndown charts, and stakeholder analysis matrices.
Pmp Complete Notes

The document discusses project life cycles and the five process groups of project management: initiating, planning, executing, monitoring and controlling, and closing. It also discusses the ten knowledge areas that projects typically use: integration management, scope management, time management, cost management, quality management, human resource management, communications management, risk management, procurement management, and stakeholder management. Finally, it provides an overview of organizational structures, communications, and the role of the project management office in supporting projects.
Pmp Complete Diagrams

This document provides an overview of various project management tools and techniques across multiple knowledge areas. It discusses predictive, iterative, and adaptive life cycles as well as variables that impact project life cycles. Various organizational structures are described including functional, weak matrix, balanced matrix, strong matrix, and projectized structures. Tools for developing schedules, managing costs, planning quality management, and performing risk analysis are also outlined.
Pmp ITTO Complete

This document provides a mind map overview of the processes involved in project management. It outlines 13 key processes including developing the project charter and management plan, directing project work, managing risk, procurement, and stakeholder engagement. For each process it lists the main inputs, tools and techniques, and outputs to plan, monitor, and control the various aspects of a project.
PMP Mind Maps Complete

This document provides a mind map overview of the processes involved in project integration management. It outlines seven key processes: develop the project charter, develop the project management plan, direct and manage project work, manage project knowledge, monitor and control project work, perform integrated change control, and close the project or phase. For each process, it lists the typical inputs, tools and techniques, and outputs involved. The mind map provides a high-level view of the integration of all project management processes.
Pmp Questions Complete

This document contains 20 multiple choice questions related to project scope management. The questions cover topics such as inputs and outputs of scope management processes, tools and techniques used in scope planning and control, and differences between scope documentation in waterfall and agile project approaches. Correct answers are provided for each question.
Pmp Extrenal Documents

May Wong provides tips on memorizing the 10 knowledge areas and 5 process groups of the PMP. She suggests creating stories or using visual tools like charts and colors. As an example, she maps the knowledge areas to characters in a story about two crows having coffee and reading poetry. She also provides memory techniques like creating acronyms or using the knowledge areas and process groups to describe steps to make cookies. The document focuses on providing creative methods for memorizing the foundational elements of project management.
Stakeholder Chapter 13

This document discusses the processes for managing project stakeholders: identify stakeholders through data gathering and analysis techniques to create a stakeholder register; plan stakeholder engagement using a stakeholder engagement assessment matrix to document current and desired engagement levels; manage engagement through communication skills and meetings; monitor engagement using the assessment matrix and provide updates based on feedback. The overall goal is to engage stakeholders appropriately throughout the project to ensure success.
Procurements Chapter 12

The document discusses the three processes for managing procurements: plan procurement management, conduct procurements, and control procurements. In plan procurement management, inputs like the project charter and business documents are used with tools like expert judgment and data analysis to create outputs including the procurement management plan, procurement strategy, and bid documents. Conduct procurements uses the procurement documentation and seller proposals along with tools like bidder conferences and negotiation to select sellers and generate agreements. Control procurements monitors performance using tools like audits and trend analysis, and results in closing procurements and updating procurement documents and plans.
Procurement ITTO

This document outlines the three main processes for procurement management: plan procurement management, conduct procurements, and control procurements. It details the key activities in each process such as gathering market research, analyzing make-or-buy decisions, selecting suppliers, negotiating agreements, administering contracts, and closing out procurements. A mind map is also provided to show the relationships between the three procurement management processes and their associated inputs, outputs, and activities.
Stakeholder ITTO

This document outlines the four main processes for managing stakeholder engagement on a project: 1) identify stakeholders using data gathering and analysis to create a stakeholder register, 2) plan engagement using a stakeholder engagement matrix to develop an engagement plan, 3) manage engagement through communication, meetings and issue tracking, and 4) monitor engagement using metrics to update the engagement plan as needed. Key project documents like the project charter and change requests feed into and out of each process.
Stakeholder Mind Map

This document outlines the stakeholder management process which includes four steps: identifying stakeholders through data gathering and analysis to create a stakeholder register; planning stakeholder engagement using a stakeholder engagement assessment matrix; managing engagement through communication, meetings, and change requests; and monitoring engagement by updating the assessment matrix and measuring against the engagement plan. Key project documents like the project charter and change requests are also referenced.
Risk Chapter 11.pptx

This document discusses the key processes involved in project risk management according to the PMBOK Guide. It includes 11 sections that cover planning risk management, identifying risks, performing qualitative and quantitative risk analyses, planning and implementing risk responses, and monitoring risks. Various tools and techniques are used in each process, such as expert judgment, data gathering, analysis, and meetings. The key outputs include the risk management plan, risk register, risk report, and updates to project documents and management plans.
Risk ITTO

This document outlines the seven steps for project risk management: 1) plan risk management, 2) identify risks, 3) perform qualitative risk analysis, 4) perform quantitative risk analysis, 5) plan risk responses, 6) implement risk responses, and 7) monitor risks. For each step it lists the key inputs, tools and techniques, and outputs to effectively manage project risks. The overall process is represented by a risk mind map showing the flow from risk planning to monitoring.
Risk Mind Map

The document outlines the steps in a risk management plan including planning risk management, identifying risks, performing qualitative and quantitative risk analysis, planning and implementing risk responses, and monitoring risks. Key project documents include the risk management plan, risk register, and change requests. Risk analysis involves expert judgement, data gathering and analysis, and tools like impact and severity matrices.
More from KareemBullard1 (20)
DP-300 Administering Relational Databases Azure_Oct2020

DP-300 Administering Relational Databases Azure_Oct2020
Procurement Mind Map
- 1. Procurements Mind Map 12.1 Plan Procurement Management PMP Project Documents - Exp. Judg. - Data Gathering(Mkt Res.) - Data Analysis (Make/Buy) - Source Selection Analysis - Meetings Procurement Mgmt. Plan Project Charter Business Docs Procurement strategy Bid docs Procurement SOW Source Selection Criteria Make or Buy Decisions Independent cost estimates Change Requests 12.2 Conduct Procurement OPA (Contract Types) Procurement Docs Seller Proposals - Exp. Judg. - Advertising - Bidder conference - Data Analysis (Proposal Eval) - ITS (Negotiation) Selected Sellers Agreements Change Requests 12.3 Control Procurement Procurement Docs Approved Change Requests WPD - Exp. Judg. - Claims administration - Data Analysis - Inspection - Audits Closed Procurements WPI Change Requests