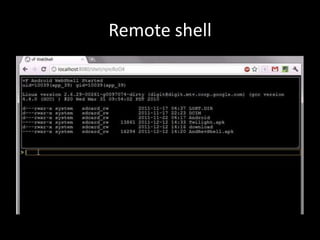
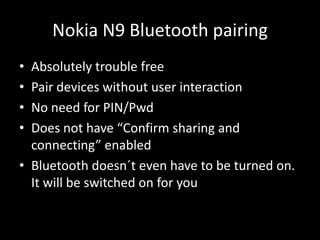
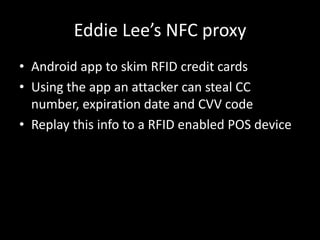
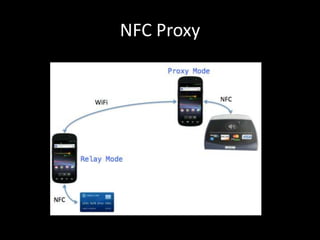
NFC attacks can be used to compromise devices and steal sensitive data. NFC allows passive communication up to 4cm and can be used to pair Bluetooth devices without user interaction, enabling theft of credit card data. Researchers have created tools like an NFC proxy Android app that can skim RFID credit cards by replaying the stolen card data to a payment terminal. Proper security measures are needed to protect against these NFC hacking techniques.