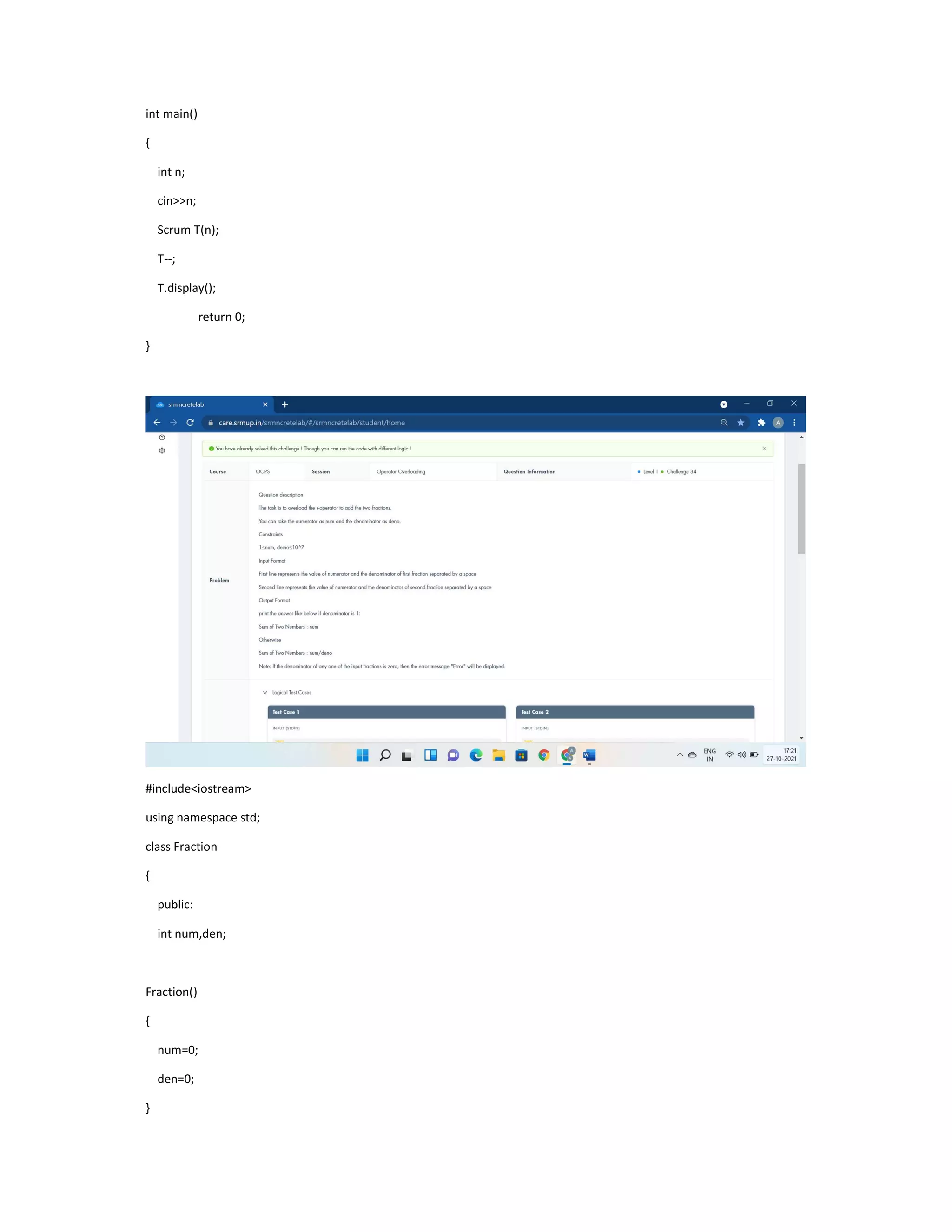
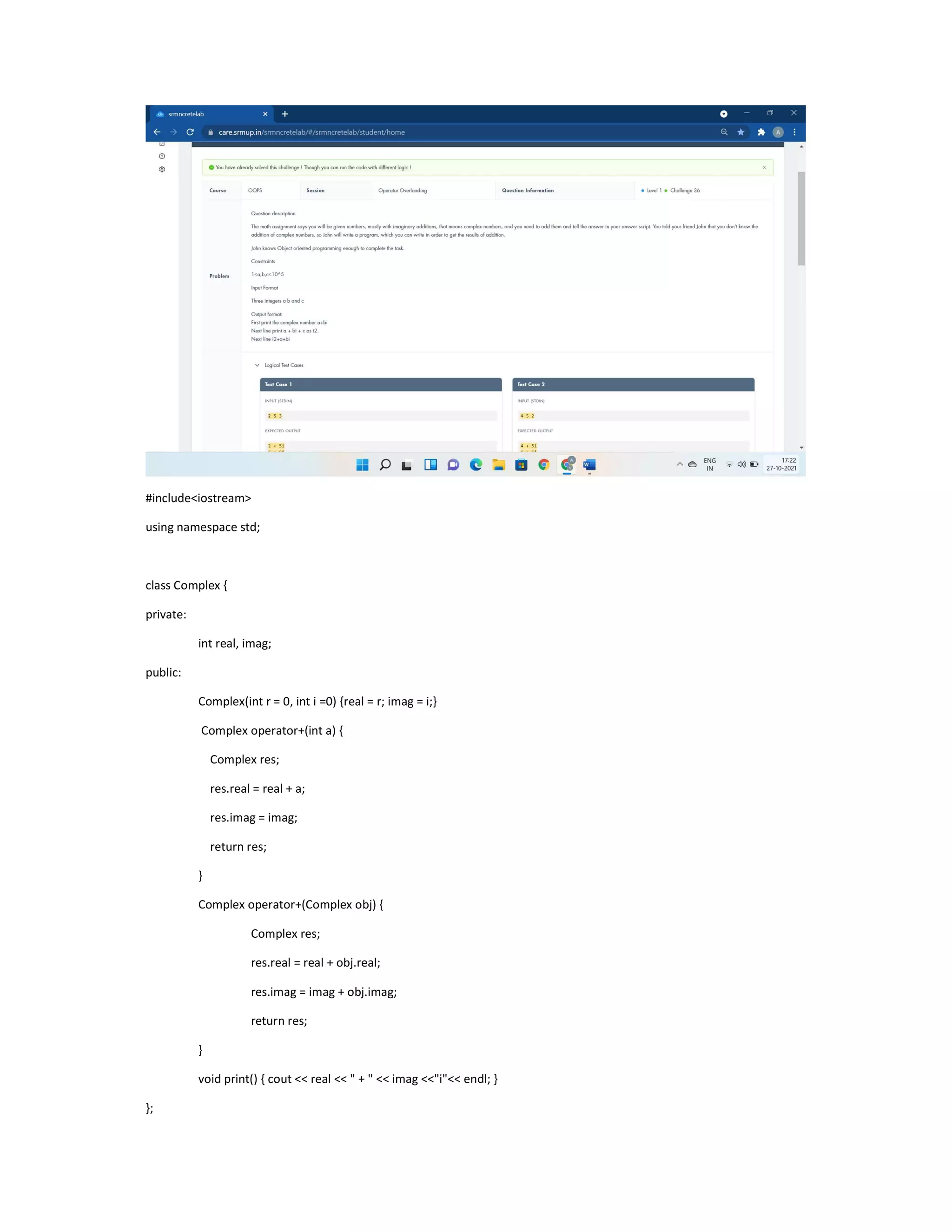
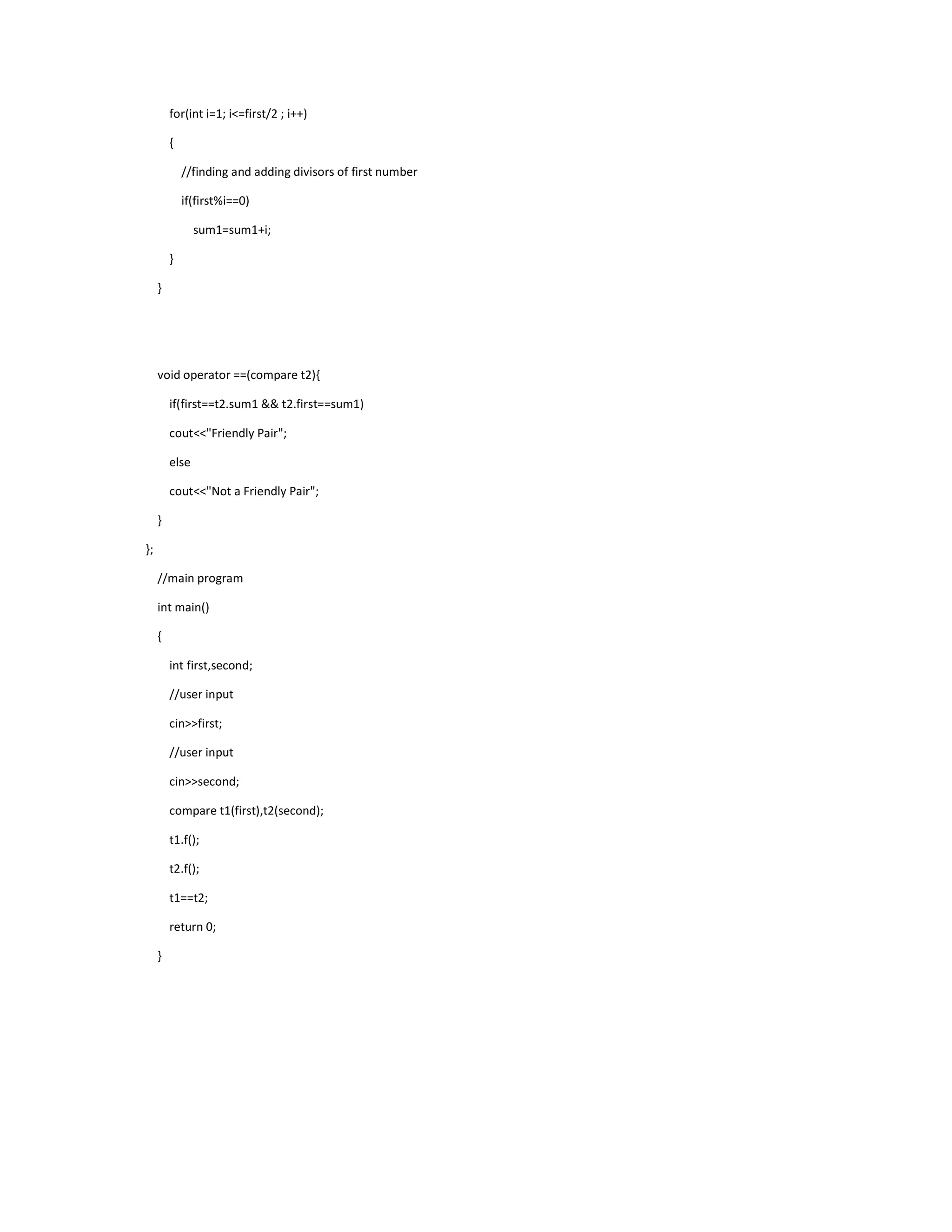
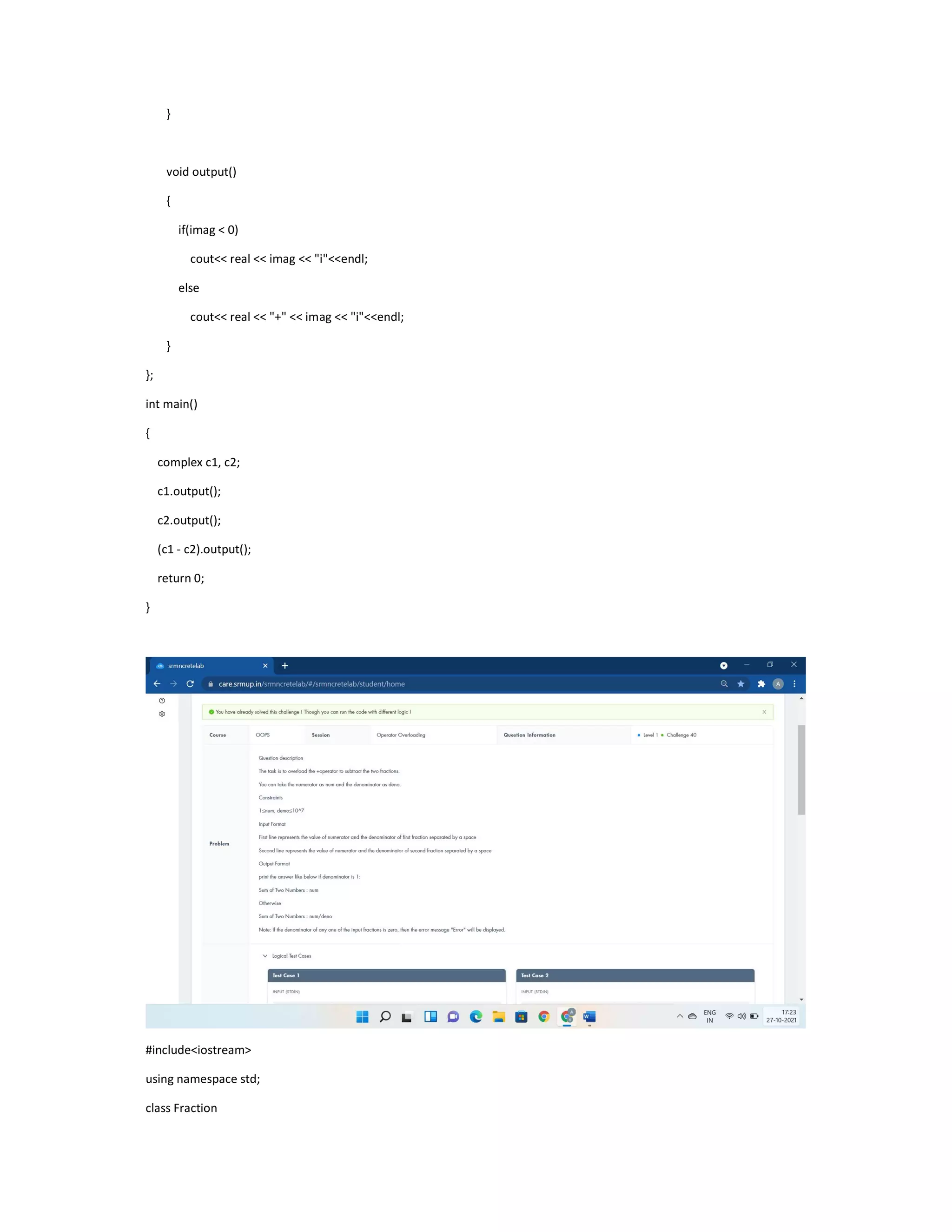
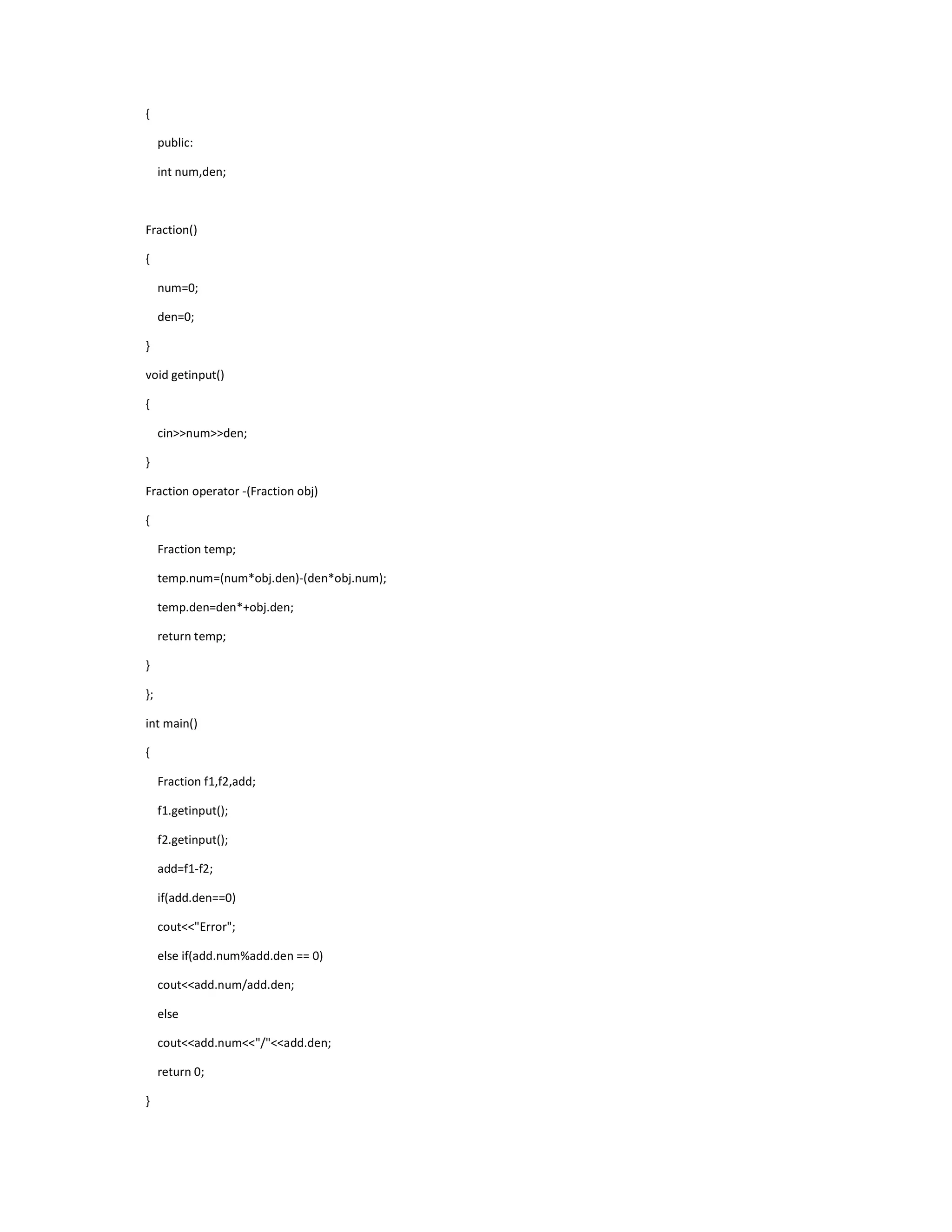
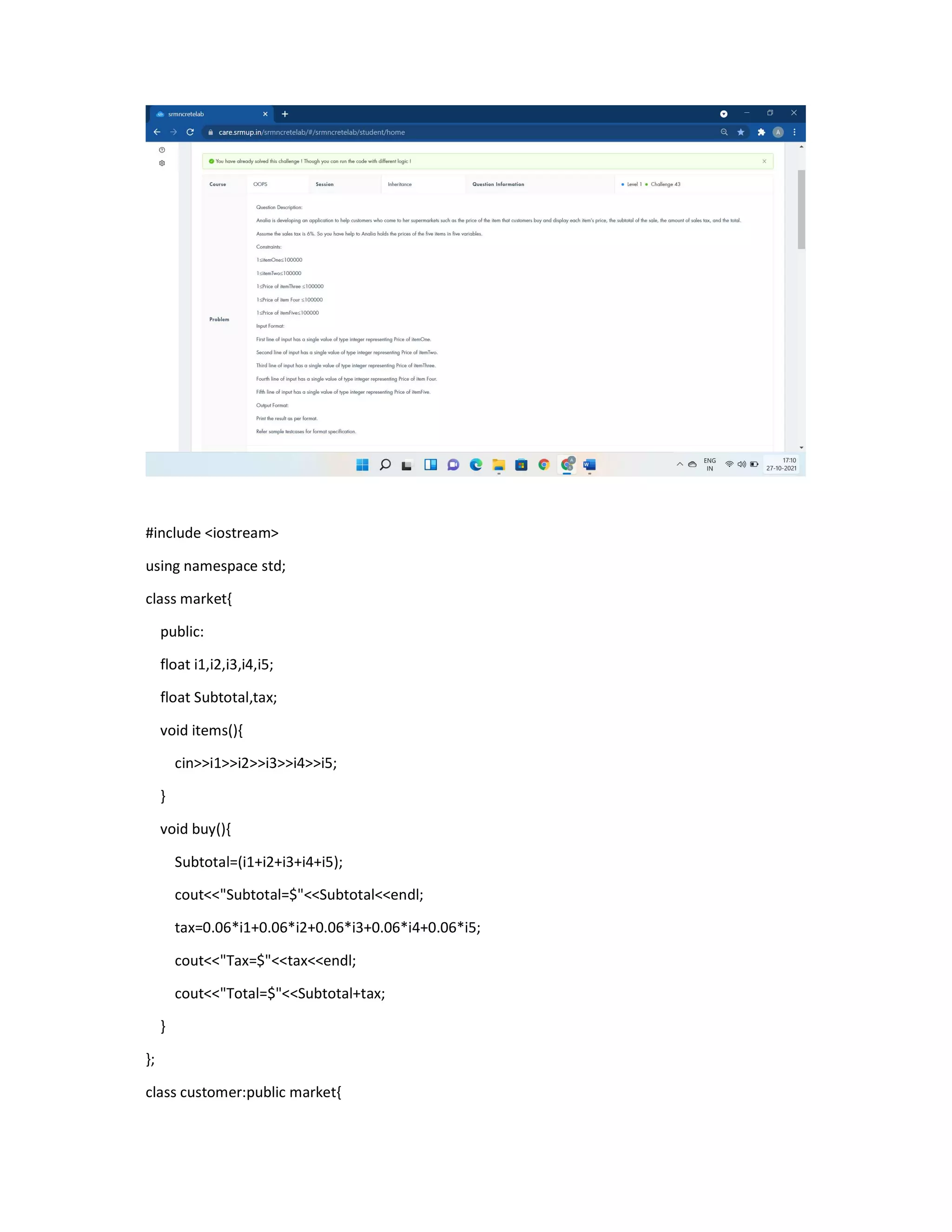
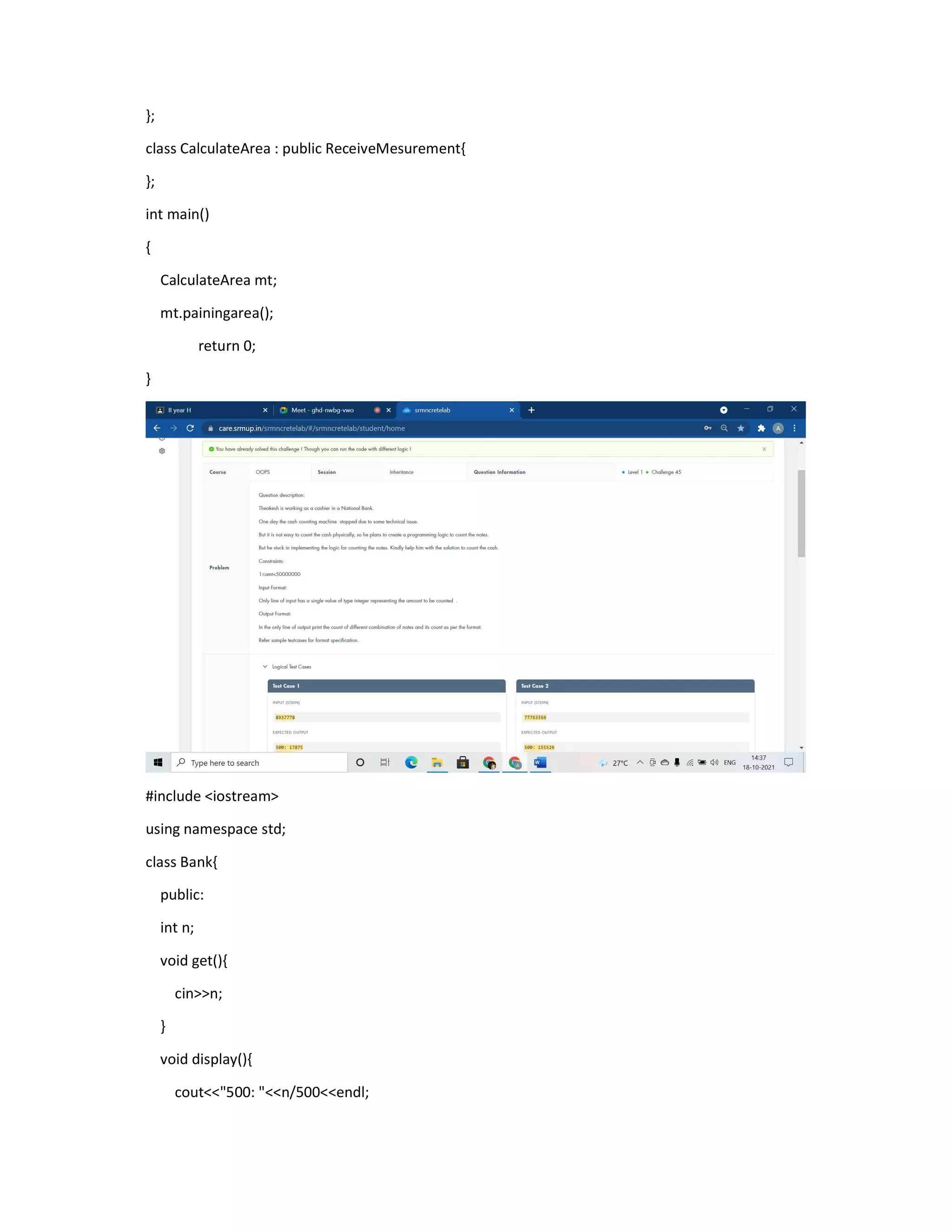
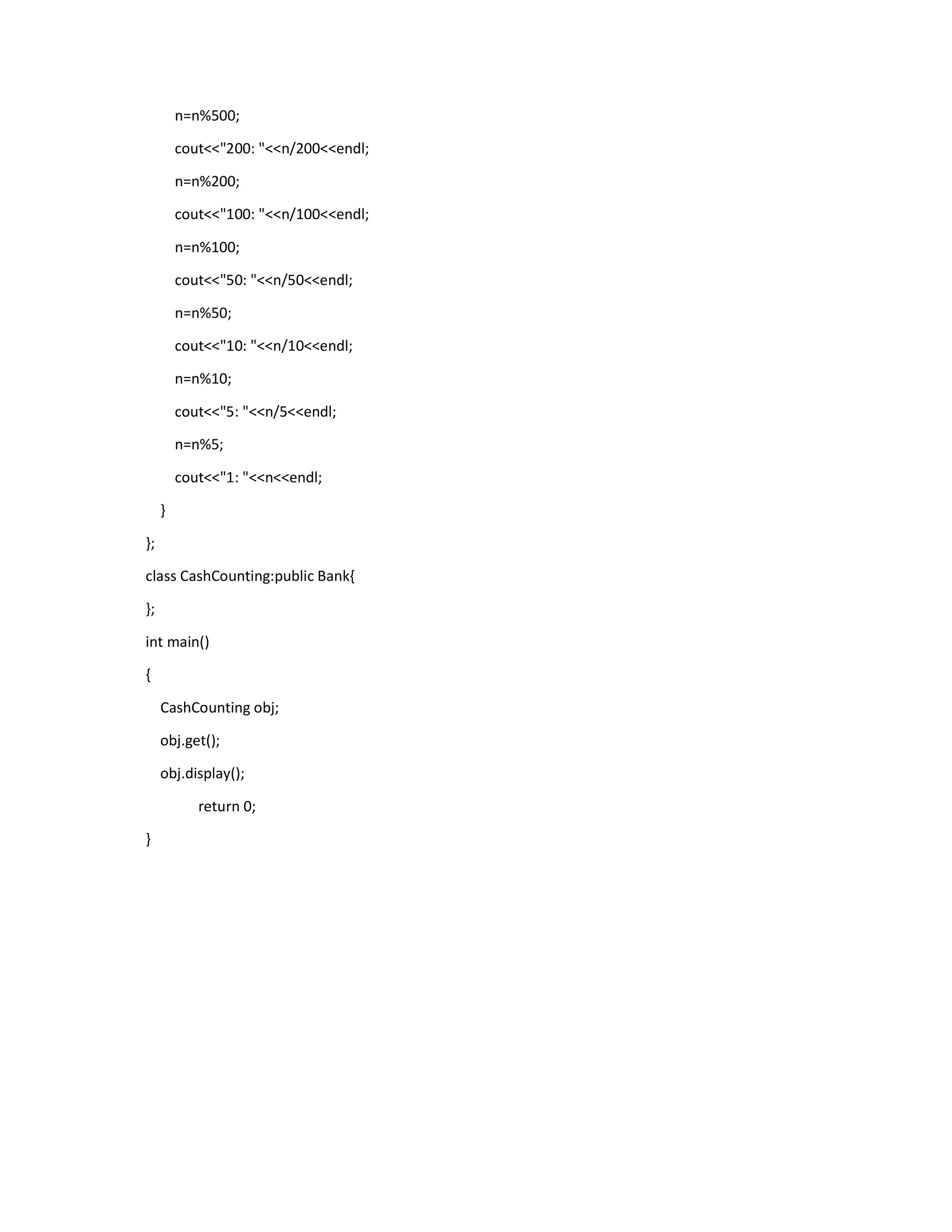
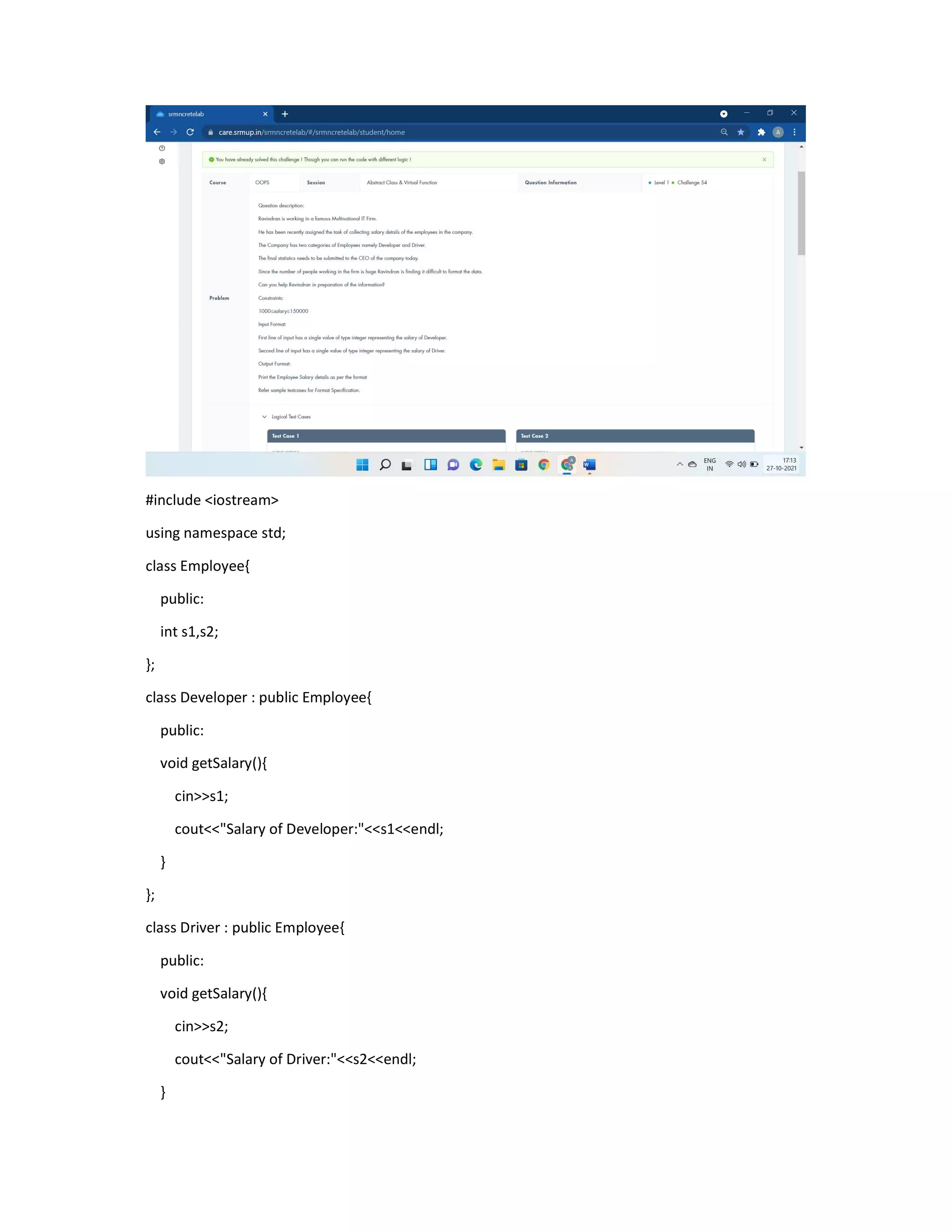
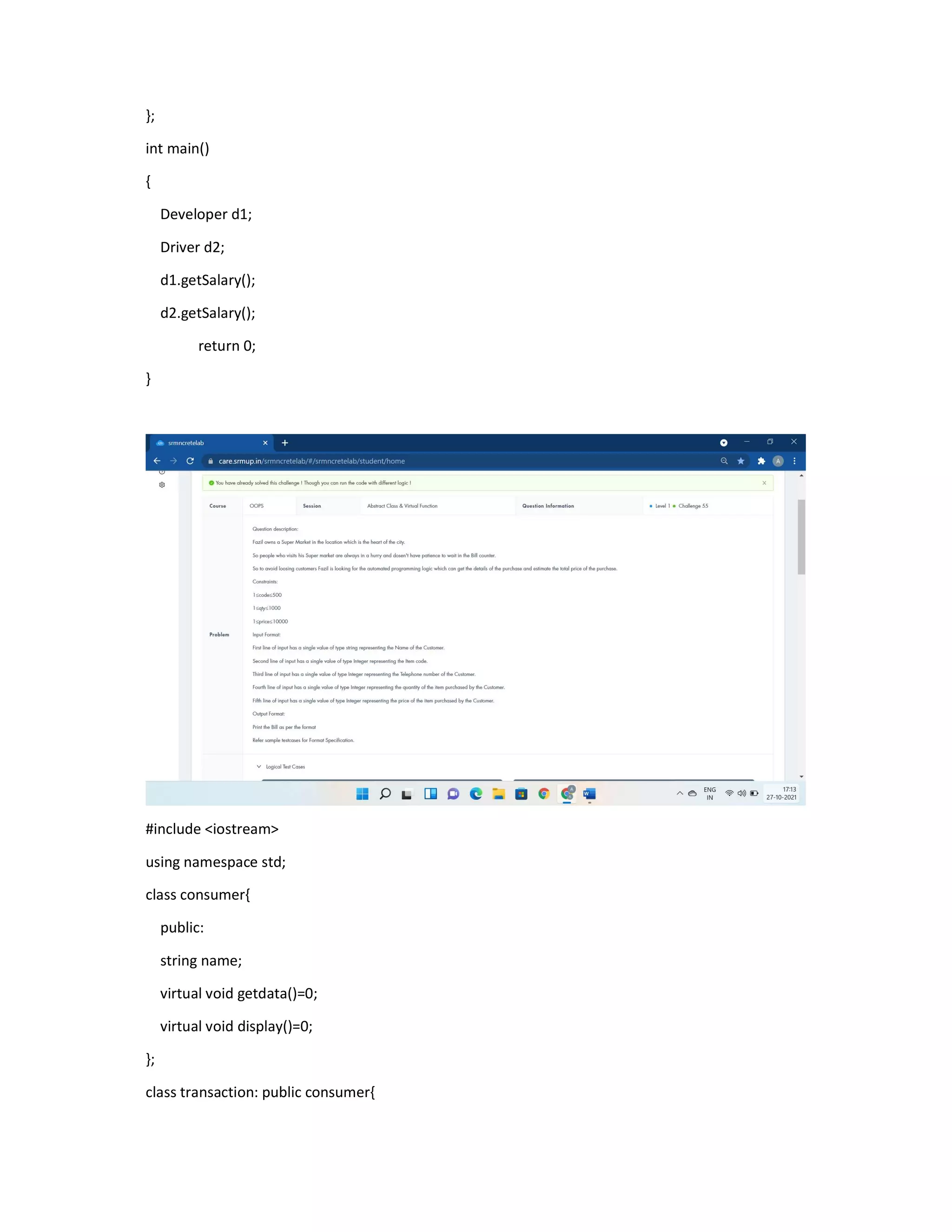
