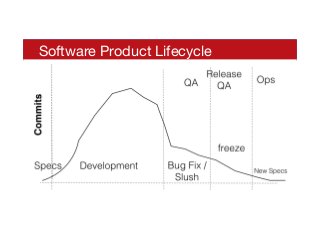
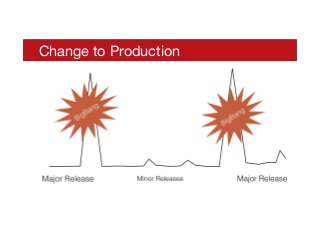
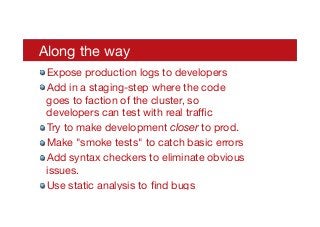
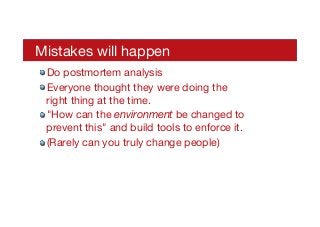
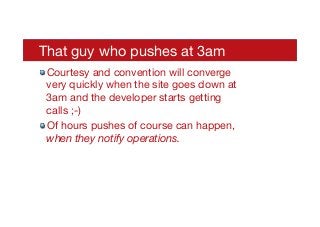
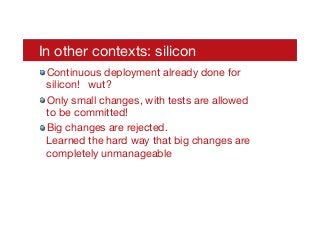
The document discusses the importance of using continuous deployment to enhance software security in development processes. It argues that traditional long release cycles hinder effective security practices and emphasizes that frequent, small changes can better integrate security into the development workflow. Additionally, it provides insights on getting started with continuous deployment, including the necessary tools and processes for successful implementation.




![Let's Just Give Up
! “You could spend all your resources chasing such
things as this,” William Ribich, the former president of
Technology Solutions Group [ QintelIQ ], said in an
interview in January. Ribich, who retired in November 2009,
shortly after the discovery of a major data theft, said he
needed to balance the uncertain risk that the hackers could
use what they stole against a growing shopping list of
security products and consulting fees.
! "You finally have to reach a point where you say
’let’s move on,’” he said.
http://www.bloomberg.com/news/2013-05-01/china-cyberspies-outwit-u-s-stealing-military-secrets.html](https://image.slidesharecdn.com/fixingsecuritybyfixingsoftwaredevelopment-130508190442-phpapp01/85/Fixing-security-by-fixing-software-development-11-320.jpg)