The document provides an overview of EMC's Symmetrix VMAX hardware, including:
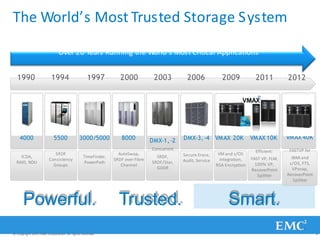
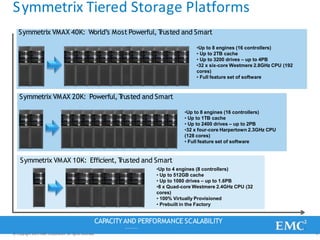
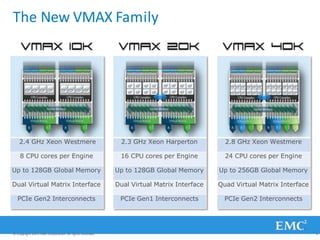
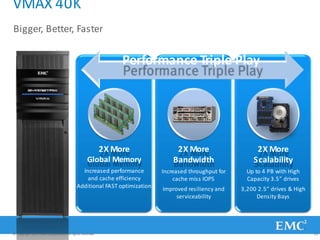
- The evolution of the VMAX platform from 1990 to present, including models 10K, 20K, and 40K.
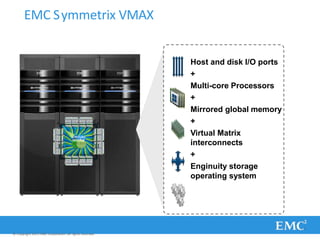
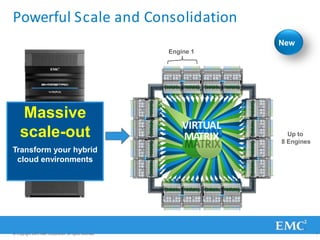
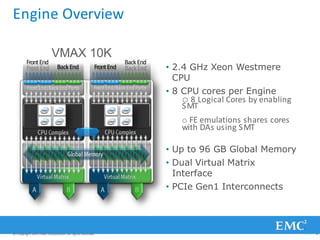
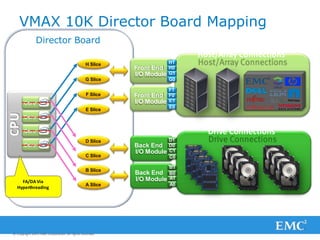
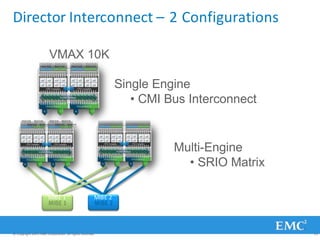
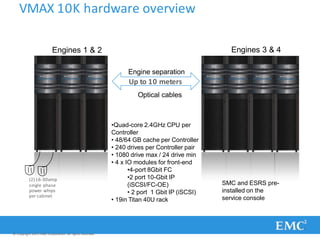
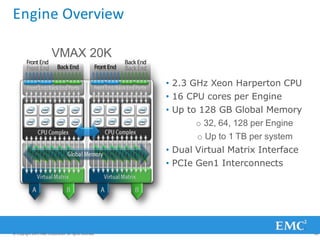
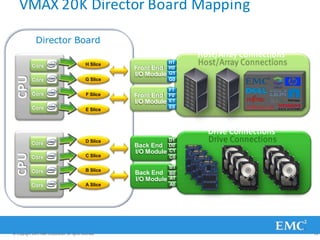
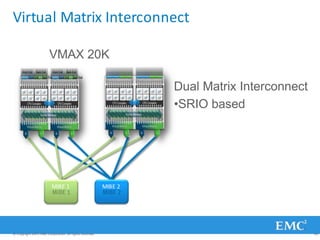
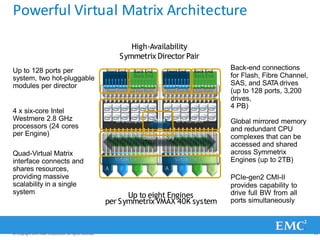