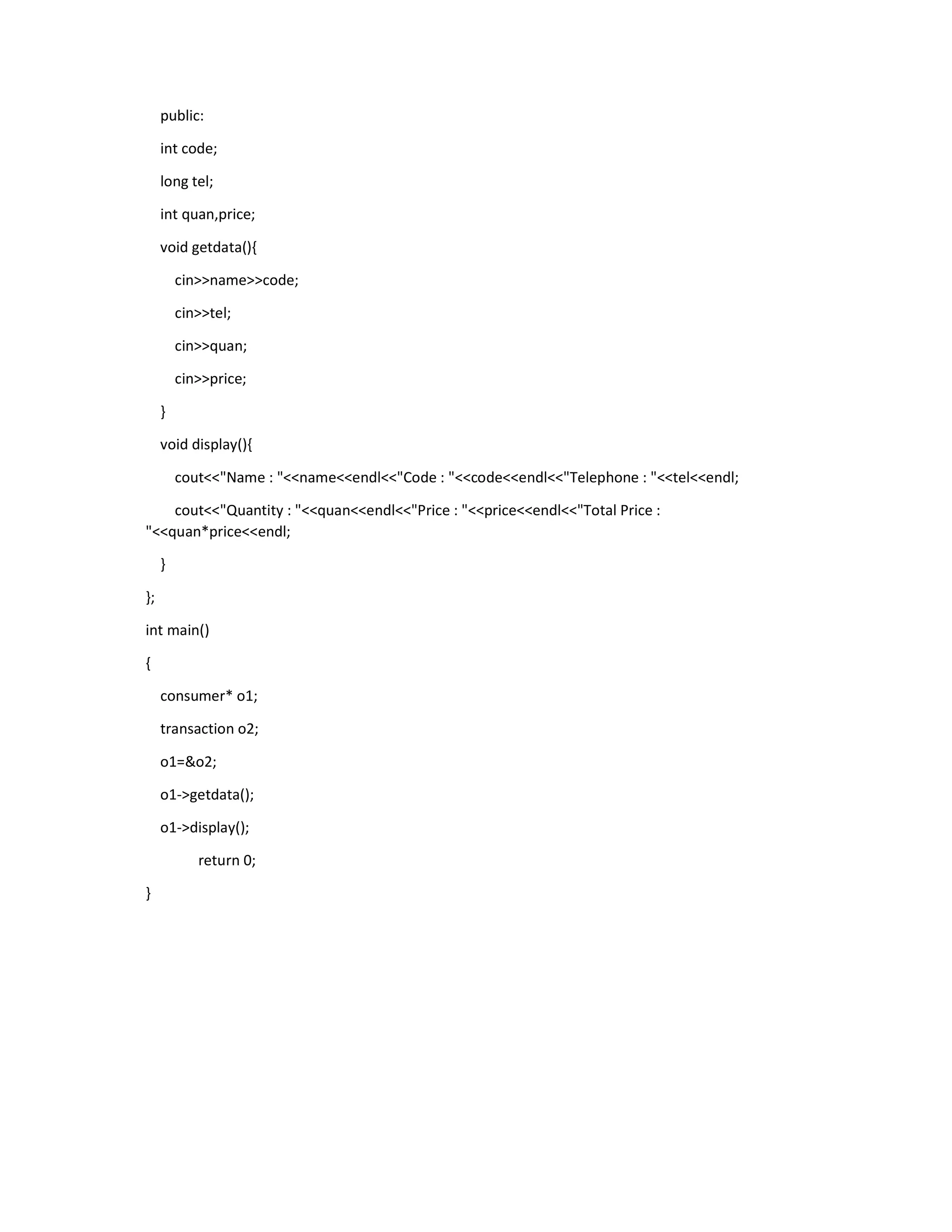
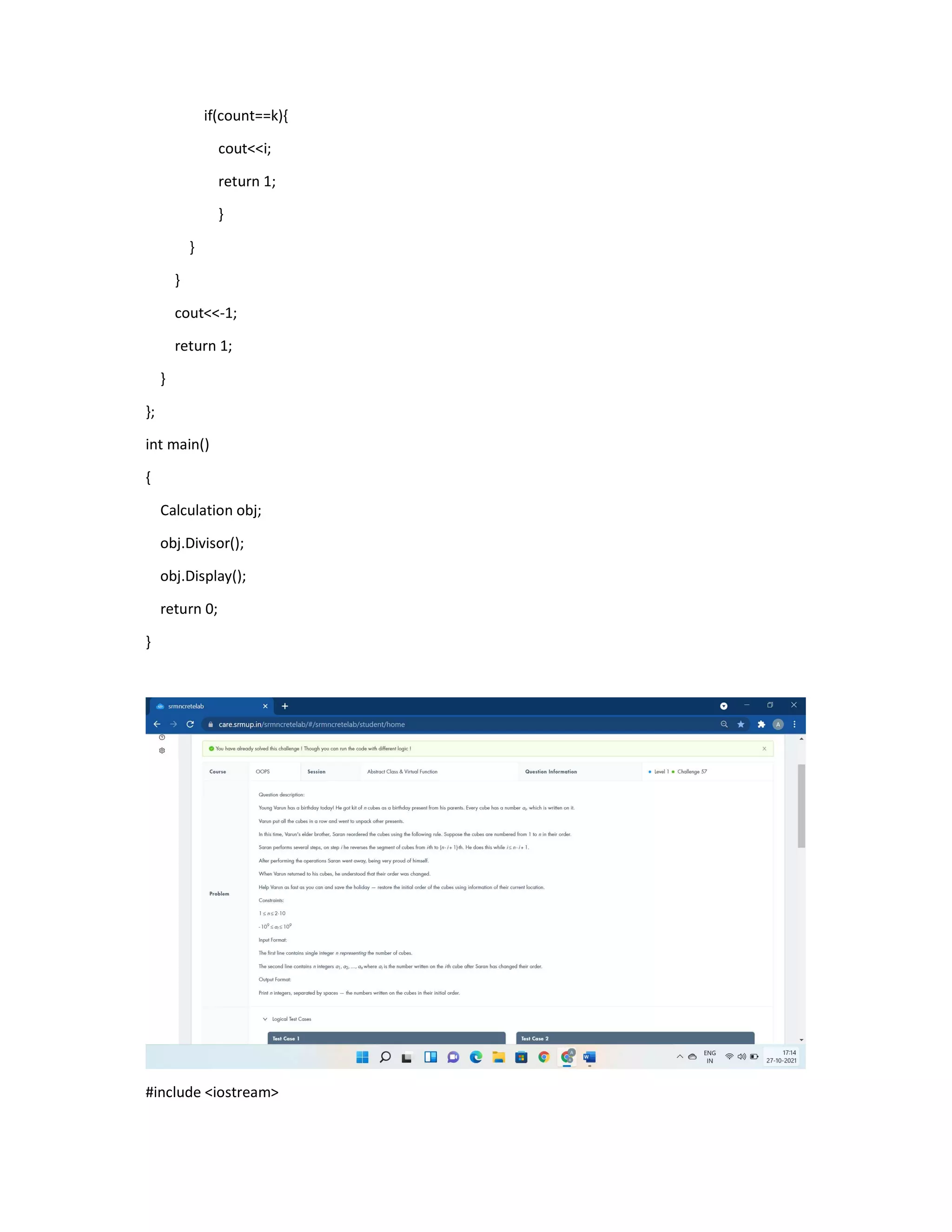
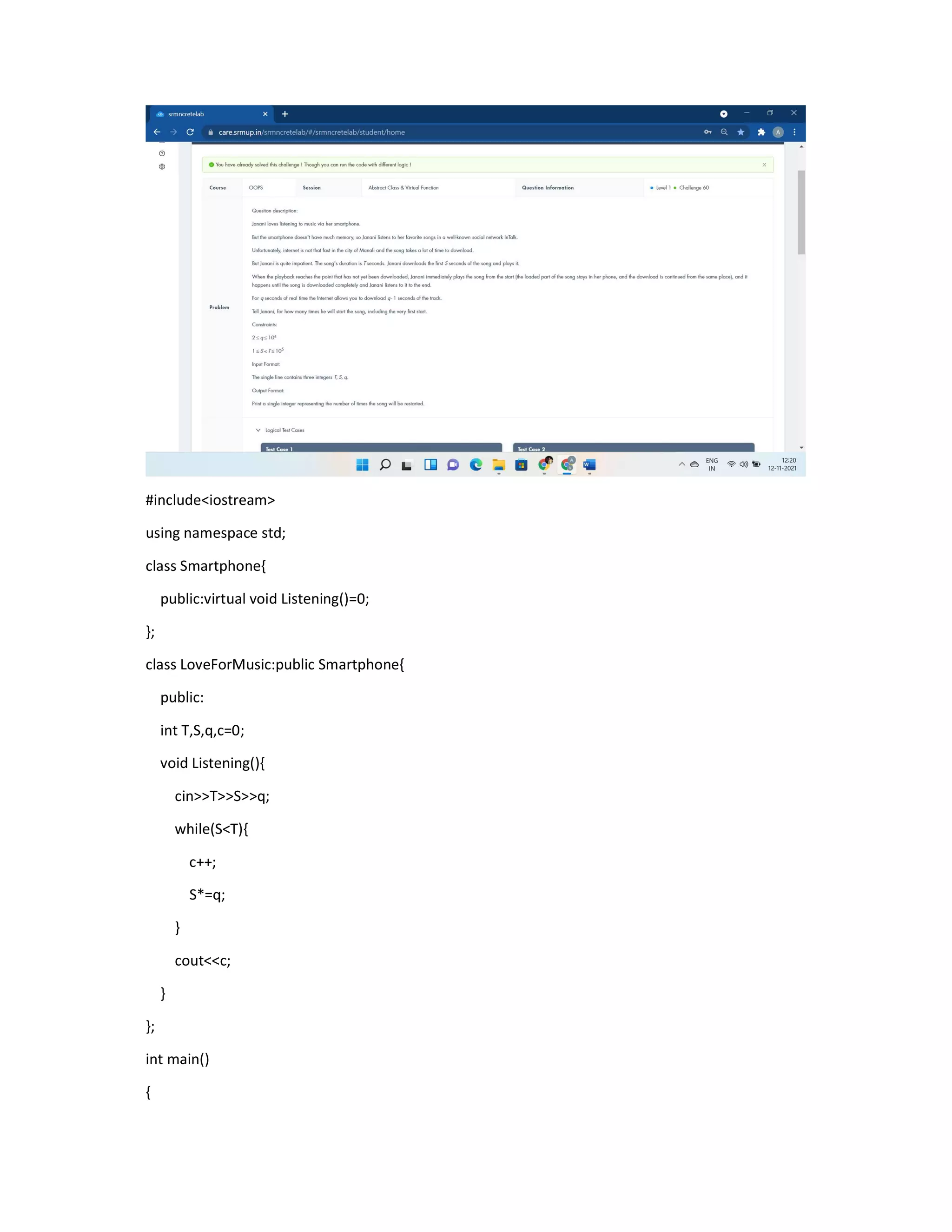
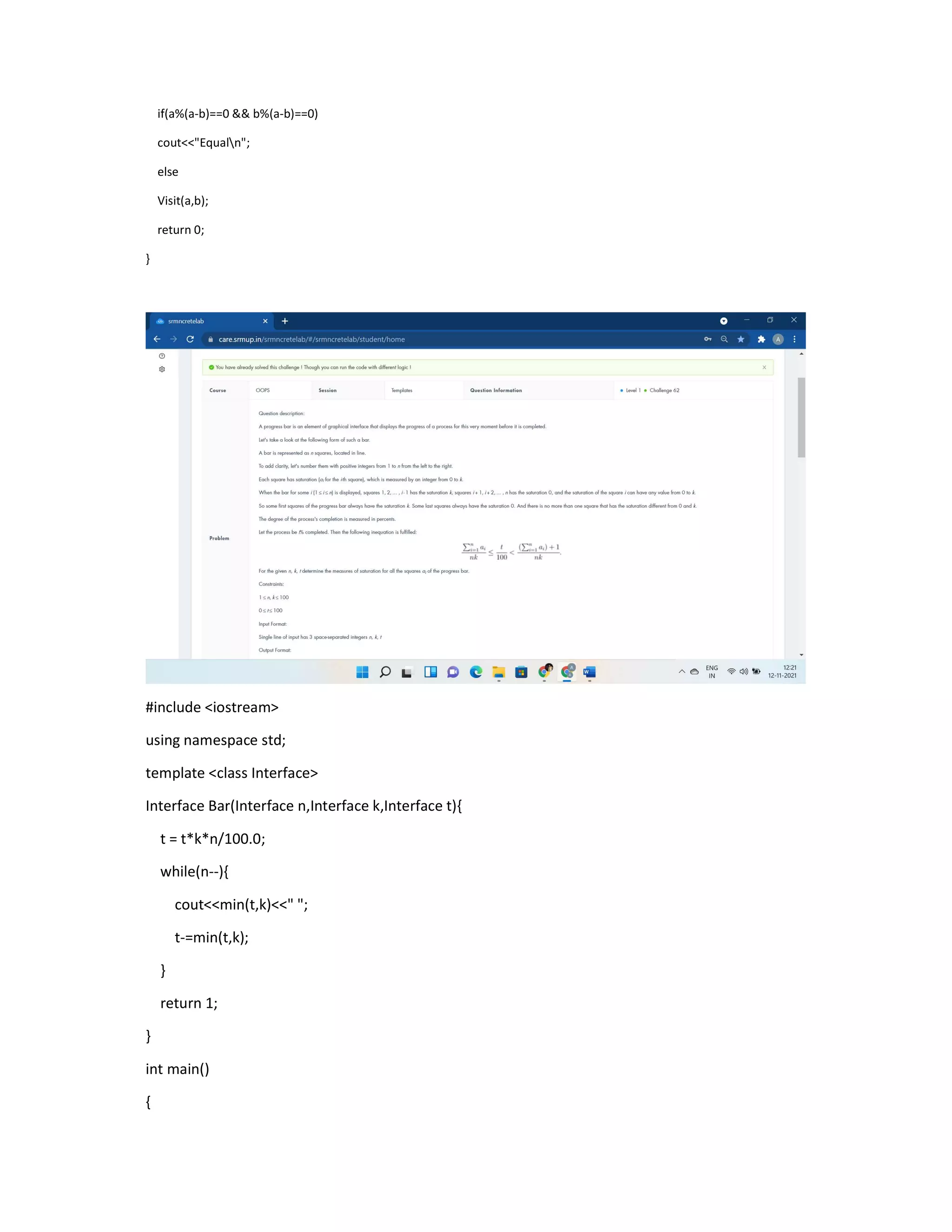
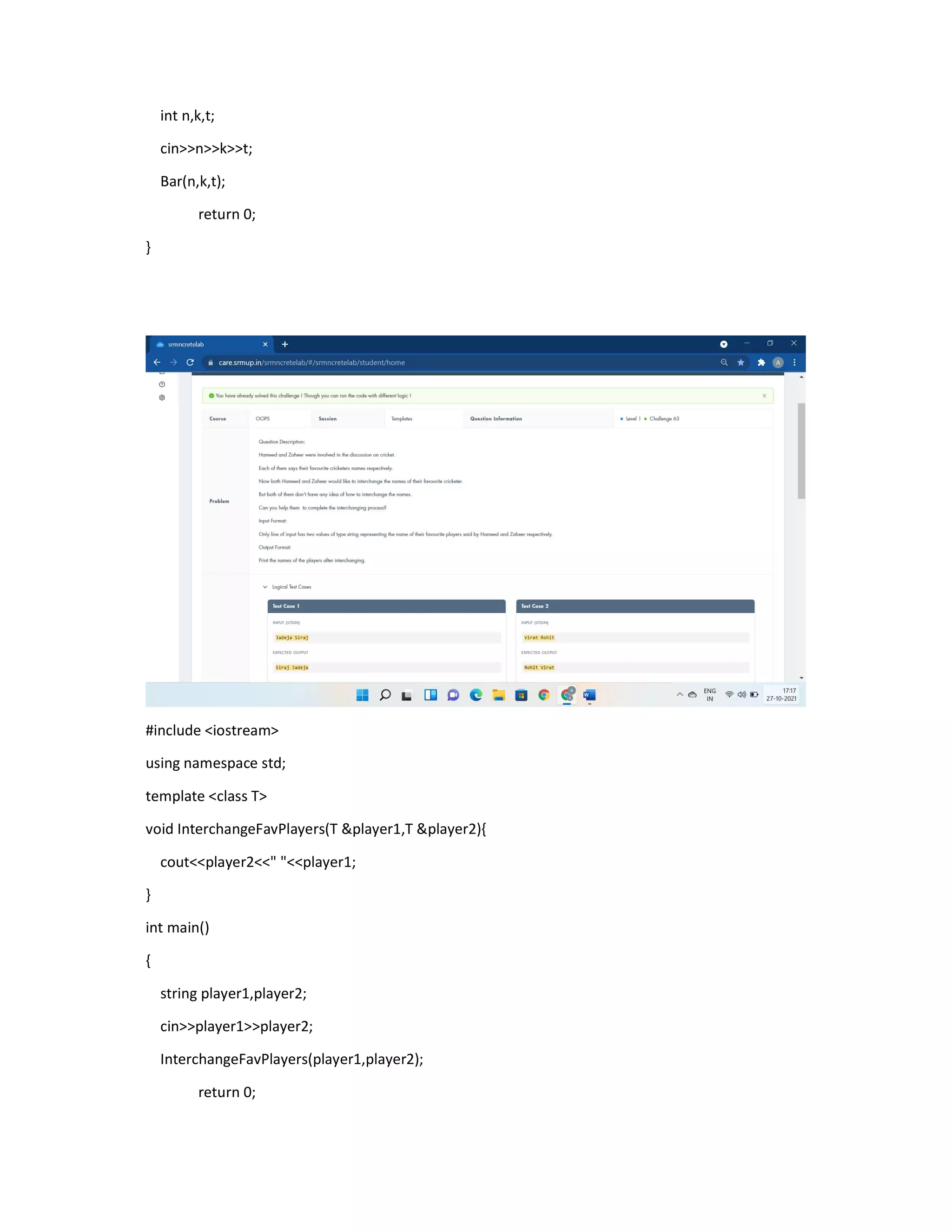
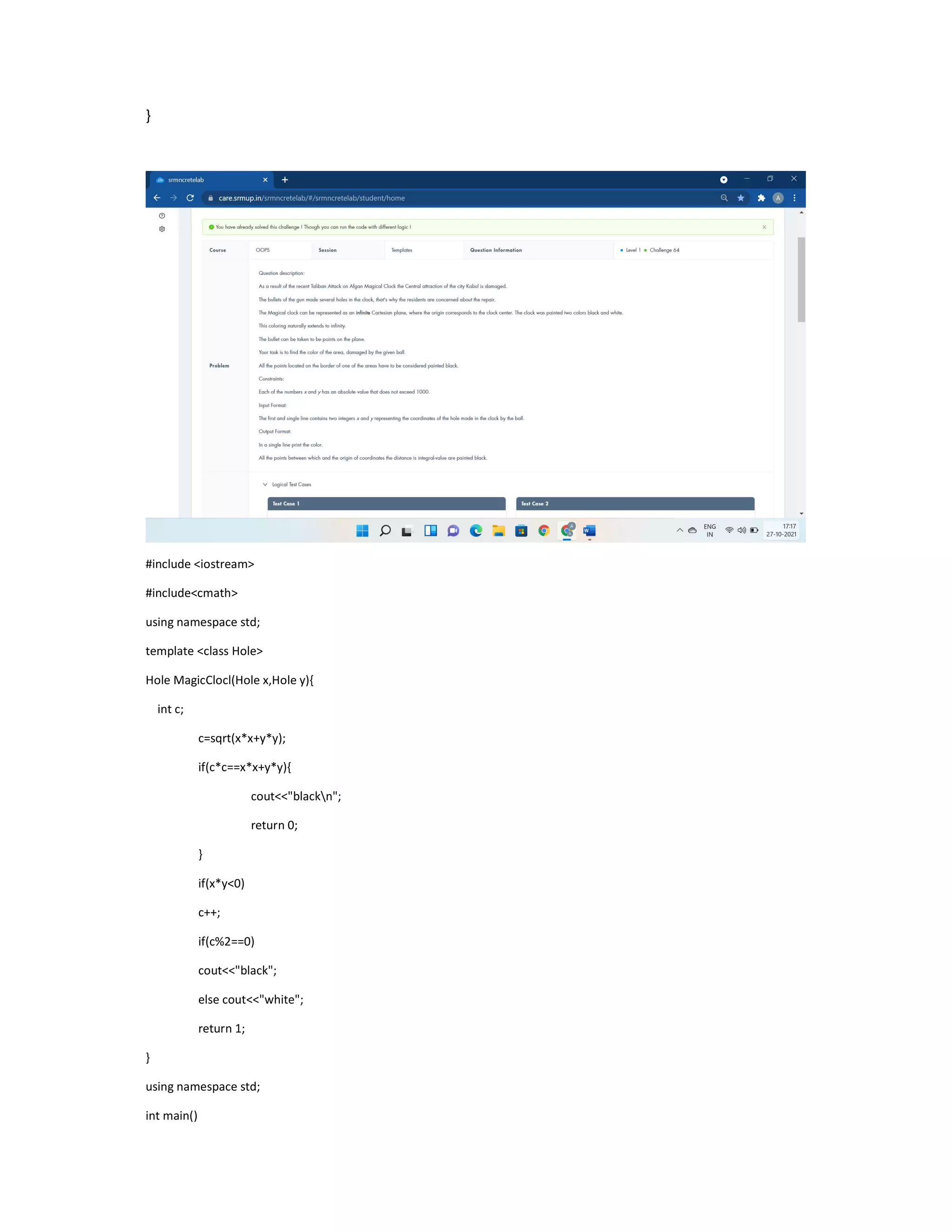
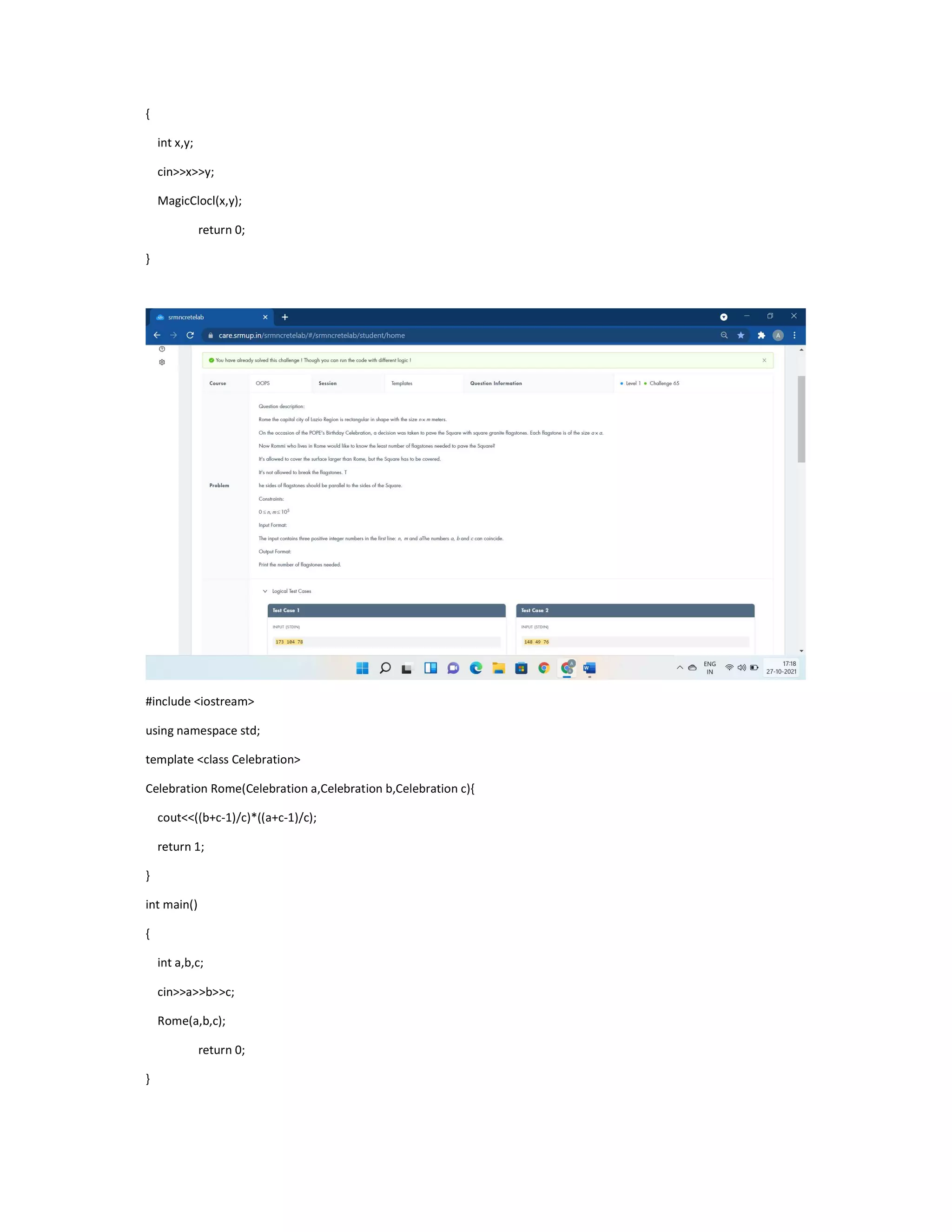
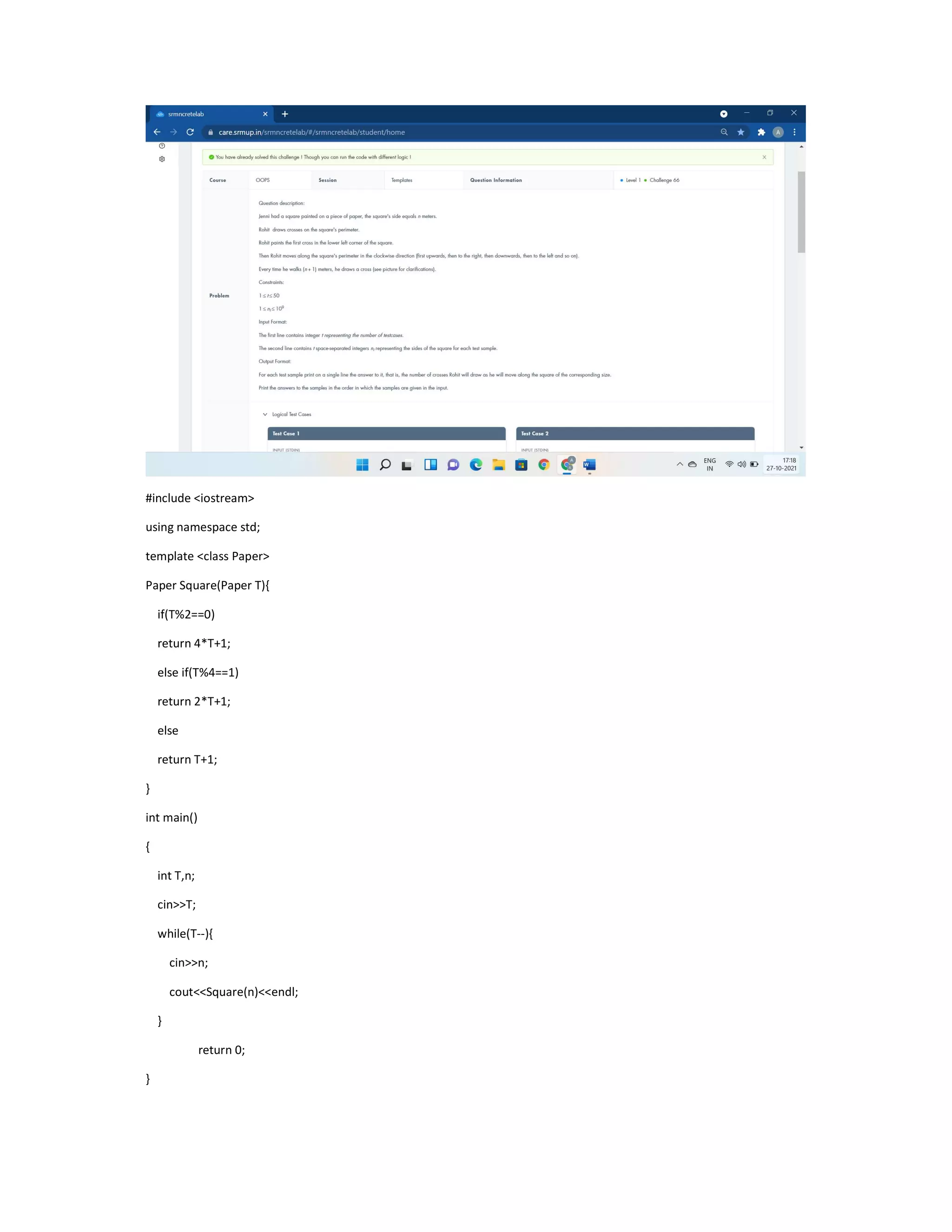
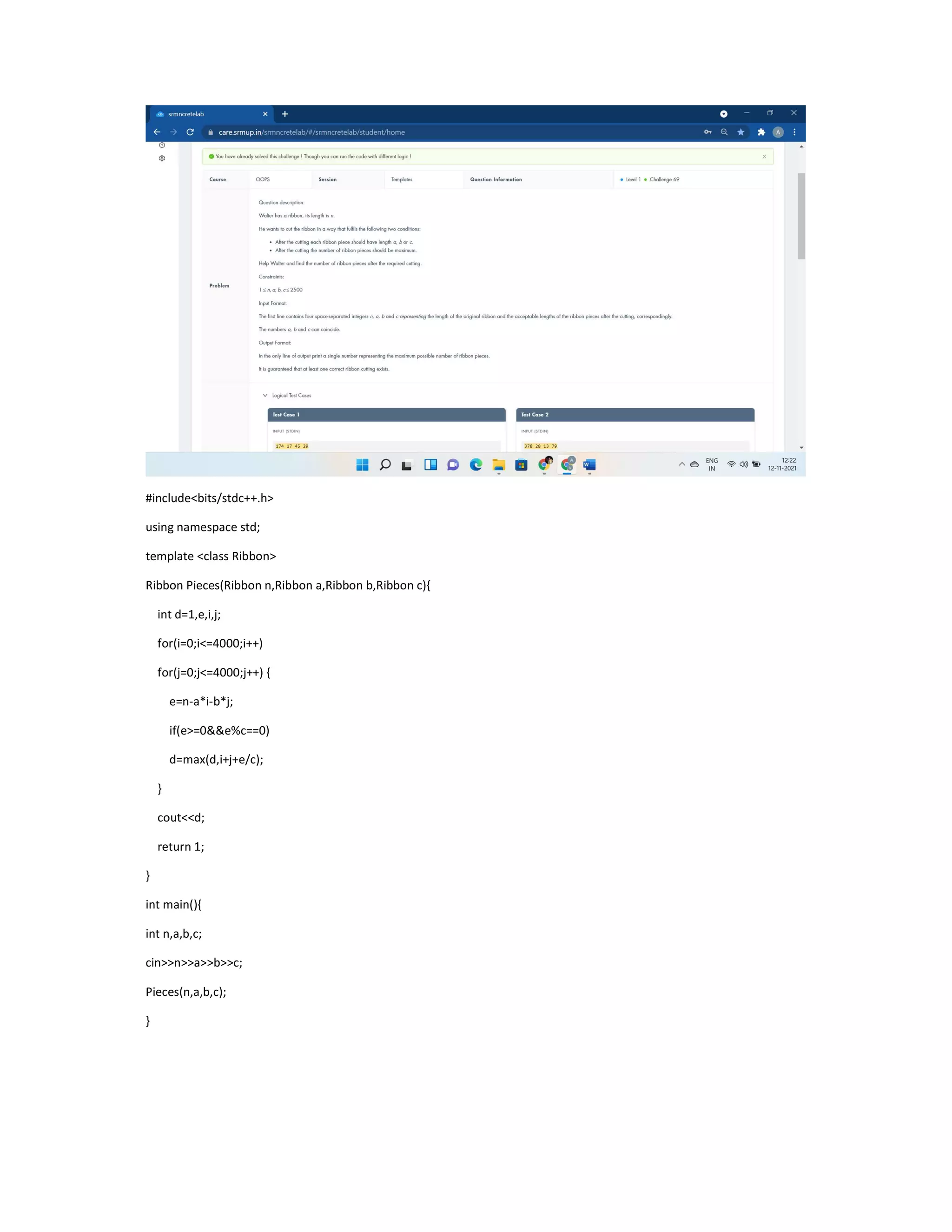
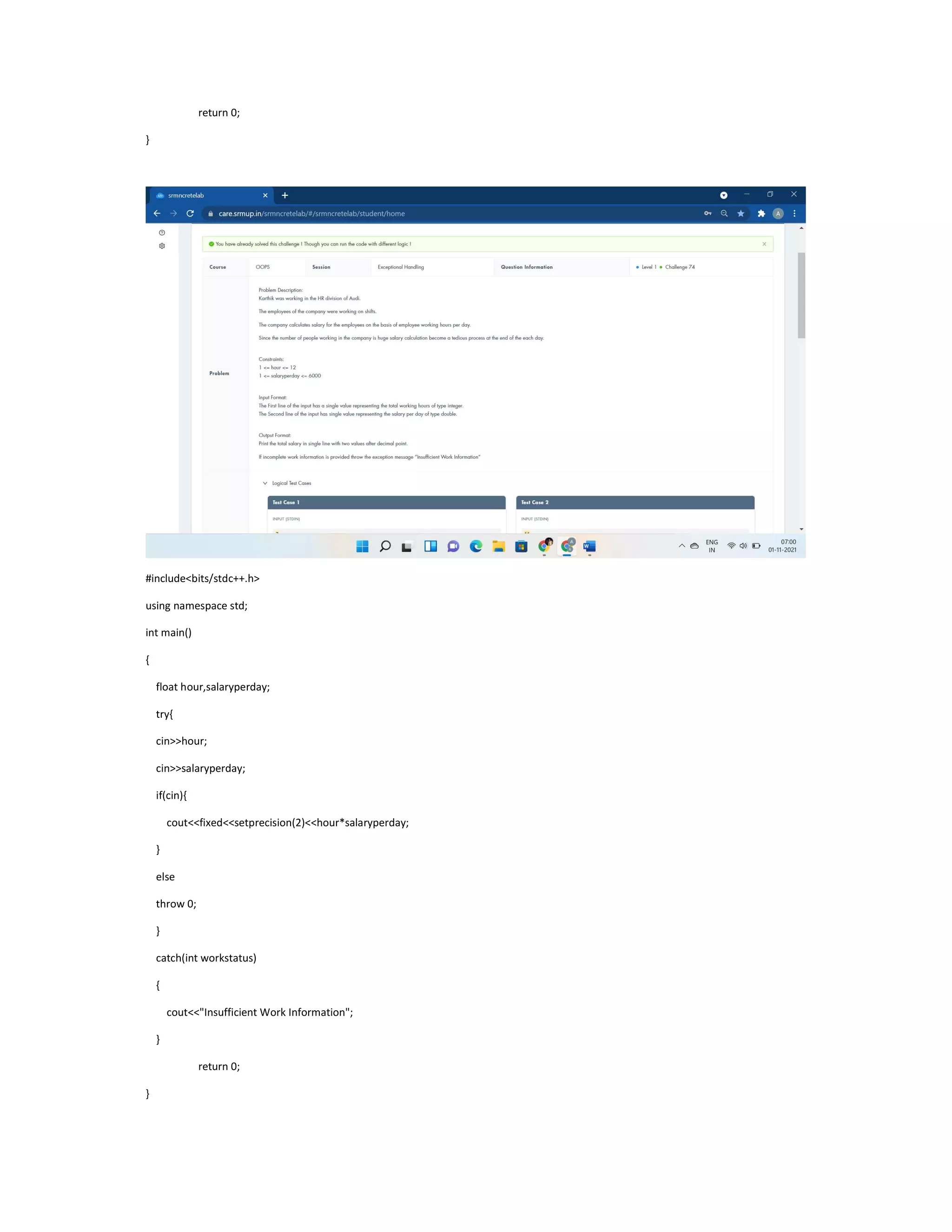
