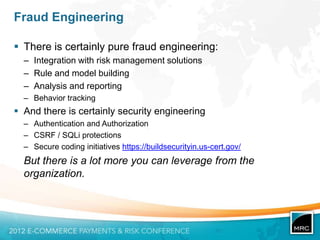
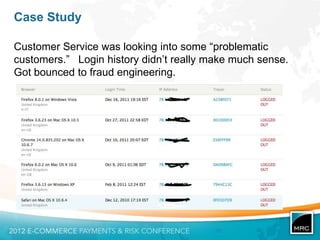
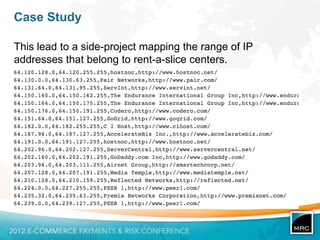
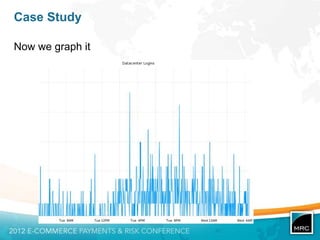
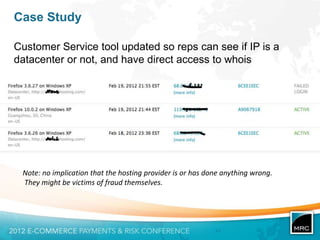
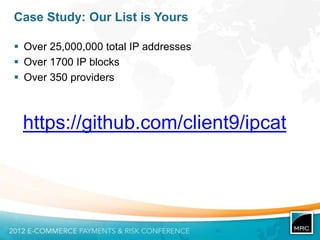
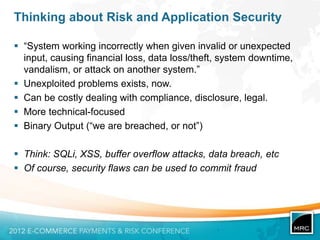
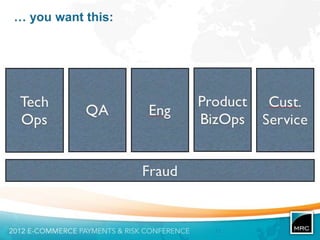
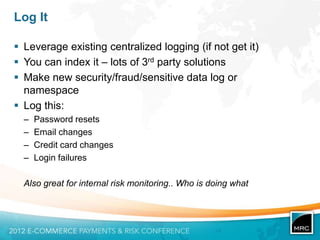
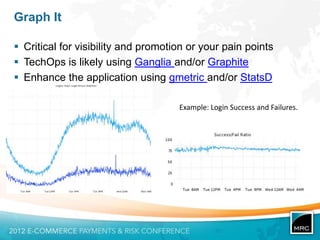
This document discusses fraud engineering at Etsy. It begins by introducing the author, Nick Galbreath, and his background in security. It then provides context about Etsy as an online marketplace. It outlines different types of risk like fraud, security threats, and business continuity. It emphasizes thinking about risk from both a fraud and security perspective. The document then provides examples of how different parts of the organization like technical operations, quality assurance, product, business operations, engineering, and customer service can work together on fraud prevention and leverages their existing tools and resources. It also provides a case study example of investigating mysterious data center logins. The overall message is about taking a holistic organizational approach to fraud engineering.




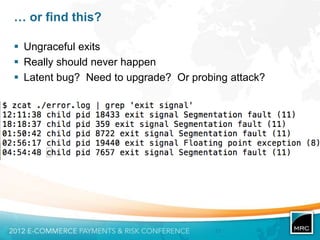
![Use the central log to find…
Syntax errors from the database!
Certainly a bug, but perhaps SQLi attempts
Uncaught DatabaseException: 42601 7 ERROR:
syntax error at position 2 near "&" in
SELECT COUNT(*) FROM convos
WHERE uid = ? AND names LIKE „?‟
with [895724897,"Ll'or1=1"]
at DBConnection.php
based on a true story
all queries and values changed to protect the guilty](https://image.slidesharecdn.com/mrc2012generalconf-120503155011-phpapp02/85/Fraud-Engineering-from-Merchant-Risk-Council-Annual-Meeting-2012-22-320.jpg)