Embed presentation
Download to read offline
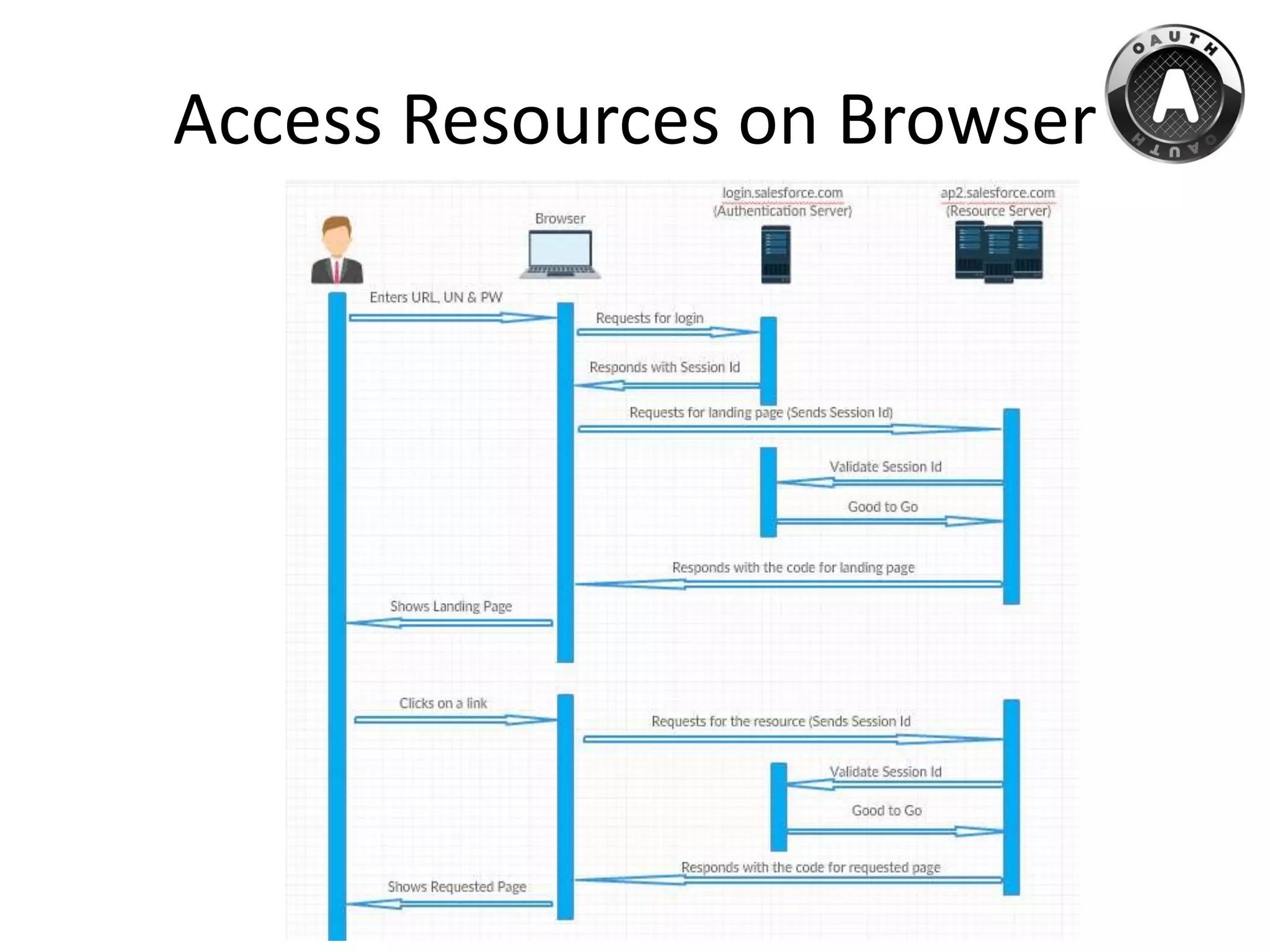
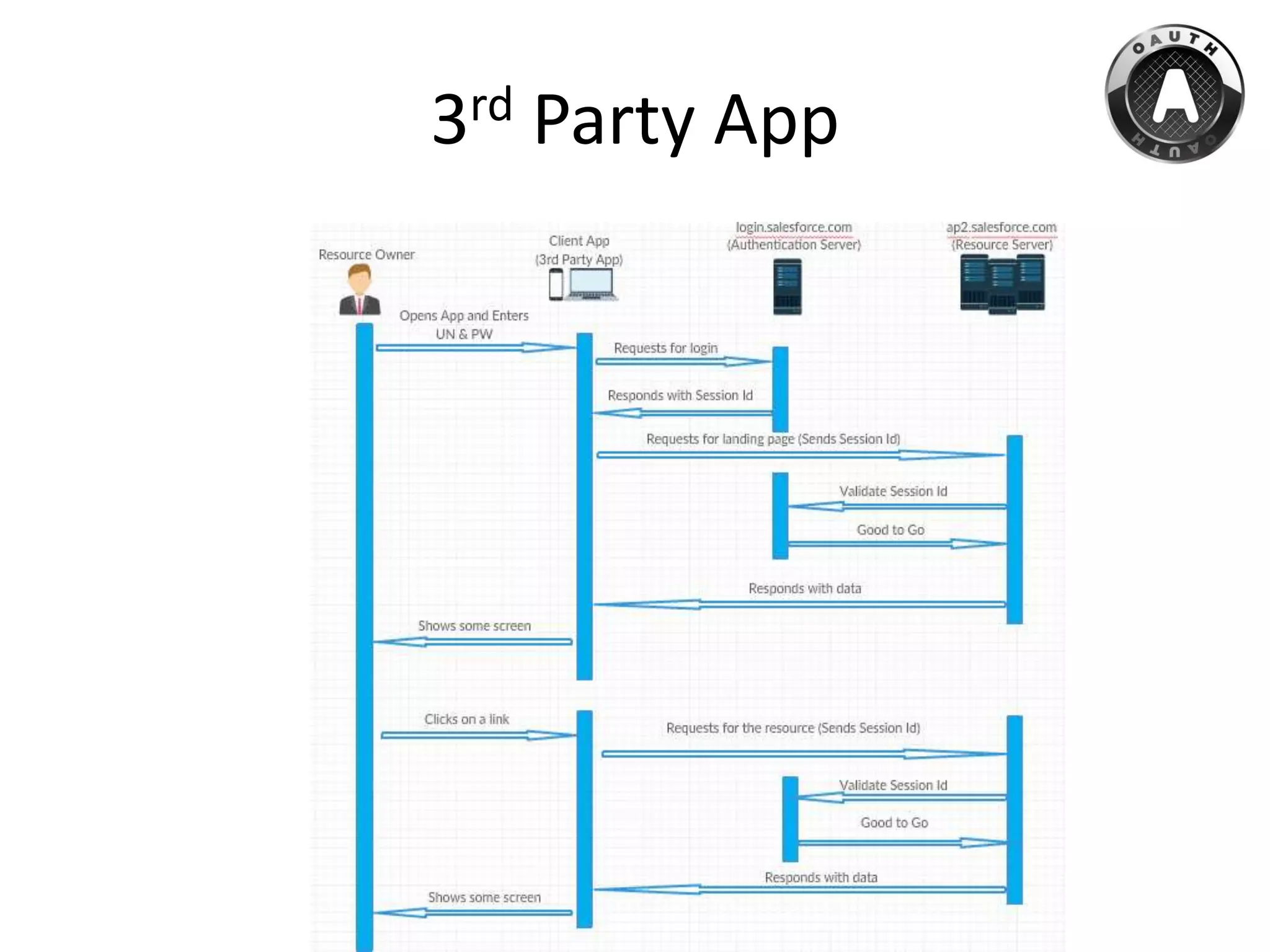