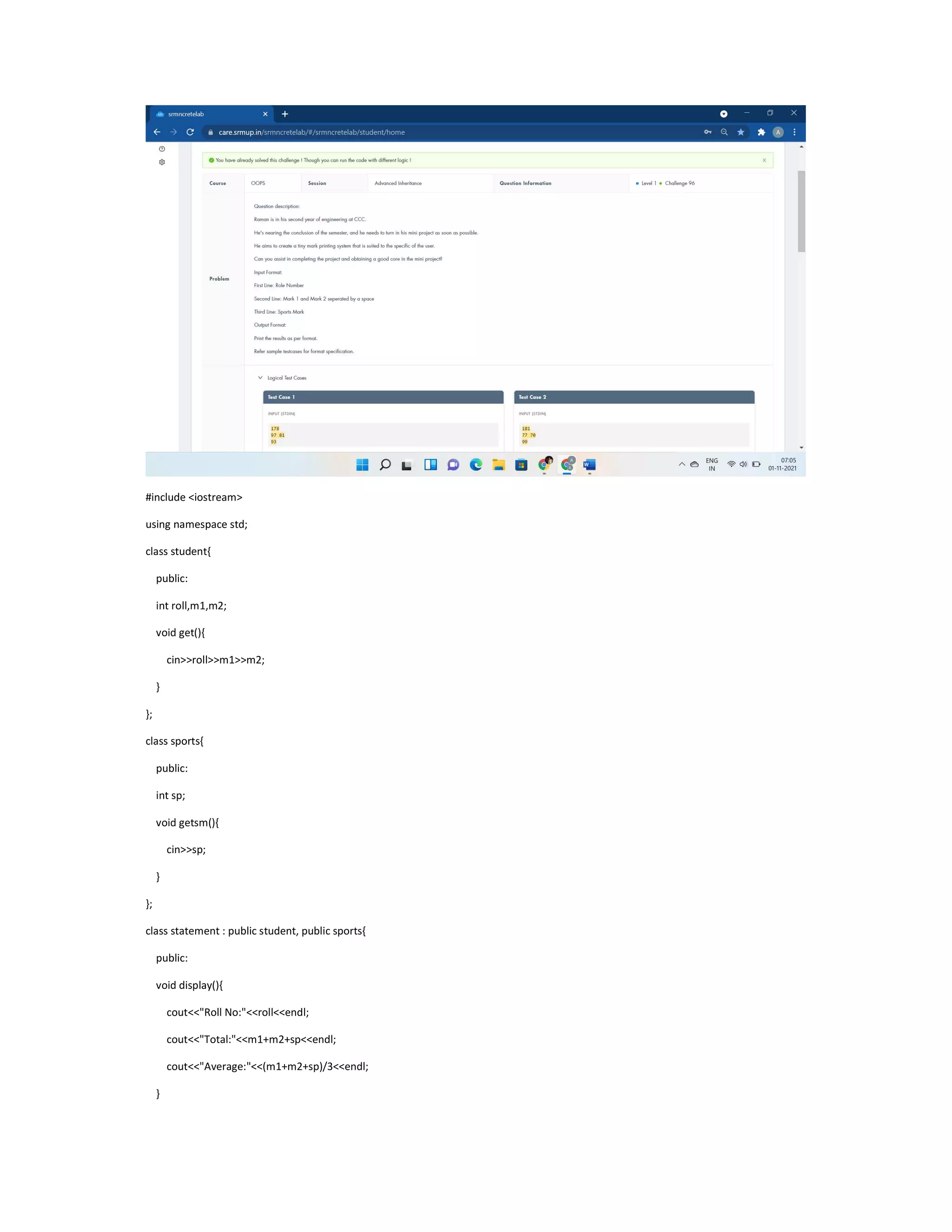
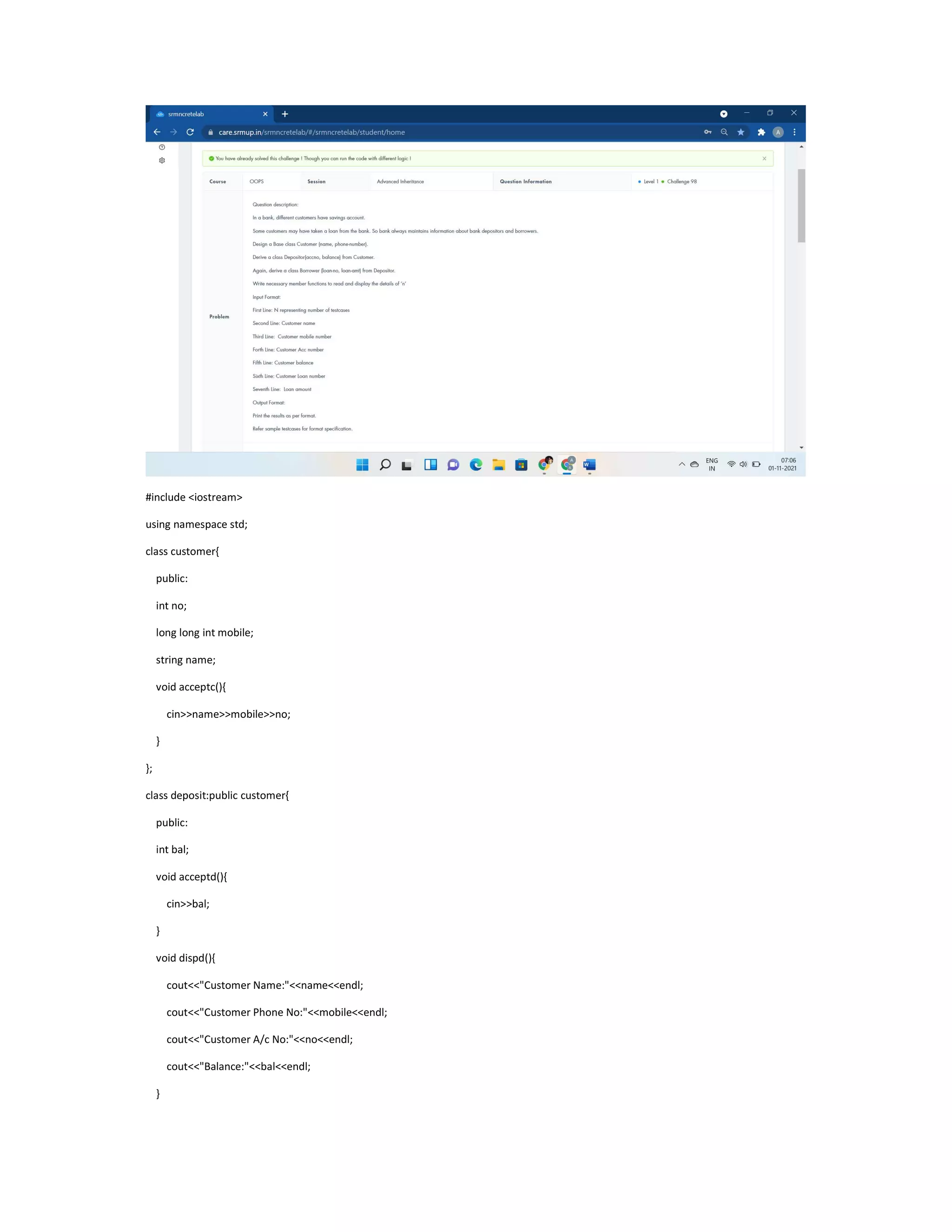
The document contains C++ code examples demonstrating various concepts in C++ including input/output, conditional statements, loops, functions, classes, constructors, operator overloading, and more. There are multiple short programs presented one after another without additional context or explanation.









