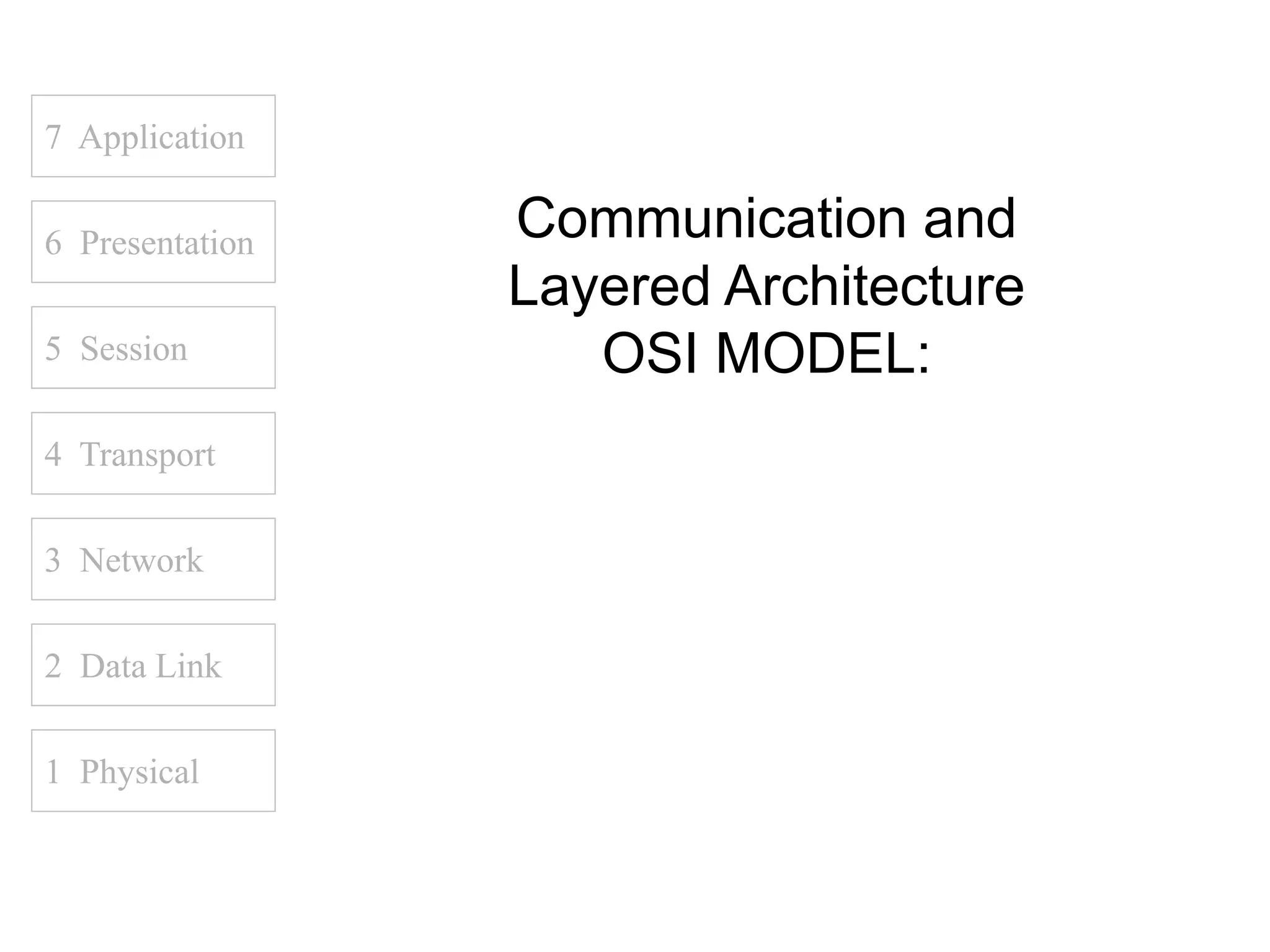
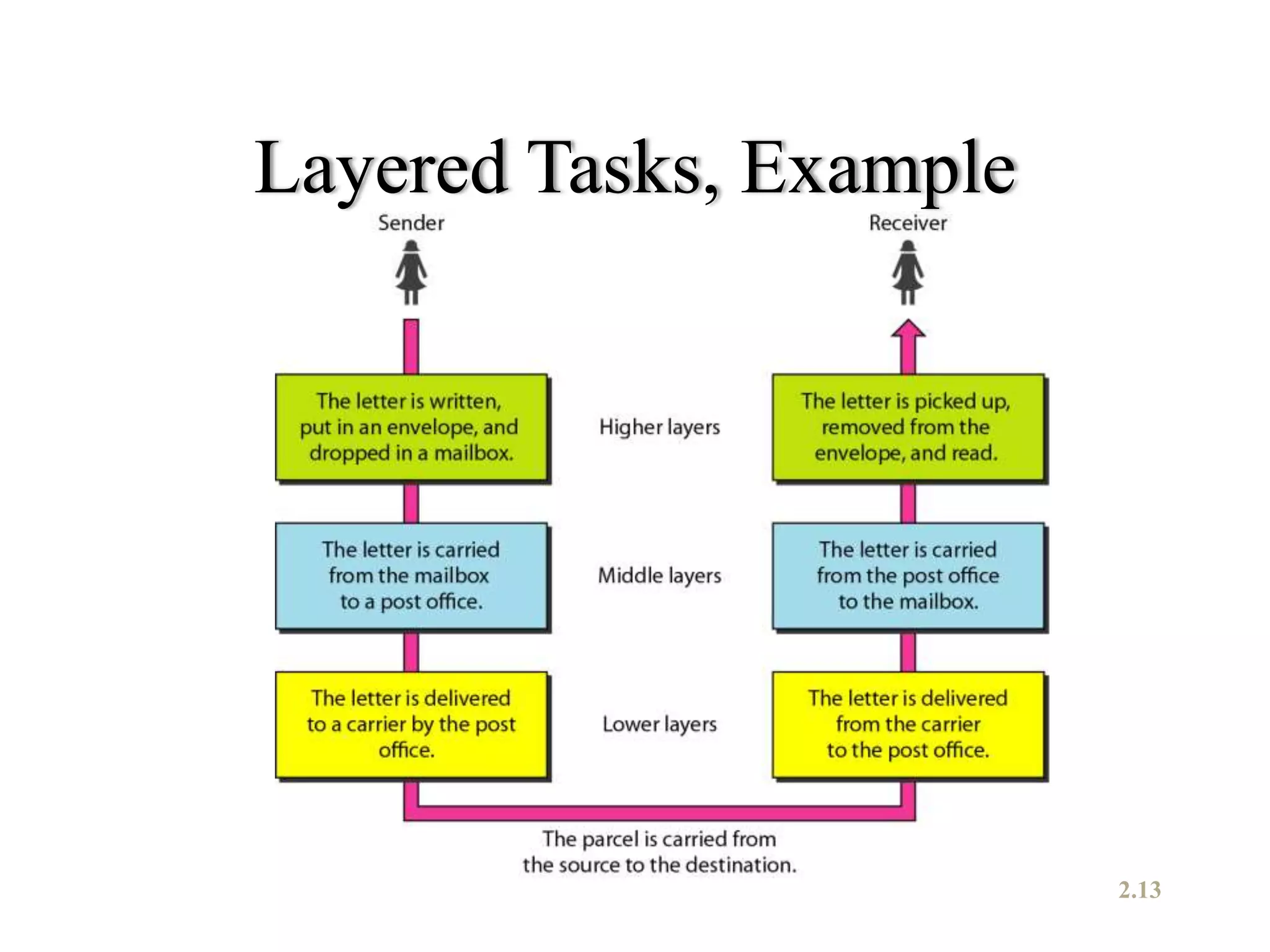
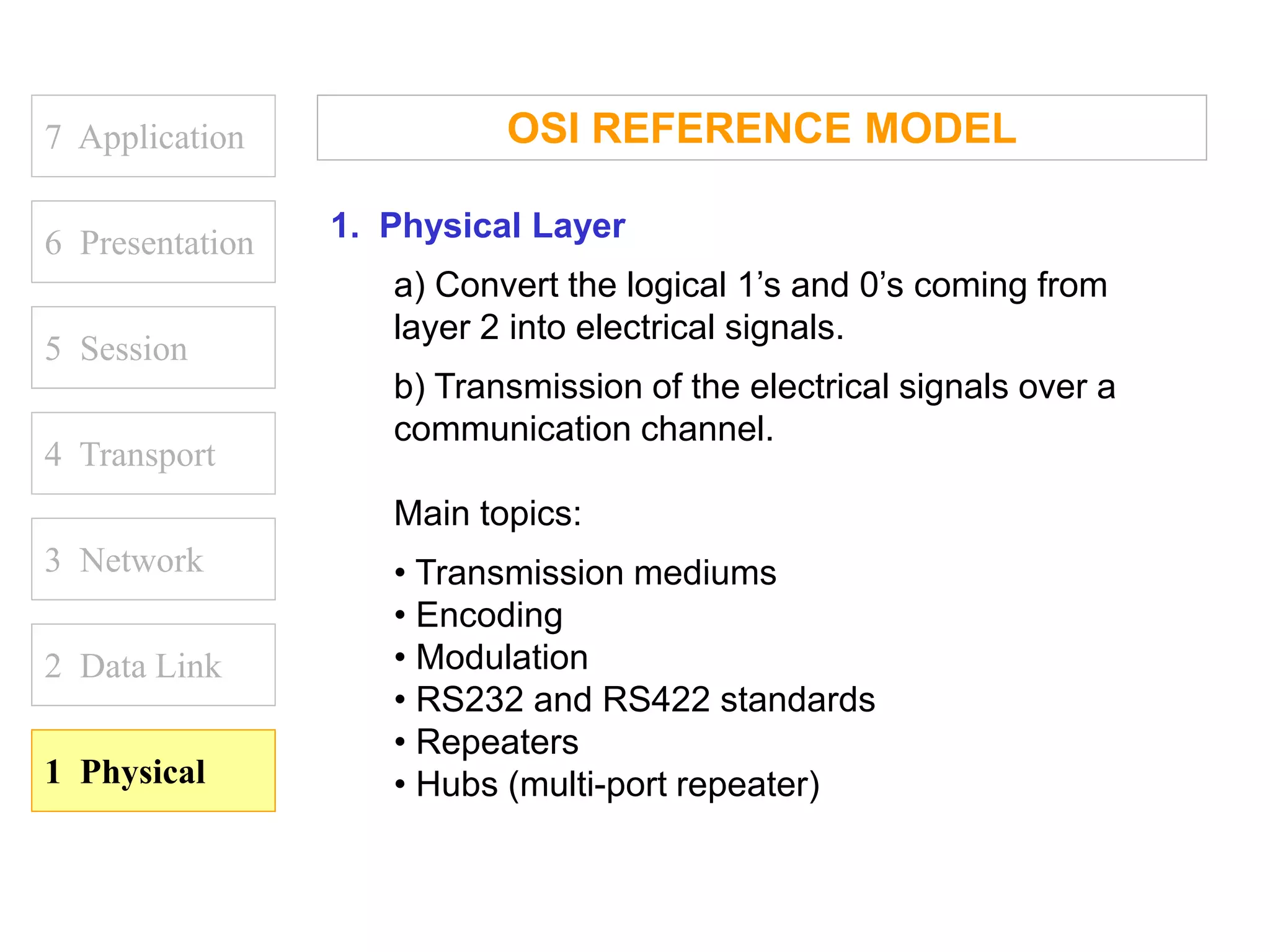