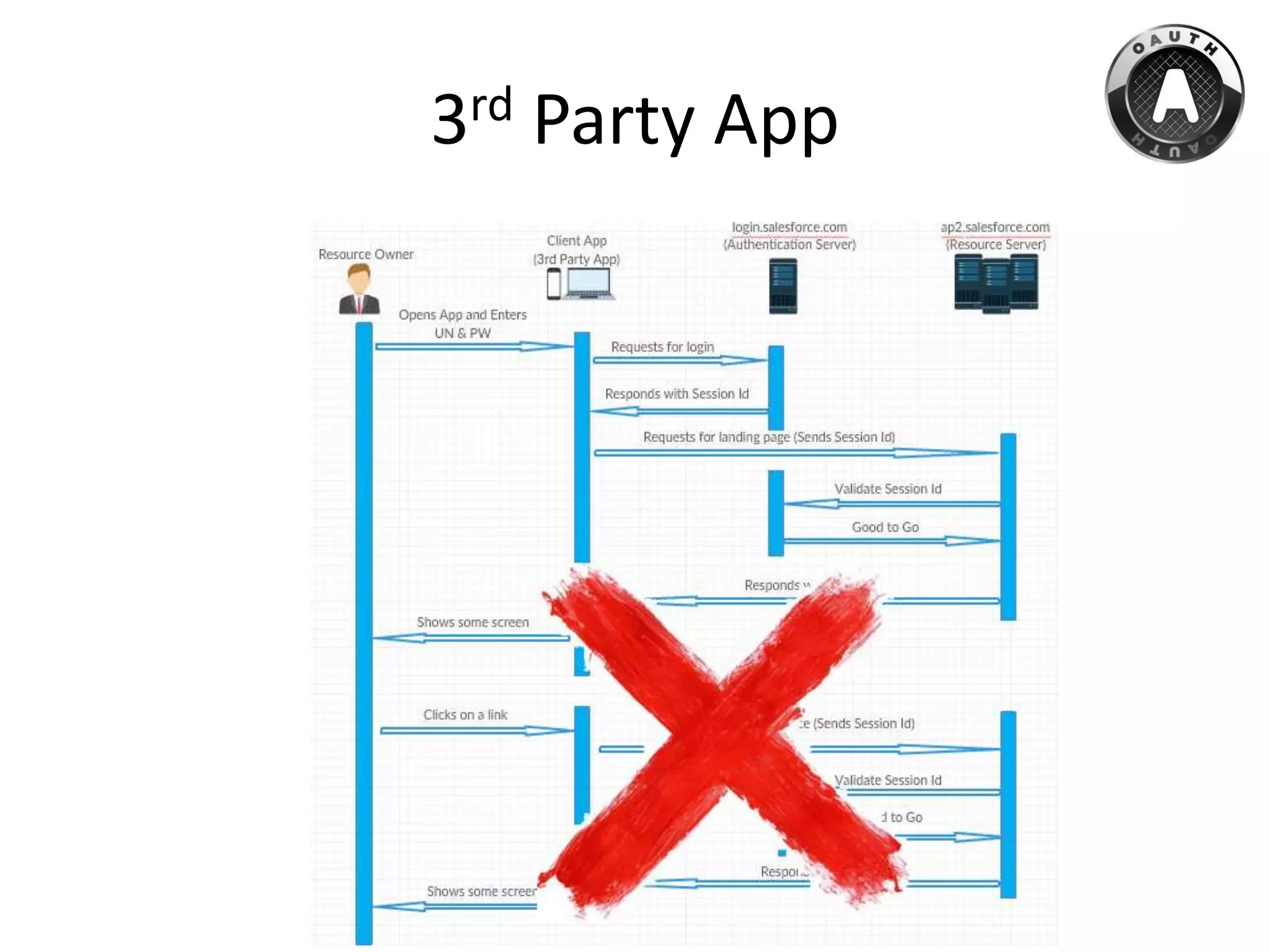
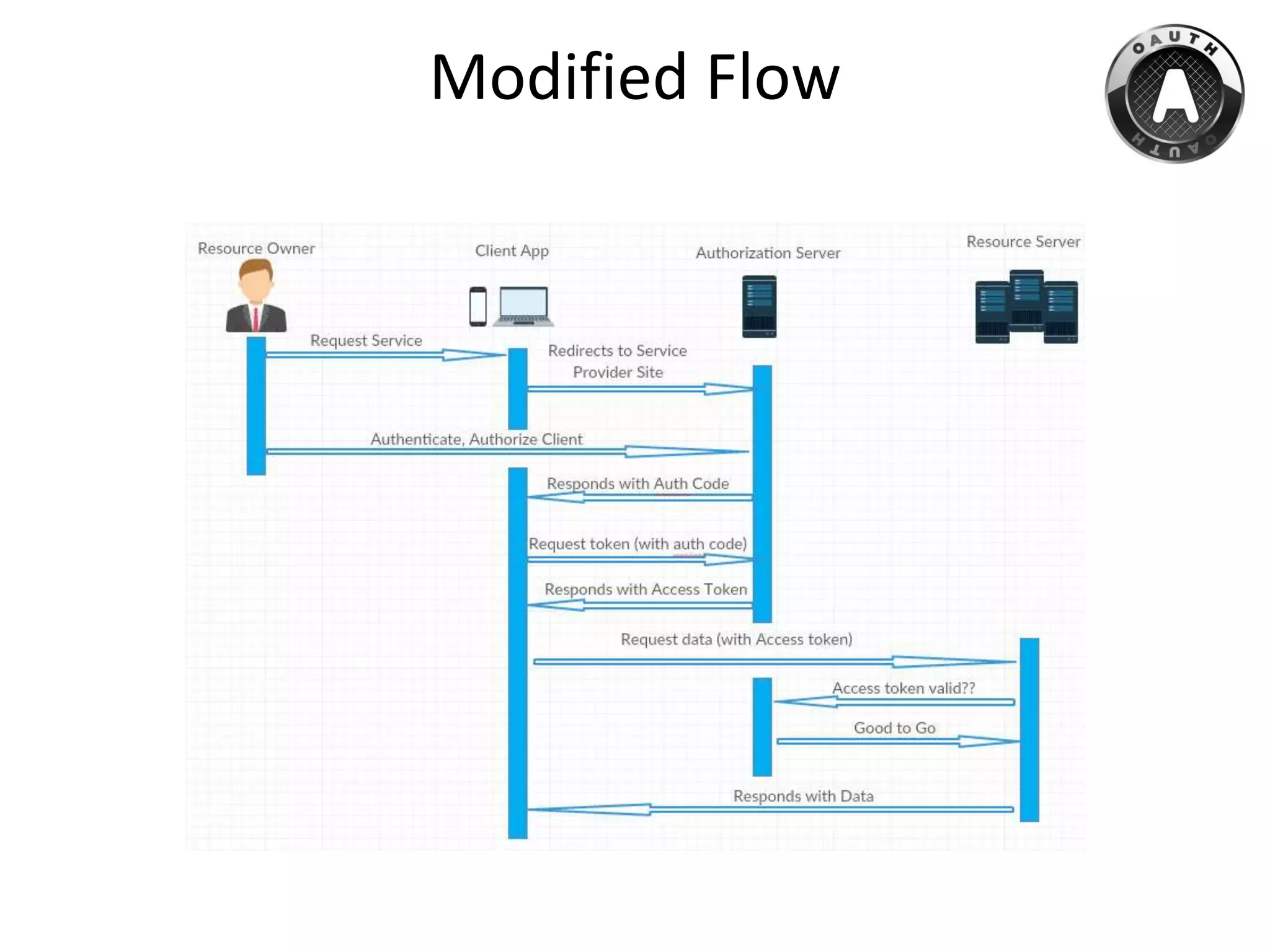


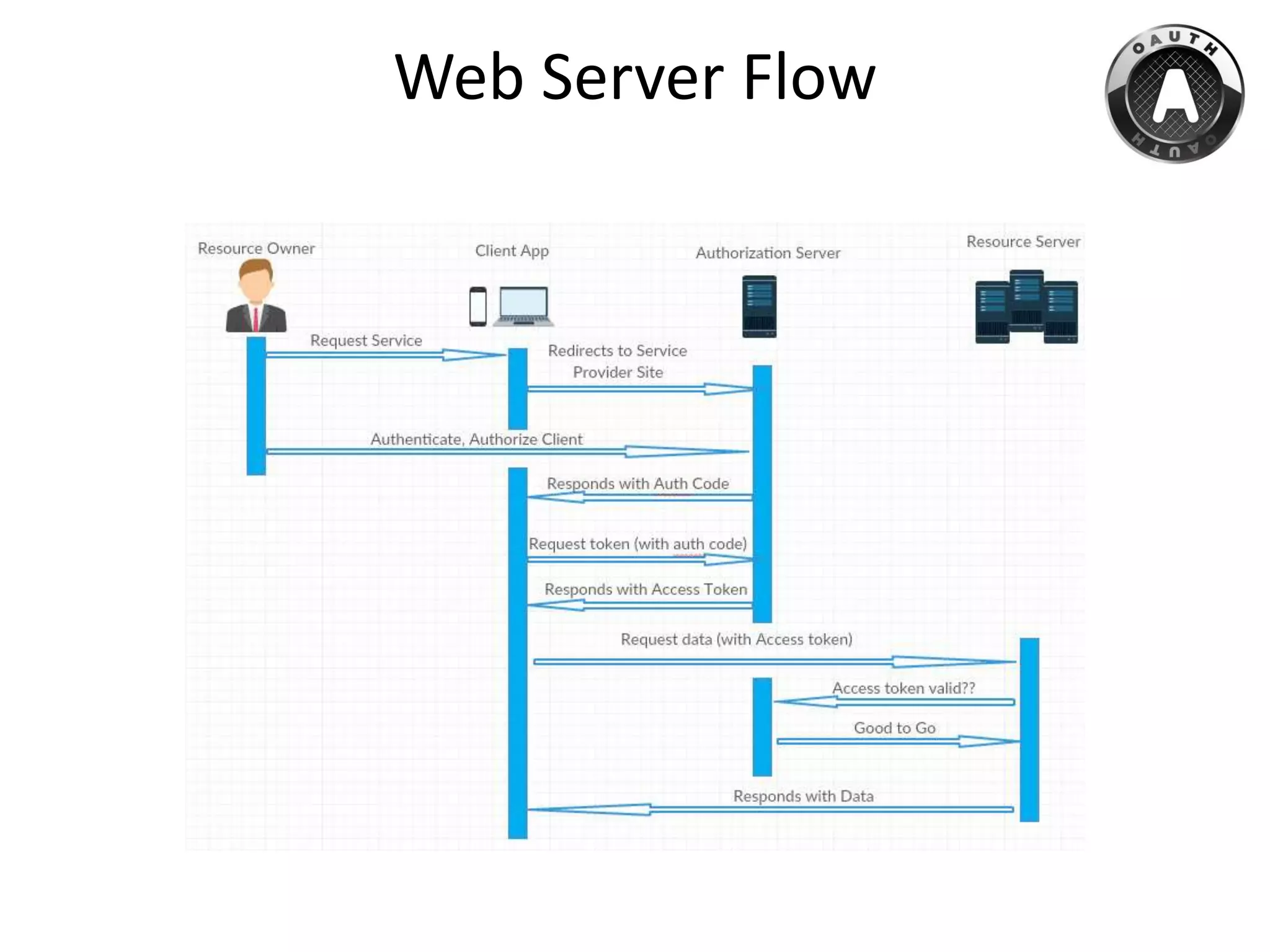
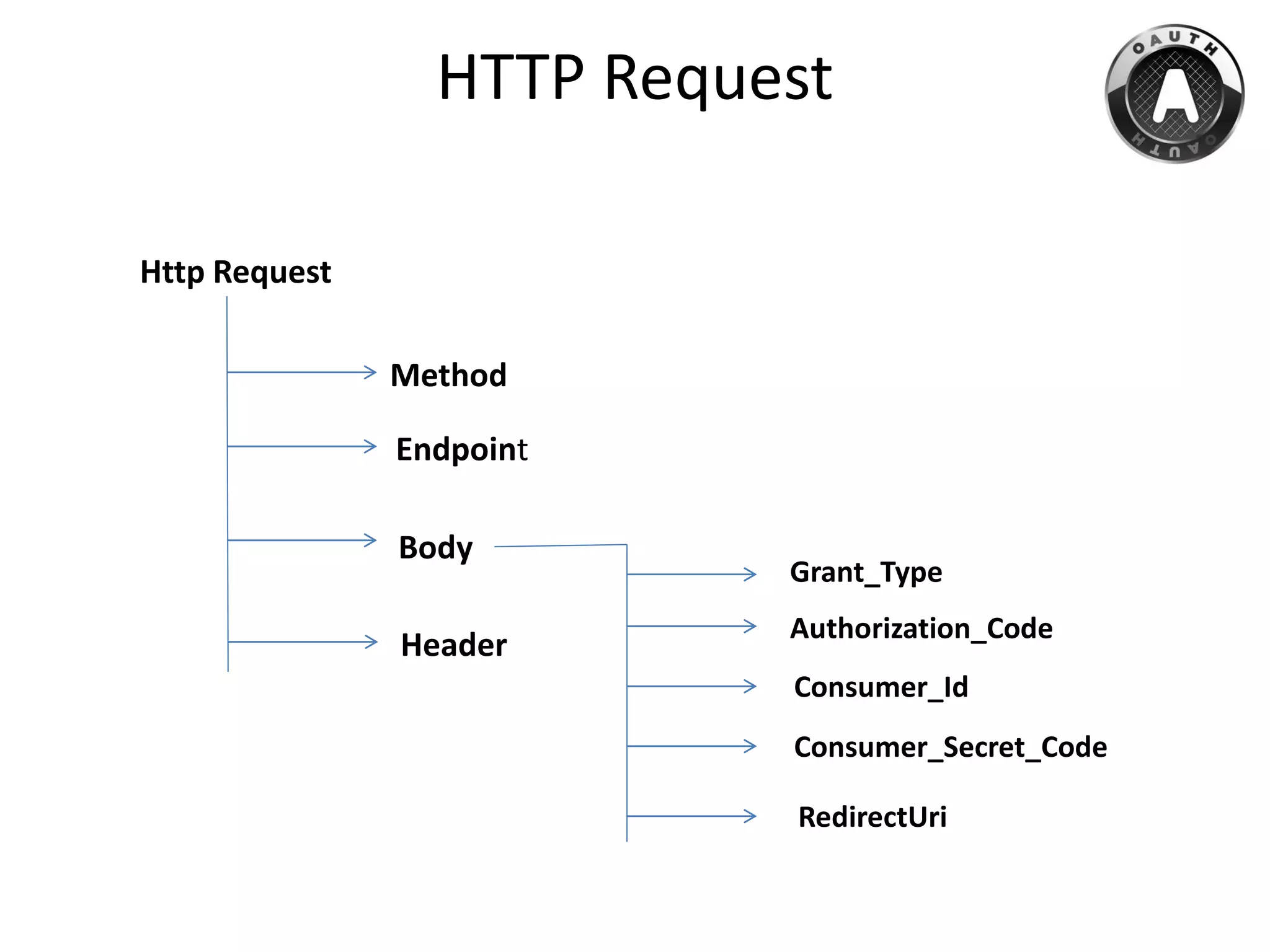