![#include <iostream>
#include <string.h>
#include <stdio.h>
using namespace std;
double a[18][18], b[1 << 18];
int fun(int x) {
int s = 0;
while (x)
{
s += x & 1;
x >>= 1;
}
return s;
}
int main() {
if(0)
cout<<"class Lake public:void survival() fish.survival();";
int n, i, r, t, j;
cin >> n;
for (i = 0; i < n; i++)
for (j = 0; j < n; j++)
scanf("%lf", &a[i][j]);
memset(b, 0, sizeof(b));
b[(1 << n) - 1] = 1;
for (i = (1 << n) - 1; i >= 0; i--) {
int c = fun(i);
c = c * (c - 1) / 2;
for (r = 0; r < n; r++)
if (i & (1 << r))
for (t = 0; t < n; t++)](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-14-2048.jpg)
![if (i & (1 << t))
b[i - (1 << t)] += b[i] * a[r][t] / c;
}
for (r = 0; r < n - 1; r++)
printf("%.6lf ", b[1 << r]);
printf("%.6lfn", b[1 << r]);
}
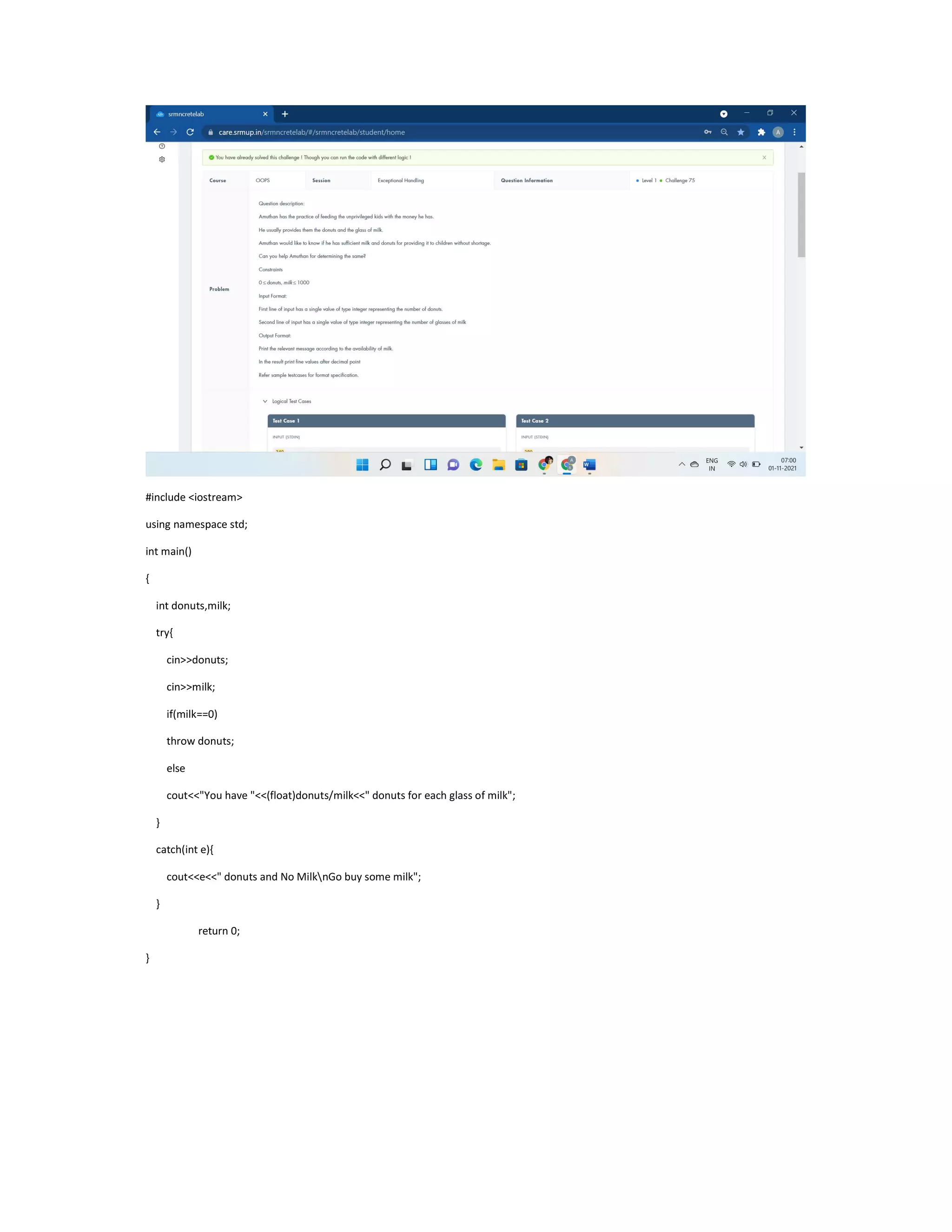
#include <iostream>
#include<cstring>
#include<string>
using namespace std;
class aadhaar
{
public:
void NameofCitizen(string fn,string mn,string ln)
{](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-15-2048.jpg)

