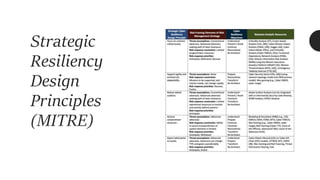
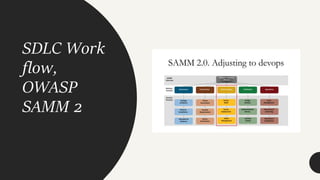
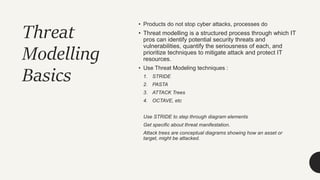
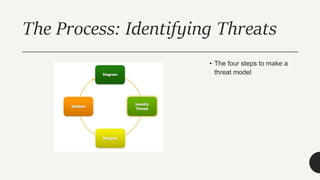
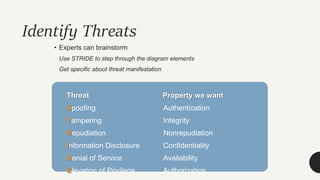
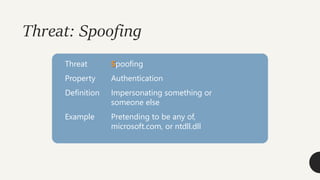
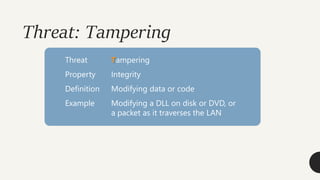
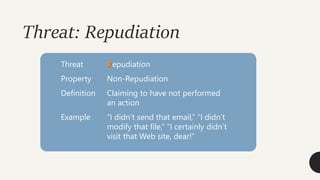
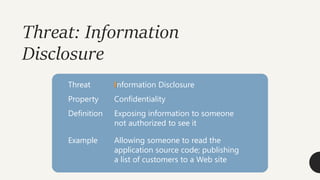
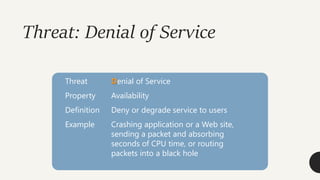
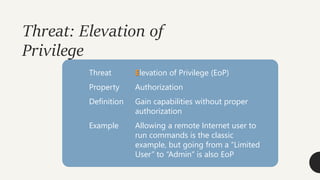
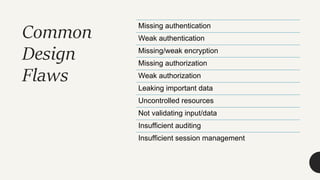
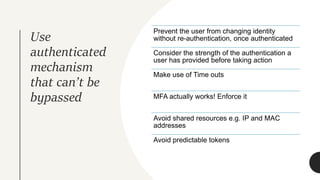
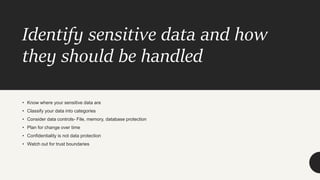
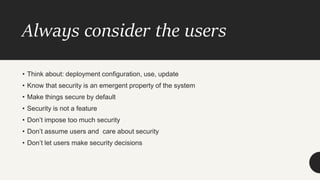
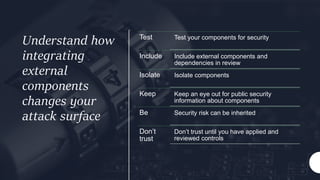
Joel Oseiga Aleburu presented on architecting for security resilience. The presentation covered basic definitions like security, vulnerability and resilience. It discussed basic principles for secure design like earning trust rather than assuming it. The presentation also covered application threat modeling, common architectural flaws, and questions. It emphasized that processes, not just products, prevent cyber attacks and outlined techniques like STRIDE for threat modeling.