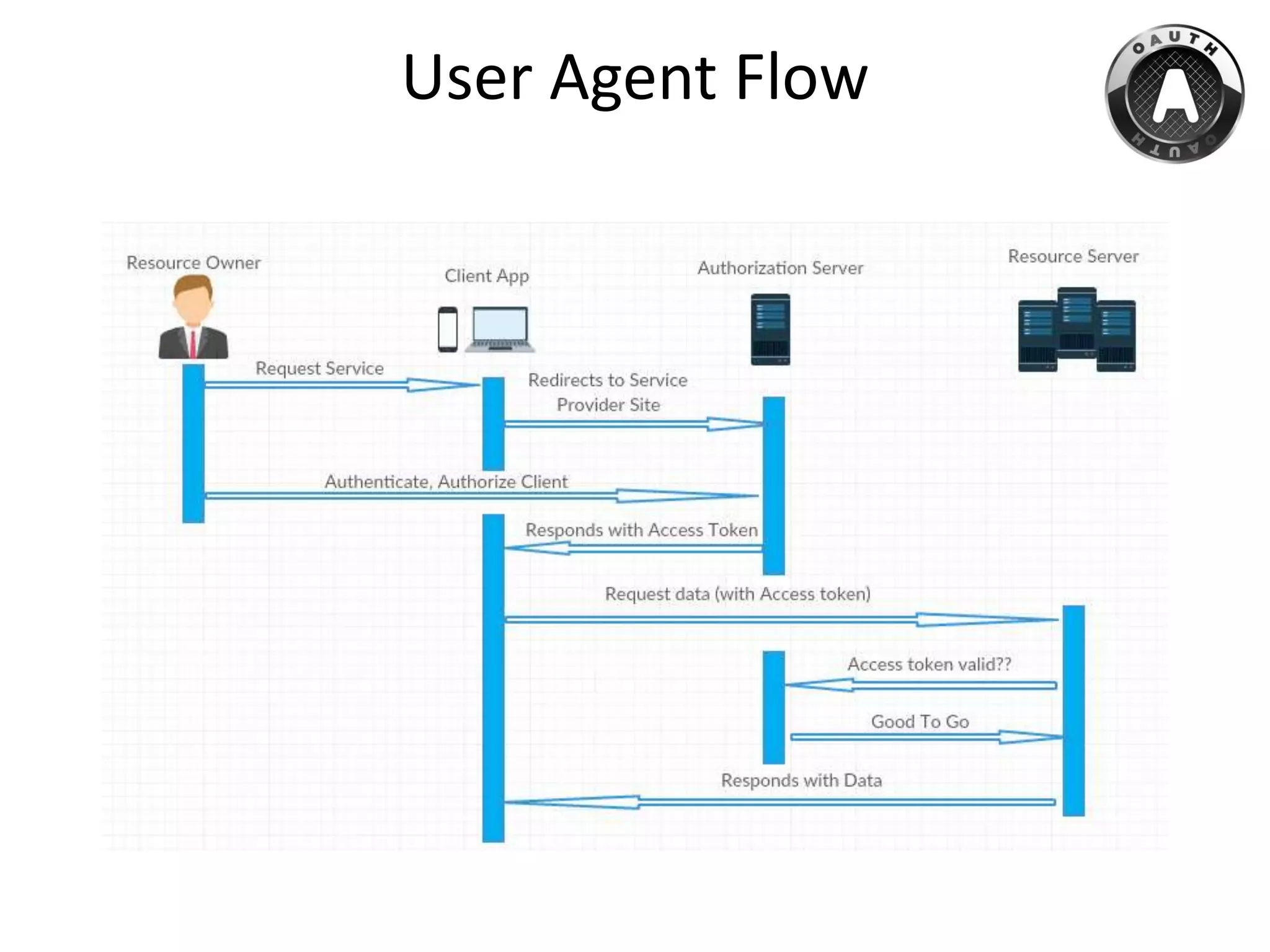
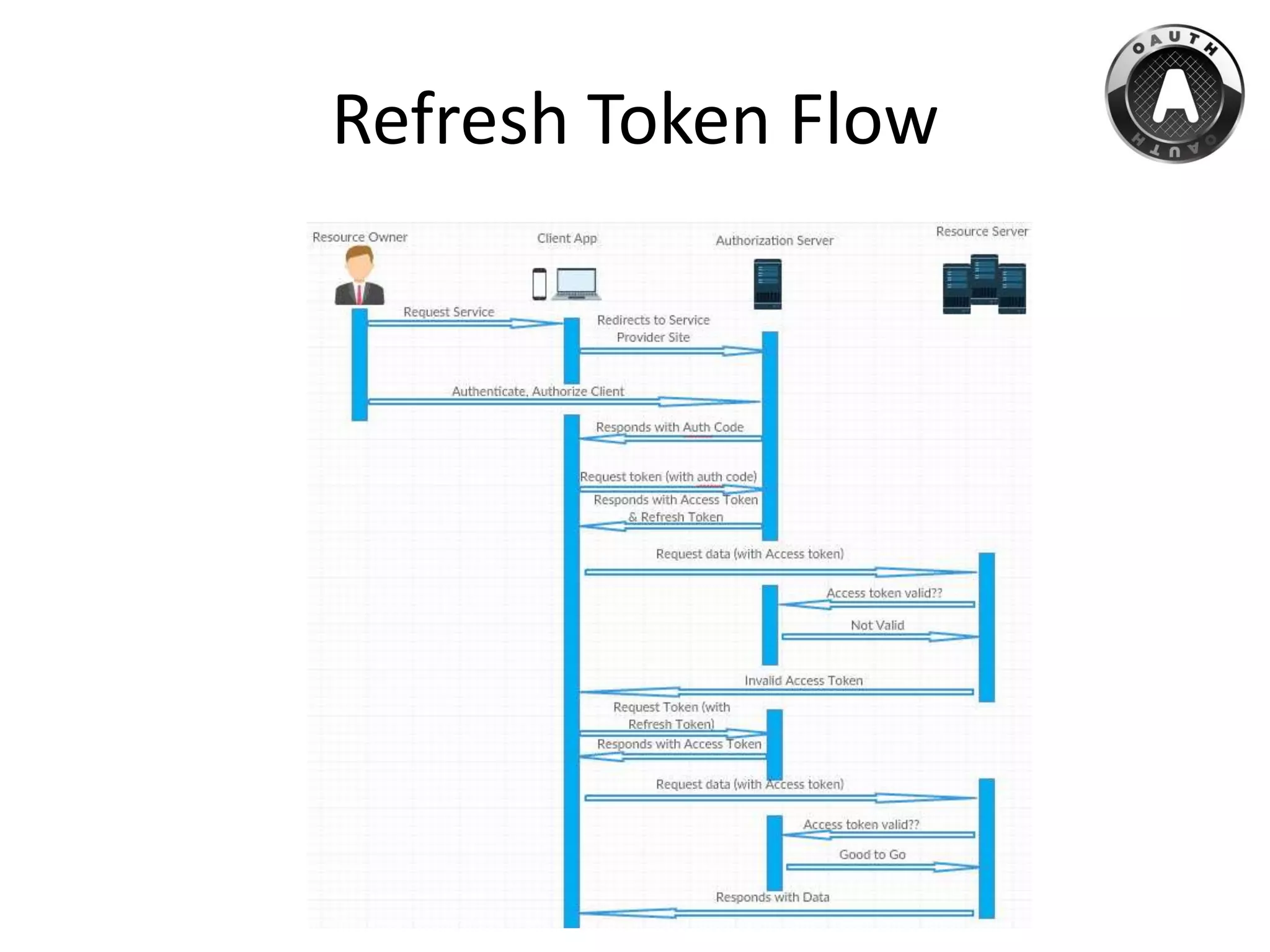
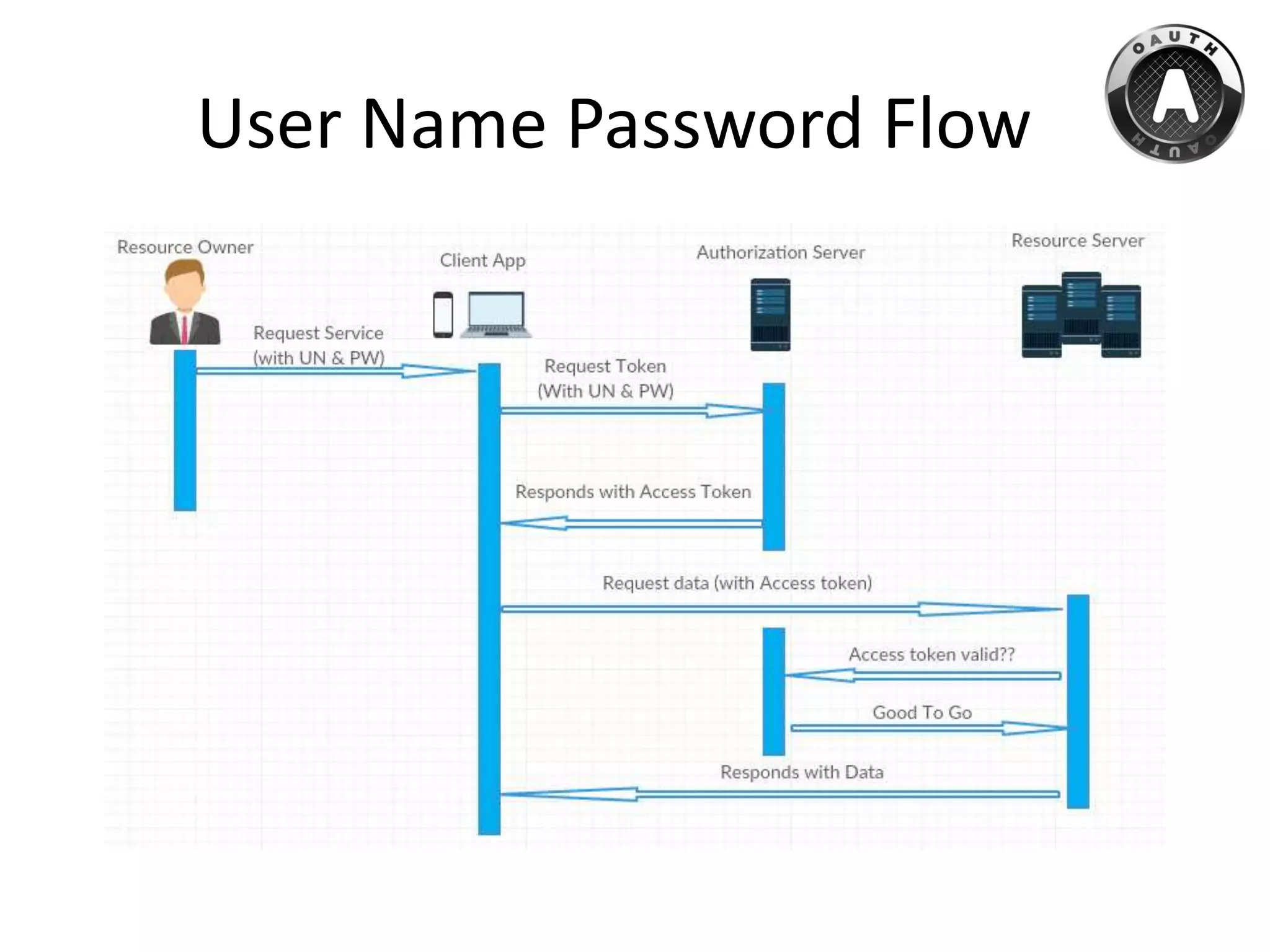

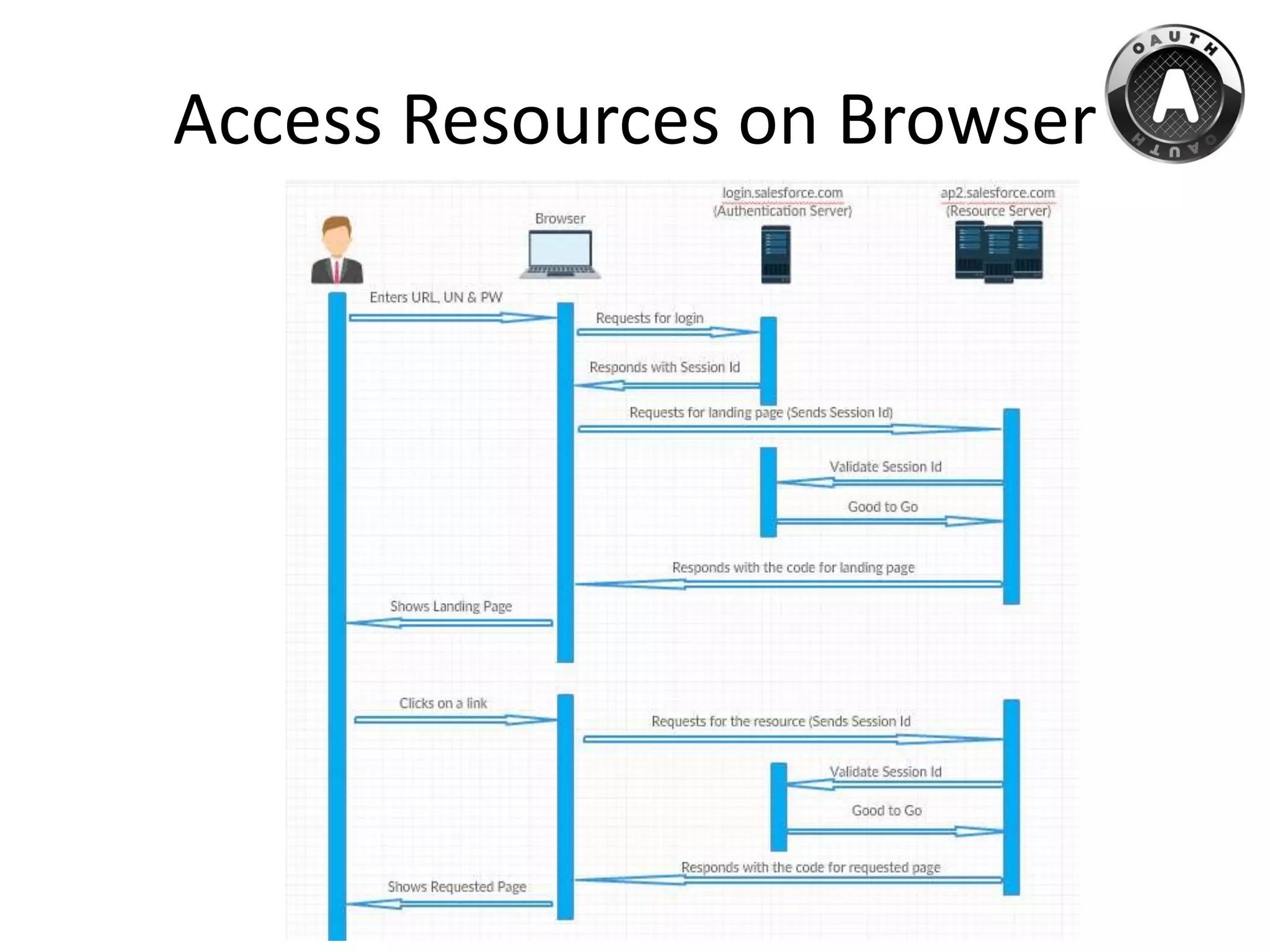