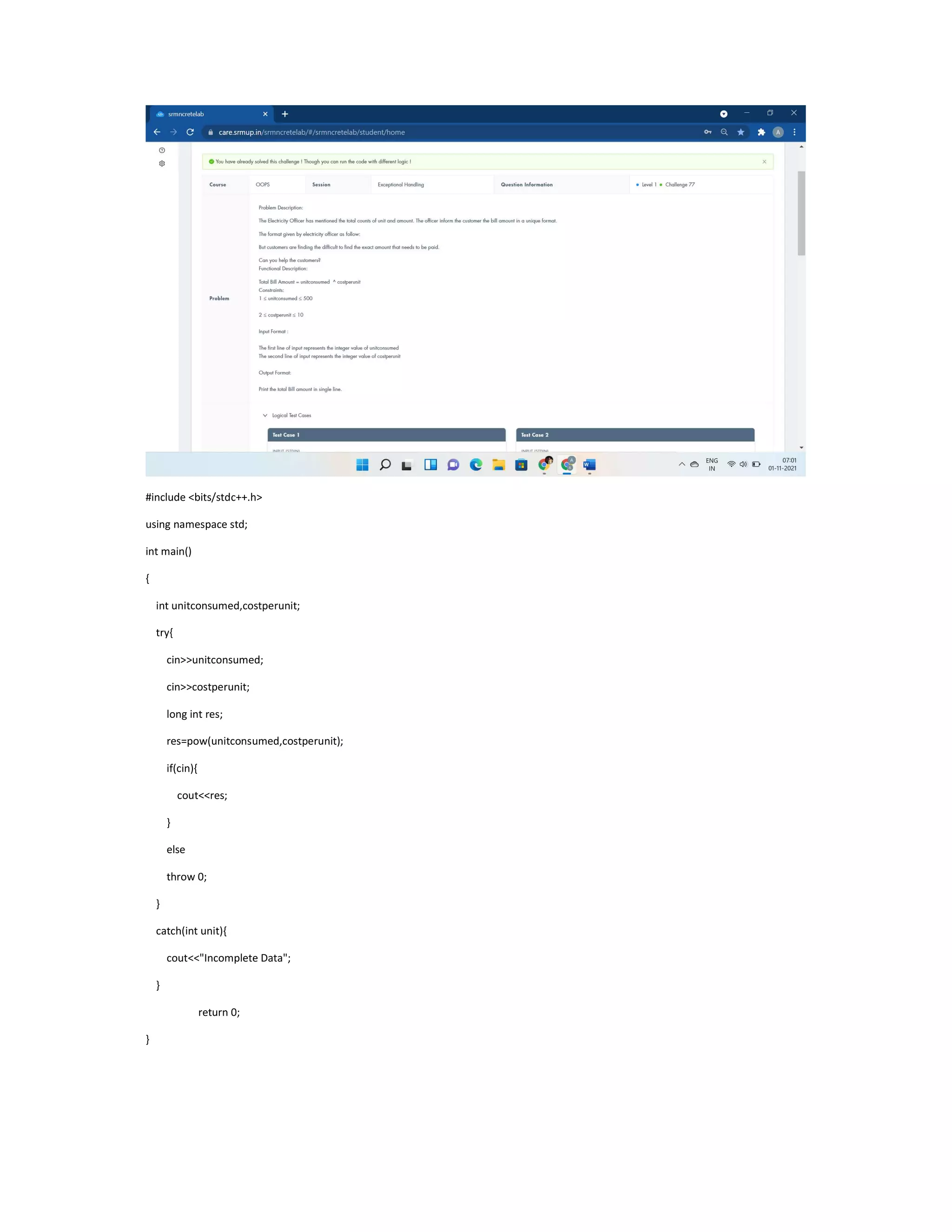
![#include <iostream>
using namespace std;
class TollBooth
{
public:
int cars;
float tollcollected;
TollBooth(){
cars=0;
tollcollected=0;
}
void payingcar(double pay){
cars++;
tollcollected+=pay;
}
void nonpayingcar(){
cars++;
}
void display(){
cout<<cars<<endl<<tollcollected<<endl;
}
};
int main()
{
TollBooth obj;
char VehicleNo[10];
float TollAmt;
int carpassed,i;
cin>>carpassed;
for(i=0;i<carpassed;i++)
{](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-17-2048.jpg)


