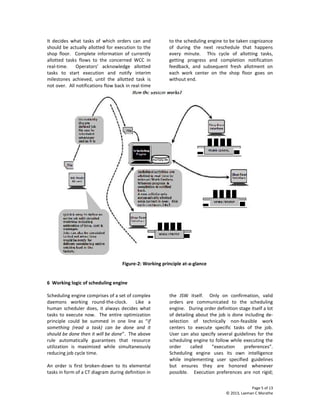
This white paper discusses the critical importance of efficient scheduling in manufacturing and project execution, highlighting its impact on cost and reliability of delivery. It introduces a new real-time production management system called Talika PMS that addresses common failings of conventional scheduling systems, providing a fully automatic and scalable solution designed to maximize resource utilization and minimize job cycle time. The document elaborates on the functionalities of Talika PMS, its feedback mechanisms, and how it adapts to real-time changes in the production environment.
![Page 1 of 13
© 2013, Laxman C Marathe
An Innovative Real Time Production Management System
A white paper
Abstract
Scheduling is indeed a major issue in all manufacturing and project execution facilities world over. It is also
recognized that if scheduling is efficient and automated huge benefits could result as existing resource usage can
be maximized allowing dramatic increase in number of orders processed at the same time substantially reducing
cost of production while ensuring reliability in delivery on the committed date. No wonder scheduling is a hot
research topic and the market is flooded with scheduling systems of sorts. Still a truly efficient and automatic
scheduling system remains an elusive dream.
This white paper lists the six important reasons why a scheduling system fails in real-life situations. It then
describes how a new scheduling system called Talika PMS satisfies all the six critical requirements in detail with real
data supporting the claims from its first major installation.
Visit www.etalika.in for more information and free download
1 Introduction
Day-to-day scheduling of any manufacturing facility
is recognized to be the most important problem to
be solved. [1] D. Ouelhadj and S. Petrovic recent
[Oct 2008] study reveals that solutions based on
creation of a static schedule are impractical in real-
life situations and discusses several dynamic
scheduling approaches only to conclude that more
work is still needed in this field of research.
We wish to present here a complete dynamic real-
time micro level scheduling system that is proven to
work in the most complex manufacturing facilities. It
is a fully scalable, decentralized, multi-location and
user configurable system to suit any manufacturing /
project environment. The core scheduling is fully
automatic and guarantees that all currently allotted
tasks in real-time can be executed with a complete
and detailed schedule prediction of all activities for
all orders in-hand. The system automatically
reschedules in response to real-time events as
notified by operators’ handling current tasks on the
shop floor, with an objective to maximize resource
utilization while minimizing job cycle time. It offers
full micro-level future schedule visibility of all
running jobs to predict when each would be over
given the current load as of NOW. The cycle of
allotting tasks, seeking task-wise feedback on
allotments made from operators’ on shop floor, and
re-predicting its impact in subsequent reschedule
happen every minute 24x7.
Before we elucidate more on the system features we
would like to re-emphasis importance of scheduling
in any manufacturing facility and why current
solutions fail to address the problem correctly.
2 Importance of scheduling
The only real differentiators to compete in
established products and services market are Cost
and Reliable delivery. Quality of product / service is
mostly considered a pre-condition to be in business
rather than a differentiator. Both cost and reliable
delivery of product / service are directly impacted by
scheduling.
2.1 Scheduling and cost of production
It is almost axiomatic to state that a major portion of
cost of production (even exceeding 70% - 80% in
made-to-order industries) is expended in
coordinating and managing production activities vis-
à-vis the actual cost of value-addition involved.
Most real life manufacturing involves execution of
several individual activities in a complex order to
create any saleable final product or service. The
starting point thus is in breaking down an order
requirement into elemental activities that must be
completed in order to accomplish the final product /
service deliverable: ranging from getting inputs or
raw material until final packing and dispatch. Unless
this detailing is not done, actual value addition
cannot begin. Once it is known “How” the order can
be fulfilled the most difficult job of scheduling](https://image.slidesharecdn.com/ourwhitepapertalikapms-130423041852-phpapp02/75/An-Innovative-Real-Time-Production-Management-System-1-2048.jpg)
![Page 2 of 13
© 2013, Laxman C Marathe
individual activities of orders begin. It primarily
translates in deciding what activity must be done,
where it should be done (that is using what limited
resources) and when. One can refer to them as the
3W’s. Most expensive and competent personnel in
any manufacturing or project execution facility are
engaged fully in the process of managing production
that involves, breaking down order execution,
estimating its cost, time and wastages, deciding
what activities to do now and next, taking feedback
on progress made, follow-up and expediting to meet
deadlines. The whole exercise is repeated all over
again by rescheduling to predict and monitor
expected completion dates for all orders in hand.
Add to this already complex situation, the burden of
estimating when new orders can be delivered given
the existing load of orders already in-hand. All this is
now possible to be completely automated resulting
in a substantial reduction in the cost of production.
