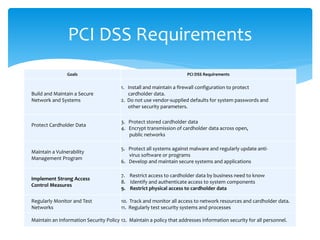
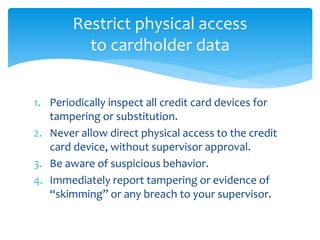
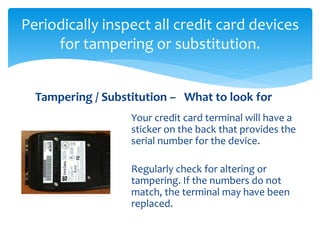
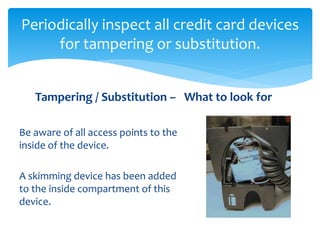
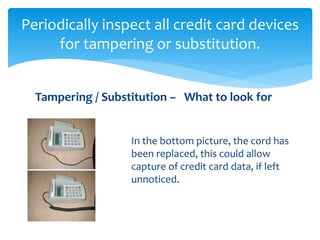
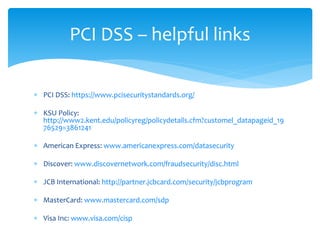
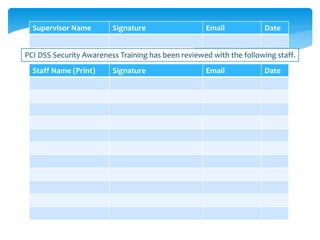
This document provides information about the Payment Card Industry Data Security Standard (PCI DSS) and requirements for organizations to protect customer payment card data. It outlines goals of the PCI DSS such as building secure networks, protecting stored data, and implementing access controls. Specific access control requirements discussed are restricting physical access to payment card devices, periodically inspecting devices for tampering, not allowing unauthorized access, being aware of suspicious behavior, and reporting issues. The document provides examples of what to look for when inspecting devices and guidelines for restricting physical access to payment card data.