![using namespace std;
class Friends
{
public:void Gifts(){
int i, n, a, b[50] = { 0 };
cin >> n;
for (i = 1; i < n+1; i++)
{
cin >> a;
b[a] = i;
}
for (i = 1; i < n+1; i++)
cout<< b[i]<<" ";
}
};
int main()
{
Friends Sharing;
Sharing.Gifts();
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-20-2048.jpg)


![#include <iostream>
using namespace std;
class ITEM
{
public:
int n;
float large=0,summ=0;
float arr[100],code[100];
void getdata(int b){
n=b;
for(int i=0;i<n;i++)
cin>>code[i]>>arr[i];
}
void largest(){
for(int i=0;i<n;i++)
{](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-23-2048.jpg)
![if(arr[i]>=large)
large=arr[i];
}
}
void sum(){
for(int i=0;i<n;i++)
summ+=arr[i];
}
void displayitems(){
cout<<"Largest Price="<<large<<endl;
cout<<"Sum of Prices="<<summ<<endl;
cout<<"Code and Price"<<endl;
for(int i=0;i<n;i++)
cout<<code[i]<<" and "<<arr[i]<<endl;
}
};
using namespace std;
int main()
{
ITEM order;
int b;
cin>>b;
order.getdata(b);
order.largest();
order.sum();
order.displayitems();
return 0;
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-24-2048.jpg)