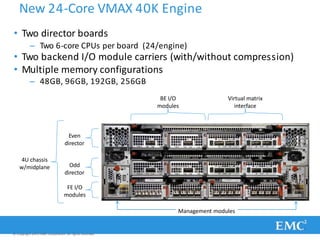
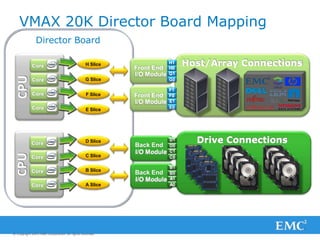
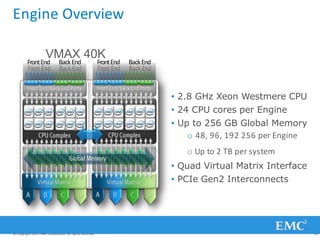
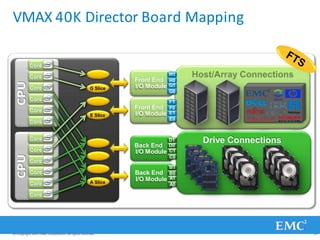
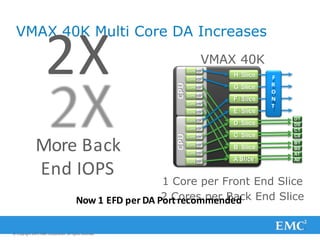
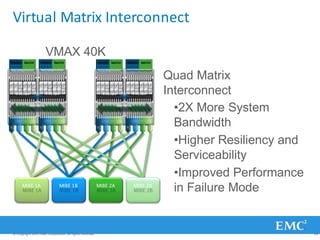
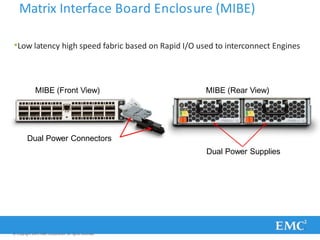
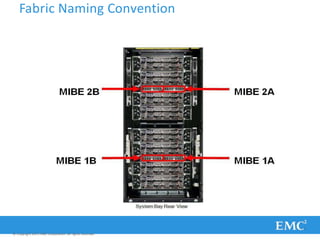
- The architecture of VMAX, which uses multiple engines with CPUs, global memory, and virtual matrix interconnects running Enginuity software.
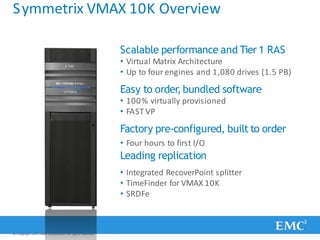
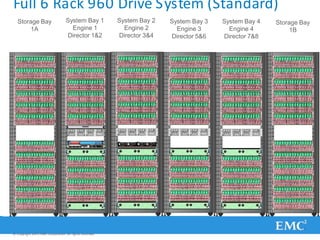
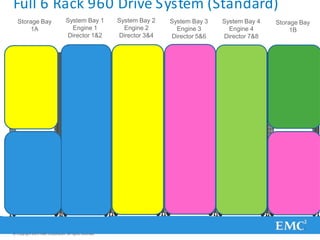
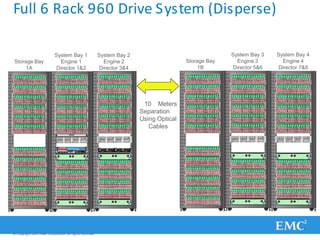
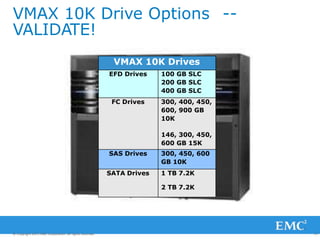
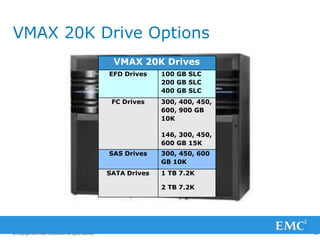
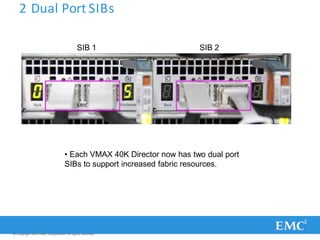
