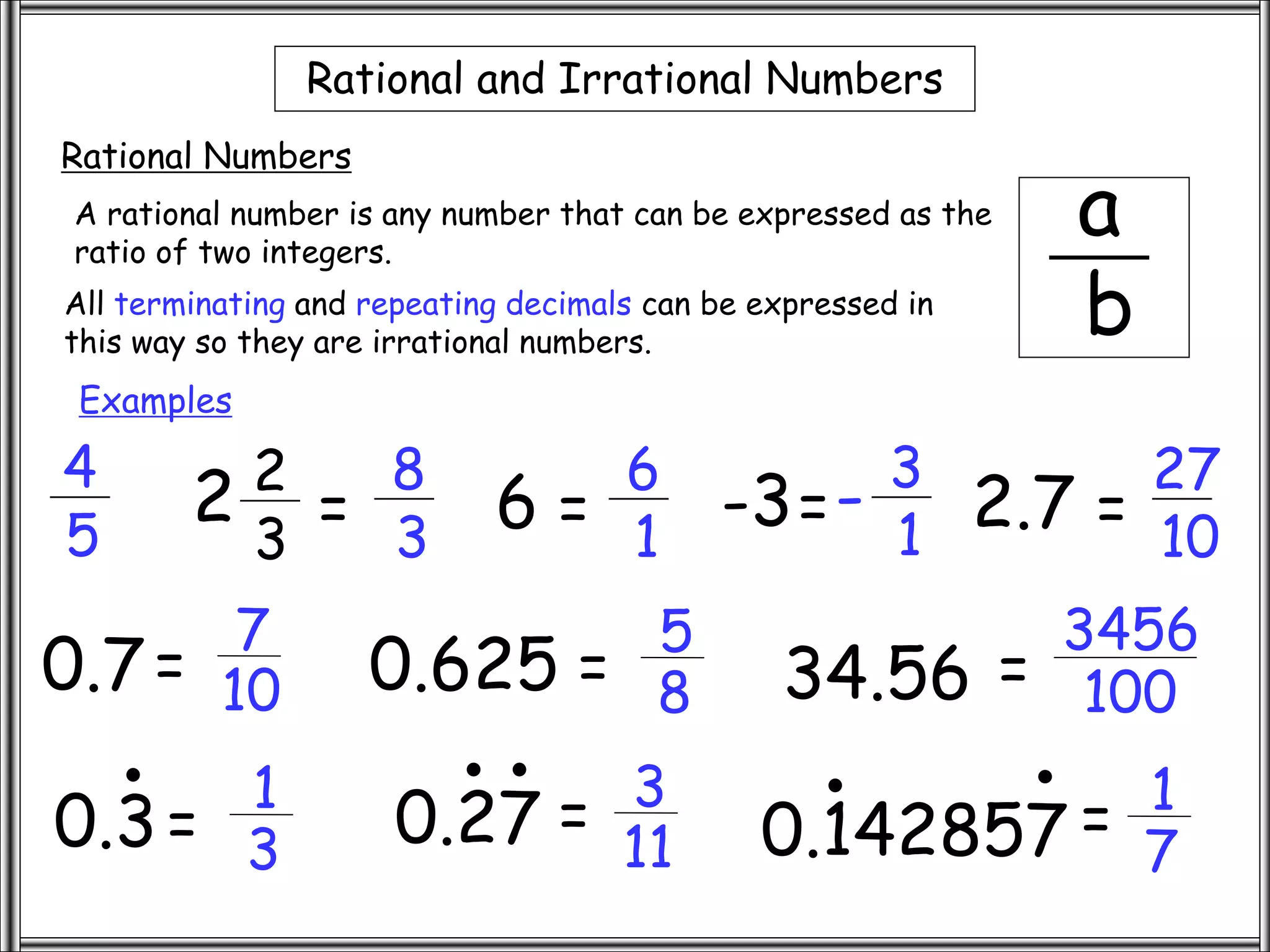
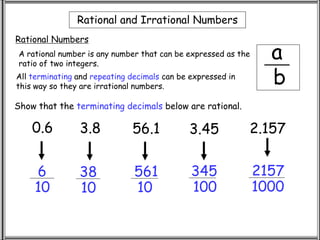
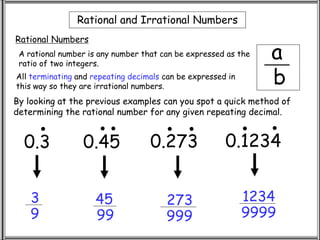
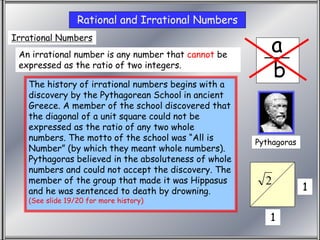
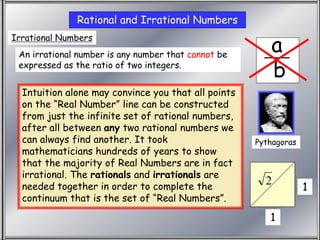
Rational numbers can be expressed as a ratio of two integers, while irrational numbers cannot. The discovery of irrational numbers began with Pythagoras, who found that the diagonal of a unit square could not be expressed as a ratio of integers, contradicting the Pythagorean belief that all numbers were rational. While intuition suggests that rational numbers can construct all real numbers, mathematicians later proved that most real numbers are actually irrational.