![#include<bits/stdc++.h>
using namespace std;
int i,n,a,mx=INT_MIN,c[1000];
int res(int n);
int dis(int n,int mx);
int main(){
cin>>n;
mx=res(n);
cout<<dis(n,mx);
return 0;
cout<<"int* GazalCoin(int arr[],int n) int* GazalCoin(int arr[],int n,int i) GazalCoin(arr,n,0);";
}
int res(int n){
for(i=0;i<n;i++){
cin>>a;
c[a]++;
mx=max(mx,c[a]);
}
return mx;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-29-2048.jpg)

![class solve{
public:
void get(){
std::cin>>a>>b>>c;
n=2*abs(a-b);
}
void get2(){
if(c>n||max(a,b)>n)
cout<<"-1"<<endl;
else if(c>n/2)
cout<<c-n/2<<endl;
else
cout<<c+n/2<<endl;
}
};
int main(){
cin>>T;
solve p;
f(i,0,T){
p.get();
p.get2();
}
return 0;
cout<<"void pline(int v[],int n) void pline(int v) else if(x>n||x<=0)";
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-32-2048.jpg)


![}
int power(int x,int p){
int a[2*x];
for(int i=0;i<2*x;i++){
cin>>a[i];
if(a[i]%2==1)
p++;
}
return p;
}
int power(int x,int y,int p){
if(x==y)
cout<<"Yes"<<endl;
else
cout<<"No"<<endl;
return 1;
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-35-2048.jpg)

![#include <iostream>
using namespace std;
class Country{
public:
Country(){cout<<"Country:INDIA"<<endl;}
Country(char statename[100],int area,int density)
{
cout<<"State:"<<statename<<endl<<"Area:"<<area<<endl<<"Density:"<<density<<endl;
}
};
int main()
{
Country country;
char statename[100];
int area,density;
cin>>statename>>area>>density;
Country statesofindia(statename,area,density);
return 0;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-37-2048.jpg)





















![using namespace std;
class Gift {
public:virtual void Cubes()=0;
};
class Birthday:public Gift{
public:
int a[10],n;
void Cubes(){
cin>>n;
for(int i=0;i<n;i++)
cin>>a[i];
for(int i=0;i<n/2;i+=2)
/*int temp=a[i];
a[i]=a[n-i-1];
a[n-i-1]=temp;*/
swap(a[i],a[n-i-1]);
for(int i=0;i<n;i++)
cout<<a[i]<<" ";
}
};
int main()
{
Birthday obj;
obj.Cubes();
return 0;
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-77-2048.jpg)
![#include <iostream>
#include<string>
using namespace std;
class Decode{
public:virtual void Convert()=0;
};
class Word:public Decode{
public:
string s1,s2;
int n;
void Convert(){
cin>>n>>s1;
for(int i=0;i<n;i++){
if((n-i)%2==1)
s2=s2+s1[i];
else
s2=s1[i]+s2;
}
cout<<s2;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-78-2048.jpg)

![public:
char a[20];
int b,c;
char d[20];
int e,f;
void getdata(){
cin>>a>>b>>c>>d>>e>>f;
}
void display()
{
cout<<"Country:"<<a<<endl<<"Country's Polio %:"<<b<<endl;
cout<<"Country Literacy %:"<<c<<endl<<"Interdependency Rate:"<<(float)b/c<<endl;
cout<<"State Name:"<<d<<endl<<"% of Polio of State:"<<e<<endl;
cout<<"% of Literacy of State:"<<f<<endl<<"Interdependency Rate:"<<(float)e/f;
}
};
int main() {
if(0)
cout<<"country::getdata();";
country *o1;
state o2;
o1=&o2;
o1->getdata();
o2.display();
return 0;
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-80-2048.jpg)




![#include <iostream>
using namespace std;
int main()
{
string str1,str2;
try{
cin>>str1>>str2;
int count, n=str1.size();
if(cin){
for(int i=0;i<n;i++){
if((str1[i]>=48 && str1[i]<=57) || (str2[i]>=48&&str2[i]<=57) )
throw 0;
if(str1[i]==str2[i])
count++;
}
if(count!=n)
cout<<str1<<" is not "<<str2;
else
cout<<str1<<" is "<<str2;
}
}
catch (int i){
cout<<"Inappropriate Input";](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-92-2048.jpg)




![#include<bits/stdc++.h>
#define f(i,a,n) for(i=a;i<n;i++)
using namespace std;
int main(){
int t,i,j;
cin>>t;
string str;
f(j,0,t){
f(i,0,2){
try{
cin>>str[i];
if(isalpha(str[i]))
cout<<str[i]<<" is alphabetic"<<endl;
else
throw str[i];
}
catch (char f){
cout<<f<<" is not alphabetic"<<endl;
}
}
}
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-100-2048.jpg)

