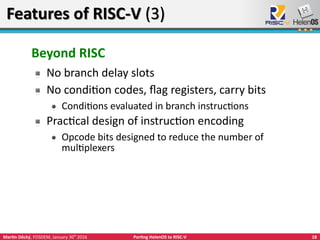
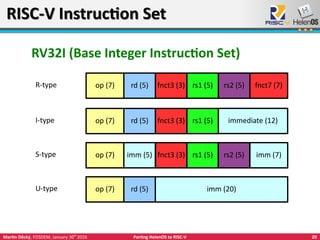
The document discusses the process of porting the HelenOS operating system to the RISC-V instruction set architecture. RISC-V, an open-source ISA developed since 2014, aims for scalability and modularity, serving a range of applications from embedded systems to large computers. The presentation, given by Martin Děcký at FOSDEM 2016, details the features of both RISC-V and HelenOS, highlighting their developmental goals and the current state of the porting effort.


























![37Martin Děcký, FOSDEM, January 30th
2016 Porting HelenOS to RISC-V
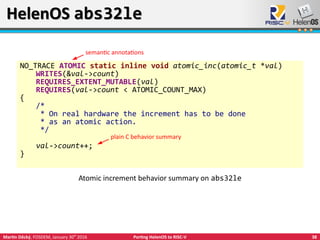
HelenOS abs32leHelenOS abs32le
NO_TRACE static inline void atomic_inc(atomic_t *val)
{
#ifdef CONFIG_SMP
asm volatile (
”lock incq %[count]n”
: [count] ”+m” (val->count)
);
#else
asm volatile (
”incq %[count]n”
: [count] ”+m” (val->count)
);
#endif /* CONFIG_SMP */
}
Atomic increment on IA-32](https://image.slidesharecdn.com/20160130deckyfosdemportinghelenostorisc-v-160130115431/85/Porting-HelenOS-to-RISC-V-37-320.jpg)















![58Martin Děcký, FOSDEM, January 30th
2016 Porting HelenOS to RISC-V
RISC-V in AcademiaRISC-V in Academia
Highlights of research projects based on RISC-V
Formal specification & verification
Chisel open source hardware construction language
[UC Berkeley]
Novel bespoke weak memory consistency models [MIT]
Novel manycore configurations [Gray Research]
First experimental photonic CPU [UC Berkeley]
Experimental ISA extensions [ETH Zürich]
Hardware loops
Faster ISA simulators using JIT [Cornell]](https://image.slidesharecdn.com/20160130deckyfosdemportinghelenostorisc-v-160130115431/85/Porting-HelenOS-to-RISC-V-58-320.jpg)