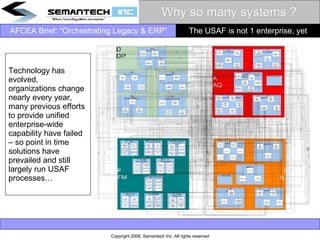
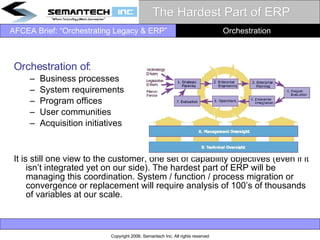
The document discusses the challenges faced by the USAF in updating its legacy IT systems and implementing ERP solutions amidst modernization efforts. It highlights the risks associated with a 'big bang' strategy for ERP and emphasizes the need for coordinated funding and process integration between legacy and ERP systems. Additionally, it calls for a pragmatic approach to address capability gaps and manage the complexities of system transitions while ensuring continued operational effectiveness.