![STL:-
#include <algorithm>
#include <iostream>
#include <vector>
using namespace std;
int main() {
int N, a, b;
while (cin>>N) {
vector<pair<int,pair<int,int>>>StorageDrives;
for (int i = 0; i < N; i++) {
cin>>a>>b;
StorageDrives.push_back(make_pair((b>a) ? a : 2000000001-b, make_pair(a, b)));
}
long long ret = 0, cap = 0;
sort(StorageDrives.begin(),StorageDrives.end());
int z=StorageDrives.size();
for (int i = 0; i < z; i++) {
if (cap < StorageDrives[i].second.first) {](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-102-2048.jpg)
![ret += StorageDrives[i].second.first - cap;
cap = StorageDrives[i].second.first;
}
cap += StorageDrives[i].second.second - StorageDrives[i].second.first;
}
cout << ret << endl;
}
}
#include<bits/stdc++.h>
using namespace std;
int n,m,sx=99999,sy=99999,x,y;
char a[55][55];
int main(){
cin>>n>>m;
for(int i=1;i<=n;i++){
for(int j=1;j<=m;j++){
cin>>a[i][j];
if(a[i][j]=='*'){
x=max(x,i),y=max(y,j),sx=min(sx,i),sy=min(sy,j);
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-103-2048.jpg)
![}
}
for(int i=sx;i<=x;i++){
for(int j=sy;j<=y;j++) cout<<a[i][j];
cout<<endl;
}
return 0;
cout<<"vector<vector<char>>drawing(n,vector<char>(m,'0')); drawing[row][col]";
}
#include <bits/stdc++.h>
using namespace std;
typedef long long LL;
const int N=55;
LL n, k, v, idx;
string name[N];
int main(){
LL t; cin>>t; while(t--){
cin>>n>>k>>v;
for(int i=0; i<n; i++)
cin>>name[i];
LL st=((v-1)*k)%n;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-104-2048.jpg)
![//cout<<"Case #"<<(++idx)<<":";
vector<int> ans;
for(int i=0; i<k; i++)
ans.push_back((st+i)%n);
sort(ans.begin(), ans.end());
for(int id: ans)
cout<<name[id]<<" ";
cout<<"n";
}
return 0;
cout<<"vector<string>visit(n); vector<pair<int,string>>seenattraction; sort(seenattraction.begin(),seenattraction.end());";
}
#include <bits/stdc++.h>
using namespace std;
int main()
{
int n;
cin>>n;
set<pair<string,string>>Descriptionofleaves;
string species,color;
while(n--){](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-105-2048.jpg)
![cin>>species>>color;
Descriptionofleaves.insert(make_pair(species,color));
}
cout<<Descriptionofleaves.size();
return 0;
}
#include <bits/stdc++.h>
using namespace std;
void sum(){}
int n,m;
vector <int> use[2020];
int cost[2020];
string g[1010];
int main()
{
cin>>n>>m;
for(int i=0;i<n;i++)
{
cin>>g[i];
for(int j=0;j<m;j++)
{](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-106-2048.jpg)
![if(g[i][j]=='#')
{
use[i].push_back(j+n);
use[j+n].push_back(i);
}
}
}
queue<int>BankChamber;
BankChamber.push(n-1);
cost[n-1]=1;
while(!BankChamber.empty())
{
int t=BankChamber.front();
BankChamber.pop();
int z=use[t].size();
for(int i=0;i<z;i++)
{
if(cost[use[t][i]]==0)
{
cost[use[t][i]]=cost[t]+1;
BankChamber.push(use[t][i]);
}
}
}
cout<<cost[0]-1<<endl;
sum();
return 0;
cout<<"BankChamber.push(n);";
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-107-2048.jpg)
![#include<bits/stdc++.h>
using namespace std;
typedef long long int ll;
ll a[100006],c[3];
int main()
{
ll n,m,i,j,k,l,sum=0;
cin>>n>>m;
for(i=0;i<m;i++)
{
sum=0;
for(j=0;j<3;j++)
{
cin>>c[j];
sum=sum+a[c[j]];
}
l=1;
for(k=0;k<3;k++)
{
if(l==sum)
l++;
if(a[c[k]]==0)](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-108-2048.jpg)
![{
a[c[k]]=l++;
}
}
}
for(i=1;i<=n;i++)
cout<<a[i]<<" ";
return 0;
cout<<"map<int,int>dance; set<int>dancer;";}
#include <bits/stdc++.h>
#define ll long long
using namespace std;
int main(){
int t;
cin >> t;
while (t--) {
int n, d;
cin >> n >> d;
map<ll, vector<pair<long,long>>>TGS;
for (int i = 0; i < n; i++){
ll day, lec, sad;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-109-2048.jpg)
![cin >> day >> lec >> sad;
TGS[day].push_back({sad, lec}); }
priority_queue<pair<long,long>>PQ;
for (int i = 1; i <= d; i++) {
for (auto x : TGS[i])
PQ.push(x);
if (!PQ.empty())
{
pair<ll, ll> p = PQ.top();
PQ.pop();
p.second--;
if (p.second == 0) {}
else
PQ.push({p.first, p.second});
}
}
ll cnt = 0;
while (!PQ.empty()) {
pair<ll, ll> p = PQ.top();
cnt += (p.first * p.second);
PQ.pop();
}
cout << cnt << endl;
}
return 0;
cout<<"vector<pair<long,long>>TGS PQ.top().first;PQ.top().second ";}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-110-2048.jpg)
![#include <bits/stdc++.h>
using namespace std;
long long ans=1e15;
deque<char>Operations(20);
void solve(vector<long long> a,int id){
if((int)a.size()==1){
ans=min(ans,a[0]);
return;
}
for(int i=0;i<(int)a.size();i++){
for(int j=0;j<i;j++){
vector<long long> b;
if(Operations[id]=='+') b.push_back(a[i]+a[j]);
else b.push_back(a[i]*a[j]);
for(int k=0;k<(int)a.size();k++){
if(k!=i && k!=j) b.push_back(a[k]);
}
solve(b,id+1);
}
}
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-111-2048.jpg)
![int main() {
vector<long long>numbers(4);
for(int i=0;i<4;i++) cin>>numbers[i];
for(int i=0;i<3;i++) cin>>Operations[i];
solve(numbers,0);
cout<<ans;
return 0;
}
#include <bits/stdc++.h>
using namespace std;
#define f(i,a,n) for(i=a;i<n;i++)
int i,j,n,x[110],d[110];
int main(){
cin>>n;
f(i,1,n+1) cin>>x[i]>>d[i];
f(i,1,n+1){
f(j,i+1,n+1){
if(x[i]+d[i]==x[j] && x[j]+d[j]==x[i]){
cout << "YESn";
return 0;
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-112-2048.jpg)
![}
}
cout << "NO";
return 0;
cout<<"map<long long,long long>palm; ";
}
#include<bits/stdc++.h>
using namespace std;
int i,n;
string s,t,u;
int D()
{
for(i=0;s[i];i++)if(s[i]^t[i])return 0;
return 1;
}
int main()
{
for(cin>>s>>n;n--;)
{
cin>>t;
if(D()&&(u.empty()||t<u))u=t;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-113-2048.jpg)
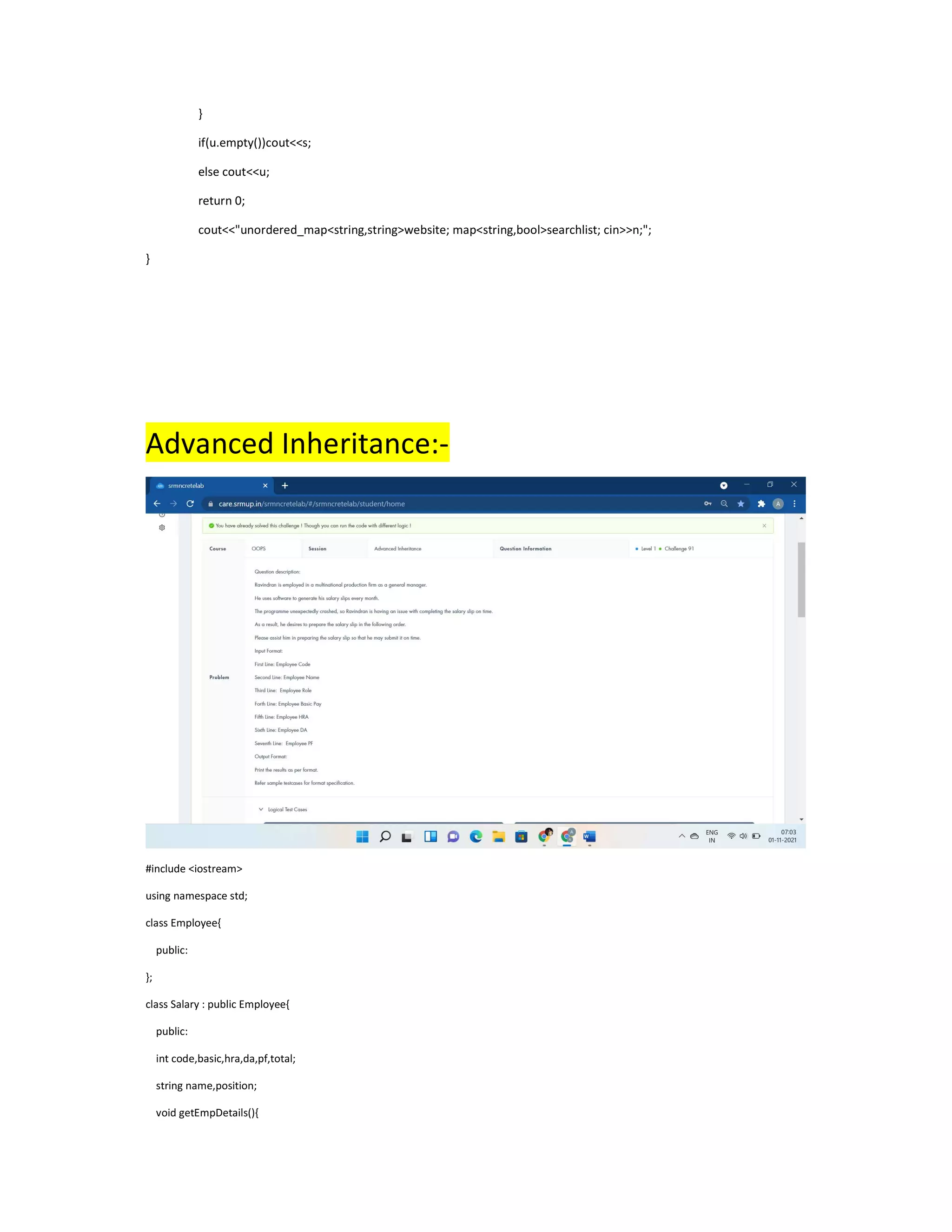


![cin>>n;
Instructor inst[n];
for(int i=0;i<n;i++){
inst[i].accept_instructor_details();
inst[i].display_instructor_details();
}
return 0;
cout<<"Instructor *inst;";
}
#include <iostream>
using namespace std;
class acc{
public:
int no;
void getacc(){
cin>>no;
}
};
class branch:public acc{
public:
string name;](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-117-2048.jpg)

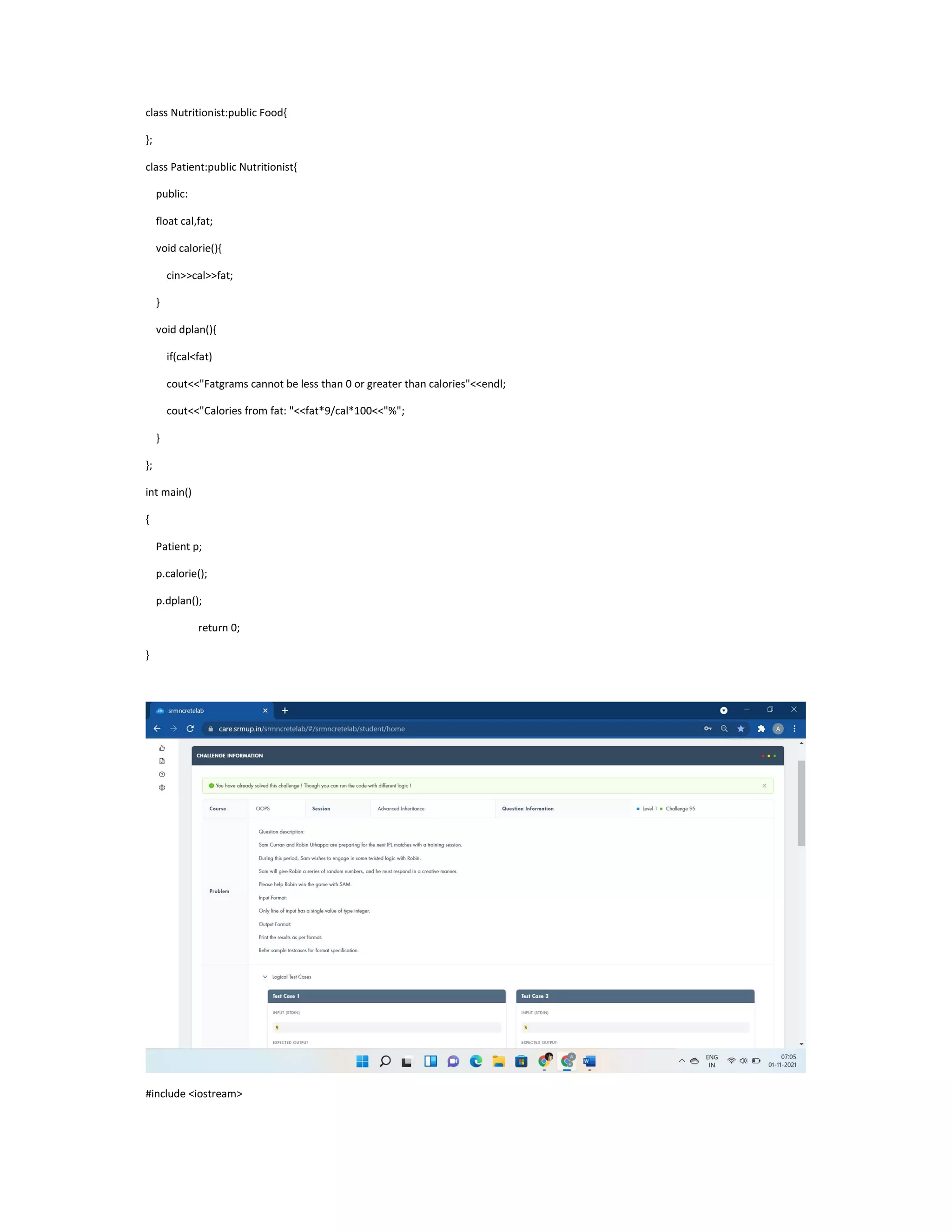



![};
class borrow:public deposit{
public:
long long int loan_no,amt;
void acceptb(){
cin>>loan_no>>amt;
}
void dispb(){
cout<<"Loan No:"<<loan_no<<endl;
cout<<"Loan Amount:"<<amt<<endl;
}
};
int main()
{
int n;
cin>>n;
borrow b1[n];
for(int i=0;i<n;i++){
b1[i].acceptc();
b1[i].acceptd();
b1[i].acceptb();
b1[i].dispd();
b1[i].dispb();
}
return 0;
}](https://image.slidesharecdn.com/oodpelab-230625060543-13c3f5a2/75/oodp-elab-pdf-125-2048.jpg)