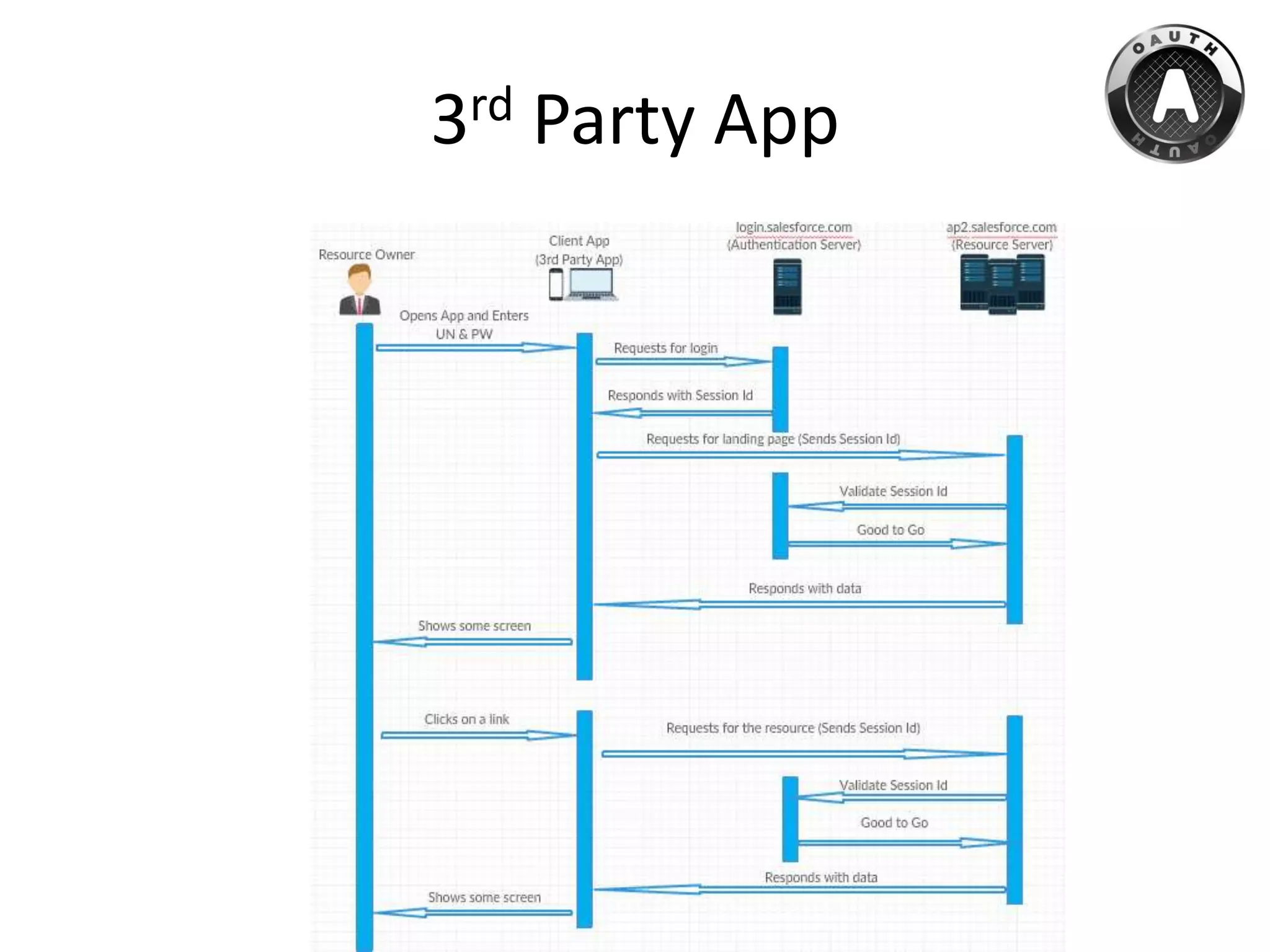
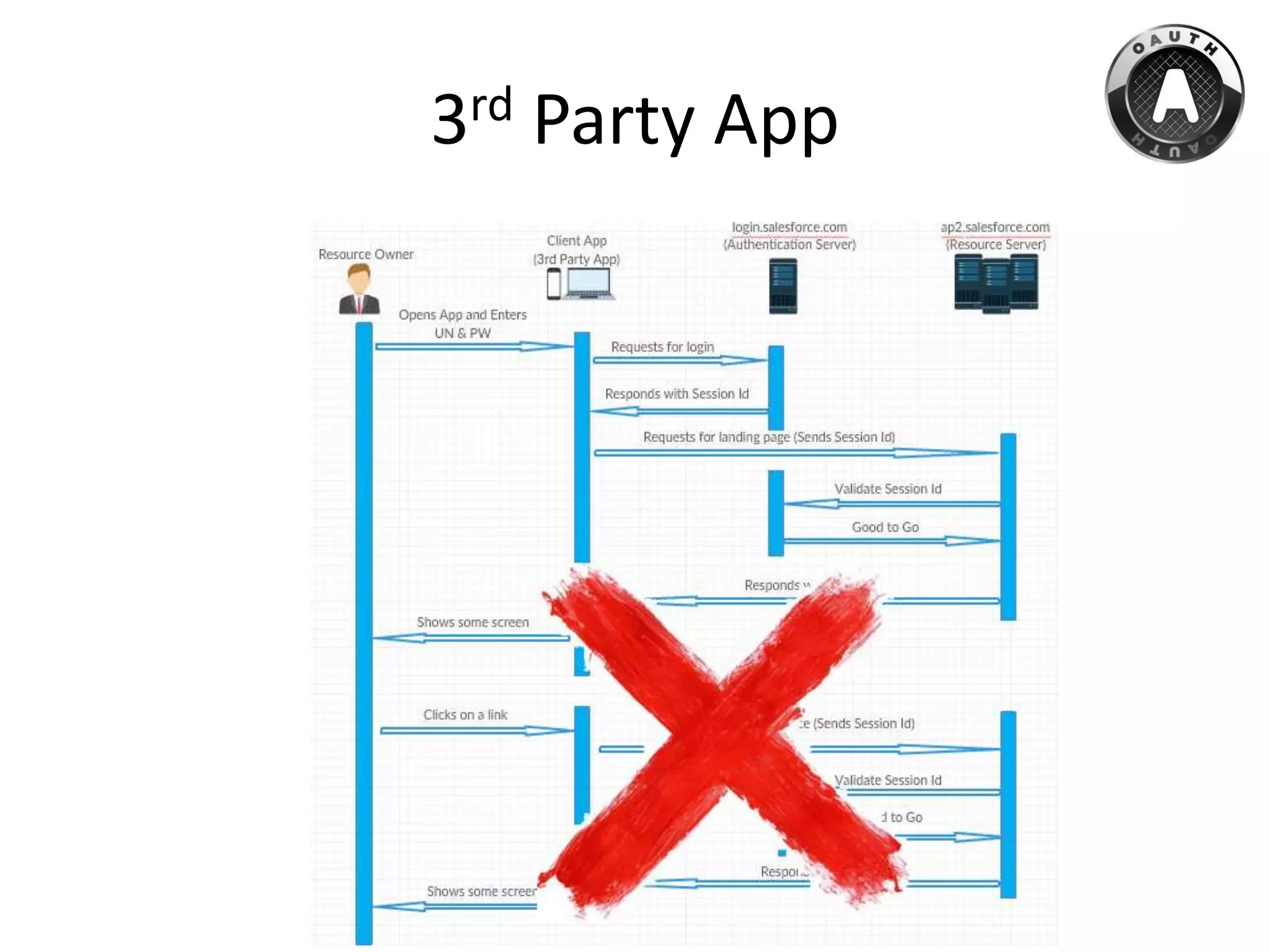
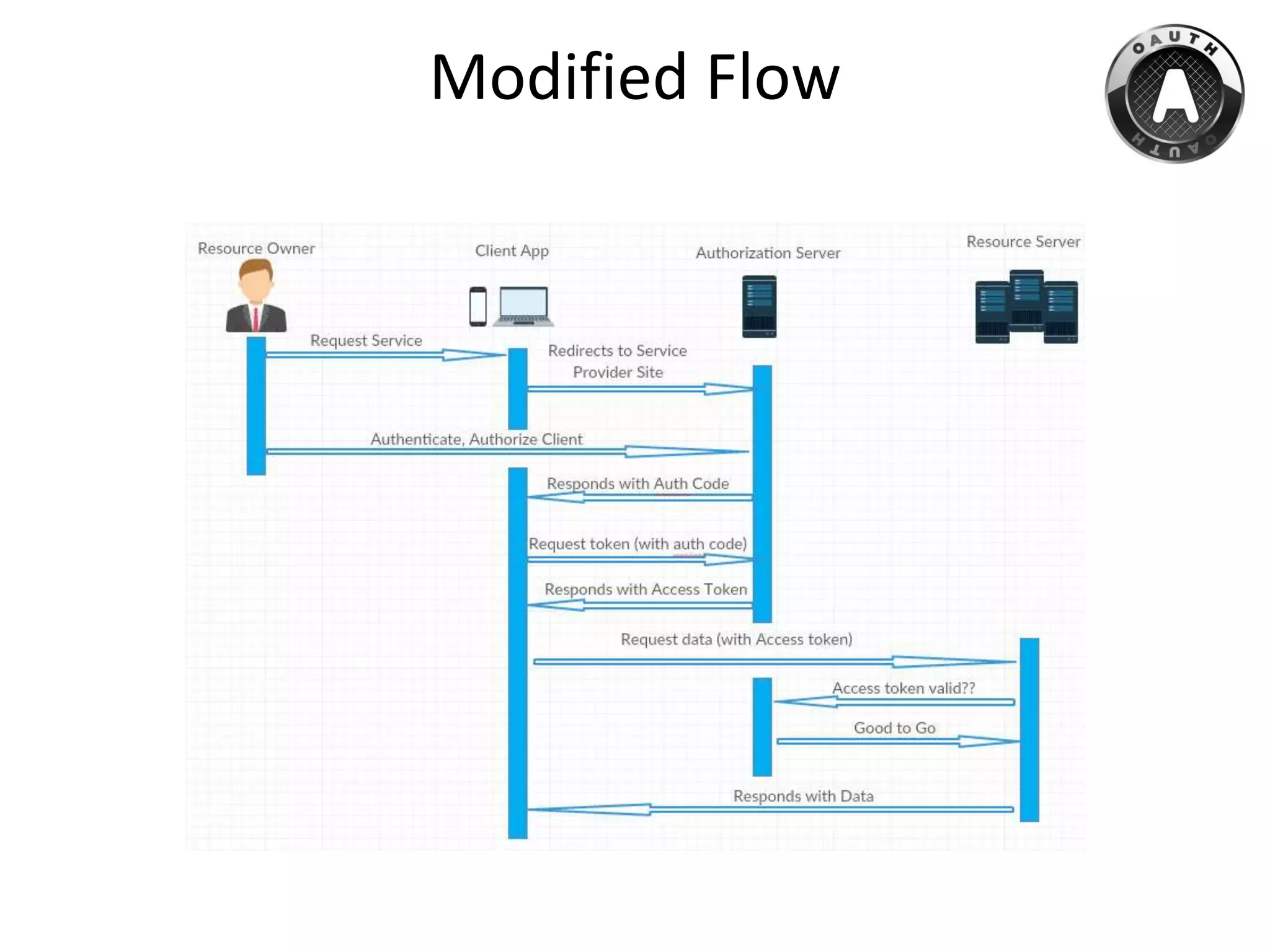
