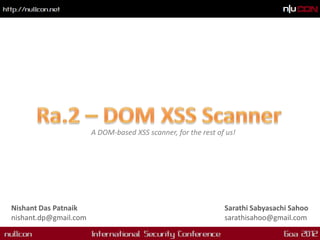
The document discusses DOM-based Cross-Site Scripting (XSS) vulnerabilities, detailing their prevalence and impact, especially in modern web applications that utilize dynamic scripting. It introduces a tool named ra.2, designed for detecting such vulnerabilities through dynamic analysis in the Firefox environment, while comparing it to other existing tools like Dominator. The authors emphasize the importance of combining automated tools with manual testing to effectively address security issues.



![DOM XSS Example Page - 01
01 <script type="text/javascript">
02 var param = location.hash.split("#")[1];
03 document.write("Hello " + param + "!");
04 </script>](https://image.slidesharecdn.com/nullcon-dom-xss-tool-2011-120221014805-phpapp01/85/NullCon-2012-Ra-2-blackbox-DOM-based-XSS-scanner-8-320.jpg)
![DOM XSS Example Page - 02
...
01 function timedMsg(callback)
02 {
03 if(callback)
04 {
05 var t=setTimeout(eval('callback'),3000);
06 return 0;
07 }
08 }
09 function fire()
10 {
11 var call = location.hash.split("#")[1];
12 timedMsg(call);
13 }
14 </script>
15 </head>
16 <body onload="fire()">
...](https://image.slidesharecdn.com/nullcon-dom-xss-tool-2011-120221014805-phpapp01/85/NullCon-2012-Ra-2-blackbox-DOM-based-XSS-scanner-9-320.jpg)
![DOM XSS Example Page - 03
...
01 function go()
02 {
03 if (document.location.hash.split("#")[1])
04 {
05 location.replace(location.hash.split("#")[1]);
06 }
07 }
08 </script>
09 </head>
10 <body onload="go()">
...](https://image.slidesharecdn.com/nullcon-dom-xss-tool-2011-120221014805-phpapp01/85/NullCon-2012-Ra-2-blackbox-DOM-based-XSS-scanner-10-320.jpg)
![DOM XSS Example Page - 04
01 <script>
02 var param = document.location.hash.split("#")[1];
03 if (param)
04 {
05 var d = document.createElement('div');
06 d.innerHTML = param;
07 if (document.body != null)
08 {
09 document.body.appendChild(d);
10 }
11 }
12 </script>](https://image.slidesharecdn.com/nullcon-dom-xss-tool-2011-120221014805-phpapp01/85/NullCon-2012-Ra-2-blackbox-DOM-based-XSS-scanner-11-320.jpg)
![DOM XSS Example Page - 05
...
01 <a id="anchor" name="anchor">Continue</a>
02 <script type="text/javascript“>
03 var redir = location.hash.split("#")[1];
04 x = document.getElementById('anchor');
05 x.setAttribute('href',redir);
06 </script>
...](https://image.slidesharecdn.com/nullcon-dom-xss-tool-2011-120221014805-phpapp01/85/NullCon-2012-Ra-2-blackbox-DOM-based-XSS-scanner-12-320.jpg)
![DOM XSS Example Page - 06
...
<body onload=reload()>
<iframe id="frame1" name="frame1" src="about:blank"></iframe>
<script>
function reload()
{
var redir = location.hash.split("#")[1];
if (redir)
{
x = document.getElementById('frame1');
x.setAttribute('src',redir);
}
}
...](https://image.slidesharecdn.com/nullcon-dom-xss-tool-2011-120221014805-phpapp01/85/NullCon-2012-Ra-2-blackbox-DOM-based-XSS-scanner-13-320.jpg)