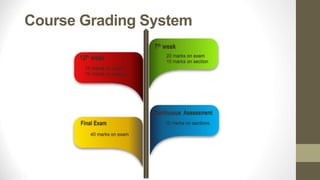
This document provides an overview of a course on security in software engineering. The course goals are to explain the need for computer security, how to meet security requirements using established techniques, and how to address risks through novel technologies. The course introduces security best practices and techniques for evaluating security solutions. It is taught by Dr. Nada Hany Sherief and provides contact information. The grading system and course timeline are outlined. Course material includes a textbook, lectures, and assignments available online. The document concludes with definitions from the glossary.