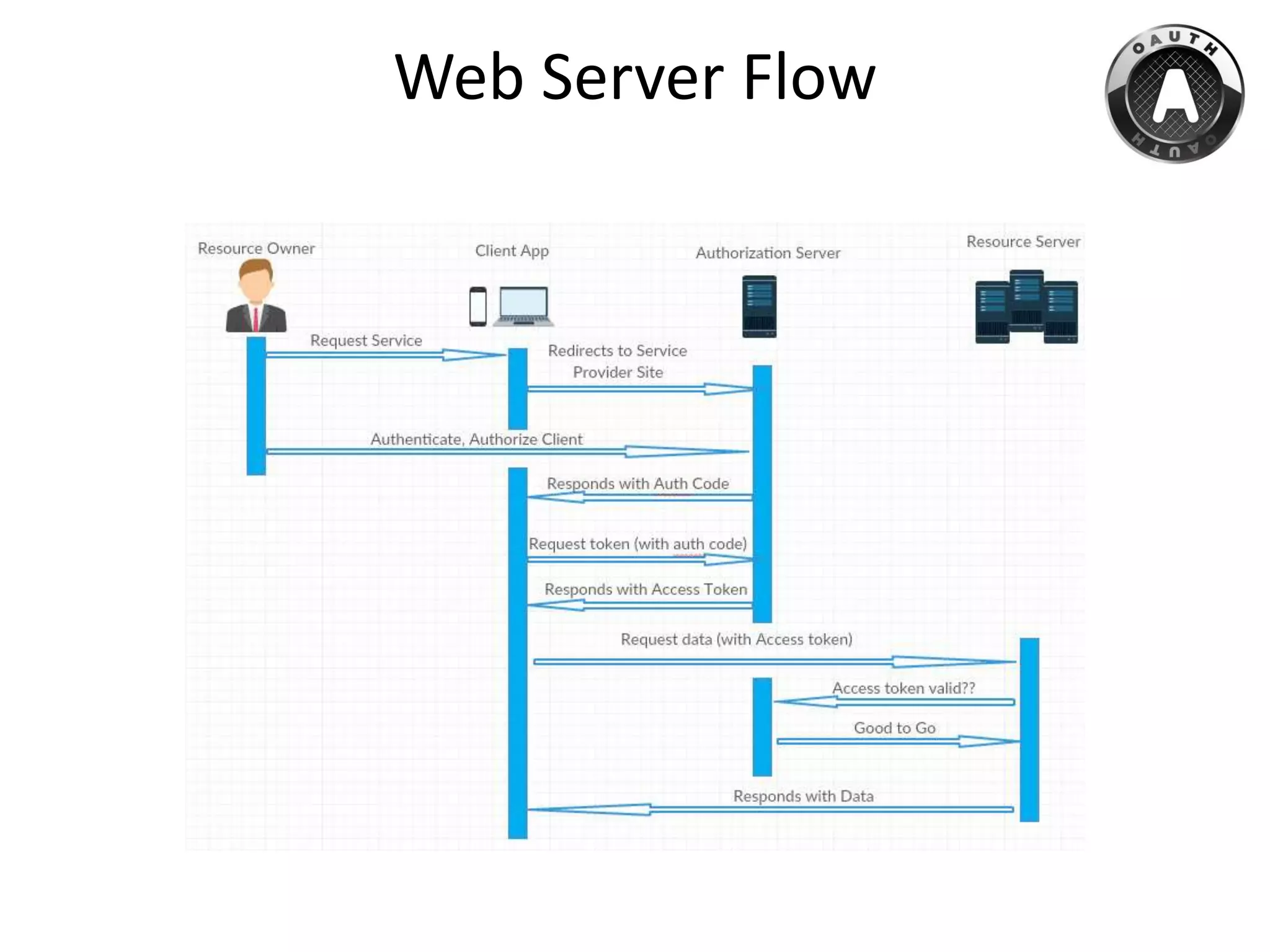
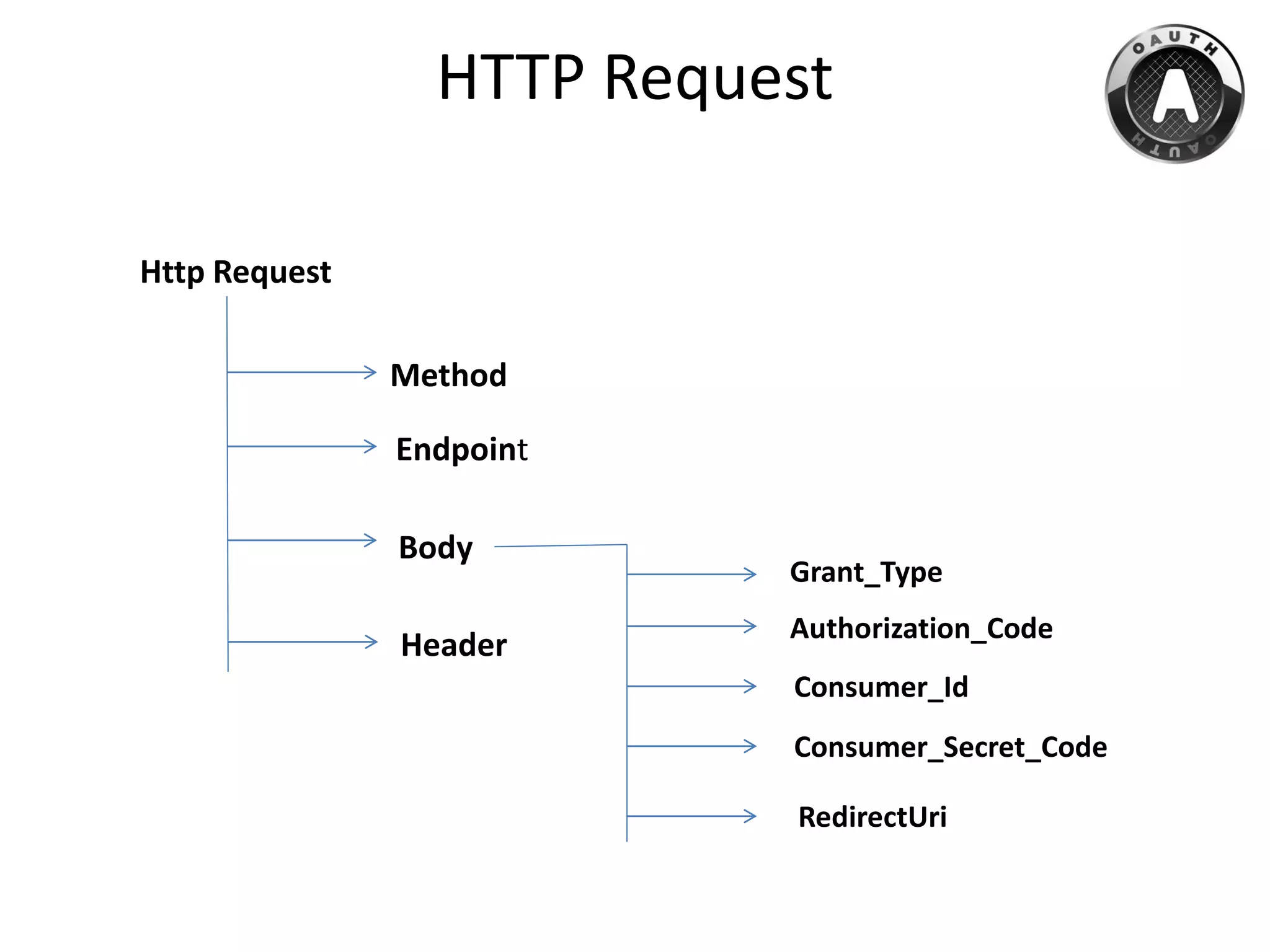
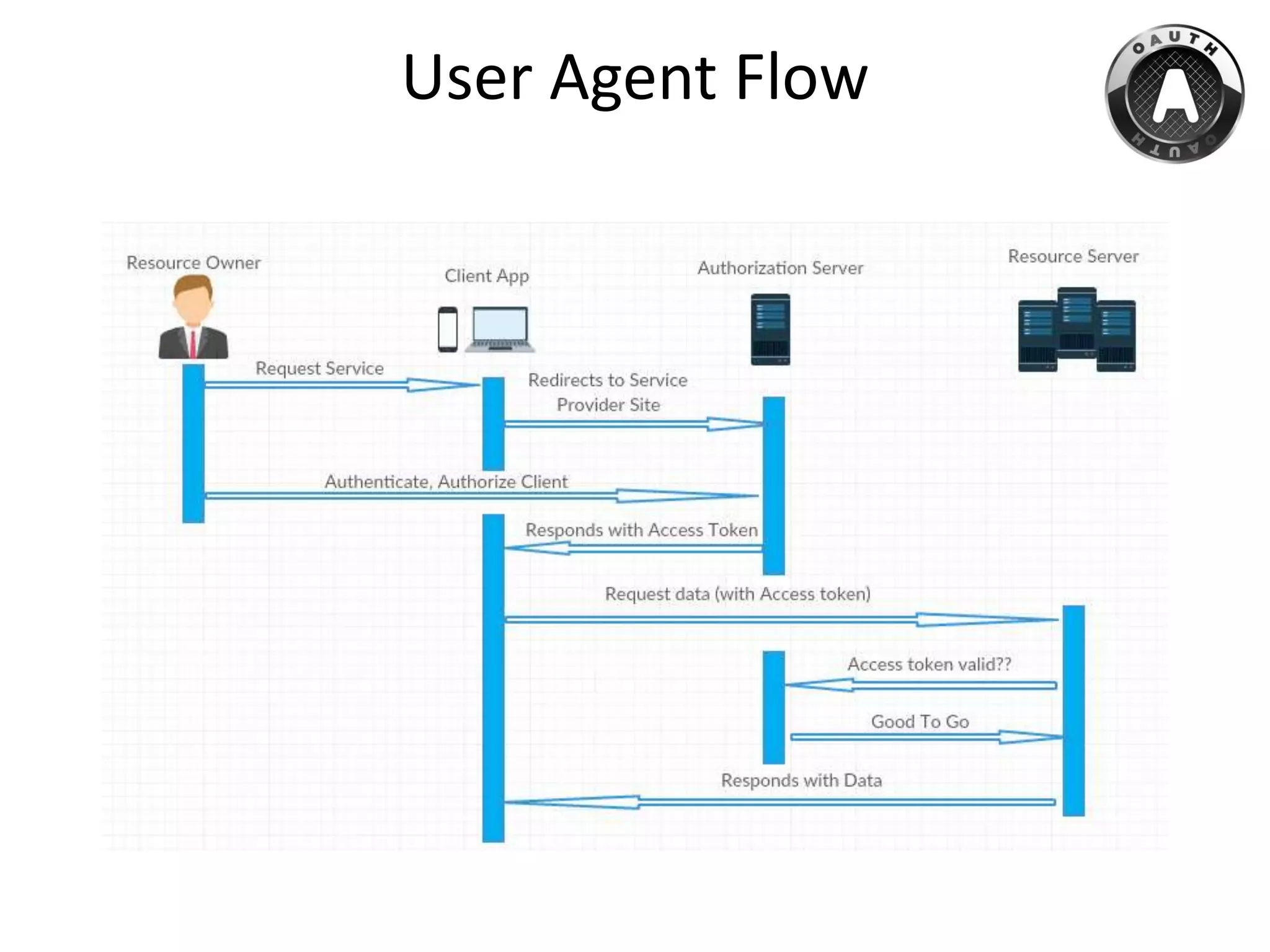
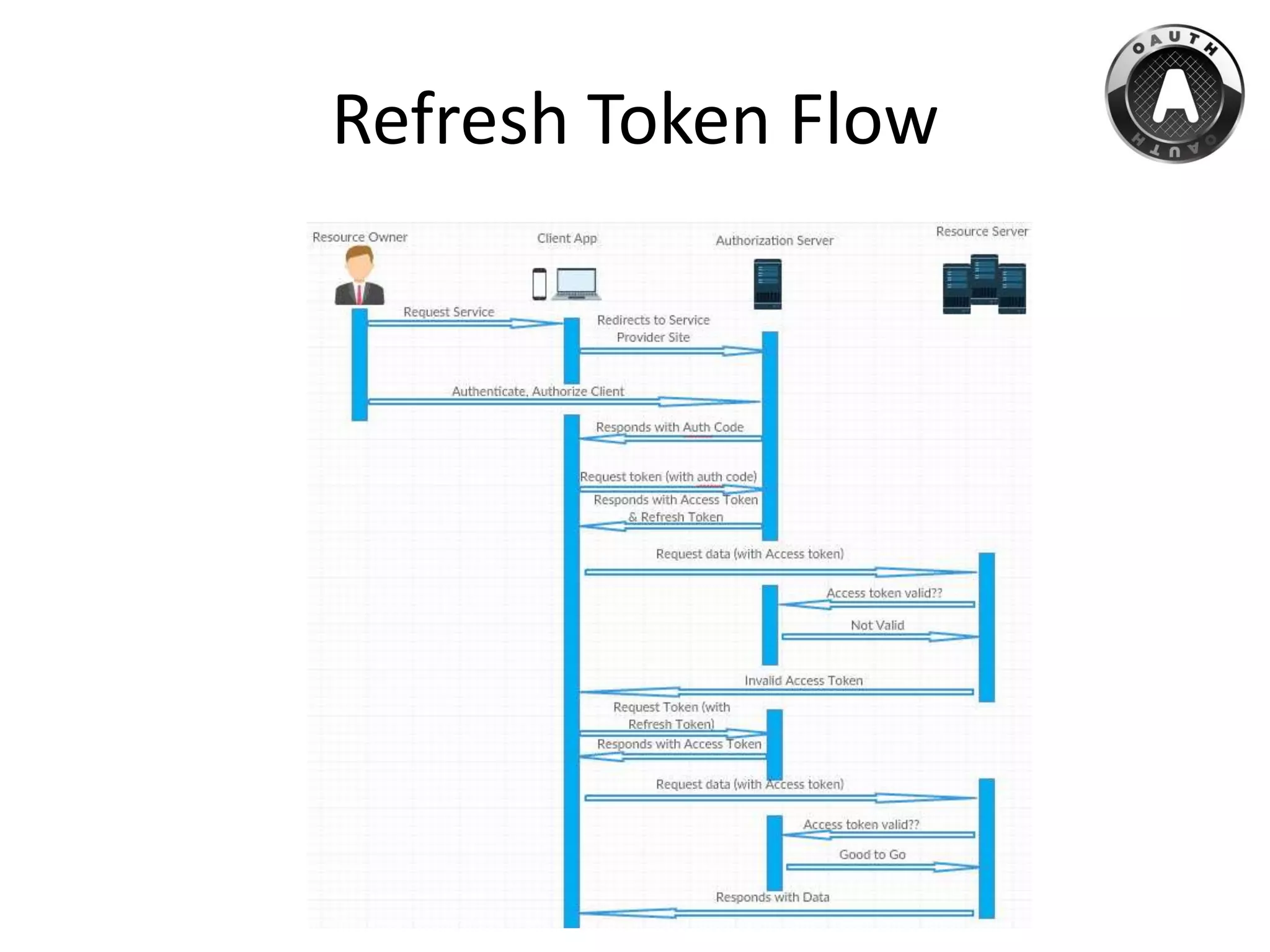
