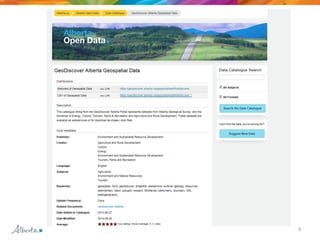
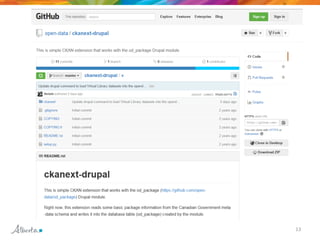
The Open Government Cyber Summit in September 2014 aimed to enhance transparency and citizen engagement in Alberta's government. It emphasized the importance of open data as a resource for fostering interconnected societies and encouraged collaboration through G8 principles. Key challenges discussed included procurement, copyright, privacy, and the need for a cultural shift within the government.