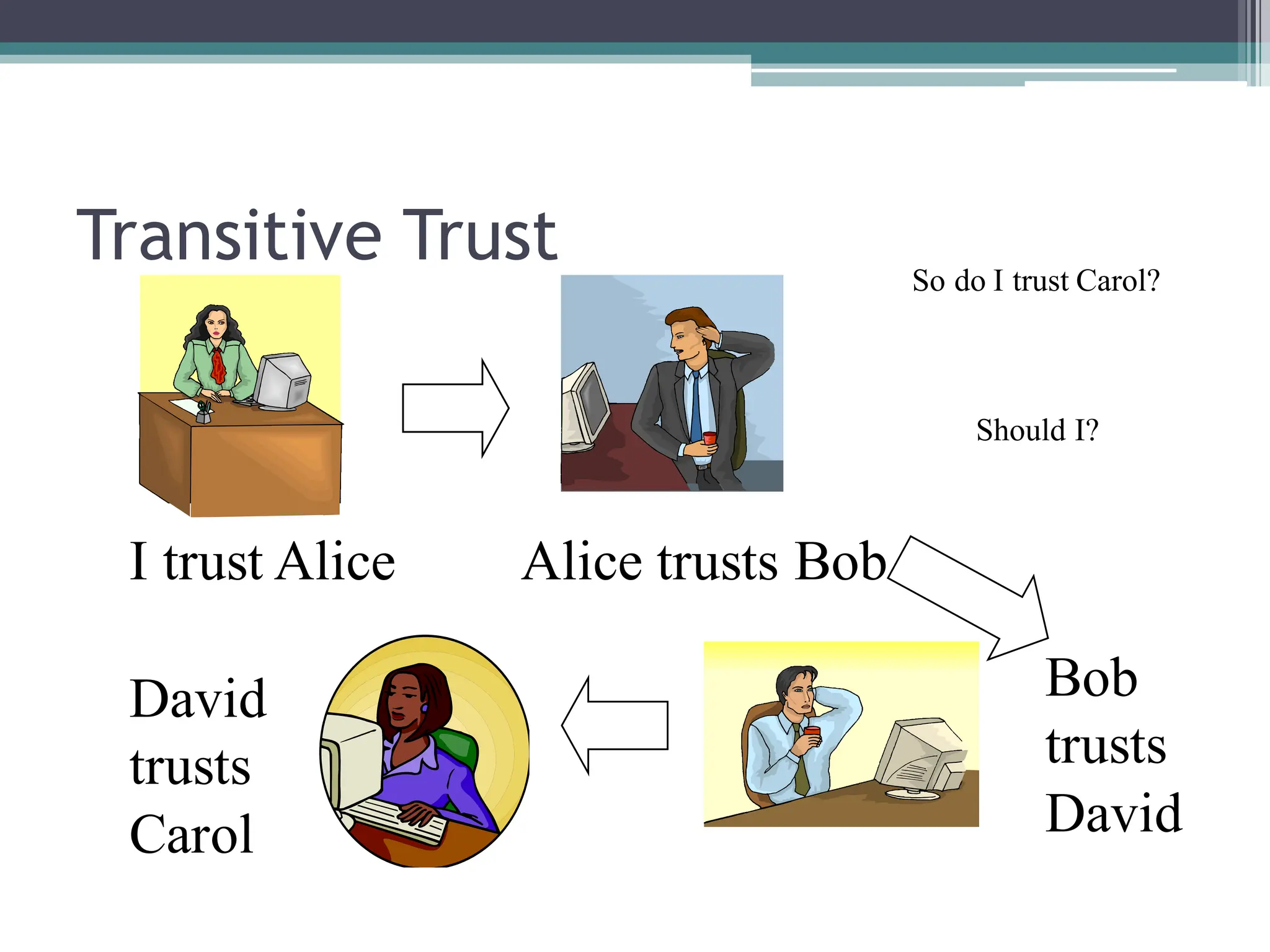
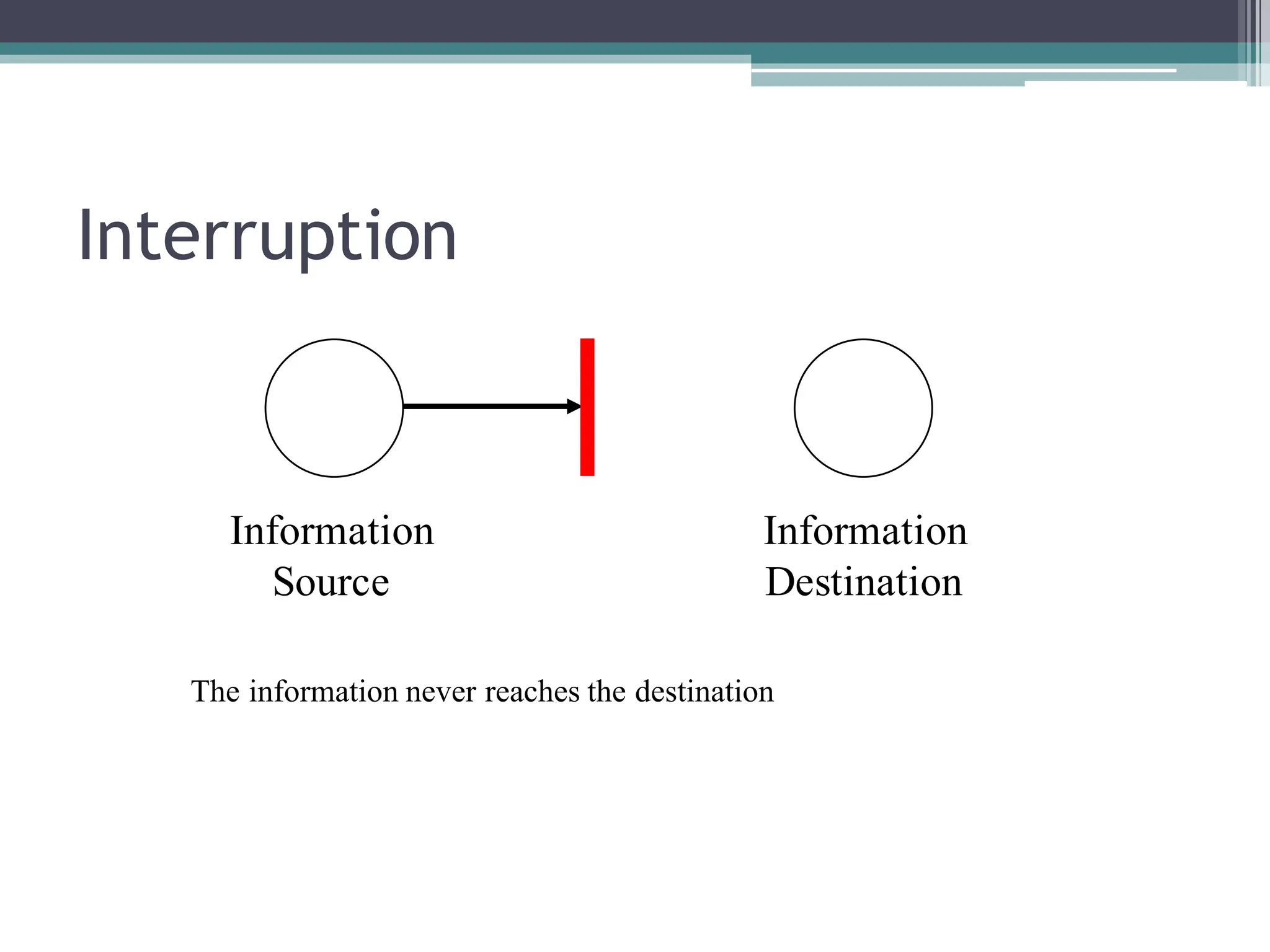
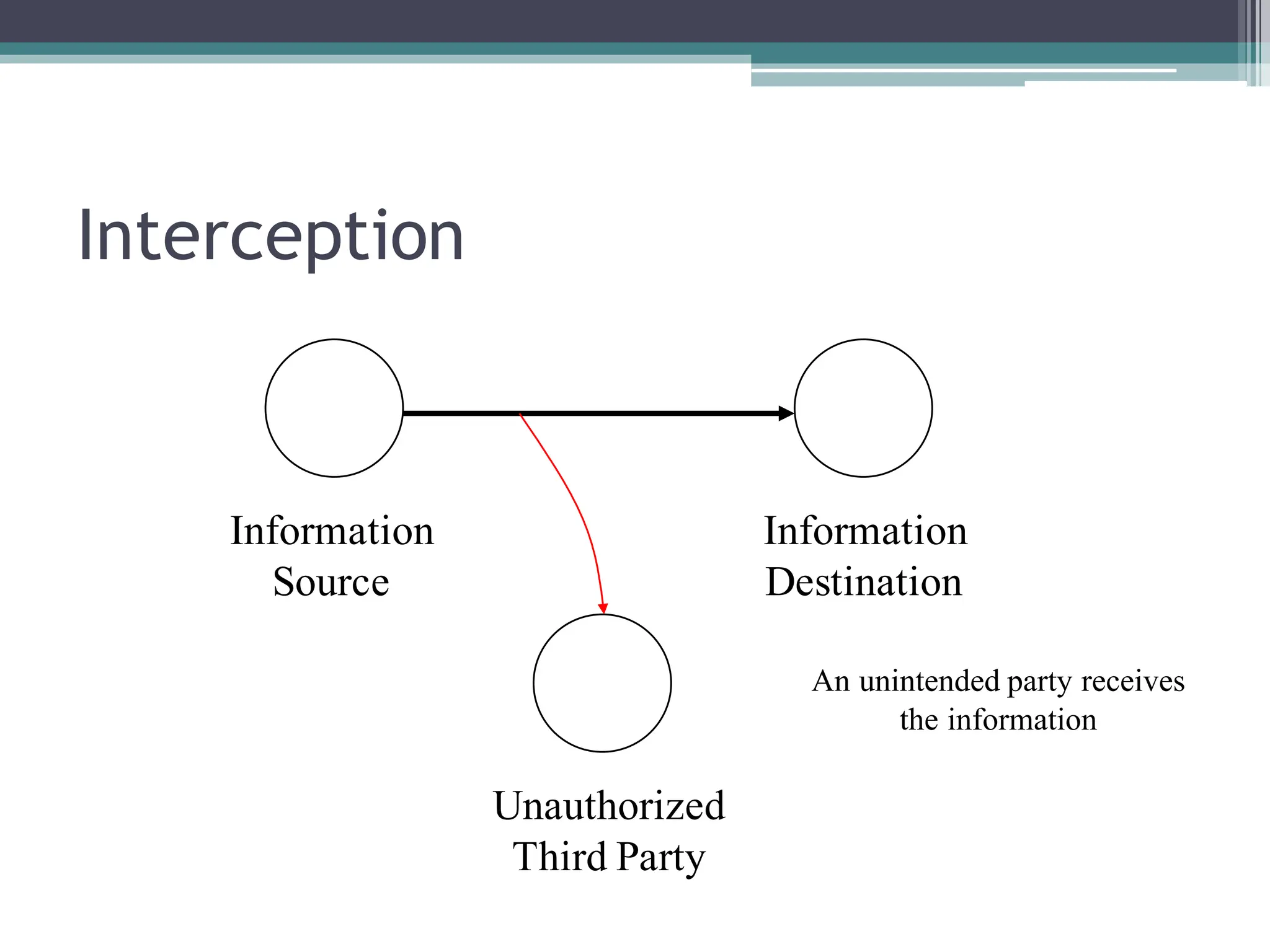
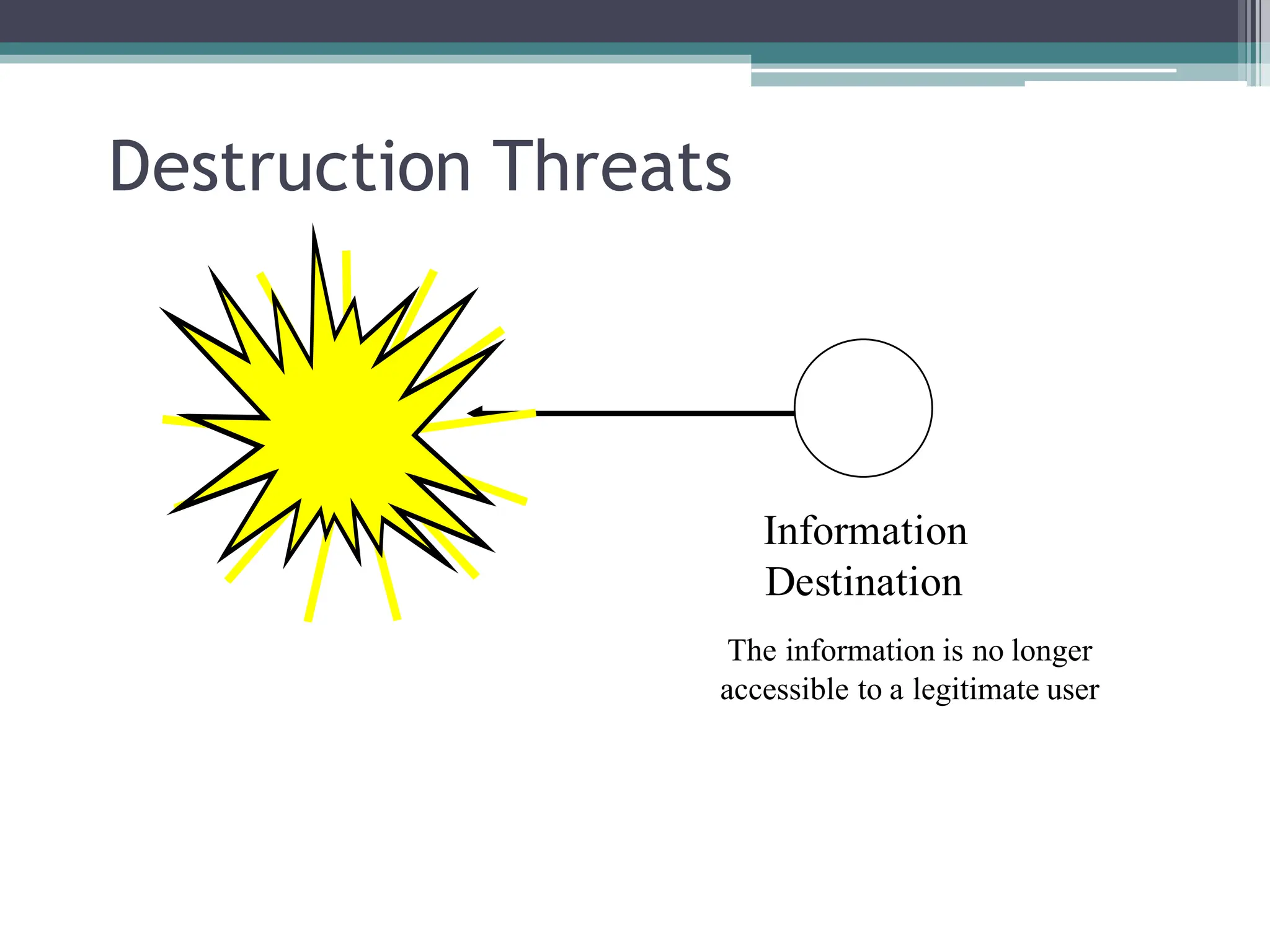
The document outlines a course on computer system security, covering fundamental topics like cryptography, access control, malware, and network security. It highlights the evolution of security concerns, common threats such as DDoS attacks and data breaches, and the challenges in securing systems amidst evolving threats and user ignorance. The course also emphasizes the importance of understanding trust, vulnerabilities, and the complexity of maintaining security in a hostile digital environment.