2.2 Scheduling & reliability
Scheduling decisions taken now directly impact
expected completion times of all orders in-hand. In
real-life situations one has to deal with several
orders, each with its own set of individual
interdependent activities requiring a certain profile
of resources that are both shared and limited. It is
well impossible, even in small setups, to manually
figure-out impact of real-time decisions on predicted
completion dates.
Honoring delivery on committed date is more
important than how fast one turns around an order
in a manufacturing facility. It is only possible to do
so, if one is in a position to predict impact of all
scheduling decisions taken now on all orders in-hand
in real time as an on-going process.
3 Why conventional scheduling systems fail in the
real world?
3.1 Static scheduling
Scheduling is a widely misunderstood term. Many
believe plotting activities to be performed on
different resources on a time scale (Gantt chart)
make a schedule. Actually a Gantt chart is just a
snap shot of what is likely to happen in the future
given the situation NOW. As one progresses in time
this representation will change because predictions
seldom match reality owing to unexpected
disruptions [3] & [5].
So, any scheduling system that fails to respond to
changing situation on ground by failing to reschedule
and redraw its prediction (Gantt chart) is a misfit in
real life making purported schedule optimality and
efficiency claims hypothetical.
3.2 No feedback mechanism
A scheduling system can only be responsive to what
is happening on the shop floor if a feedback
mechanism exists. This feedback mechanism should
be both real-time and automatic. Peter Cowling and
Marcus Johansson [2] argue in a well researched
paper that “in many production processes real time
information may be obtained from process control
computers and other monitoring systems, but most
existing scheduling models are unable to use this
information to effectively influence scheduling
decisions in real time”. This is a major disconnect
making the schedule infeasible as it is soon out of
synchronization with reality.
We have recognized that the only authentic real-
time source of feedback information from the shop
floor is the personnel (Operators’) in charge of
performing individual activities. However, each
operator can only give feedback on what each one
does and that too ideally limited to the current task
in-hand. We achieve a seamless feedback
mechanism to the scheduling engine by allocating
elemental executable tasks in real-time to individual
Operators, and seeking task-specific feedback for
each such allotted task. The process of task
allotment, progress feedback and subsequent
reschedule to decide what to do next happens 24x7
automatically.
3.3 Schedule not actionable
The decision to execute an elemental task or activity
of an order requires one to take into account several
aspects; availability of inputs, availability of
resources and technical feasibility of performing the
task. Most scheduling systems usually fail on this
count. Proposed activities are either not actionable
or represent a group of activities leaving the decision
of what exactly to do now to the operators. In order
to circumvent this problem, many systems offer a
“drag & drop” facility to correct or manipulate
proposed schedule before it is released. As [4] P.](https://image.slidesharecdn.com/ourwhitepapertalikapms-130423041852-phpapp02/85/An-Innovative-Real-Time-Production-Management-System-2-320.jpg)









![Page 13 of 13
© 2013, Laxman C Marathe
Console Function Number & Location
Factory dB Manager
(FDM)
System is fully user configurable and all
this information resides in one logical
database called the factory dB.
However, user must have a means to
modify the factory dB without affecting
current working system. FDM allows
one to check-out locally a copy of the
factory dB for manipulation / change,
revalidate it and check-in the factory dB
when finalized.
As many as required.
Money Management
Console (MMM)
All monetary information generated by
the scheduling core is fetched
periodically by this console for financial
accounting purposes. One can then
build or dove tail this information into
any existing financial ERP system.
As many as required. Only in
concept stage.
Human Resource
Consoles (HRC)
Manpower information like past usage,
current manning information being used
and future requirements too flow from
the scheduling core. This console is
designed to cull out or control such
information or feed it into any existing
ERP system.
As many as required. Only in
concept stage.
References
[1] D. Ouelhadj, S. Petrovic - A survey of dynamic scheduling in manufacturing systems - Springer Science:
Journal Scheduling (2009) 12: 417–431 - Published online: 28 October 2008
[2] Cowling, P.; Johansson, M. - Production, Manufacturing and Logistics
Using real time information for effective dynamic scheduling - Elsevier: European Journal of Operational
Research 139 (2002) 230–244
[3] Guilherme, E.V.; Herrmann, J.W.; Lin, E. - Rescheduling Manufacturing Systems: A framework of
strategies, policies and methods - Journal of scheduling, Kluwer Academic Publishers, Netherlands
[4] Velaga P., Ph.D. (Scheduling) President, Optisol, 3910 Stony Creek Ln, College Station, Texas 77845 -
Advantages & Difficulties with Drag-and-Drop Operations – Web page link: http://www.optisol.biz/Drag-
and-Drop.htm
[5] Zhang L., Li, X., Gao, L., Yang, Y., Jiang , P. - Predictive/reactive scheduling with uncertain disruptions -
proceedings of the 41st international Conference on Computers & Industrial Engineering P 260-265](https://image.slidesharecdn.com/ourwhitepapertalikapms-130423041852-phpapp02/85/An-Innovative-Real-Time-Production-Management-System-13-320.jpg)