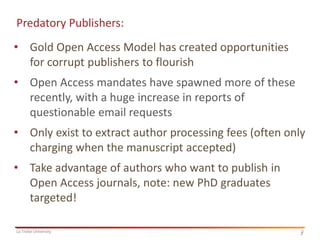
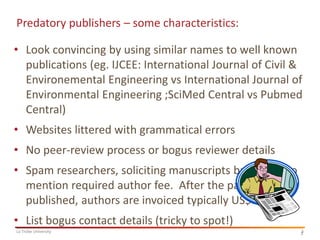
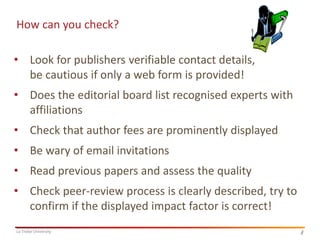
The document discusses the rise of predatory publishers, which exploit the gold open access model to extract fees from authors, particularly targeting new PhD graduates. Characteristics of these publishers include convincing names, lack of peer review, and questionable contact details, along with advice on how to identify and avoid them. Recommendations for checking journals include consulting Beall's list, assessing quality factors, and considering green open access options that avoid processing fees.