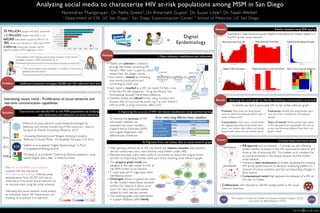
This research aims to characterize HIV at-risk populations among men who have sex with men (MSM) in San Diego by analyzing social media data. The researchers collect tweets from San Diego and classify them based on risk categories like drug use, sex venues, etc. They build a social network graph of Twitter users and their connections and compare the structure to the real-world HIV transmission network. Exploratory analysis of the social graph reveals patterns in topics of discussion and network structures that can help predict HIV transmission risk and enable prevention efforts. Future work includes further data collection, interactive visualizations, and computational models to understand how the social network evolves and relates to the sexual network transmitting HIV.