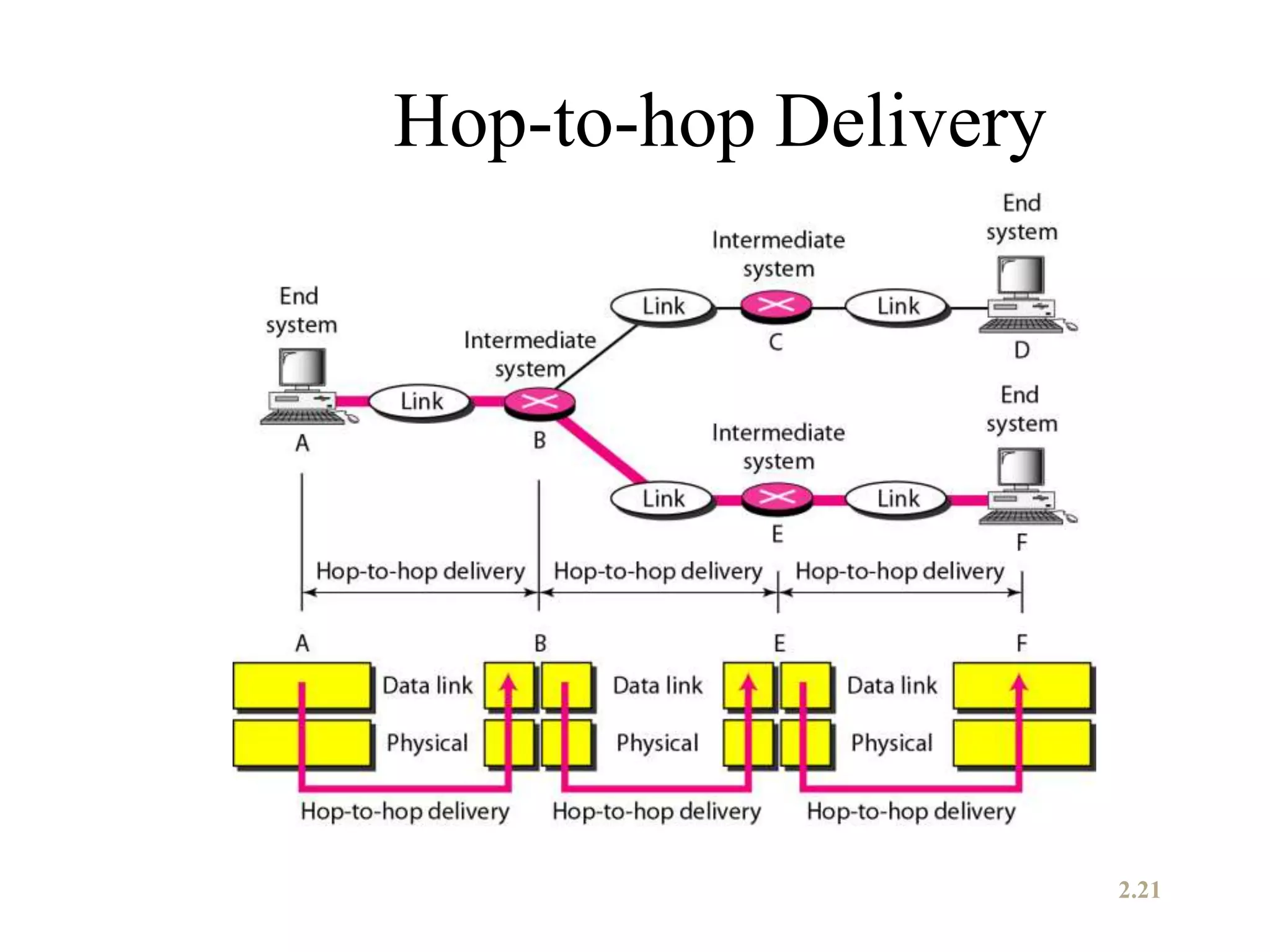
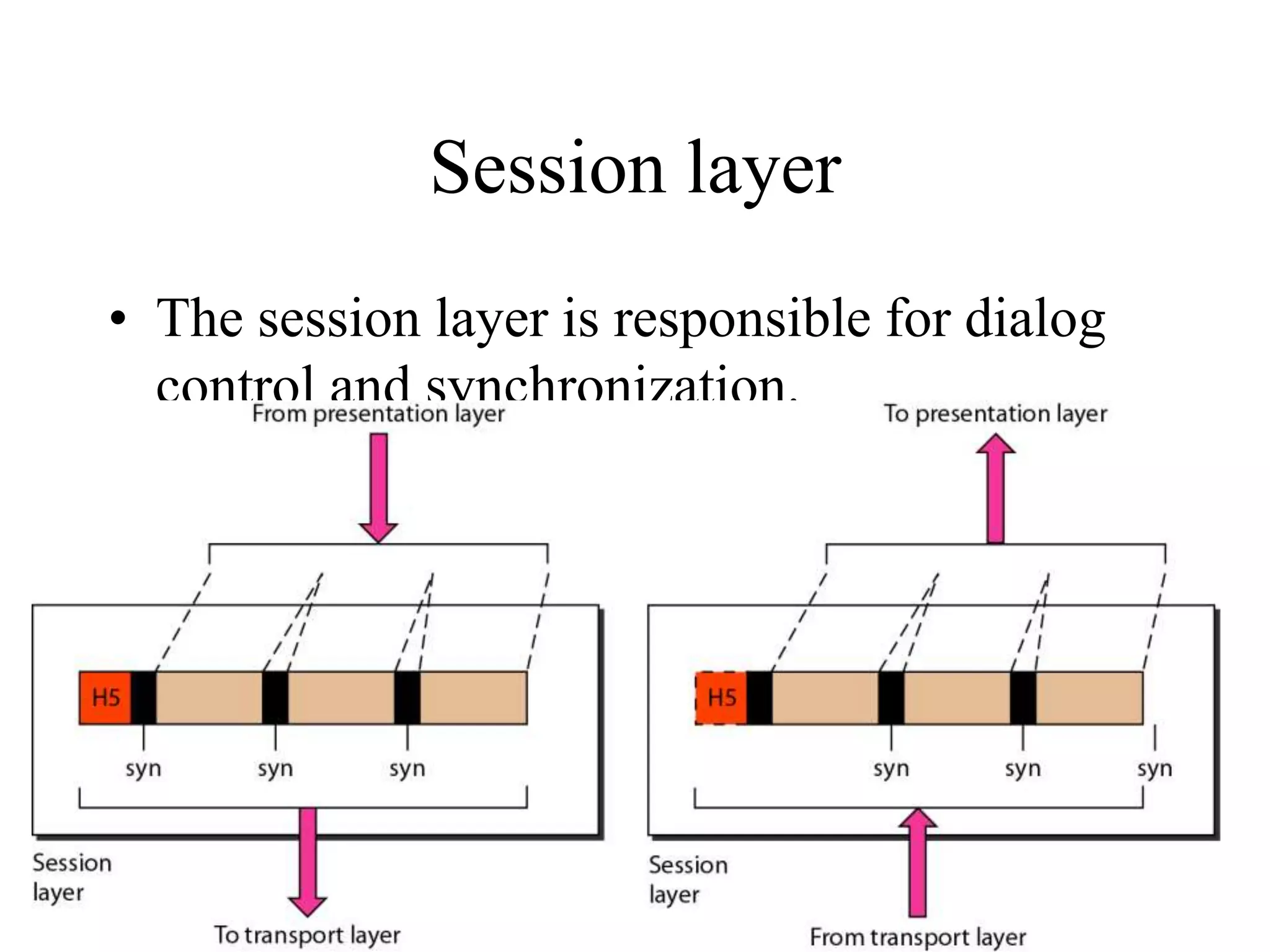
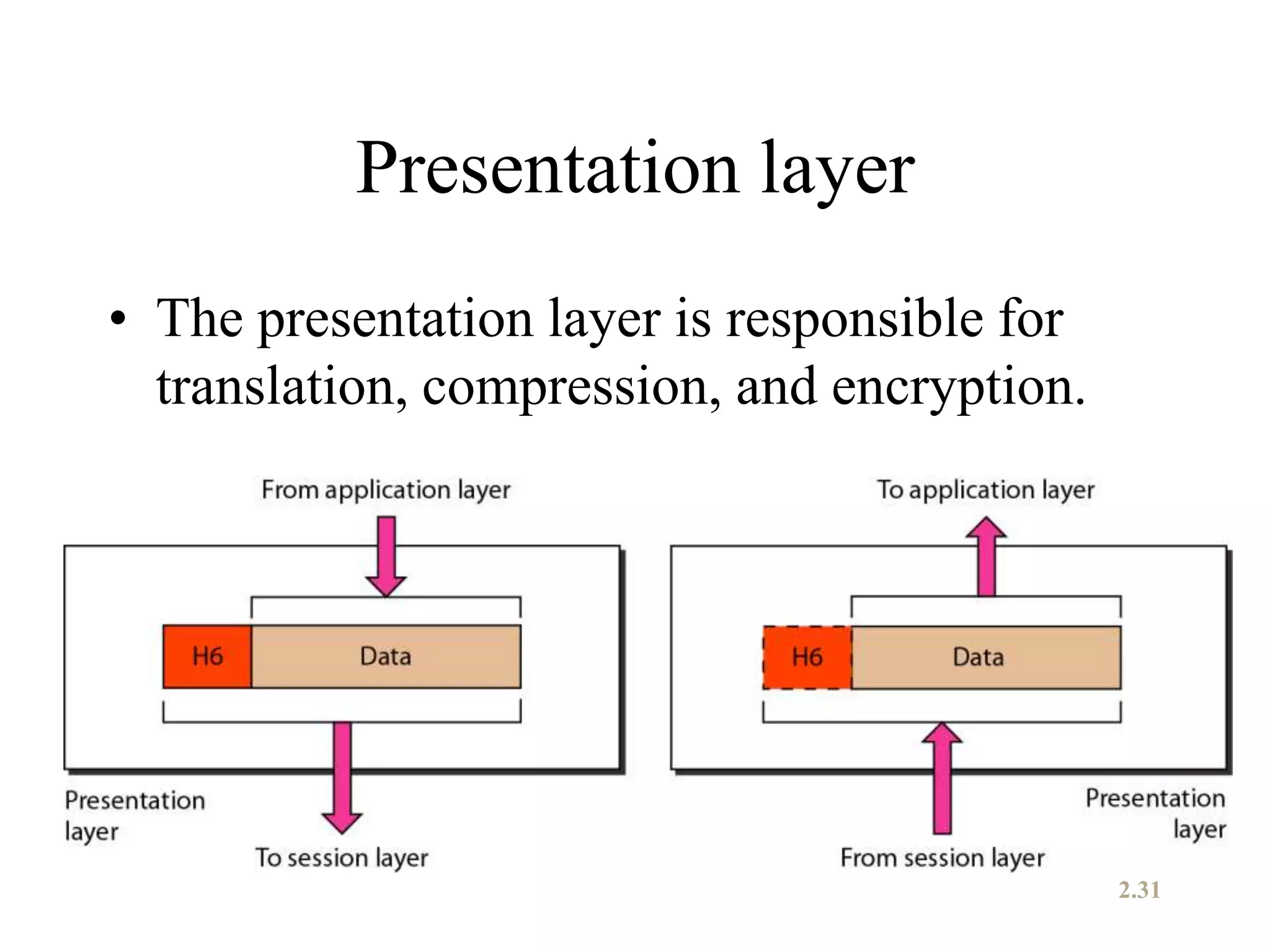