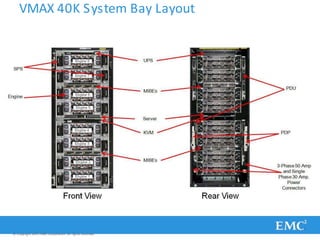
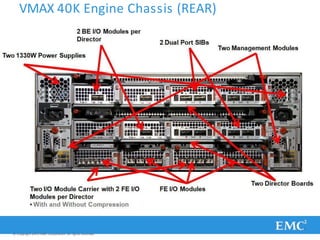
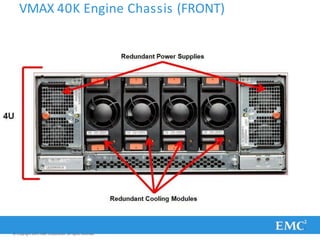
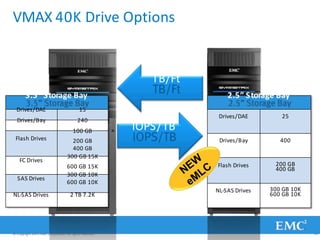
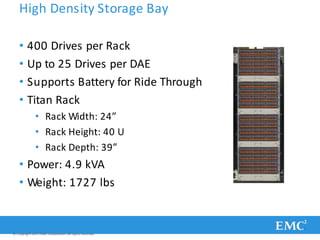
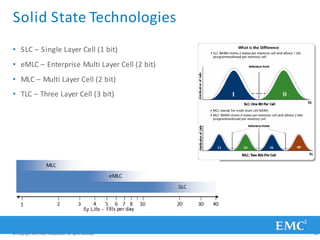
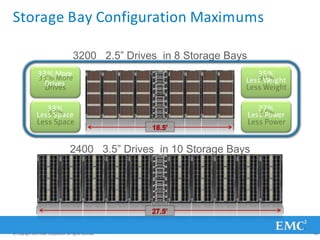
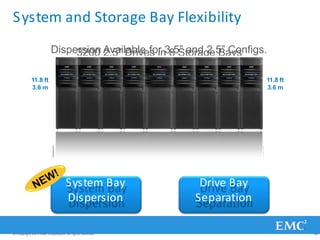
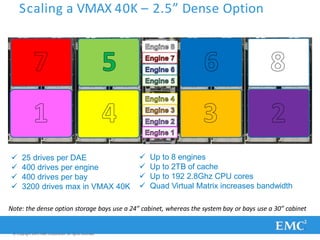
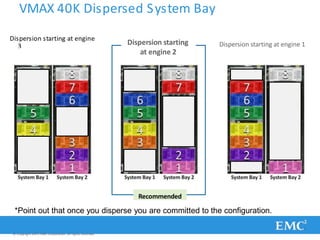
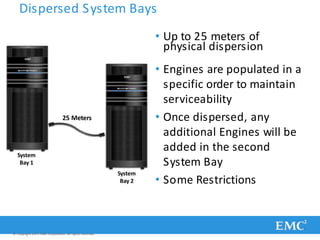
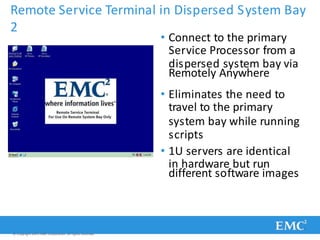
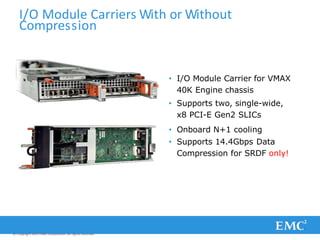
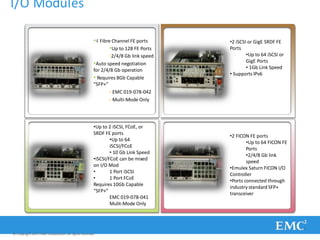
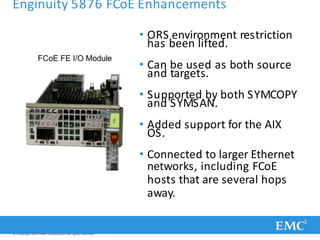
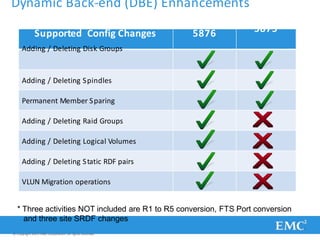
- Details on the components, scaling, and configurations of the VMAX 10K, 20K, and 40K models.