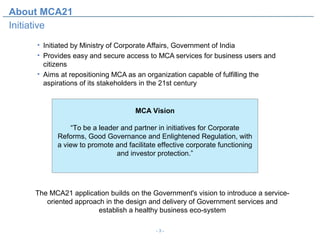
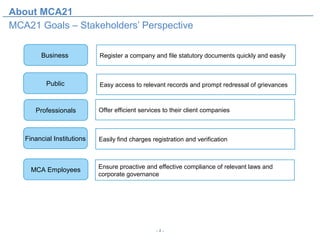
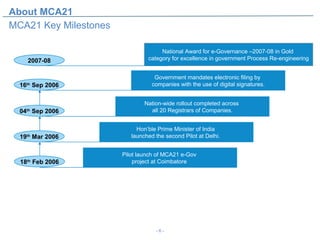
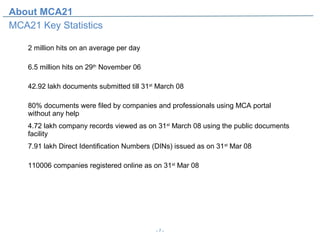
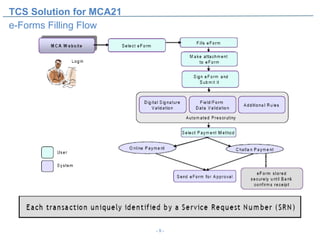
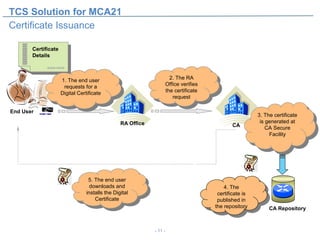
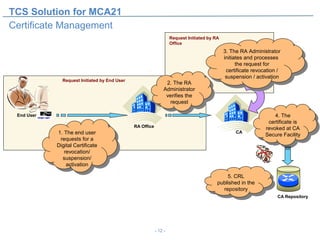
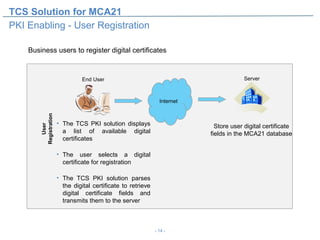
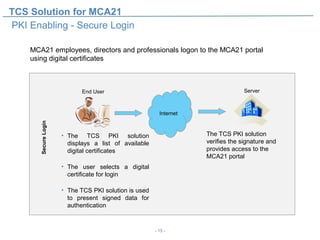
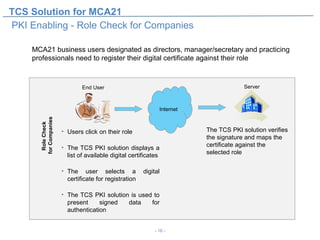
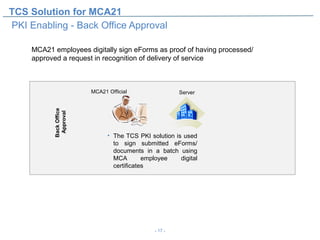
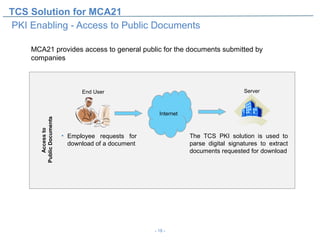
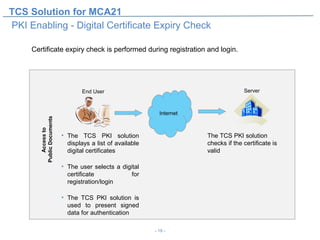
The document discusses MCA21, an initiative by the Ministry of Corporate Affairs in India to provide easy and secure access to MCA services. It aims to modernize MCA and facilitate business functions. The TCS solution for MCA21 includes an e-forms filing flow, certificate issuance and management using a PKI, which allows for digital signatures on filed documents. Key features of MCA21 include online company registration, annual filings, and public access to company records. It has processed millions of documents and digital certificates since launching in 2006.