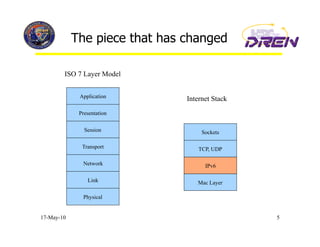
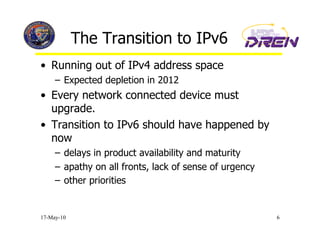
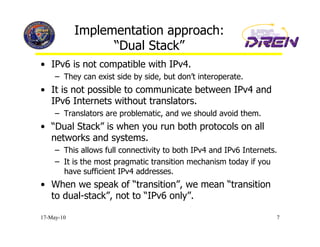
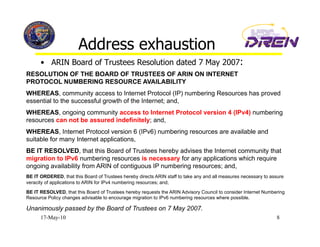
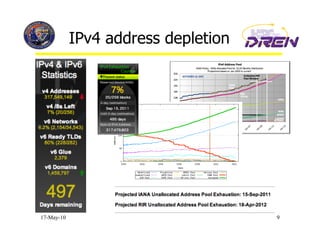
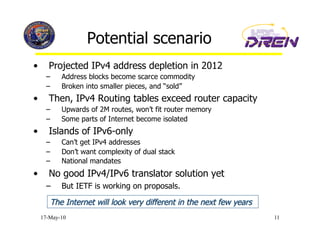
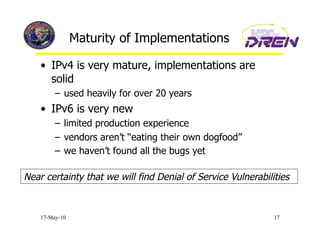
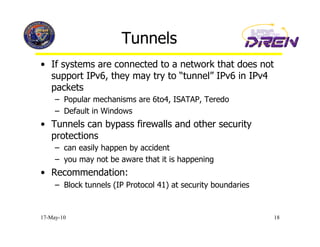
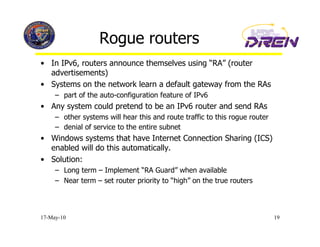
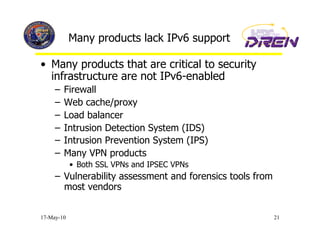
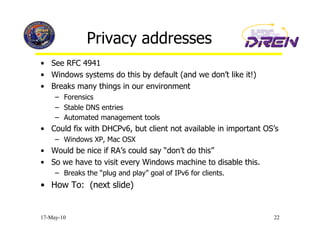
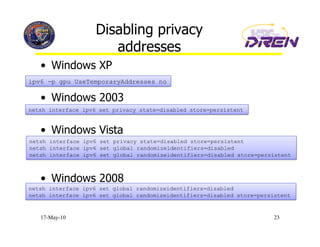
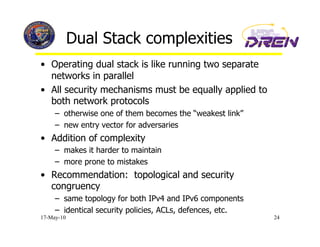
The document discusses IPv6 and its implementation across the Defense Research and Engineering Network (DREN). It provides a brief introduction to IPv6, noting its vast address space and other benefits. It describes DREN's dual stack implementation approach and some security challenges introduced by IPv6, such as vulnerabilities in new implementations and issues with privacy addresses. The document recommends deploying IPv6 now rather than waiting for a crisis scenario due to IPv4 address depletion.