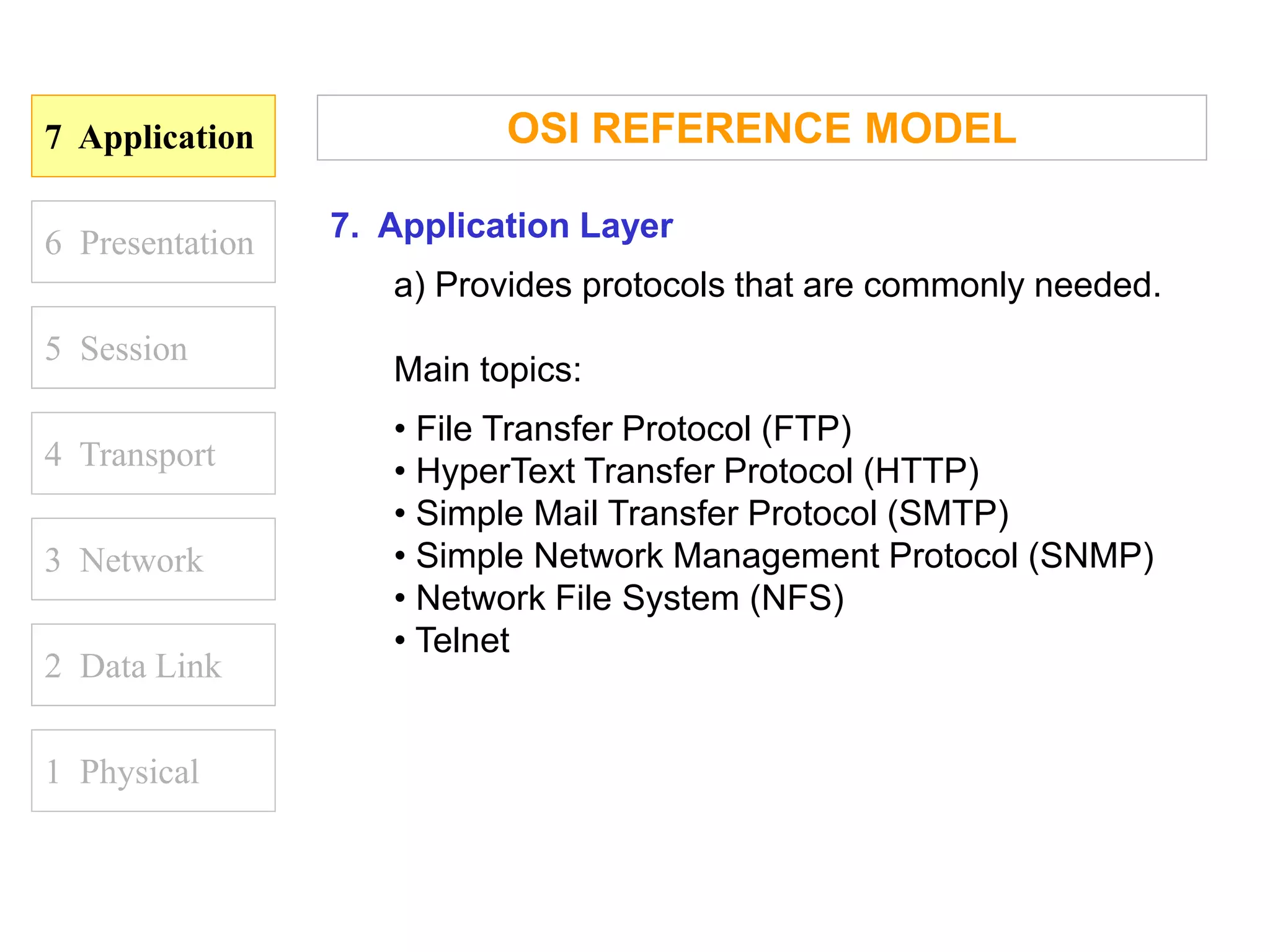
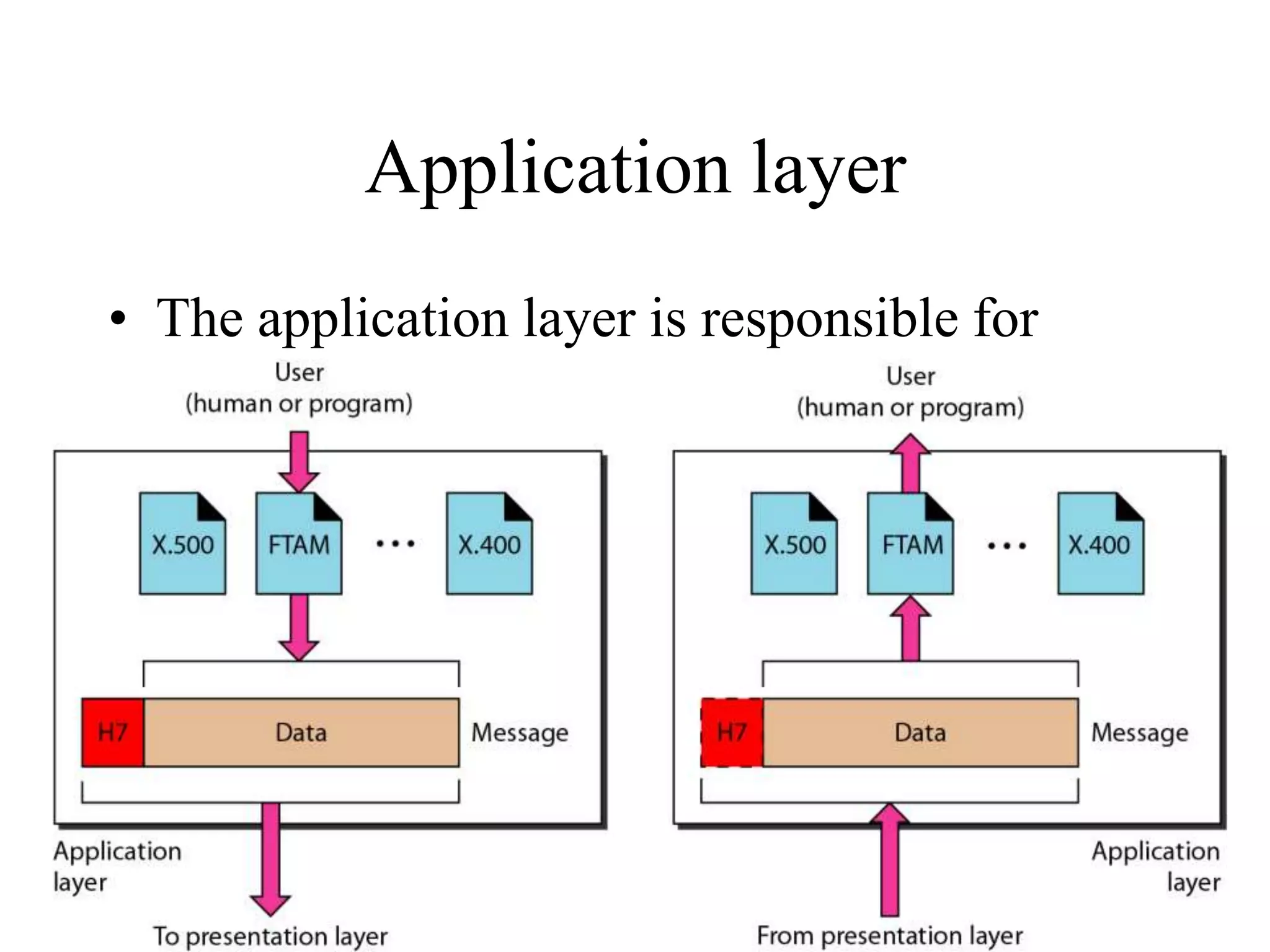
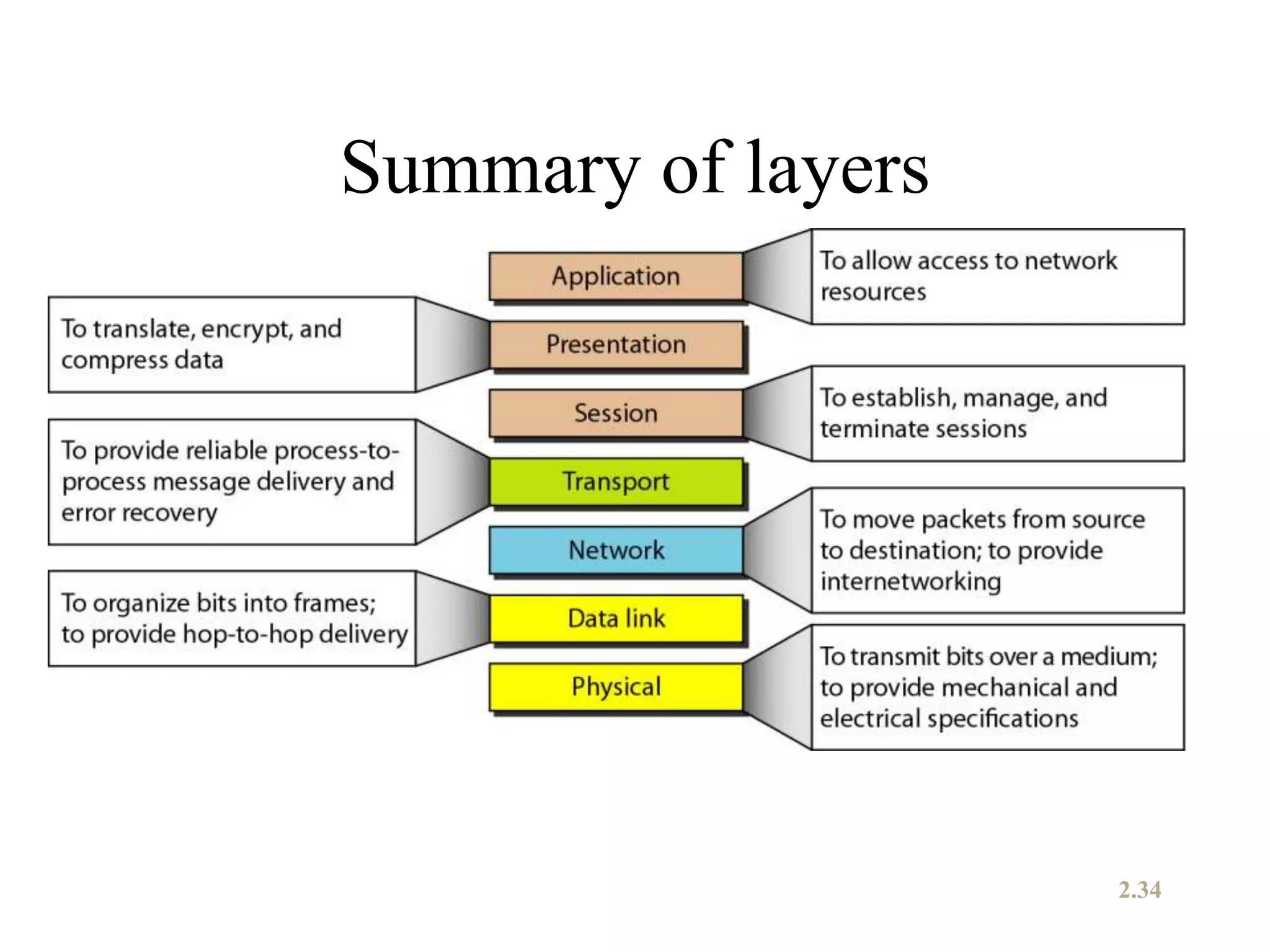