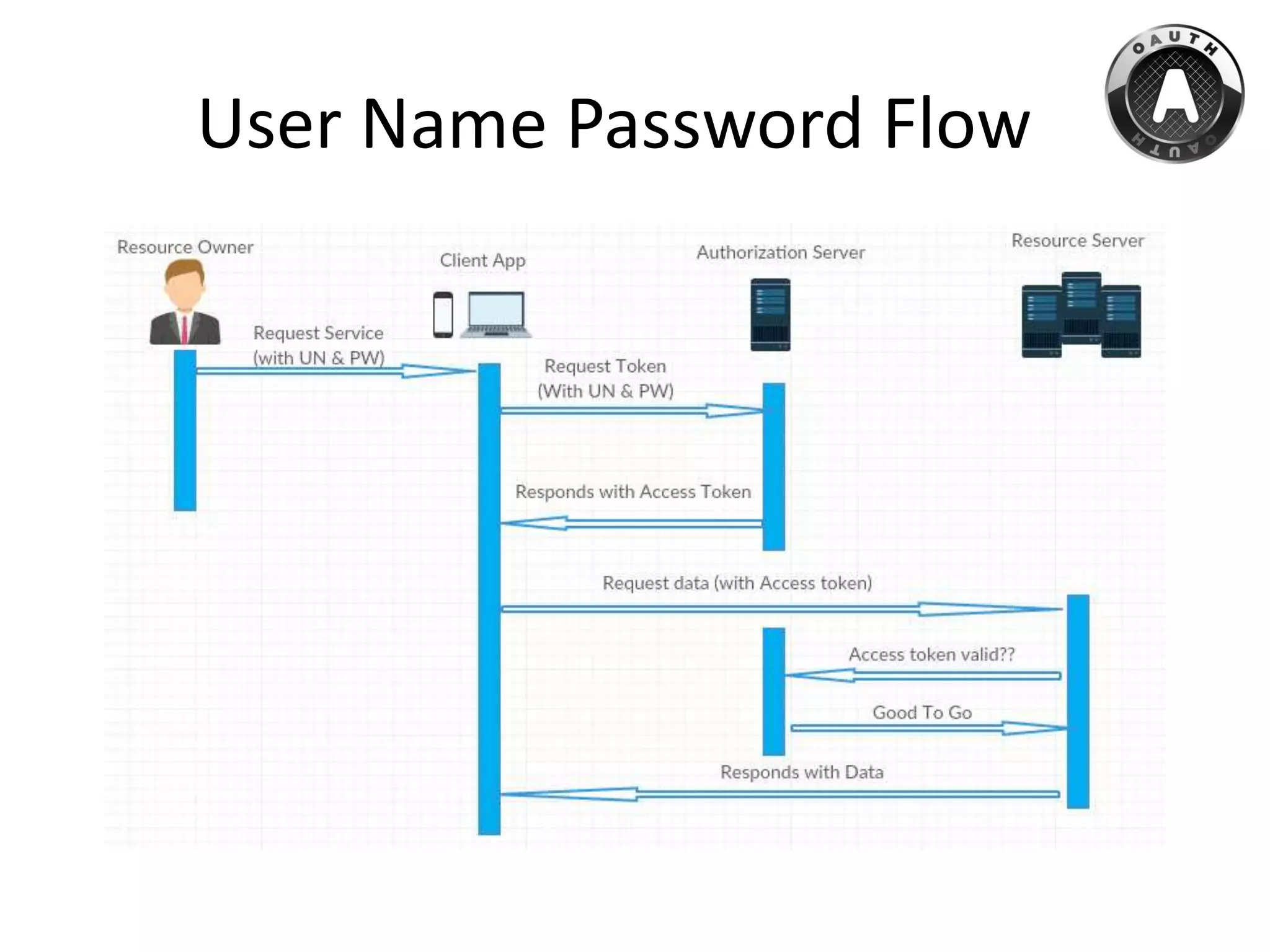
The document provides an overview of OAuth, an authorization protocol that enables third-party applications to access user data securely without sharing passwords. It discusses the need for OAuth to restrict access and how to generate access tokens for API interaction. Additionally, it covers specific implementations of OAuth within Force.com and connected app administration details.