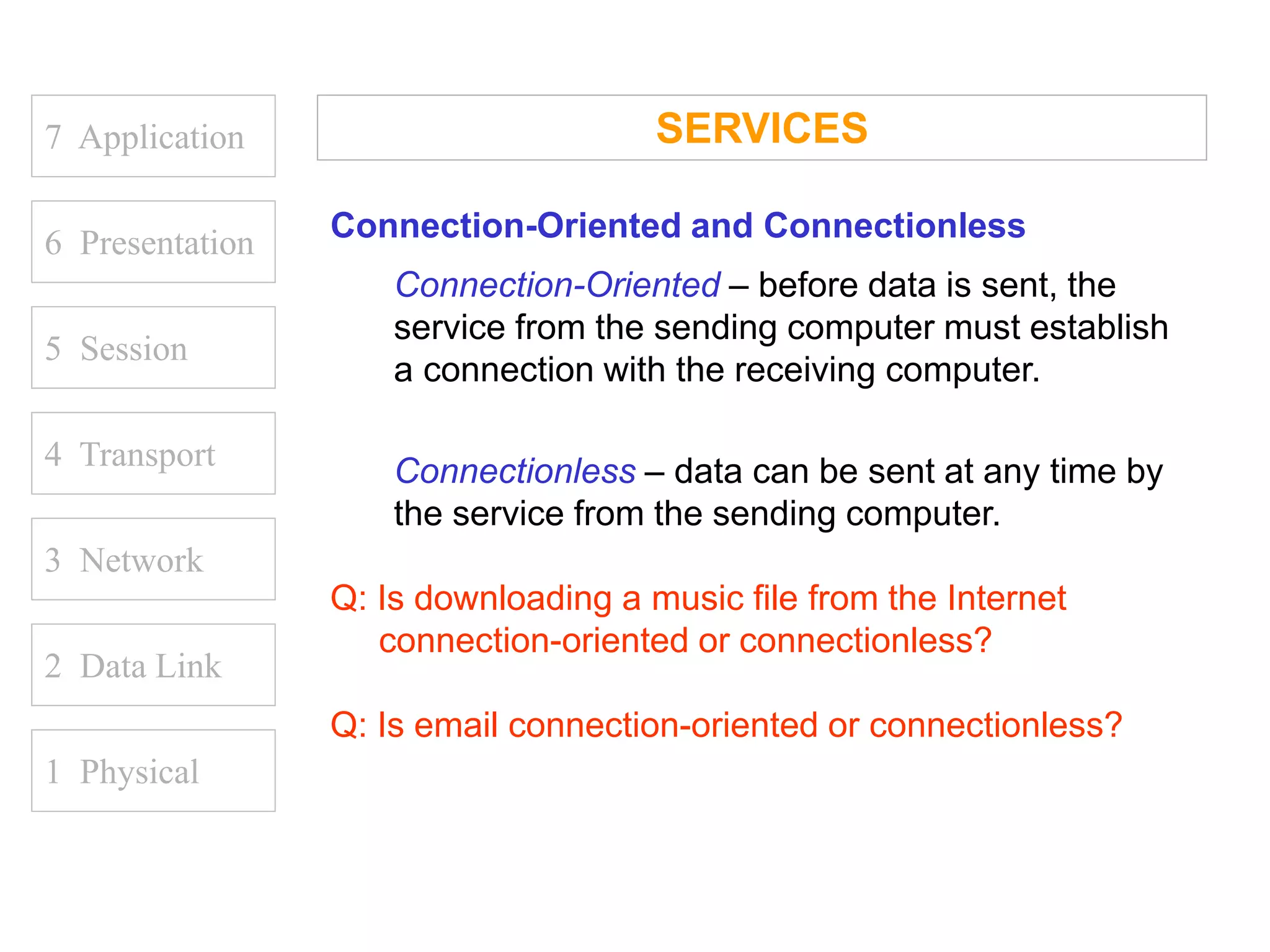
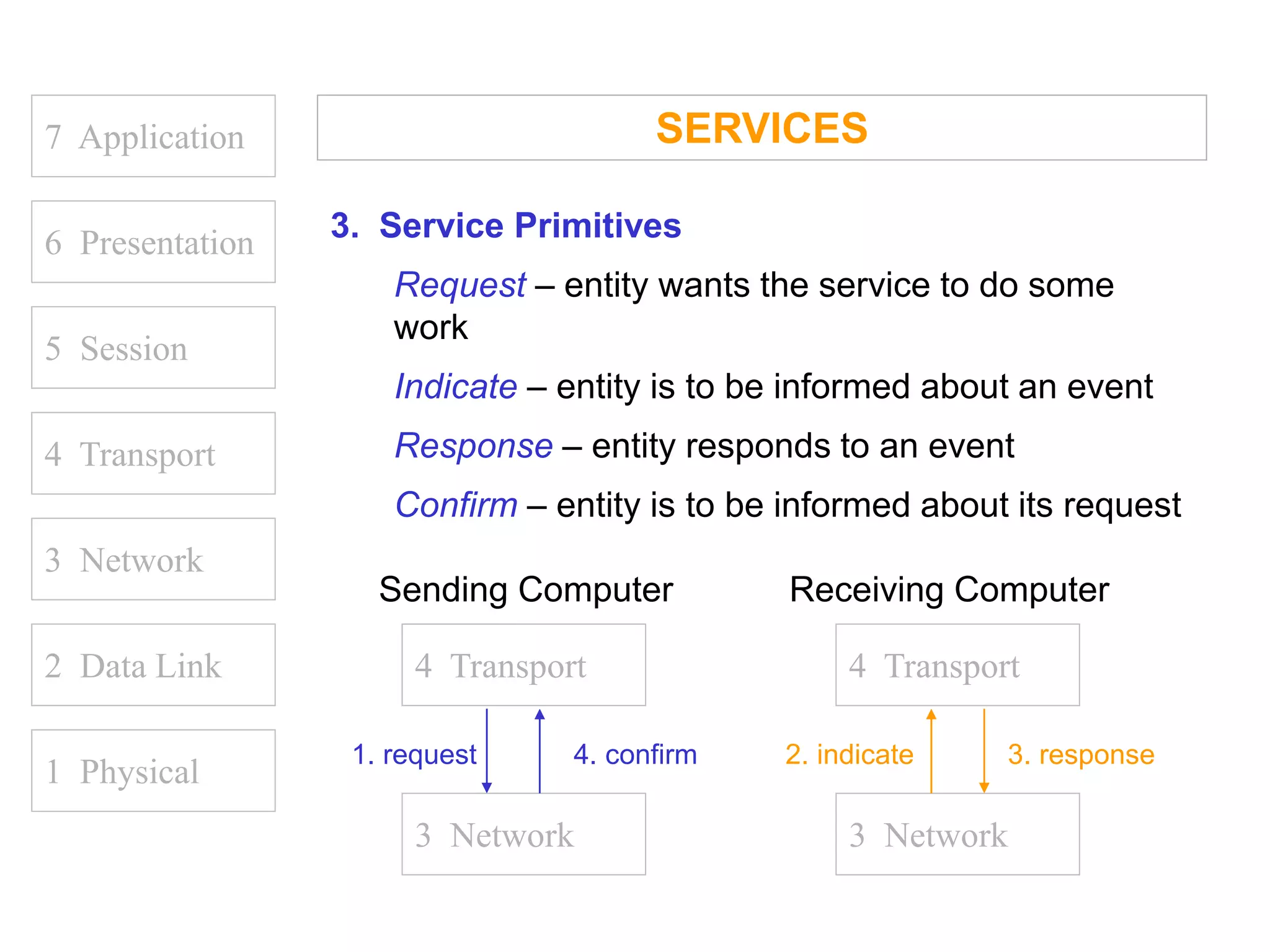
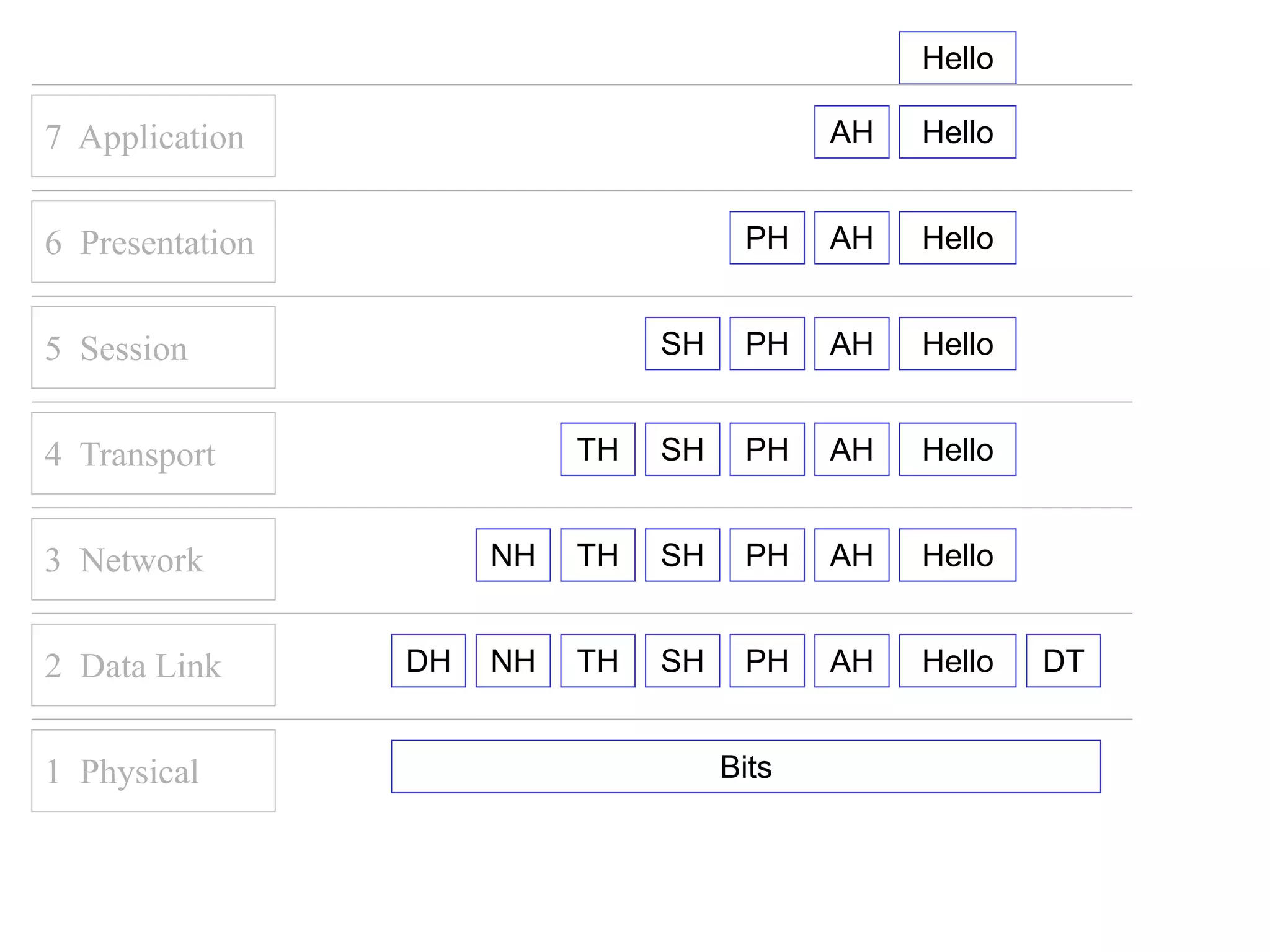
The document discusses the OSI (Open Systems Interconnection) model and its seven layers, emphasizing the importance of standardized communication protocols for network interoperability. It outlines the roles of key standards organizations such as ISO, ITU, ANSI, IEEE, EIA, and IETF in developing these standards to enhance global communication systems. Each layer of the OSI model addresses specific tasks and issues, facilitating efficient data transmission and network communication.